kami@kali:~$ journalctl
-
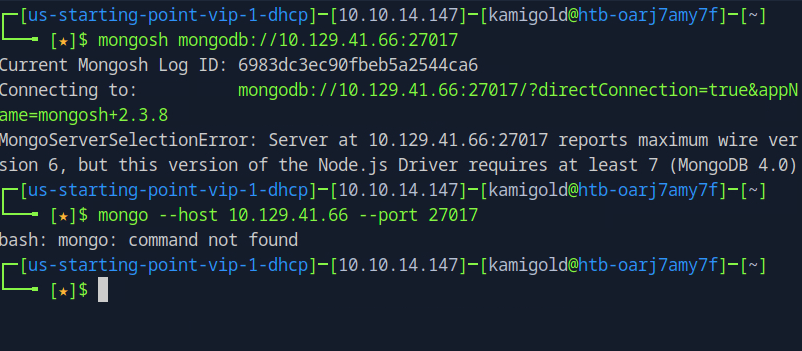
Synced writeup
10.129.41.246
Task 1 – What is the default port for rsync?
Scanned the machine with “”nmap -A -p- 10.129.41.246”
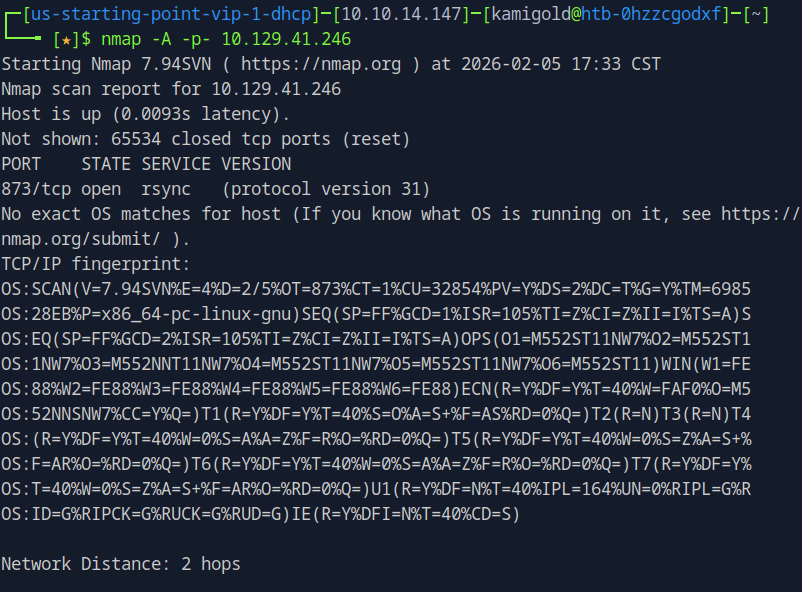
Only port open was 873, so assumption is that is the default.
A: 873
Task 2 – How many TCP ports are open on the remote host?
Previous scan.
A: 1
Task 3 – What is the protocol version used by rsync on the remote machine?
Previous scan.
A: 31
Task 4 – What is the most common command name on Linux to interact with rsync?
Had notes on this from before, unsurprisingly it’s just rsync
A: rsync
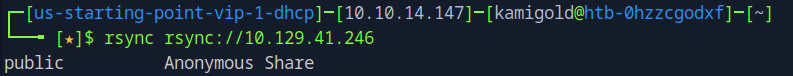
Task 5 – What credentials do you have to pass to rsync in order to use anonymous authentication? anonymous:anonymous, anonymous, None, rsync:rsync
A: None
Task 6 – What is the option to only list shares and files on rsync? (No need to include the leading — characters)
I didn’t know this. As usual in my notes I keep how to get to the help menu of commands. Ran “”rsync -h”” and looked through the output.
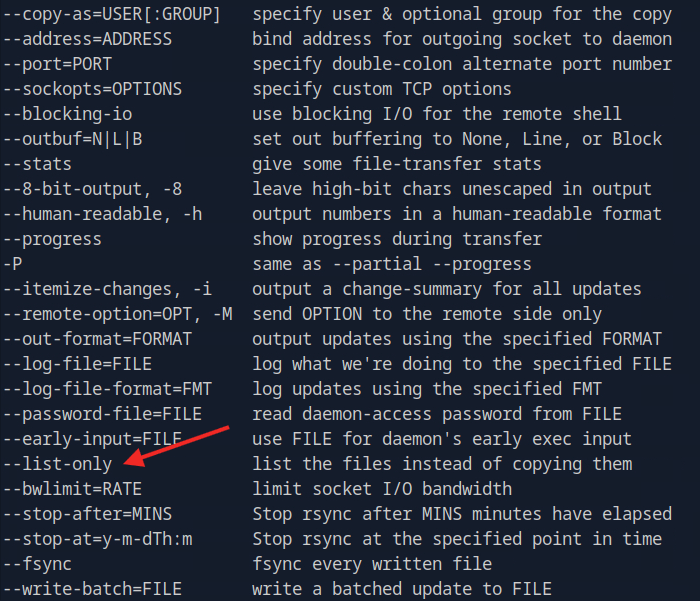
A: list-only
Submit Flag:
With the previous knowledge I ran it on the ‘public’ directory.
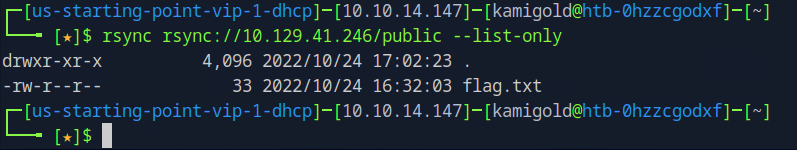
I somehow needed to read or download this file so I reviewed the help command again. I couldn’t find anything through that, but it turns out I ended up having notes already. Looking back in the help menu I just missed it. This will download the file to my /kamigold directory.
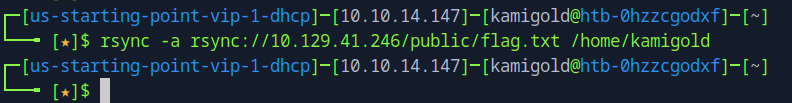
A: 72eaf5344ebb84908ae543a719830519
-
Mongod writeup
10.129.41.66
Task 1 – How many TCP ports are open on the machine?
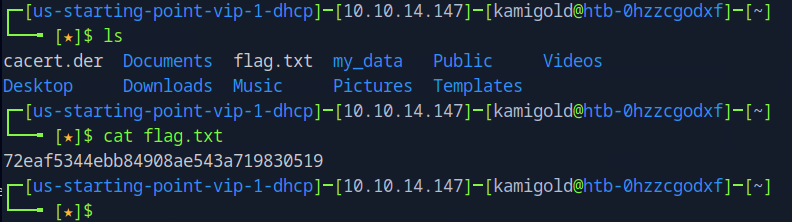
Ran “”nmap -A -p- 10.129.41.66””
A: 2
Task 2 – Which service is running on port 27017 of the remote host?
