10.129.41.66
Task 1 – How many TCP ports are open on the machine?
Ran “”nmap -A -p- 10.129.41.66””
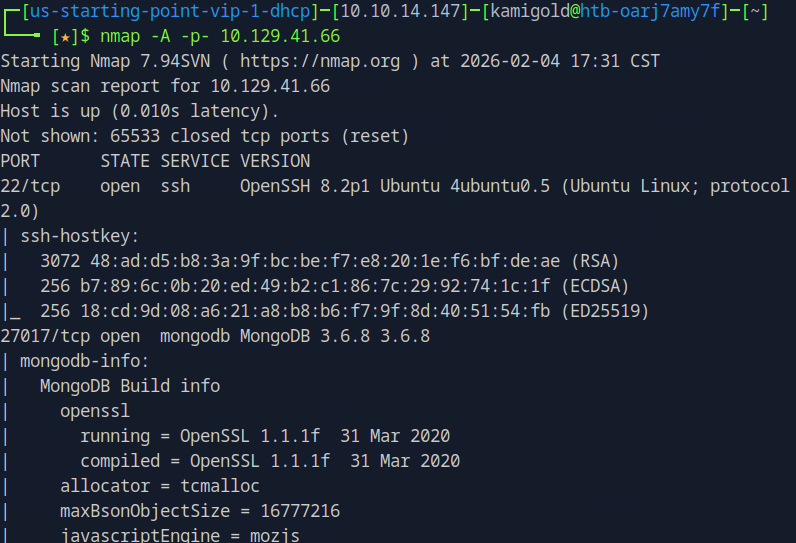
A: 2
Task 2 – Which service is running on port 27017 of the remote host?
A: MongoDB 3.6.8
Task 3 – What type of database is MongoDB? (Choose: SQL or NoSQL)
I didn’t know this. I tried scanning the rest of the nmap scan but I don’t think it provided anything that could point toward it being NoSQL. Also not sure if any further nmap switch could reveal more. I ended up just googling this.
A: NoSQL
Task 4 – What command is used to launch the interactive MongoDB shell from the terminal?
Didn’t know any of this so looked up some pentesting notes. Found this https://hackviser.com/tactics/pentesting/services/MongoDB
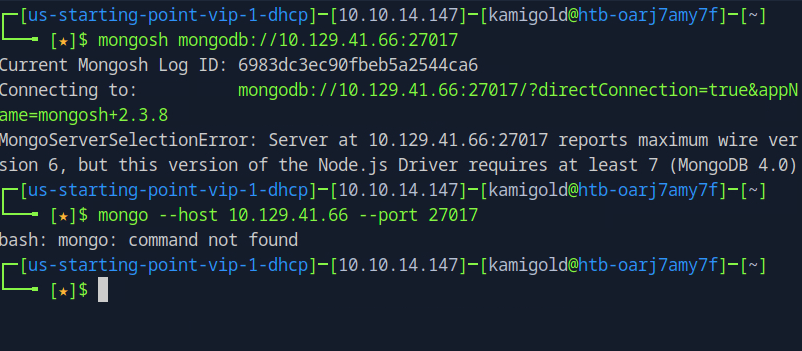
Mongo wasnt on our attacker machine and mongosh doesnt work for that version. I went to install Mongo to see if that would connect and it did
“”wget https://fastdl.mongodb.org/linux/mongodb-linux-x86_64-3.6.23.tgz””
“”tar -xvzf mongodb-linux-x86_64-3.6.23.tgz””
Navigated to the folder and ran “”./mongo 10.129.41.66:27017””
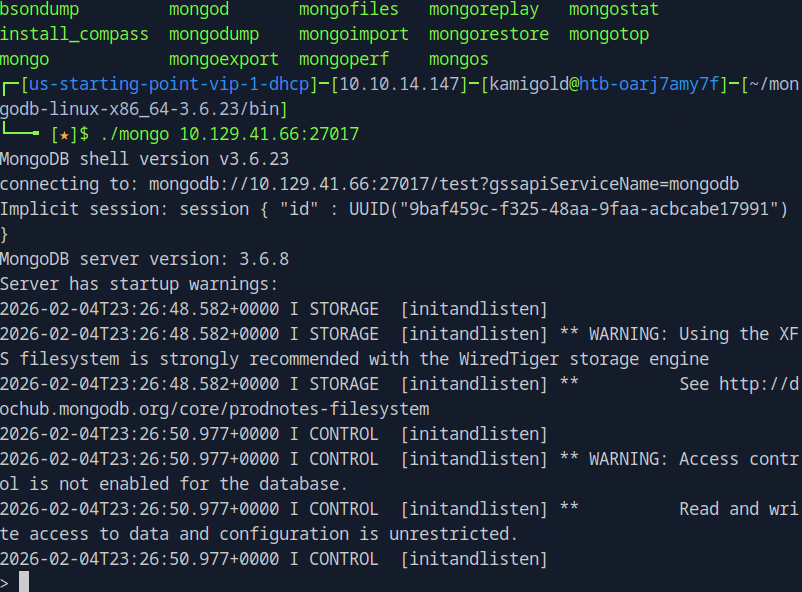
That worked but looking at the answer ending in h, it must have been mongosh. Probably because the machine is older and mongosh has updated since then but it was intended we use that.
