10.129.1.15
Task 1 – What Nmap scanning switch employs the use of default scripts during a scan?
I use to use this command a lot but I ended up just switching to -A instead for nmap scans.
A: -sC
Task 2 – What service version is found to be running on port 21?
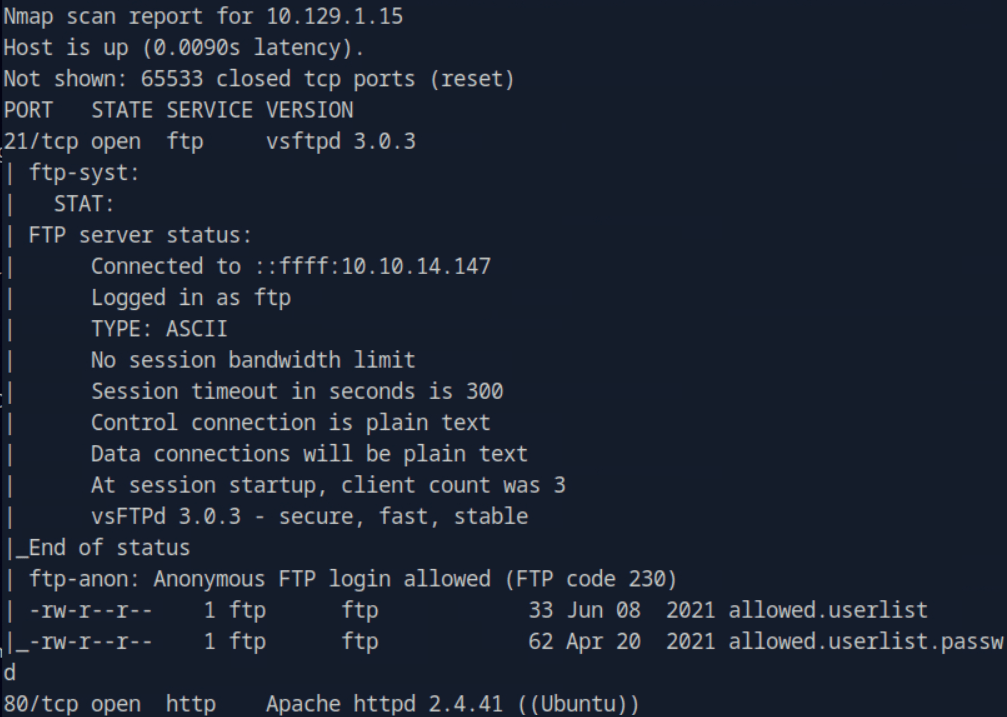
A: vsftpd 3.0.3
Task 3 – What FTP code is returned to us for the “Anonymous FTP login allowed” message?
FTP’d to the machine using anonymous.
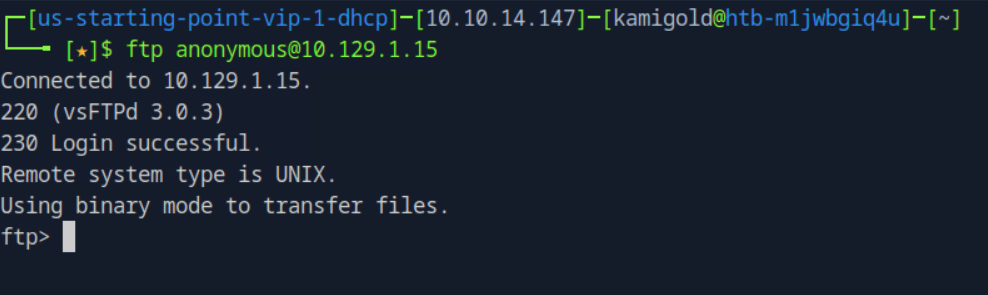
A: 230
Task 4 – After connecting to the FTP server using the ftp client, what username do we provide when prompted to log in anonymously?
A: anonymous
Task 5 – After connecting to the FTP server anonymously, what command can we use to download the files we find on the FTP server?
A: get
Task 6 – What is one of the higher-privilege sounding usernames in ‘allowed.userlist’ that we download from the FTP server?