A: MongoDB 3.6.8
Task 3 – What type of database is MongoDB? (Choose: SQL or NoSQL)
I didn’t know this. I tried scanning the rest of the nmap scan but I don’t think it provided anything that could point toward it being NoSQL. Also not sure if any further nmap switch could reveal more. I ended up just googling this.
A: NoSQL
Task 4 – What command is used to launch the interactive MongoDB shell from the terminal?
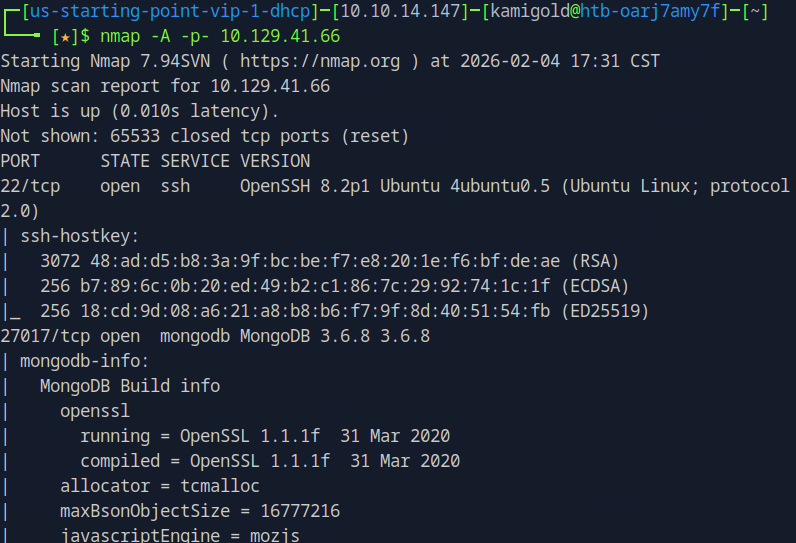
Didn’t know any of this so looked up some pentesting notes. Found this https://hackviser.com/tactics/pentesting/services/MongoDB
Mongo wasnt on our attacker machine and mongosh doesnt work for that version. I went to install Mongo to see if that would connect and it did
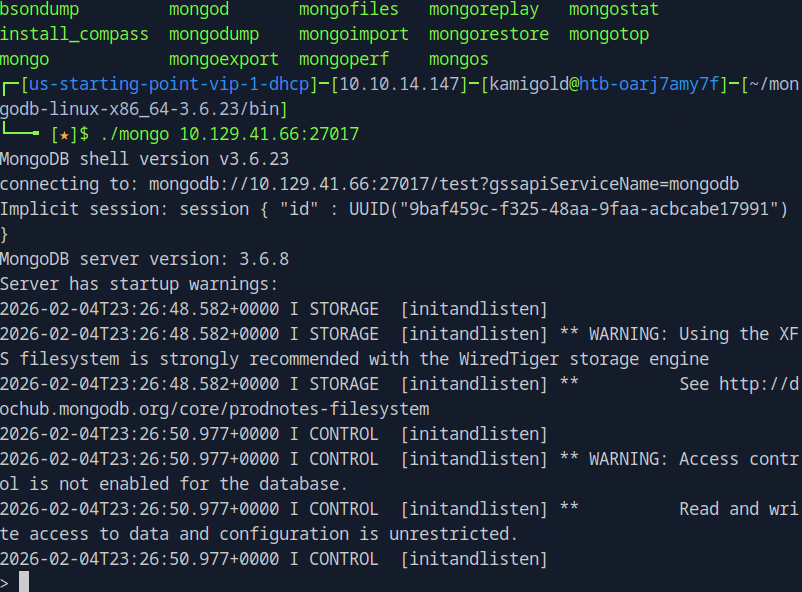
“”wget https://fastdl.mongodb.org/linux/mongodb-linux-x86_64-3.6.23.tgz””
“”tar -xvzf mongodb-linux-x86_64-3.6.23.tgz””
Navigated to the folder and ran “”./mongo 10.129.41.66:27017””
That worked but looking at the answer ending in h, it must have been mongosh. Probably because the machine is older and mongosh has updated since then but it was intended we use that.
A: mongosh
Task 5 – What is the command used for listing all the databases present on the MongoDB server? (No need to include a trailing 😉
Following the notes on the site
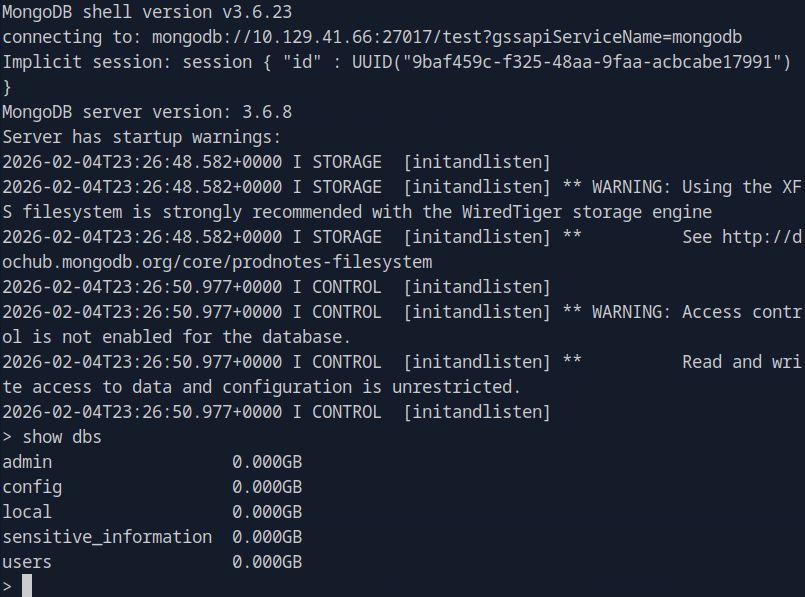
A: dbs
Task 6 – What is the command used for listing out the collections in a database? (No need to include a trailing 😉
Still following those notes, these are great.

It didnt seem to return anything though.
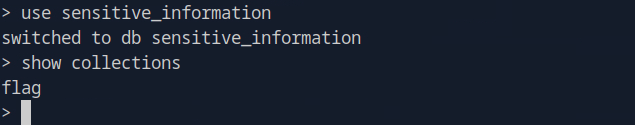
A: show collections
Task 7 – What command is used to dump the content of all the documents within the collection named flag?
I then realised that I’m supposed to “”use {database}”” then show collections. Poked around and found ‘flag’ in the sensitive_information database.