A: mongosh
Task 5 – What is the command used for listing all the databases present on the MongoDB server? (No need to include a trailing 😉
Following the notes on the site
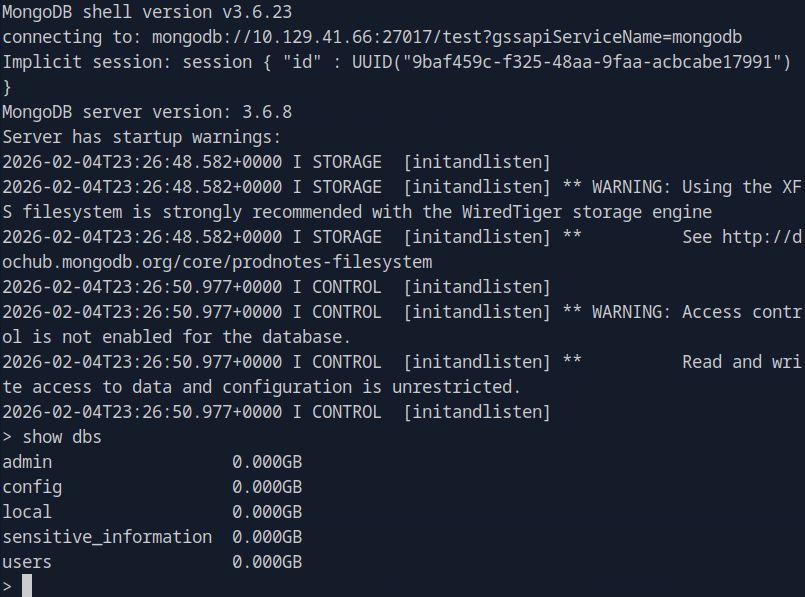
A: dbs
Task 6 – What is the command used for listing out the collections in a database? (No need to include a trailing 😉
Still following those notes, these are great.

It didnt seem to return anything though.
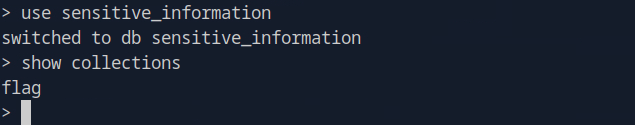
A: show collections
Task 7 – What command is used to dump the content of all the documents within the collection named flag?
I then realised that I’m supposed to “”use {database}”” then show collections. Poked around and found ‘flag’ in the sensitive_information database.
I couldn’t find how to interact with ‘flag’ from the notes on that website. Ended up researching further and found myself in the actual documentation. https://www.mongodb.com/docs/manual/crud/#find-documents
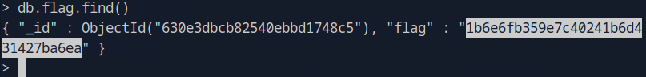
A: db.flag.find()
Submit Flag: 1b6e6fb359e7c40241b6d431427ba6ea
Leave a comment