10.129.40.89
Task 1 – Directory Brute-forcing is a technique used to check a lot of paths on a web server to find hidden pages. Which is another name for this? (i) Local File Inclusion, (ii) dir busting, (iii) hash cracking.
A: dir busting
Task 2 – What switch do we use for nmap’s scan to specify that we want to perform version detection
A: -sV
Task 3 – What does Nmap report is the service identified as running on port 80/tcp?
Ran nmap to scan the device, even though it is likely a webserver on http
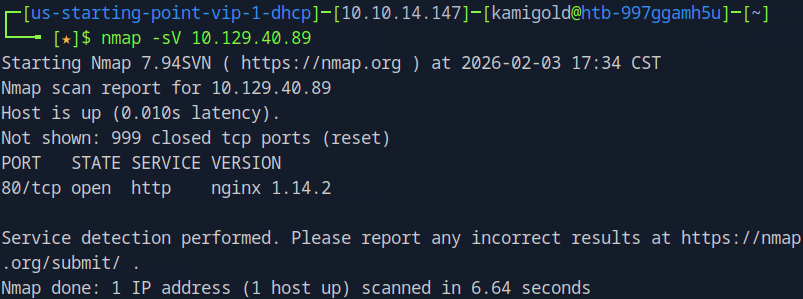
A: http
Task 4 – What server name and version of service is running on port 80/tcp?
A: nginx 1.14.2
Task 5 – What switch do we use to specify to Gobuster we want to perform dir busting specifically?
Already used gobuster, so I know this
A: dir
Task 6 – When using gobuster to dir bust, what switch do we add to make sure it finds PHP pages?
A: -x php
Already had this in notes to, can remember this as x for extension
Task 7 – What page is found during our dir busting activities?
Ran
‘’gobuster dir -u 10.129.40.89 -w gobuster dir -u 10.129.40.89 -w /usr/share/wordlists/dirbuster/directory-list-1.0.txt’’
That returned nothing but that didn’t seem right. Even though its a smaller list I couldn’t imagine a easier box that had issue. Considering Task 6 I decided to add that switch
“gobuster dir -u 10.129.40.89 -w /usr/share/wordlists/dirbuster/directory-list-1.0.txt -x php”
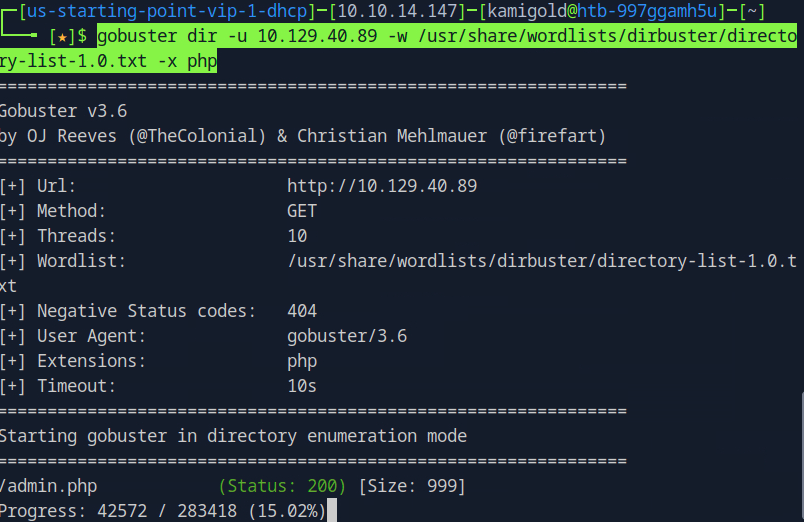
This worked and found /admin.php right away
Task 8 – What is the HTTP status code reported by Gobuster for the discovered page?
In previous screenshot status is 200
A: 200
Submit Flag:
Navigated to the website at that newly found directory and it brought us to an Admin Console Login searching for a username and password. Considering they fastballs thrown at me, I attempted admin:admin and it worked.
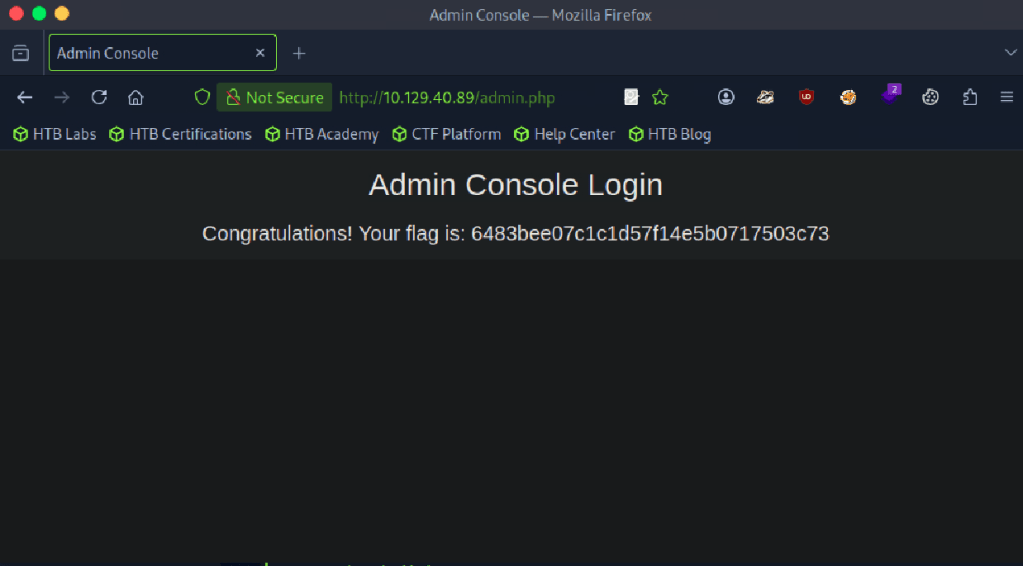
A: 6483bee07c1c1d57f14e5b0717503c73
Leave a comment