I couldn’t find how to interact with ‘flag’ from the notes on that website. Ended up researching further and found myself in the actual documentation. https://www.mongodb.com/docs/manual/crud/#find-documents
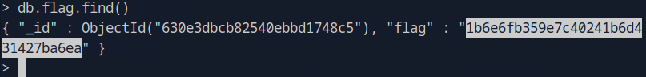
A: db.flag.find()
Submit Flag: 1b6e6fb359e7c40241b6d431427ba6ea
-
Preignition writeup
10.129.40.89
Task 1 – Directory Brute-forcing is a technique used to check a lot of paths on a web server to find hidden pages. Which is another name for this? (i) Local File Inclusion, (ii) dir busting, (iii) hash cracking.
A: dir busting
Task 2 – What switch do we use for nmap’s scan to specify that we want to perform version detection
A: -sV
Task 3 – What does Nmap report is the service identified as running on port 80/tcp?
Ran nmap to scan the device, even though it is likely a webserver on http
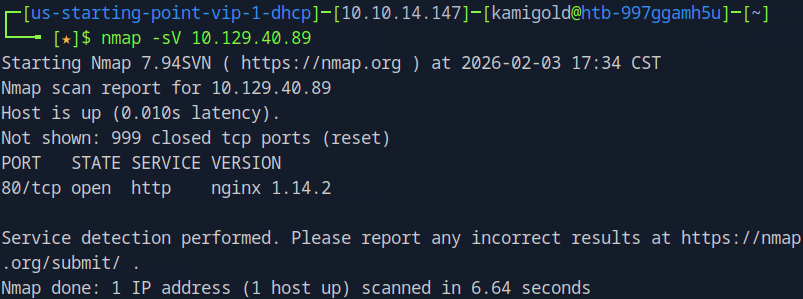
A: http
Task 4 – What server name and version of service is running on port 80/tcp?
A: nginx 1.14.2
Task 5 – What switch do we use to specify to Gobuster we want to perform dir busting specifically?
Already used gobuster, so I know this
A: dir
Task 6 – When using gobuster to dir bust, what switch do we add to make sure it finds PHP pages?
A: -x php
Already had this in notes to, can remember this as x for extension
Task 7 – What page is found during our dir busting activities?
Ran
‘’gobuster dir -u 10.129.40.89 -w gobuster dir -u 10.129.40.89 -w /usr/share/wordlists/dirbuster/directory-list-1.0.txt’’
That returned nothing but that didn’t seem right. Even though its a smaller list I couldn’t imagine a easier box that had issue. Considering Task 6 I decided to add that switch
“gobuster dir -u 10.129.40.89 -w /usr/share/wordlists/dirbuster/directory-list-1.0.txt -x php”
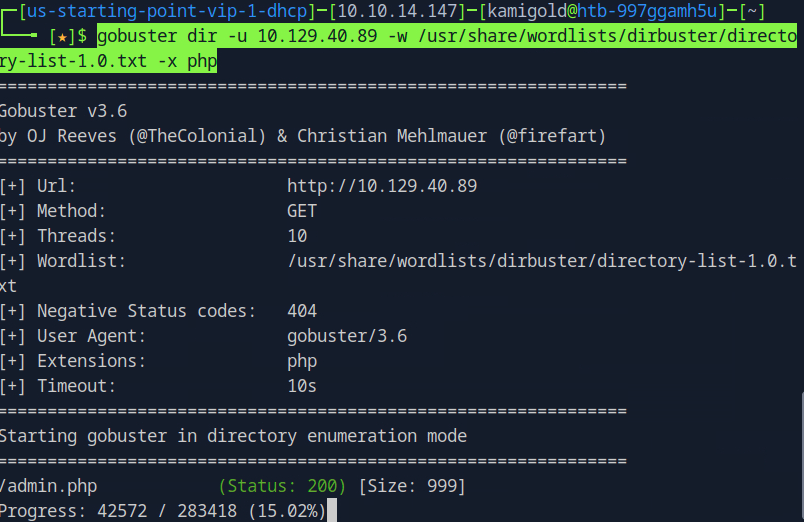
This worked and found /admin.php right away
Task 8 – What is the HTTP status code reported by Gobuster for the discovered page?
In previous screenshot status is 200
A: 200
Submit Flag:
Navigated to the website at that newly found directory and it brought us to an Admin Console Login searching for a username and password. Considering they fastballs thrown at me, I attempted admin:admin and it worked.
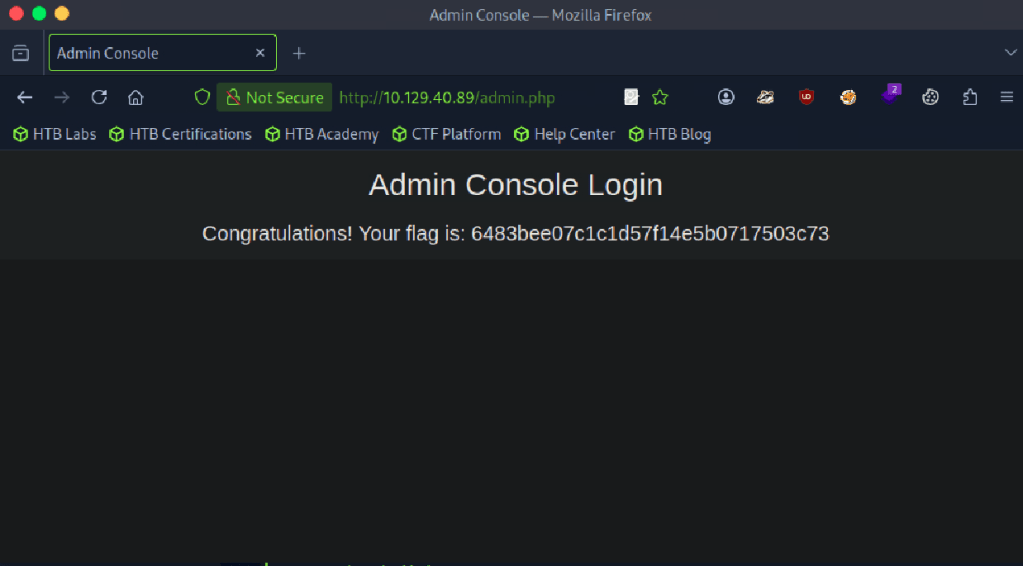
A: 6483bee07c1c1d57f14e5b0717503c73
-
Explosion writeup
This is a very easy box so the first few tasks I just knew from previous experience.
Task 1: What does the 3-letter acronym RDP stand for?
A: Remote Desktop Protocol
Task 2: What is a 3-letter acronym that refers to interaction with the host through a command line interface?
A: CLI
Task 3: What about graphical user interface interactions?
A: GUI
Task 4: What is the name of an old remote access tool that came without encryption by default and listens on TCP port 23?
Task 5: What is the name of the service running on port 3389 TCP?
Couldn’t remember this off the top of my head and my machine has started by now.