A: admin
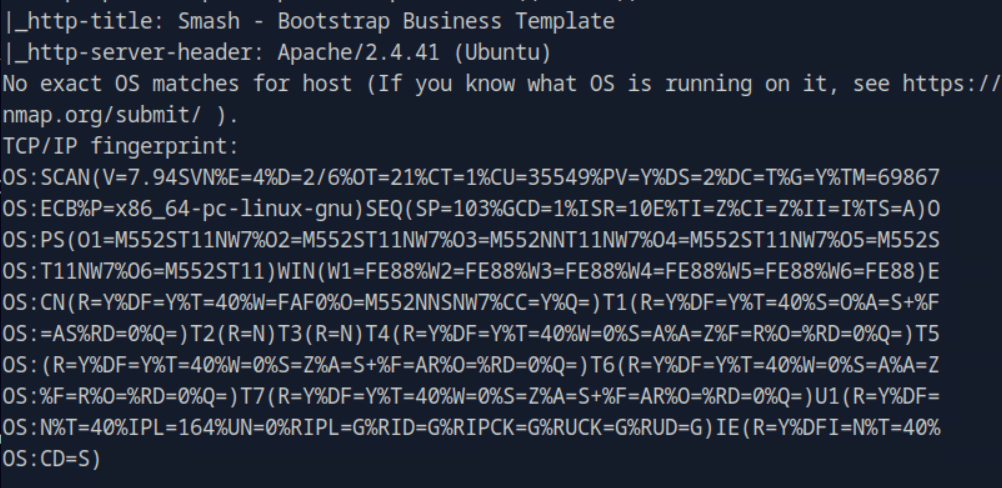
Task 7 – What version of Apache HTTP Server is running on the target host?
From previous scan.
A: Apache httpd 2.4.41
Task 8 – What switch can we use with Gobuster to specify we are looking for specific filetypes?
I ran gobuster without the specific file type, but I know that is -x.
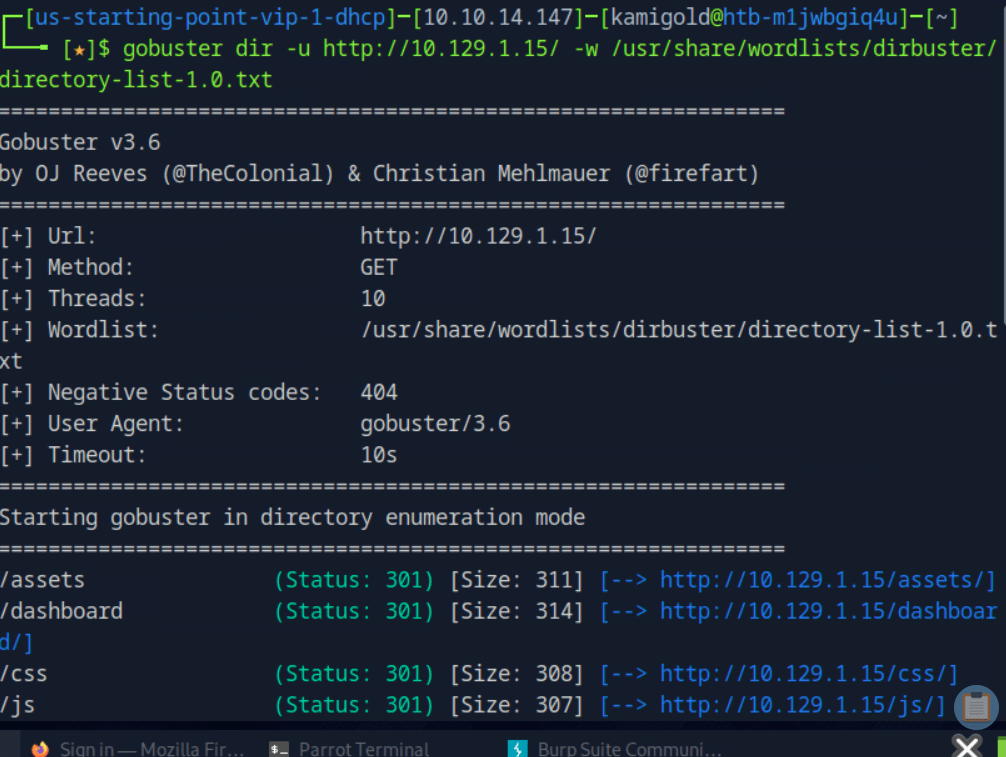
A: -x
Task 9 – Which PHP file can we identify with directory brute force that will provide the opportunity to authenticate to the web service?