10.129.39.161
Scanned the machine with nmap -p- 10.129.39.161 that shows 135, 139, 445,
3389, 5985, 47001, 49664, 49665, 49666, 49667, 49668,49669, 49670, 49671
Ran nmap -A -p135, 139, 445,
3389, 5985, 47001, 49664, 49665, 49666, 49667, 49668,49669, 49670, 49671 10.129.39.161
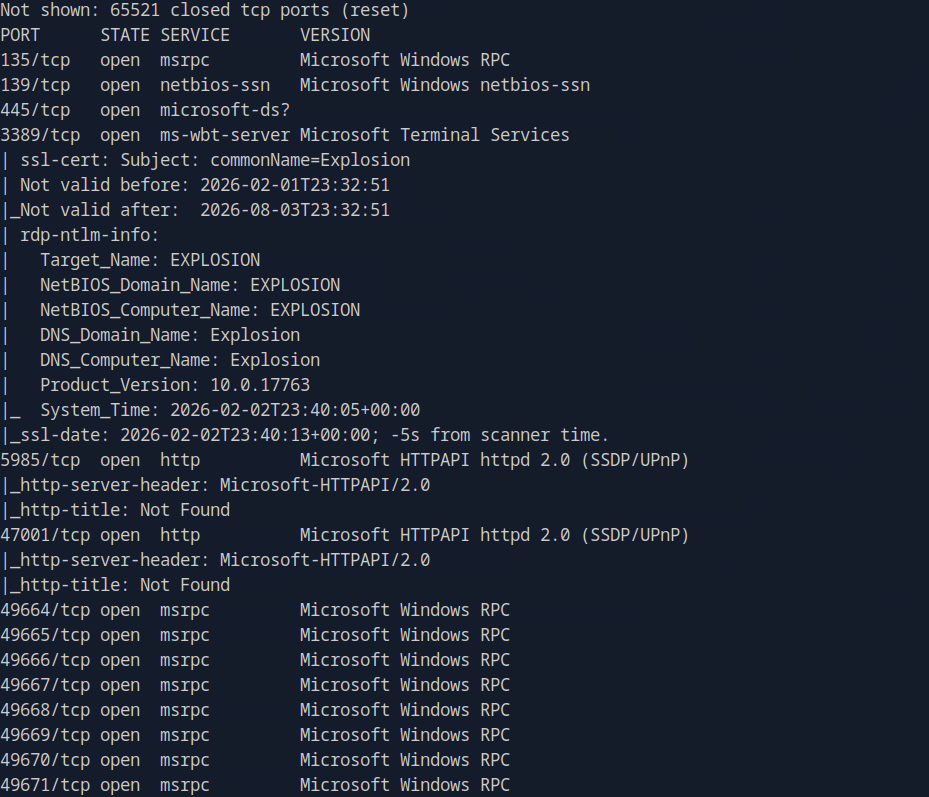
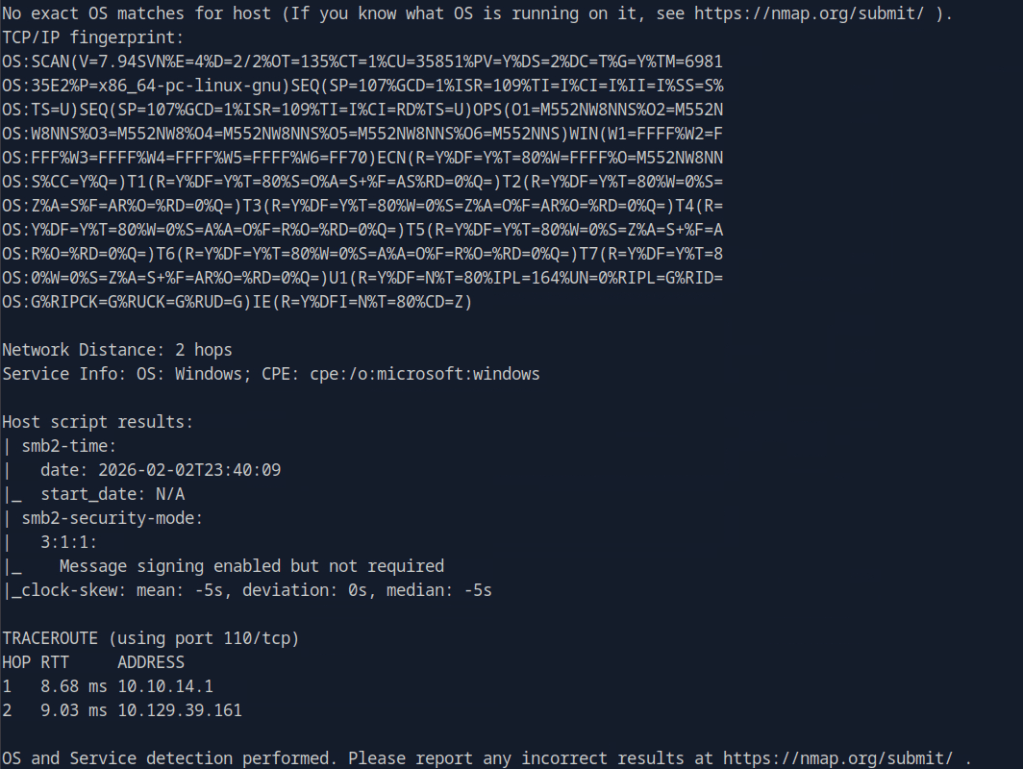
A: ms-wbt-server
Task 6: What is the switch used to specify the target host’s IP address when using xfreerdp?
Knew this from previous experience
“”xfreerdp /v:10.10.161.253 /u:thm /p:TryHackM3””
A: /v:
Task 7: What username successfully returns a desktop projection to us with a blank password?
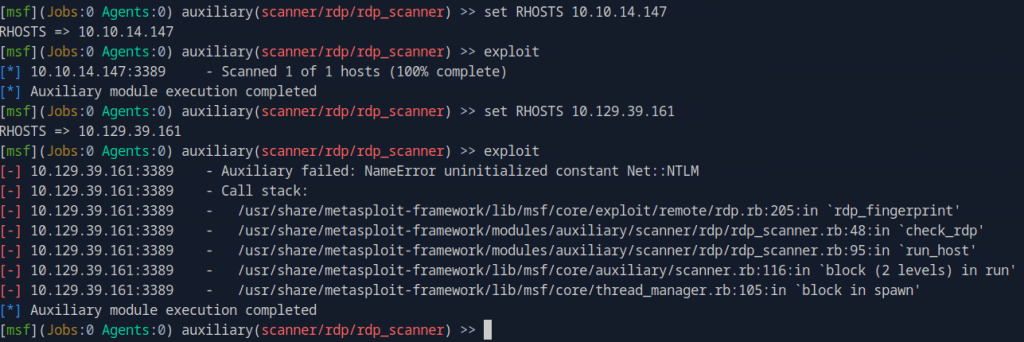
Considering that this box looks RDP related I wanted to scan it. I kicked up metasploit to use auxiliary/scanner/rdp/rdp_scanner and it didnt work. Realize I mistakenly set RHOSTS to myself, so set it properly to 10.129.39.131 but got some errors.
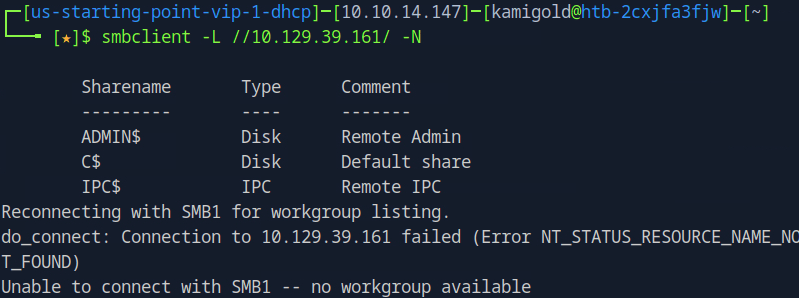
If I’m thinking about this properly, our next step will be to find credentials to use against RDP. I’m going to move to poking at the SMB ports instead. I attempted to list any interesting shares.
When I did this I have to be completely overcomplicating things since this must be a Very Easy box. A bit of meta, but then actually reading the question I just guessed that the default Administrator may be enabled and turns out I was correct.
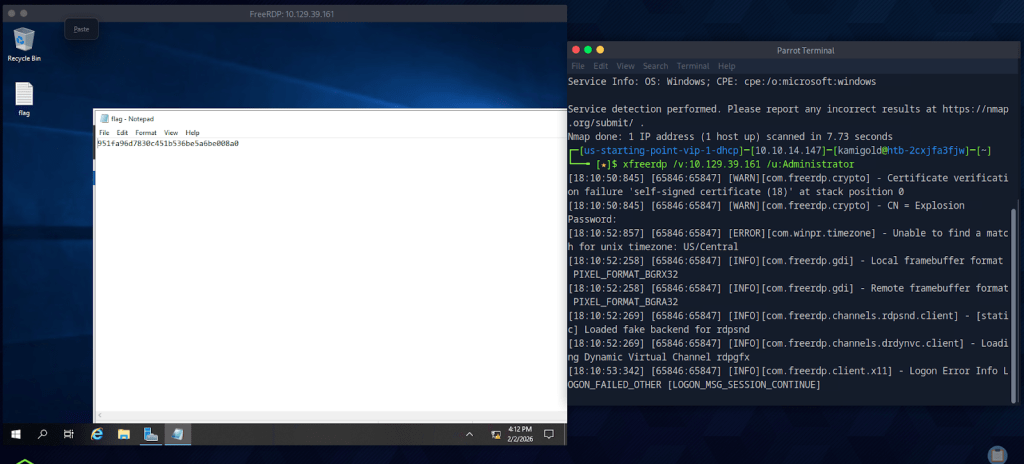
A: Administrator
Submit Flag: 951fa96d7830c451b536be5a6be008a0
GG
-
Redeemer writeup
10.129.136.187
Task 1 – Which TCP port is open on the machine?
Scanned the target with “”nmap -A -p- 10.129.136.187””.
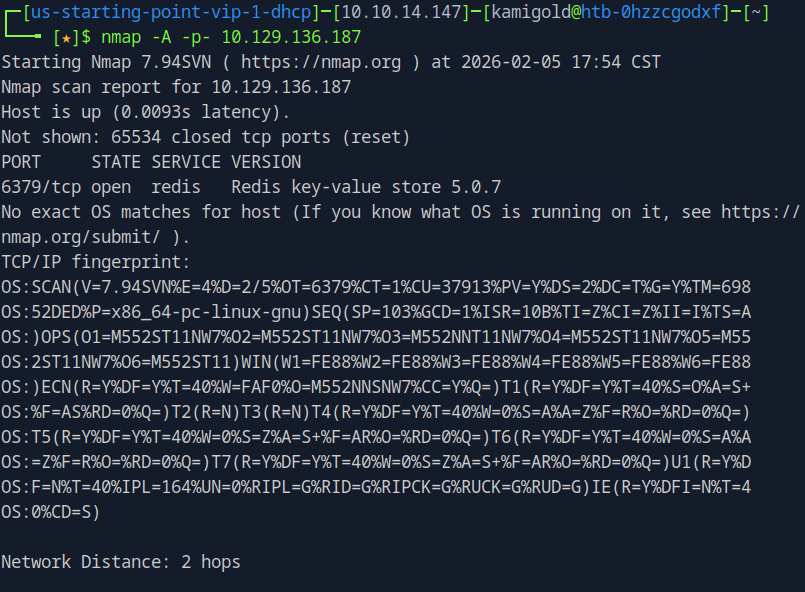
A: 6379
Task 2 – Which service is running on the port that is open on the machine?
A: redis
Task 3 – What type of database is Redis? Choose from the following options: (i) In-memory Database, (ii) Traditional Database
Knew this from previous knowledge.
A: In-memory Database
Task 4 – Which command-line utility is used to interact with the Redis server? Enter the program name you would enter into the terminal without any arguments.
Think I learned this from a TryHackMe box in the past.
A: redis-cli
Task 5 – Which flag is used with the Redis command-line utility to specify the hostname?
A: -h
Task 6 – Once connected to a Redis server, which command is used to obtain the information and statistics about the Redis server?
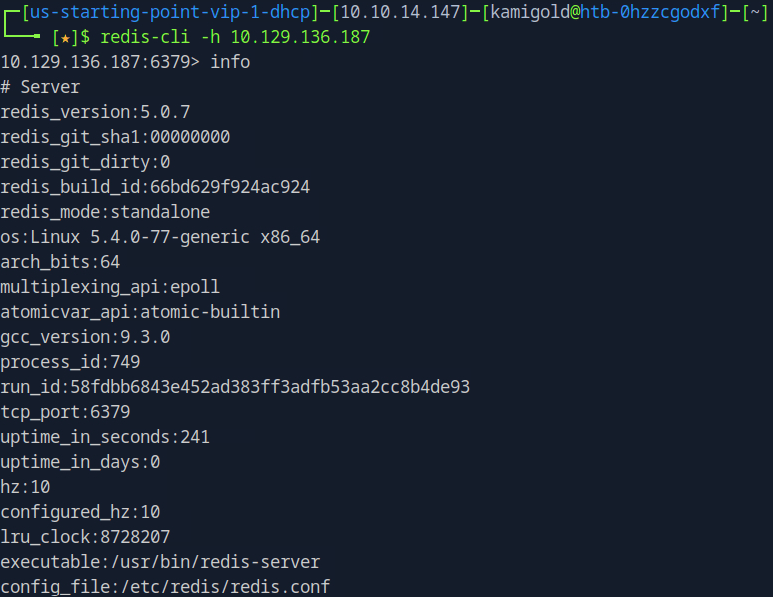
A: INFO
Task 7 – What is the version of the Redis server being used on the target machine?
Besides “”info””, Nmap results also gave us this.