I guess I actually needed to run the scan with -x. I ended up finding this anyway with the last scan at /dashboard as that redirected me here.
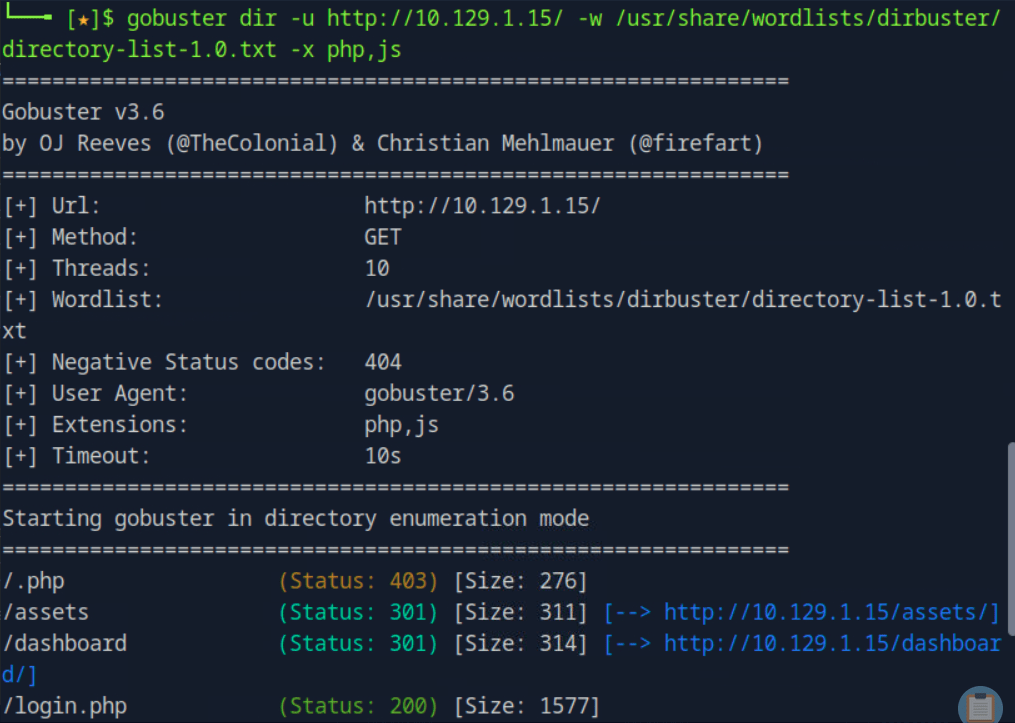
A: login.php
Submit root:
I ended up guessing each username and password we found earlier. There is a faster way if these lists were longer but since there was few passwords and we obviously needed to get into admin I just guessed manually.
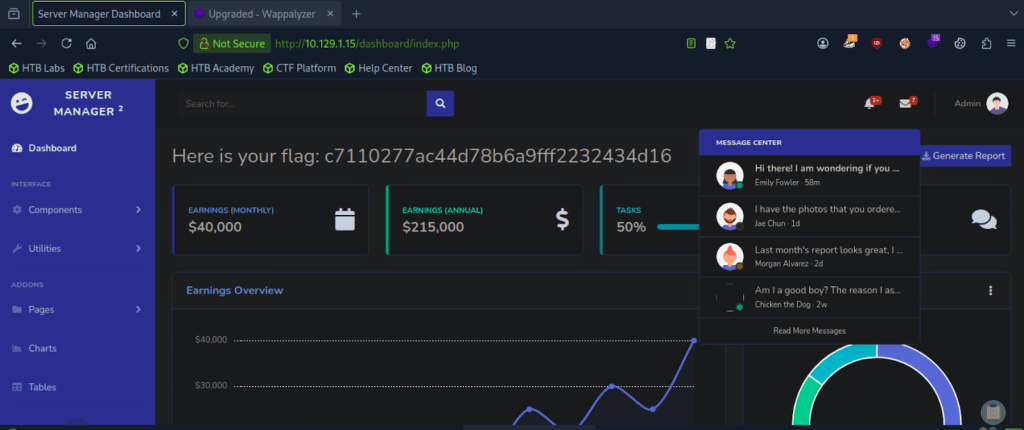
A: c7110277ac44d78b6a9fff2232434d16
GG
Leave a comment