A: 5.0.7
Task 8 – Which command is used to select the desired database in Redis?
A: SELECT
Task 9 – How many keys are present inside the database with index 0?
It skipped a few important parts here but to list databases you’ll need to run “”CONFIG GET databases””. That listed “databases” and “16”. To see what’s inside you can select and run “”KEYS *””. I didn’t find anything in those but the question mentioned index 0 anyways. Selected that, listed keys and we get 4 results.
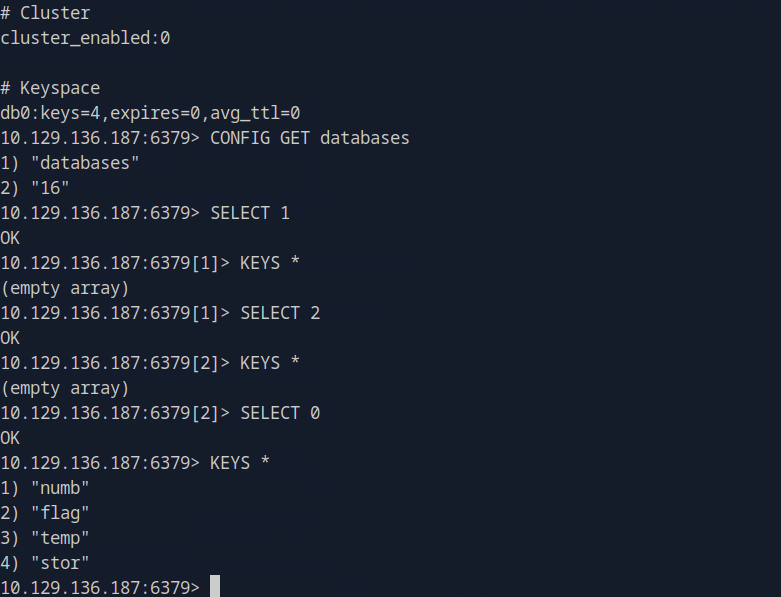
Task 10 – Which command is used to obtain all the keys in a database?
The questions seem like in a weird order if you had no previous knowledge of interacting with redis but luckily I have.
A: KEYS *
Submit Flag:
To actually read the file, you’ll need to use “”GET””
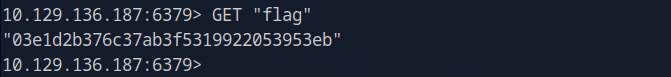
A: 03e1d2b376c37ab3f5319922053953eb
-
Dancing writeup
10.129.1.12
Task 1 – What does the 3-letter acronym SMB stand for?
Previous knowledge
A: Server Message Block
Task 2 – What port does SMB use to operate at?
A: 445
Task 3 – What is the service name for port 445 that came up in our Nmap scan?
Definitely don’t know this off the top of my head so I’ll scan it.
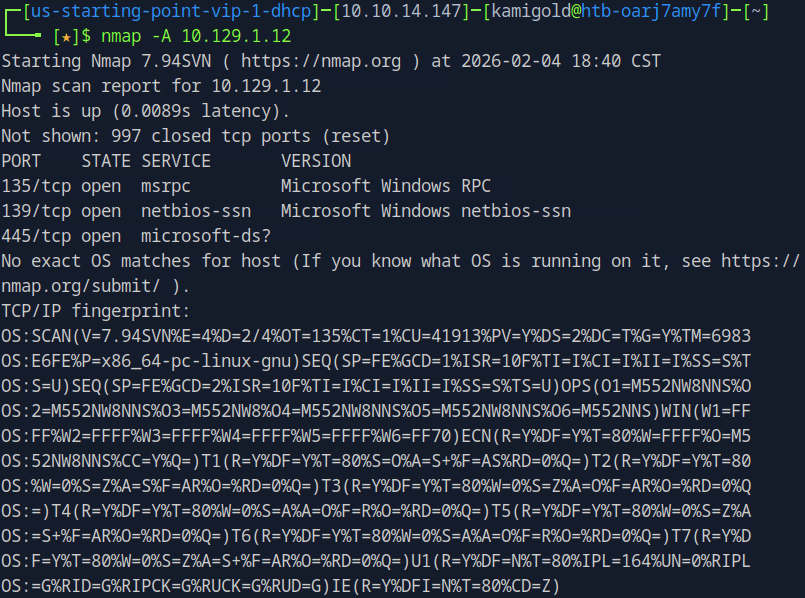
A: microsoft-ds
Task 4 – What is the ‘flag’ or ‘switch’ that we can use with the smbclient utility to ‘list’ the available shares on Dancing?
Back to some previous knowledge of already using these tools. Just remember though this switch needs to exist before the IP for it to work properly. That took me a bit to realize that I was messing up my commands.
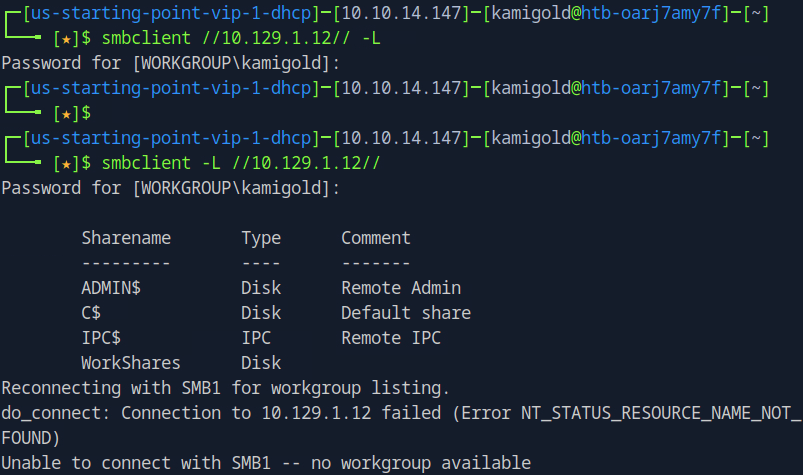
Hitting enter twice I was able to log in anonymously.
A: -L
Task 5 – How many shares are there on Dancing?
A: 4
Task 6 – What is the name of the share we are able to access in the end with a blank password?
A: WorkShares
Task 7 – What is the command we can use within the SMB shell to download the files we find?
A: get
Submit Flag:
Connected anonymously to this share and there are two directories in there.
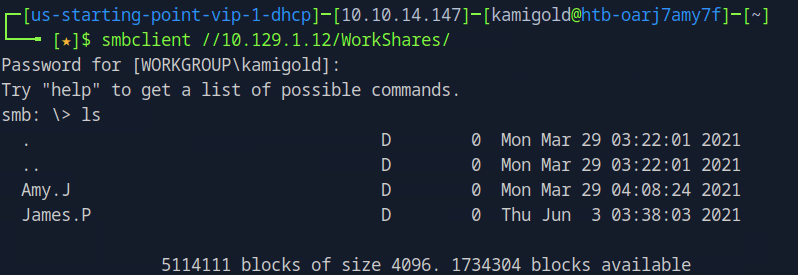
Enumerated the directories and found a flag.txt and worknotes.txt.
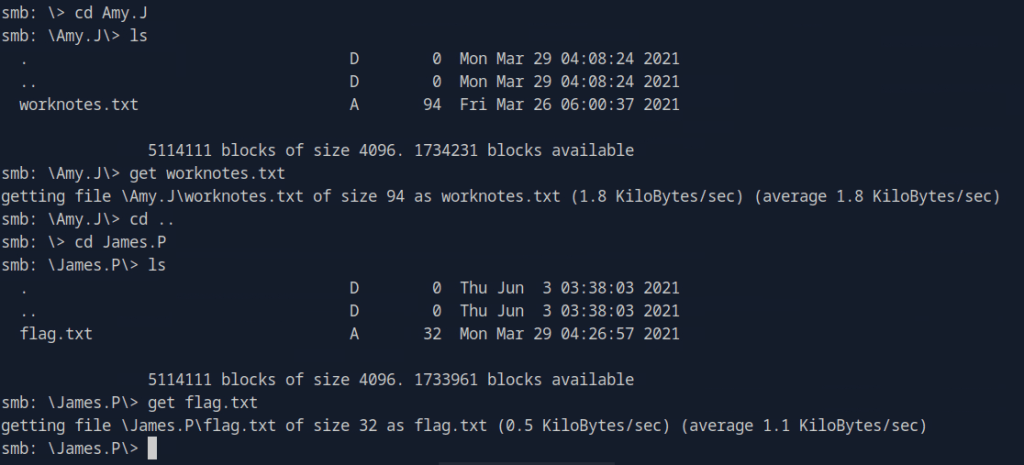
Using “”get”” I downloaded both files on my device and read them.
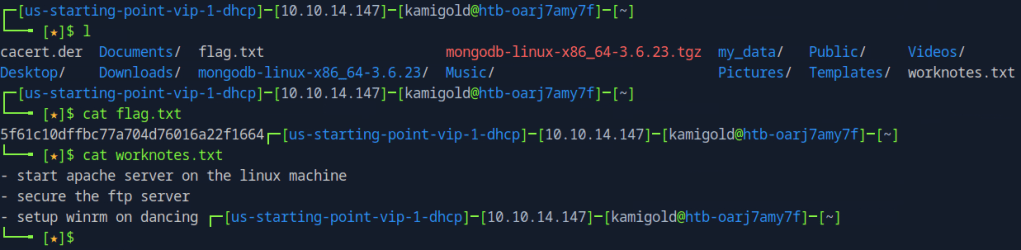
A: 5f61c10dffbc77a704d76016a22f1664
-
Fawn writeup
Task 1 – What does the 3-letter acronym FTP stand for?
A: File Transfer Protocol
Task 2 – Which port does the FTP service listen on usually?
A: 21
Task 3 – FTP sends data in the clear, without any encryption. What acronym is used for a later protocol designed to provide similar functionality to FTP but securely, as an extension of the SSH protocol?
A: SFTP
Task 4 – What is the command we can use to send an ICMP echo request to test our connection to the target?
A: ping
Task 5 – From your scans, what version is FTP running on the target?
Started up our machine got IP 10.129.1.14 and ran nmap
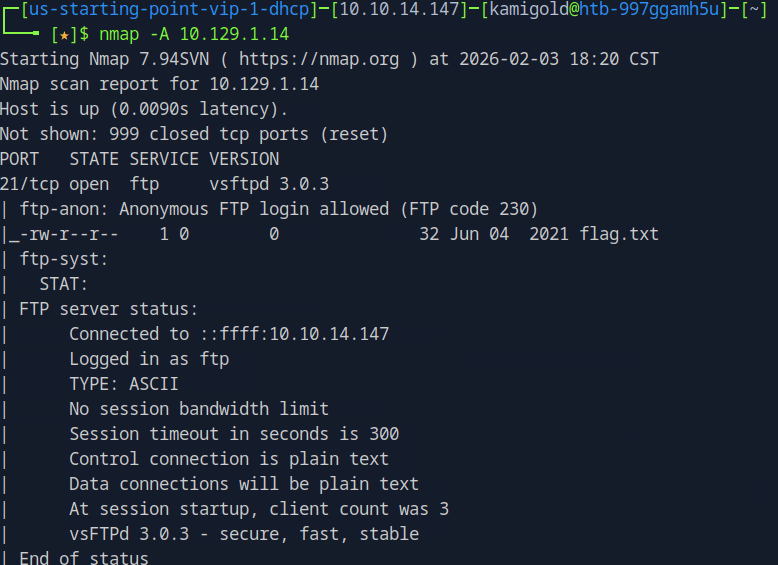
A: vsftpd 3.0.3
Task 6 – From your scans, what OS type is running on the target?
Since I ran -A in the previous command I also got that output
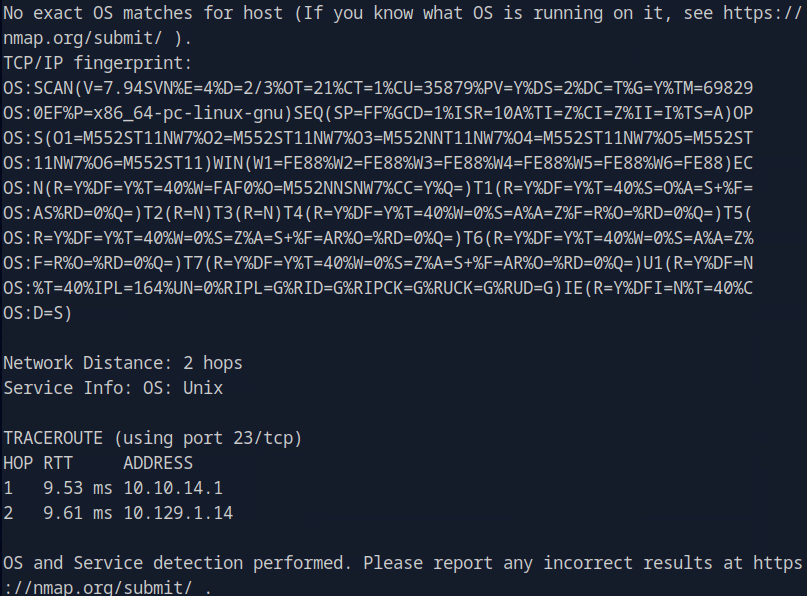
A: Unix
Task 7 – What is the command we need to run in order to display the ‘ftp’ client help menu?
A: ftp -?
Task 8 – What is username that is used over FTP when you want to log in without having an account?
A: anonymous
Task 9 – What is the response code we get for the FTP message ‘Login successful’?
Didn’t recall this from memory so I ftp’d to the machine and logged in with anonymous:anonymous
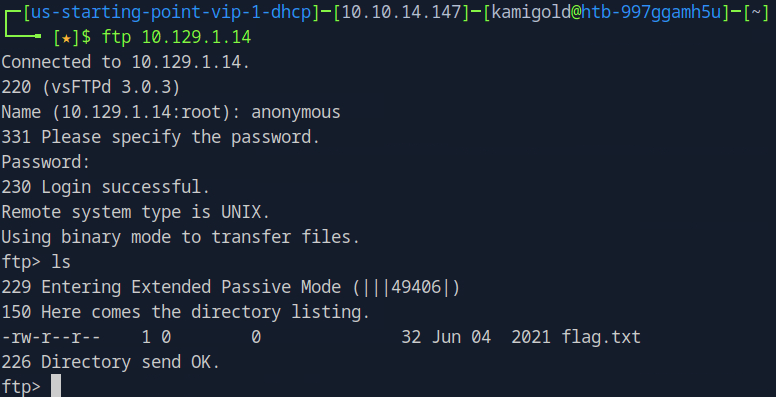
A: 230
Task 10 – There are a couple of commands we can use to list the files and directories available on the FTP server. One is dir. What is the other that is a common way to list files on a Linux system.
Ran this in last screenshot just out of habit when connecting to ftp
A: ls
Task 11 – What is the command used to download the file we found on the FTP server?
A: get
Submit Flag:
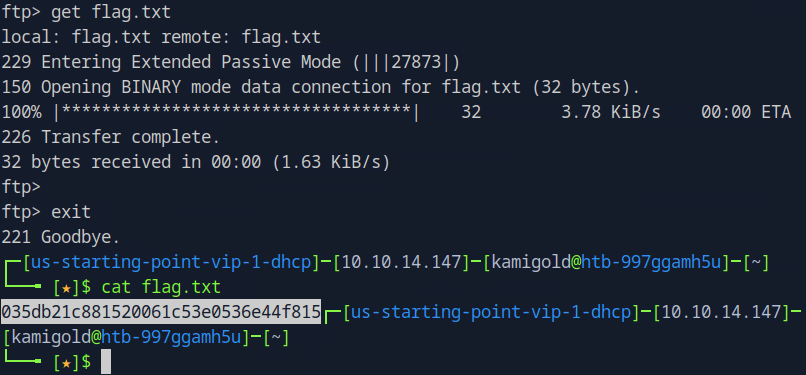
Pulled the file to my machine and read it
A: 035db21c881520061c53e0536e44f815
-
Meow write up
https://app.hackthebox.com/machines/Meow
10.129.1.17
Task 1 – What does the acronym VM stand for?
A: Virtual Machine
Task 2 – What tool do we use to interact with the operating system in order to issue commands via the command line, such as the one to start our VPN connection? It’s also known as a console or shell.
A: terminal
Task 3 – What service do we use to form our VPN connection into HTB labs?
I just know this from clicking around in HackTheBox
A: openvpn
Task 4 – What tool do we use to test our connection to the target with an ICMP echo request?
I use this everyday
A: ping
Task 6 – What is the name of the most common tool for finding open ports on a target?
A: nmap
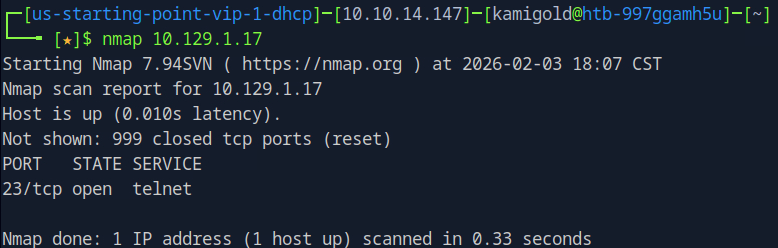
Task 7 – What service do we identify on port 23/tcp during our scans?
A: telnet
I knew all the previous questions from past experience.
Submit Flag
Started up the machine. Following the questions I nmap scanned it anyway and only receive port 23 open
Attempted to connect to that port to see if it had anything interesting and received a log in.
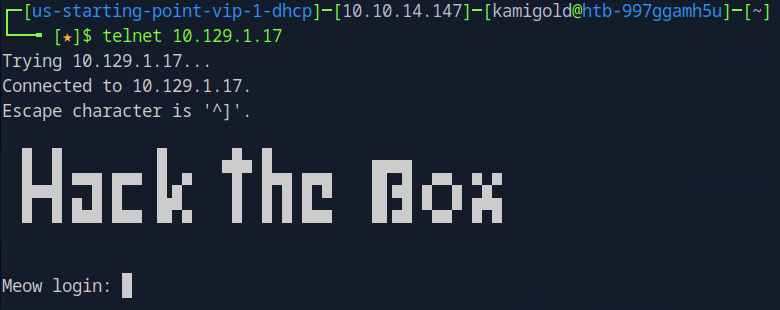
I attempted admin:admin, meow:meow, cat:cat and other iterations of that which did not work. I was confused for a second, but after looking through the questions I ended up using root and it got me in.
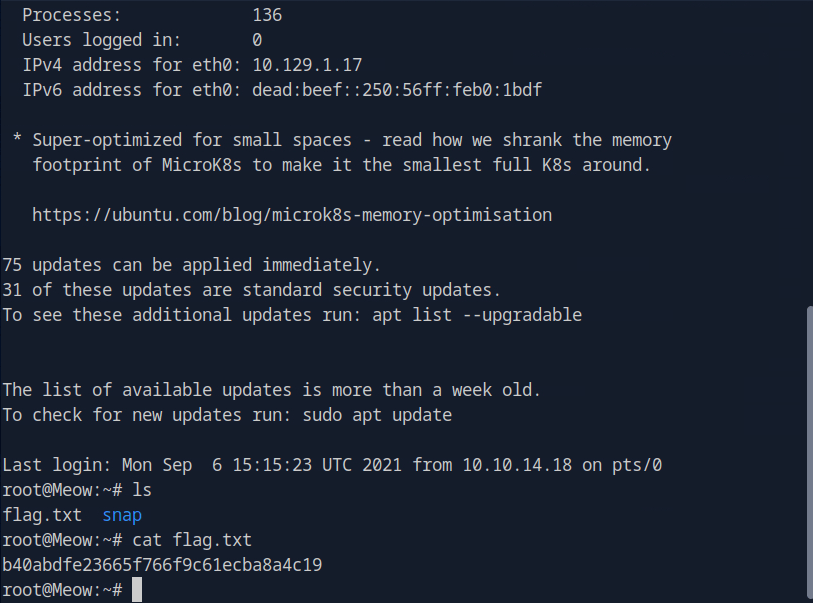
A: b40abdfe23665f766f9c61ecba8a4c19
-
Hello World!
Welcome to my website! This is my very first post, and I’m excited to start sharing ideas, projects, and updates here. Stay tuned for more content coming soon!